January 27, 2026
Updated: May 11, 2026
A procurement-focused ranking of leading U.S. penetration testing providers by testing depth, compliance fit, reporting quality, and cloud/API relevance.
Mohammed Khalil

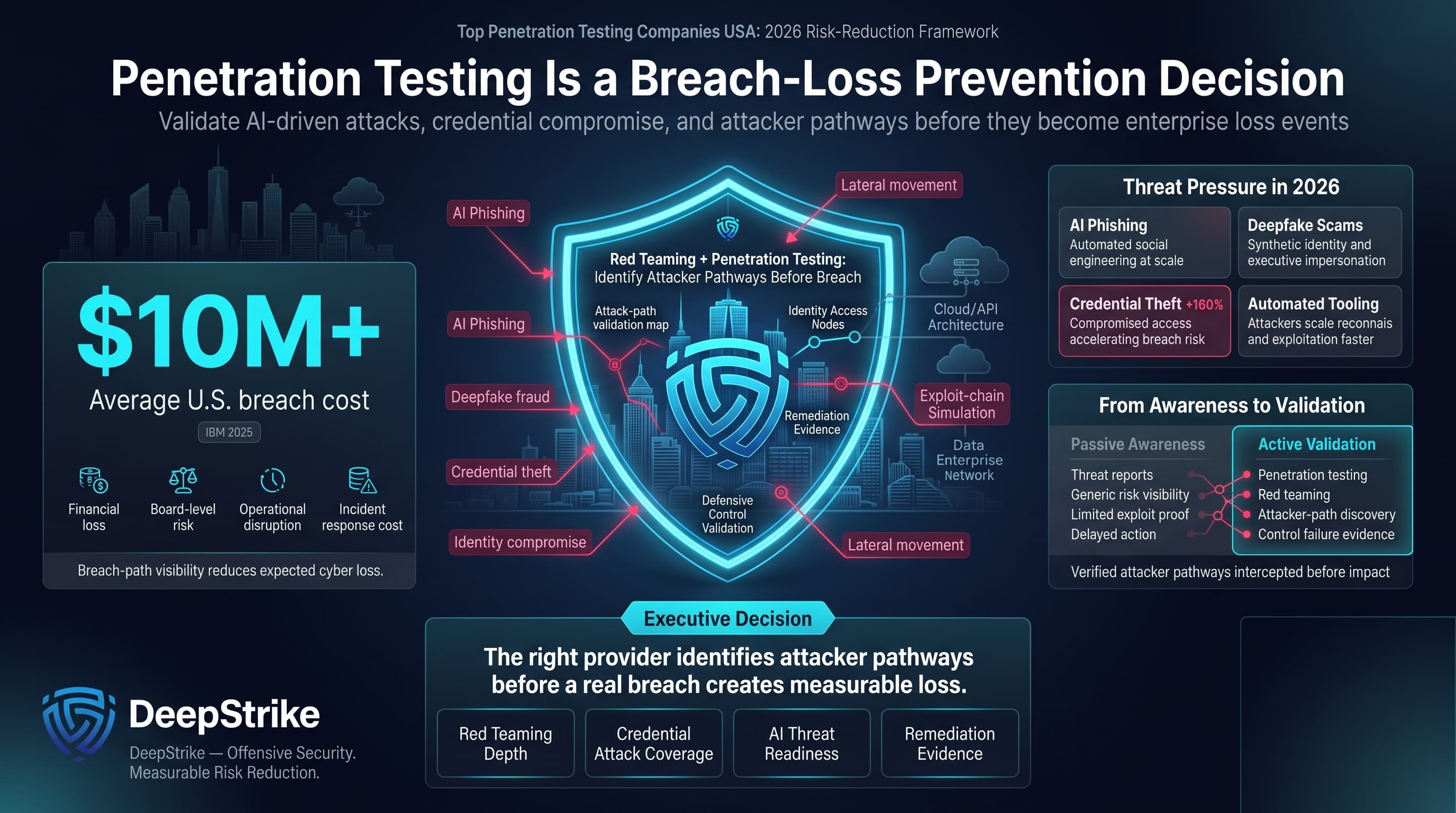
Cyber threats are intensifying for U.S. organizations. For example, IBM reports the average cost of a data breach in the United States exceeded $10 million in 2025. Simultaneously, attackers are leveraging AI and automated tools to amplify attacks (e.g., AI-enabled phishing and deepfake scams), along with rampant credential theft (compromised credentials are surging, up 160% in 2025). In this high-stakes context, choosing among the top penetration testing companies in the USA becomes a critical decision for risk-conscious enterprises. Penetration testing (red teaming) helps identify attacker pathways before a real breach, reducing expected loss from cyber incidents.
