August 26, 2025
Updated: April 19, 2026
A complete guide to penetration testing methodologies in 2025, covering PTES, NIST SP 800-115, OWASP, OSSTMM, and MITRE ATT&CK.
Mohammed Khalil
Let's get one thing straight: a real penetration testing methodology is more than just a checklist. It's a formal, documented game plan that outlines the scope, phases, and rules for an ethical hacking engagement. Think of it as the strategic blueprint that separates a professional security assessment from an unstructured, ad hoc "hack." It ensures the process is repeatable, thorough, and, most importantly, safe for your environment.
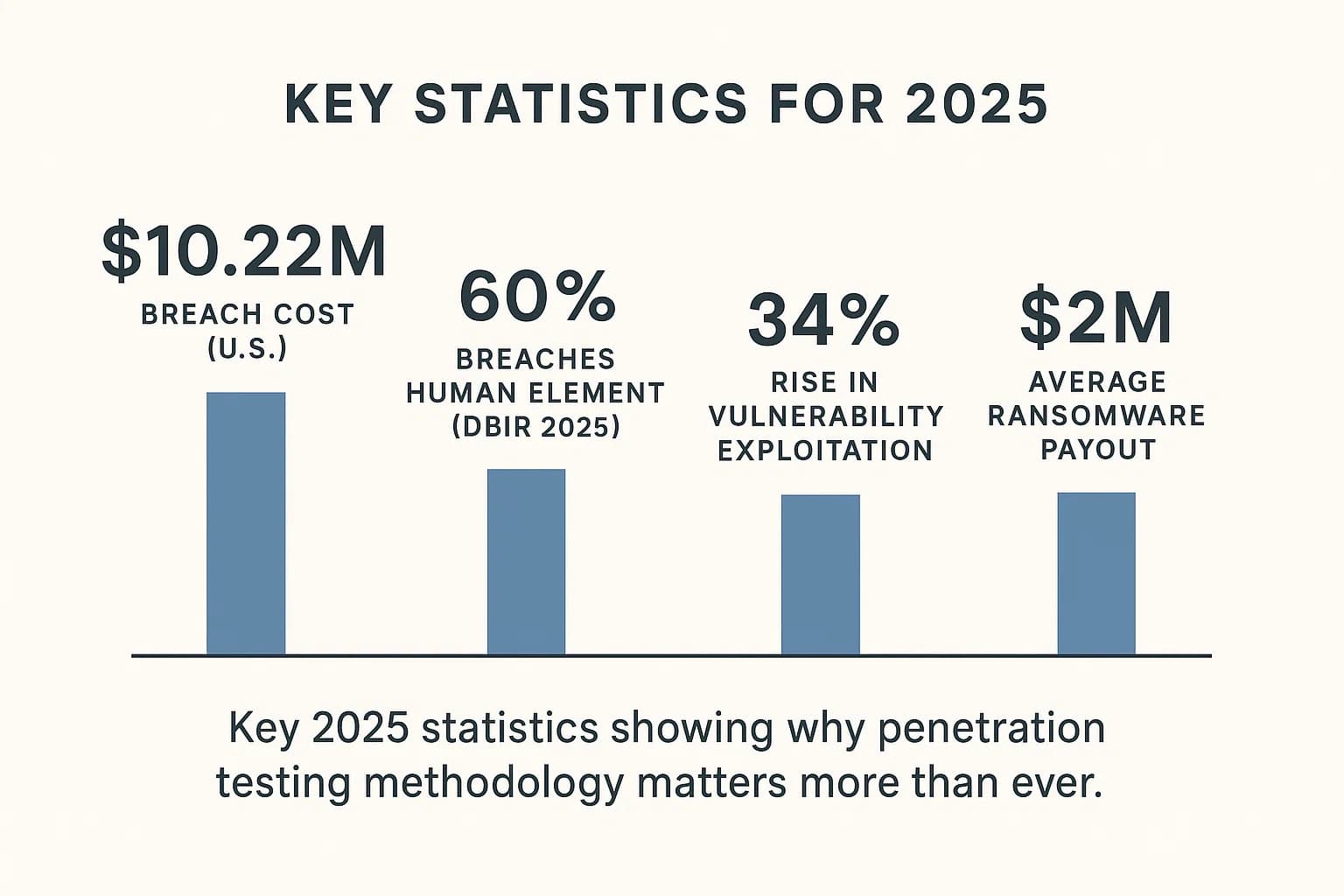
In the early days of cybersecurity, pentesting was often an unguided art form. As one source notes, "there weren't many rules and regulations guiding the work of early pen testers. Businesses didn't know what to expect, so results varied widely". That's a huge problem. In 2025, with the average cost of a data breach in the U.S. soaring to a staggering $10.22 million according to IBM's latest report , businesses can't afford inconsistency.