USA enterprises face growing compliance and assurance pressure, but penetration-testing obligations depend on the buyer’s sector, control boundary, contracts, and audit scope. PCI DSS includes explicit penetration-testing requirements where cardholder-data environments are in scope. Healthcare-sensitive buyers may use penetration testing to support HIPAA risk analysis and technical-control validation, while finance-sensitive organizations may use it as part of broader GLBA, FFIEC, or FTC Safeguards security-program expectations where relevant. Public companies may also use testing evidence to support cyber-risk governance and disclosure readiness. SOC 2, ISO 27001, and NIST-aligned programs can make penetration testing commercially important, but buyers should confirm exact applicability rather than assuming every framework applies universally.
The USA penetration testing market is mature and evolving. Analysts project global pentesting revenues rising above $3 billion by 2026. North America drives a large share, with increasing adoption of continuous PTaaS and cloud-based testing models. Modern buyers value providers that can test cloud-native and API-heavy architectures, reflecting the shift to SaaS and distributed apps. Against this backdrop, this ranking is methodology-driven and not sponsored. Providers are compared by testing depth, reporting usefulness, cloud and API relevance, retesting clarity, and evidence-sensitive USA buyer fit.
Penetration testing is a structured adversarial security assessment that combines automated vulnerability discovery with manual exploit validation to identify real-world attack paths, validate control effectiveness, and reduce breach probability.
U.S. buyers, especially in regulated industries, bring unique procurement expectations. They operate under stricter compliance scrutiny (HIPAA for healthcare, GLBA/FFIEC for banking, SEC/FTC rules for public companies, etc.), so pentesting is often treated as more than a technical check-box. Buyers demand alignment with relevant frameworks: for example, mapping findings to SOC 2, ISO 27001, PCI DSS, or NIST controls helps satisfy auditors. Providers that explicitly tie results to these standards score higher in a compliance-focused review. In highly regulated sectors (finance, healthcare, federal contracting, critical infrastructure), buyers are cautious and usually favor detailed reporting and evidence-backed remediation guidance.
Cultural factors also play a role. Some U.S. enterprises prefer vendors with a U.S. presence or references, due to procurement rules or data residency concerns, though global/cross-border models are common. Buyers often scrutinize a vendor’s methodology: they expect manual exploit validation rather than raw scan outputs, and they seek credible certifications (e.g. OSCP, OSWE, CREST). Oversimplified "scan-only" approaches or unverified automated findings are viewed skeptically. In cloud and API-heavy environments, U.S. organizations pay extra attention to cloud security expertise and DevSecOps integration. Finally, government or defense-related buyers may require vendors to commit to specific clearances or FedRAMP-like rigour, so providers with past federal engagements or FedRAMP guidance have an edge.
In summary, USA buyers look for penetration test providers that combine proven technical depth with audit-ready deliverables. Reports are expected to be comprehensive, clearly mapping issues to controls. Buyers often verify a vendor’s track record in U.S. environments; local trust and references matter. This ranking reflects those preferences and aims to highlight methodological differences rather than marketing claims.
The ranking evaluates vendors against criteria important to enterprise U.S. buyers. Key factors included:
We did not accept unverified marketing claims. For each capability, we sought supporting evidence (certifications, client references, or technical details). Where evidence was lacking, we treated it as unproven. Our methodology emphasizes demonstrable exploitability validation and audit-friendly practices over mere scanning volume.
Why They Stand Out: DeepStrike stands out in this ranking for manual exploit-validation depth, cloud and API testing relevance, remediation-oriented reporting, and a flexible delivery model compared with larger consulting structures. Public material positions the company around manual testing and PTaaS-style workflows, but buyers should confirm exact tester assignment, retesting terms, and compliance-mapping scope during procurement.
USA Relevance: DeepStrike is relevant to USA buyers that prioritize manual testing depth, cloud/API validation, remediation clarity, and evidence suitable for audit-heavy environments. Buyers with federal contracting, on-site, data-residency, framework-specific, or public-sector requirements should confirm those conditions directly before procurement.
Testing Depth Model: Manual exploit chaining. DeepStrike prioritizes human-led analysis. Testers manually validate and exploit vulnerabilities (beyond automated discovery), simulating real attacker paths. This model excels at uncovering complex business-logic flaws and advanced attack chains, which benefits regulated and risk-sensitive environments.
Key Strengths:
Potential Limitations:
Best For: Regulated enterprises and technology companies that need expert manual testing and compliance-friendly reporting. Also suited for continuous testing programs (cloud- or API-first firms) that can benefit from its PTaaS model.
Why They Stand Out: Rapid7 is relevant in this ranking because of its broad security platform ecosystem and enterprise-scale service coverage (e.g. InsightVM, Metasploit). Its pentesting services leverage deep vulnerability intelligence and attacker knowledge. Pentesters contribute to open-source tools like Metasploit and devote substantial bench time to research. Rapid7’s scale and mature processes make it capable of handling complex, multi-geography engagements for large corporations.
USA Relevance: U.S.-headquartered with a strong presence in North America, Rapid7 is well-positioned to serve domestic enterprises and federal agencies. Its public positioning indicates broad enterprise-market relevance. Buyers should confirm sector-specific references, public-sector suitability, and delivery requirements directly during procurement. Rapid7’s corporate maturity and SOC/ISO compliance posture are familiar to U.S. procurement teams, though buyers should confirm whether local support or specific clearances are needed.
Testing Depth Model: Hybrid model. Rapid7 combines automated scanning (powered by its Insight platform) with manual verification by consultants. This approach allows broad coverage (via tools) while retaining human-driven exploit validation. The hybrid model provides balance between scale and depth, suitable for enterprises needing both efficiency and credible exploit evidence.
Key Strengths:
Potential Limitations:
Best For: Large enterprises, especially those already using Rapid7 security products or requiring extensive coverage. Also suited for organizations wanting a one-stop solution that ties pentesting into a larger security platform.
Why They Stand Out: HackerOne stands out for crowdsourced vulnerability discovery, vulnerability disclosure workflows, and continuous security-testing programs. Its model can expand testing coverage beyond a single consulting team, but buyers should confirm whether the engagement is intended to supplement or replace a fixed-scope penetration test.
USA Relevance: With a major U.S. presence and a large number of U.S.-based researchers, HackerOne is widely adopted by American companies and agencies. Public materials may show enterprise and public-sector-adjacent relevance, but buyers should verify specific customer references, public-sector applicability, and program constraints from source notes before relying on them in procurement. Buyers in the USA who want a continuous, crowd-driven supplement to pentesting may find HackerOne relevant. (However, note that bug bounties complement but do not replace targeted red-team projects.)
Testing Depth Model: Hybrid model. HackerOne leverages both automated triage and a vast pool of human testers. While many vulnerabilities are found by independent researchers submitting reports, internal team members verify and reproduce issues. The model scales well for large attack surfaces but can vary in depth depending on bounty scope.
Key Strengths:
Potential Limitations:
Best For: Organizations with mature security programs that want continuous, crowd-driven testing (e.g. large tech firms or financial institutions). Also useful for supplementing periodic pentests, especially when covering large or dynamic attack surfaces.
Why They Stand Out: Synack combines a private bug bounty model with platform controls. Its vetted researcher model provides continuous testing under controlled conditions where evidenced. Synack is positioned around controlled researcher access, platform oversight, and structured validation workflows. Buyers should confirm founder-background claims and public-sector relevance from source notes before relying on them. It even developed an AI agent (Sara) for autonomous testing. This hybrid crowdsourcing approach has earned Synack placements in Gartner’s PTaaS Radar.