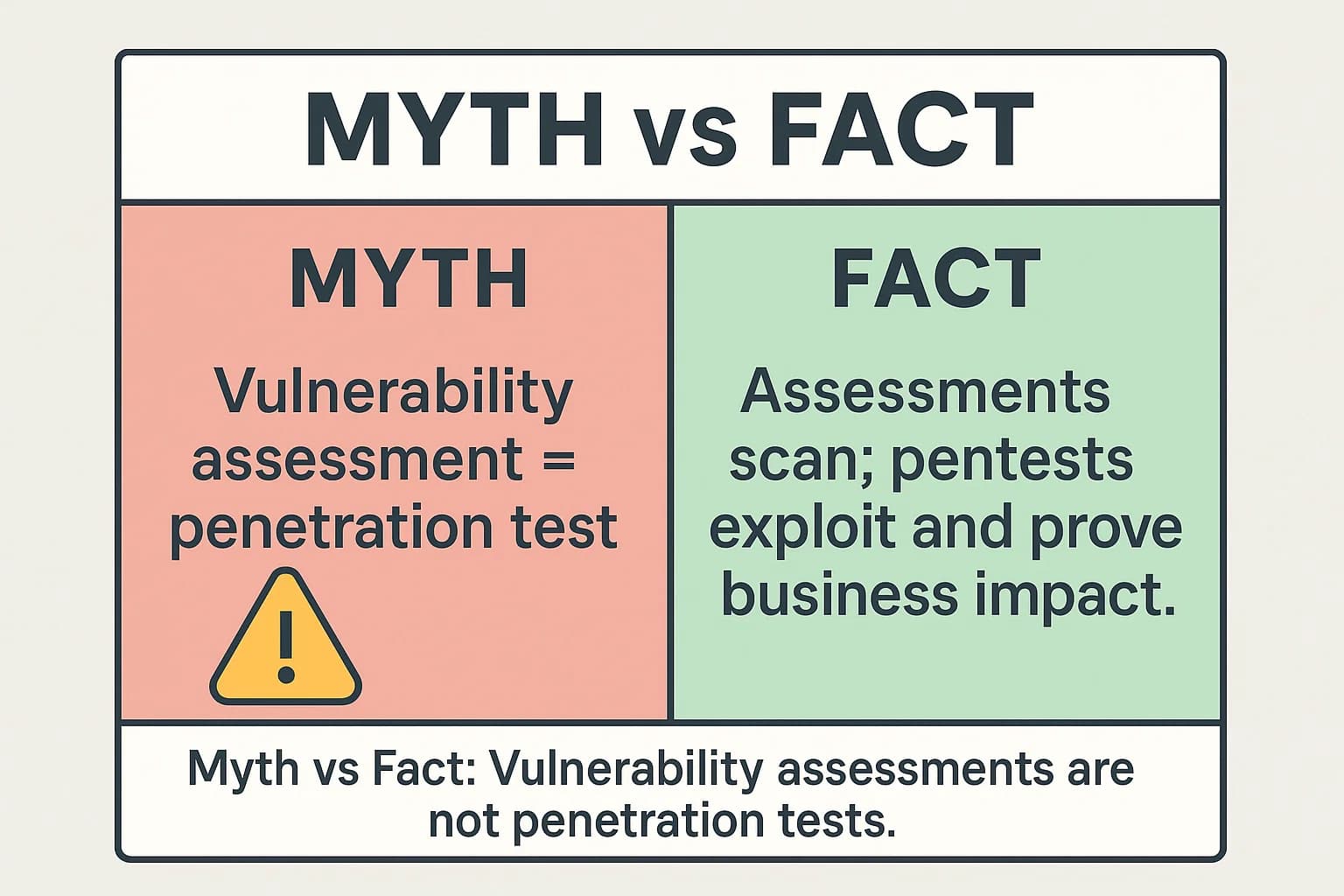
From my experience leading red team engagements, the choice of methodology is the single most important decision made before any testing begins. It dictates whether we simply find a list of CVEs or if we uncover the multi stage attack chain that could actually take down the business. It’s the core difference between a basic scan and a true security validation, a distinction we'll break down completely by exploring the difference between a vulnerability assessment and penetration testing.