USA Relevance: Synack’s strong ties to U.S. federal security initiatives make it relevant for government and regulated sectors. Public materials may indicate relevance for sensitive public-sector-adjacent environments where evidenced; buyers should verify named public-sector references directly. For U.S. healthcare and financial firms, Synack’s platform is designed to meet strict audit requirements. (Buyers should review how Synack’s crowdsourced model aligns with any specific procurement or compliance standards in their industry.)
Testing Depth Model: Hybrid model. The Synack platform lets clients define scopes and manage researcher assignments. While the model relies on crowdsourced reporting, Synack enforces high testing standards (triage, proof-of-concept requirements). The depth can approach that of a traditional engagement, especially given the large researcher pool, but depends on incentives and duration.
Key Strengths:
Potential Limitations:
Best For: Highly regulated and government organizations (e.g. federal agencies, defense contractors) needing continuous, compliant pentesting. Also suitable for enterprises willing to leverage crowdsourced insights and requiring stringent validation of test results.
Why They Stand Out: Cobalt stands out for platform-led pentesting workflows, developer collaboration, and practical fit for product-led teams. Its platform positioning emphasizes fast launch, tester collaboration, and workflow visibility. Buyers should confirm actual kickoff timelines, tester availability, and specialist assignment terms contractually. The focus is on developer enablement, with CI/CD integration and API-first tools.
USA Relevance: U.S.-based with North American and European offices, Cobalt serves many American tech companies. Its emphasis on continuous testing resonates with SaaS firms and product teams common in Silicon Valley and other U.S. tech hubs. Cobalt has also been active in U.S. cybersecurity events and content (e.g., State of Pentesting reports).
Testing Depth Model: Hybrid model. Cobalt combines automated scans (continuous scanning options) with manual validation by its pentesters. The model emphasizes quick turnarounds and breadth, but experienced Cobalt reviewers still verify critical vulnerabilities. For clients, this yields faster feedback cycles but may vary in depth per engagement.
Key Strengths:
Potential Limitations:
Best For: Agile, cloud-native companies (especially SaaS and DevOps teams) that need frequent, automated pentesting with developer-friendly workflows. Also appropriate for mid-size enterprises that value quick, integrated security testing.
Why They Stand Out: BreachLock markets itself as an AI-enhanced PTaaS provider. It offers a platform that continuously discovers and tests attack surfaces. The company’s public positioning emphasizes offensive-security experience, PTaaS delivery, and attack-surface visibility. BreachLock emphasizes automation and rapid engagement turnaround (public materials may describe fast response or onboarding; buyers should confirm exact service-level expectations contractually).
USA Relevance: BreachLock is relevant to USA buyers evaluating PTaaS, attack-surface management, and continuous testing models. Buyers should confirm office locations, delivery footprint, and regional support from source notes. The LinkedIn profile touts continuous testing and attack surface monitoring, which aligns with priorities of modern U.S. businesses. Notably, BreachLock has promoted compliance-focused content (e.g. PCI DSS 4.0 guidance), indicating readiness to serve regulated sectors.
Testing Depth Model: Automated-heavy. BreachLock’s platform combines automated scanning (using AI) with expert review. The focus on continuous ASM suggests that much of the workload is automated, flagging exposures for pentesters to confirm. This is effective for high coverage and quick iteration, though it may be less focused on deep manual exploitation than pure red-team vendors.
Key Strengths:
Potential Limitations:
Best For: Fast-moving organizations (including tech startups and SMBs) that need continuous, automated pentesting and attack surface monitoring. Also suitable for companies under PCI DSS 4.0 or similar requirements seeking evidence-backed penetration testing.
Why They Stand Out: Bishop Fox stands out for red-team-oriented testing, application and cloud assessment relevance, and visible offensive-security research. Its model is most relevant when buyers need deeper breach-path validation rather than broad scan output.
USA Relevance: U.S.-based with a strong footprint in major tech hubs, Bishop Fox caters heavily to American enterprises. Enterprise-market relevance appears in public positioning, but specific Fortune-scale, federal, national-security, or critical-infrastructure claims should be confirmed from source notes before publication.
Testing Depth Model: Red-team oriented. Bishop Fox specializes in manual, goal-driven testing designed to emulate sophisticated attackers. Its engagements focus on thorough exploit chaining and emerging threats. This model is relevant for mature security organizations that need deeper breach-path validation, subject to scope, budget, and evidence of delivery fit.
Key Strengths:
Potential Limitations:
Best For: Enterprise-level organizations (especially in tech and critical sectors) seeking deep-red-team capabilities and expert offensive security. Also ideal for companies under strict breach-impact scenarios that require exhaustive testing.
| Company | Specialization | Testing Depth Model | Best For | USA Fit | Compliance Alignment | Ideal Organization Size |
|---|---|---|---|---|---|---|
| DeepStrike | Manual-depth penetration testing and PTaaS-style workflows | Manual exploit chaining | Cloud-first and API-heavy teams | USA relevance; exact delivery footprint should be confirmed | Compliance-oriented reporting appears in public positioning | Mid-market to enterprise |
| Rapid7 | Enterprise security platform and penetration testing services | Hybrid model | Enterprise-scale programs | USA-headquartered with broad enterprise relevance | Formal assurance alignment where evidenced | Large enterprise |
| HackerOne | Crowdsourced vulnerability discovery and bug bounty programs | Hybrid model | Continuous exposure discovery | USA-headquartered platform with global researcher relevance | Compliance fit should be confirmed per program | Mid-market to enterprise |
| Synack | Controlled researcher-based PTaaS and platform validation | Hybrid model | Sensitive and high-change environments | USA-headquartered platform; public-sector fit should be confirmed | Regulated-environment relevance where evidenced | Enterprise |
| Cobalt | PTaaS for web, mobile, API, and product teams | Hybrid model | Agile SaaS and developer-led teams | USA-founded with product-led buyer relevance | Compliance support should be confirmed per scope | SMB to mid-market |
| BreachLock | PTaaS, ASM, and continuous security testing | Automated-heavy | SMBs and compliance-sensitive mid-market buyers | USA-headquartered with global relevance where evidenced | PCI/ISO-oriented positioning appears relevant where supported | SMB to mid-market |
| Bishop Fox | Manual penetration testing, red teaming, and offensive security | Red-team oriented | High-assurance enterprise programs | USA-headquartered with enterprise-market relevance | Audit-heavy and regulated-environment fit where evidenced | Enterprise |
In choosing a provider, consider organizational scale and needs. Large enterprises typically require comprehensive scope (hundreds of apps/infrastructure components), support for multiple simultaneous projects, and granular compliance reporting. They can afford higher-tier consulting services (e.g. multi-week red teams) and benefit from dedicated account teams. Boutique or mid-size firms may struggle to supply dozens of testers on short notice, though their small size can offer faster communication and customization.
SMBs or startups often prioritize budget and speed. They may opt for smaller engagements focused on critical assets, or continuous scanning models to maintain oversight with lower cost. However, they should be wary of very low-cost vendors that only run tools. For an SMB, a mid-size PTaaS provider (with predictable pricing and developer integration) might strike a balance.
Key trade-offs:
In summary, match the vendor scale and model to your needs: if you need high assurance and have a complex environment, prioritize depth (even at higher cost). If you have limited scope or budget, a smaller PTaaS-oriented provider may suffice just to verify they can scale up if needed in the future.
Penetration testing cost depends on many factors rather than fixed rates. Primary drivers include the scope and complexity of the assessment. Testing a large web application with millions of lines of code, numerous APIs, and multi-tenant cloud infrastructure will require significantly more effort than a small static site or network segment. Authentication level matters: authenticated (credentialed) tests take more effort to plan and execute than unauthenticated scans. Attack surface size (number of IPs, subnets, cloud accounts) scales cost, as does the inclusion of additional areas like physical or social engineering tests.
Technology factors also influence cost. For example, testing cloud-native microservices, complex APIs, identity flows, or specialized systems usually requires deeper expertise and more testing time. Depth of testing is key: adversarial engagements (red teams) that attempt persistent breach scenarios are more expensive than point-in-time vulnerability scans. Similarly, providing detailed deliverables (e.g. comprehensive executive and technical reports, compliance mappings) increases labor input and price.
Additional considerations include the delivery model. On-site testing (if required) adds travel costs and scheduling complexities. Retesting policy can affect budgeting: some firms include limited retesting, while others price remediation validation separately. Engagement speed matters too; accelerated timelines may change staffing requirements and commercial terms.
In regulated or continuous environments, companies might also adopt subscription or retainer models (e.g. quarterly scans or PTaaS subscriptions). In such cases, total cost is influenced by contract length and frequency of tests rather than individual project size.
Crucially, USA buyers should avoid relying on average price benchmarks. Instead, focus on understanding what your specific requirements entail and how different providers price those services. A tailored quote, aligned to your environment’s complexity and compliance needs, is the best way to predict investment levels.
How much do penetration testing services cost in the USA?Pricing varies widely by scope, organization size, and test depth. Rather than quoting fixed rates, providers typically offer quotes based on factors like application complexity, number of hosts, and testing methodology. Enterprise-level engagements usually require broader scoping, deeper manual testing, more stakeholder reporting, and stronger remediation validation than smaller projects. Exact figures should come from vendor proposals after scope definition. Focus on what drives cost: more assets, advanced techniques, and broader compliance work will raise the price.
What is included in enterprise penetration testing?A thorough enterprise pentest will encompass network and application layers (external, internal, web/mobile, APIs), plus potentially cloud infrastructure and identity systems. It usually includes reconnaissance, vulnerability scanning, manual exploitation, and post-exploit activities to map out full attack paths. Deliverables typically consist of a detailed report with vulnerability findings, risk ratings, remediation advice, and in-depth executive summary. Many enterprise assessments also incorporate a retesting phase to confirm fixes and align results with relevant compliance standards.
Are certifications more important than tools?Neither alone suffices. Effective pentesting requires both skilled testers and good tooling. Certifications (OSCP, OSWE, CISSP, CREST GPEN, etc.) are evidence of a tester’s competence and can be a proxy for expertise. However, access to high-quality automated tools and threat intelligence can also improve coverage and efficiency. Buyers should look for a combination: certified, experienced analysts who can leverage robust testing frameworks.
How long does a pentest engagement take?Engagement length depends on scope. A small web app test might take 2–3 weeks, whereas a comprehensive enterprise assessment could take 4–8 weeks or more. Red team simulations can last several months. Preparation and scoping also add time (e.g., weeks for planning, kickoff, and optional retest). It’s best to discuss timelines with vendors upfront. Many providers can compress schedules for an additional fee if needed.
Is penetration testing required for HIPAA, GLBA, SEC/FTC compliance, FedRAMP, CMMC, SOC 2, ISO 27001, or PCI DSS?Requirements vary. PCI DSS contains explicit penetration-testing requirements where cardholder-data environments are in scope. FedRAMP, CMMC, HIPAA, GLBA/FFIEC, SEC disclosure expectations, FTC Safeguards, SOC 2, ISO 27001, and state privacy laws do not apply uniformly to every USA buyer. These frameworks or regulatory regimes may make penetration testing commercially important as part of risk analysis, technical-control validation, or audit evidence, but buyers should confirm obligations against their sector, contracts, control boundary, and assessor expectations.
How often should penetration testing be performed?As a baseline, most frameworks advise at least annual testing or after significant changes. Many U.S. organizations now move toward more frequent or continuous testing (e.g. quarterly, or rolling PTaaS) for faster risk reduction. Critical systems (especially internet-facing apps) might be tested multiple times per year. The exact cadence should balance risk (frequency of updates or exposure changes) with budget and operational impact.
Should USA buyers choose a local provider or a cross-border specialist firm?It depends on requirements. A local U.S. provider may simplify contracting, time-zone alignment, communication, and some procurement workflows where relevant. However, a specialist firm (even if headquartered overseas) might offer superior technical expertise or cost-effectiveness, provided they meet any legal/residency conditions. Verify that the provider can legally and securely work with your data. Language and responsiveness also matter: confirm that remote teams can adequately support your time zone and compliance needs. Ultimately, choose the firm that best matches your technical and regulatory requirements, regardless of geography.
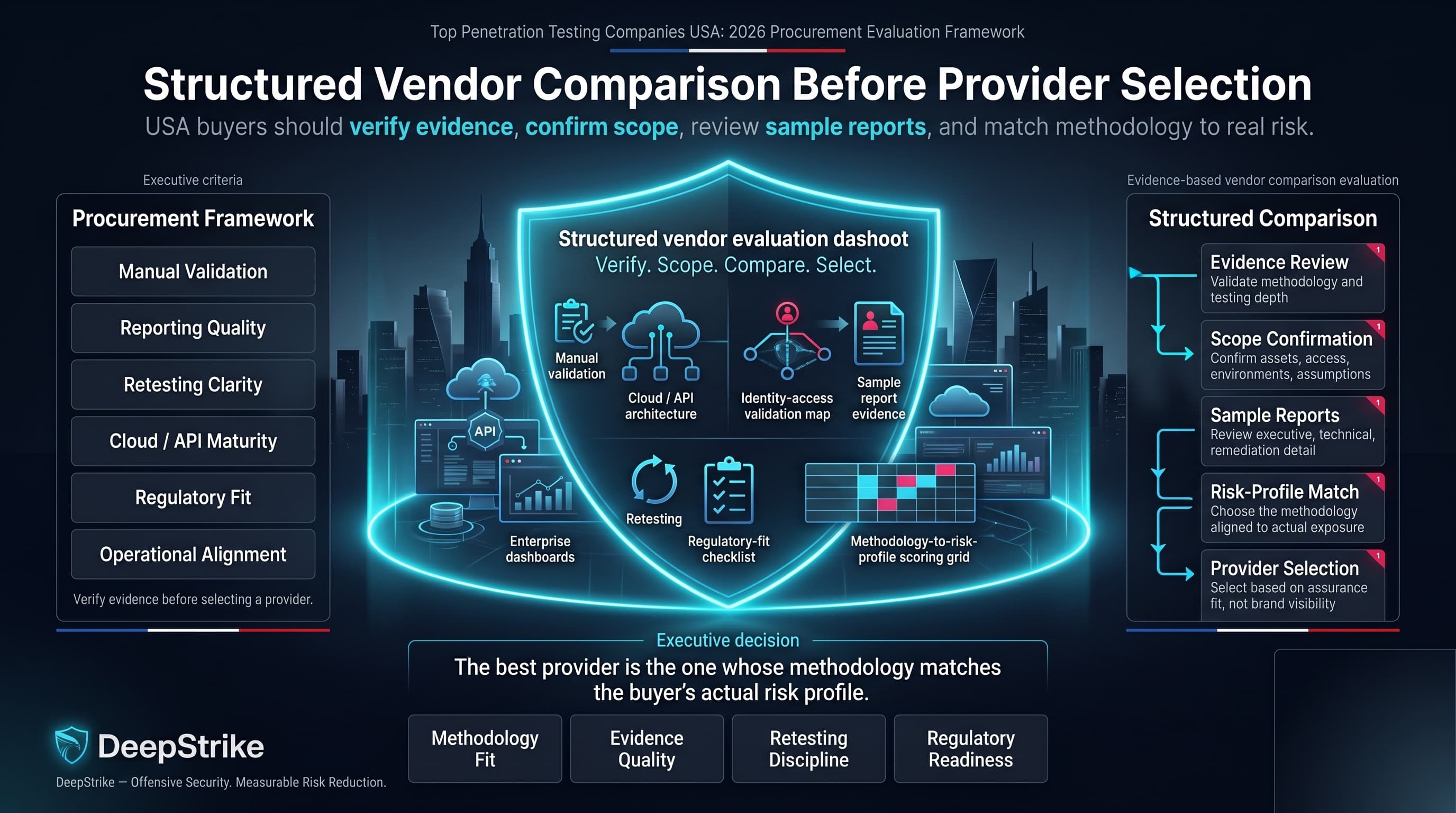
This ranking of the top penetration testing companies USA for 2026 is built around structured vendor comparison rather than brand visibility alone. The most useful shortlist is not the provider with the broadest service menu, but the provider that can evidence manual validation, reporting quality, retesting clarity, cloud and API maturity, and fit for the buyer’s regulatory or operational environment. USA buyers should treat this comparison as a procurement framework: verify the evidence, confirm the scope, review sample reports, and choose the provider whose methodology matches the actual risk profile.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us