The move toward formal methodologies wasn't an academic exercise; it was a direct market response to the increasing financial and reputational damage caused by data breaches. As the stakes grew, the need for auditable, repeatable, and professional security validation became a business necessity, driving the creation of standards like PTES and the adoption of government frameworks like NIST SP 800 115 to bring order and predictability to the field.
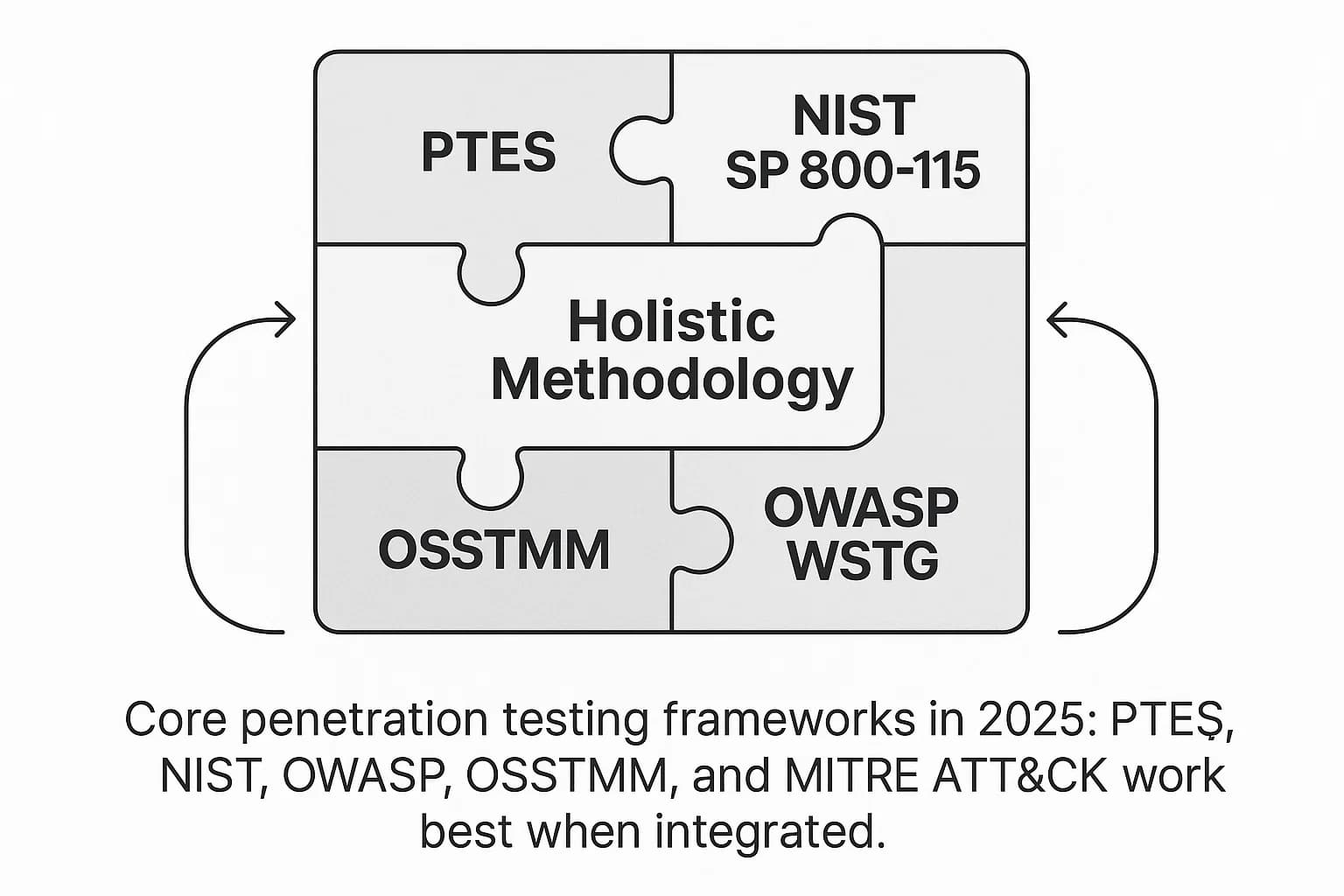
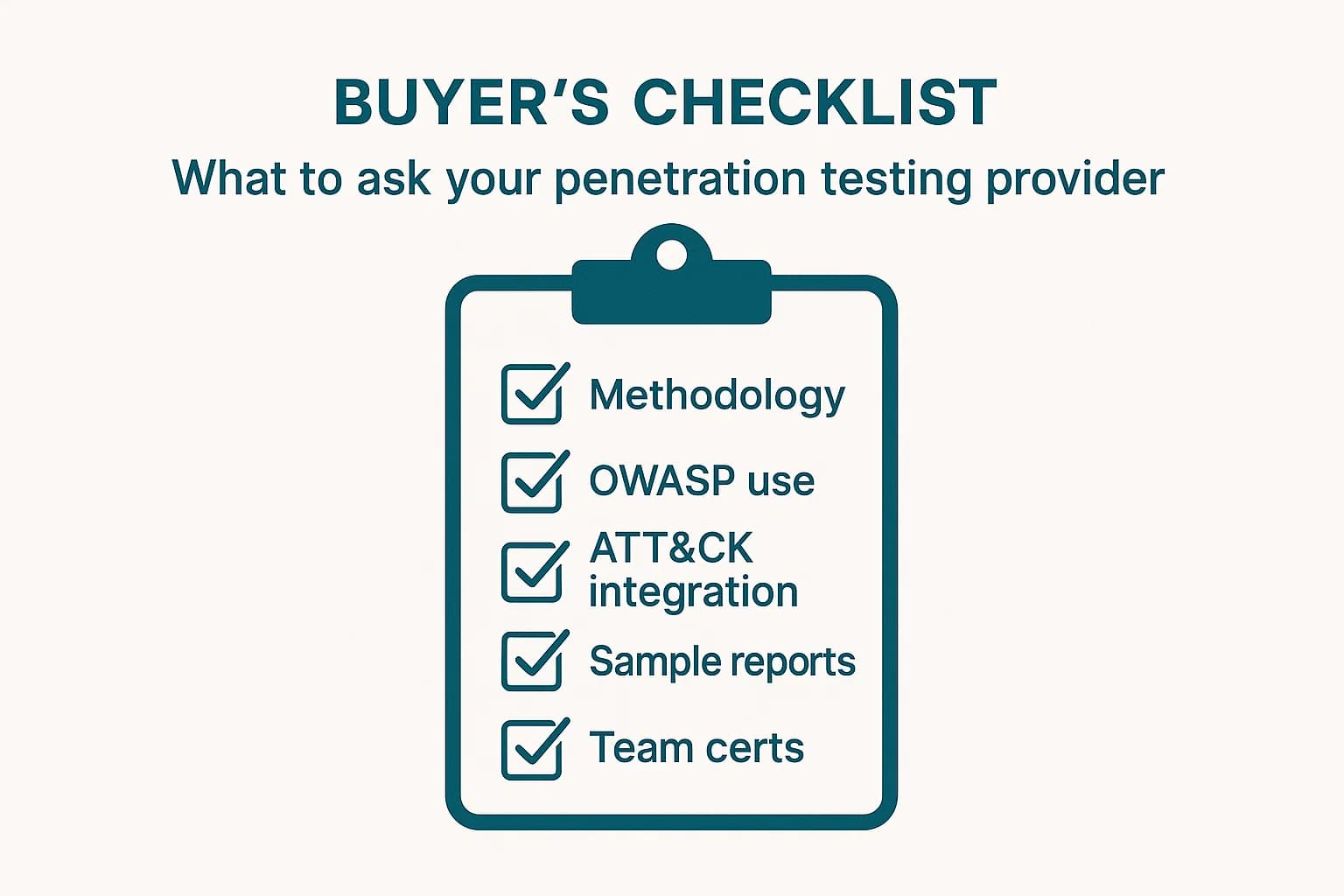
No single methodology is a silver bullet. A mature testing provider must be a "polymethodologist," blending the lifecycle management of PTES or NIST with the technical depth of OWASP and the threat intelligence of MITRE ATT&CK. Here’s how they stack up.
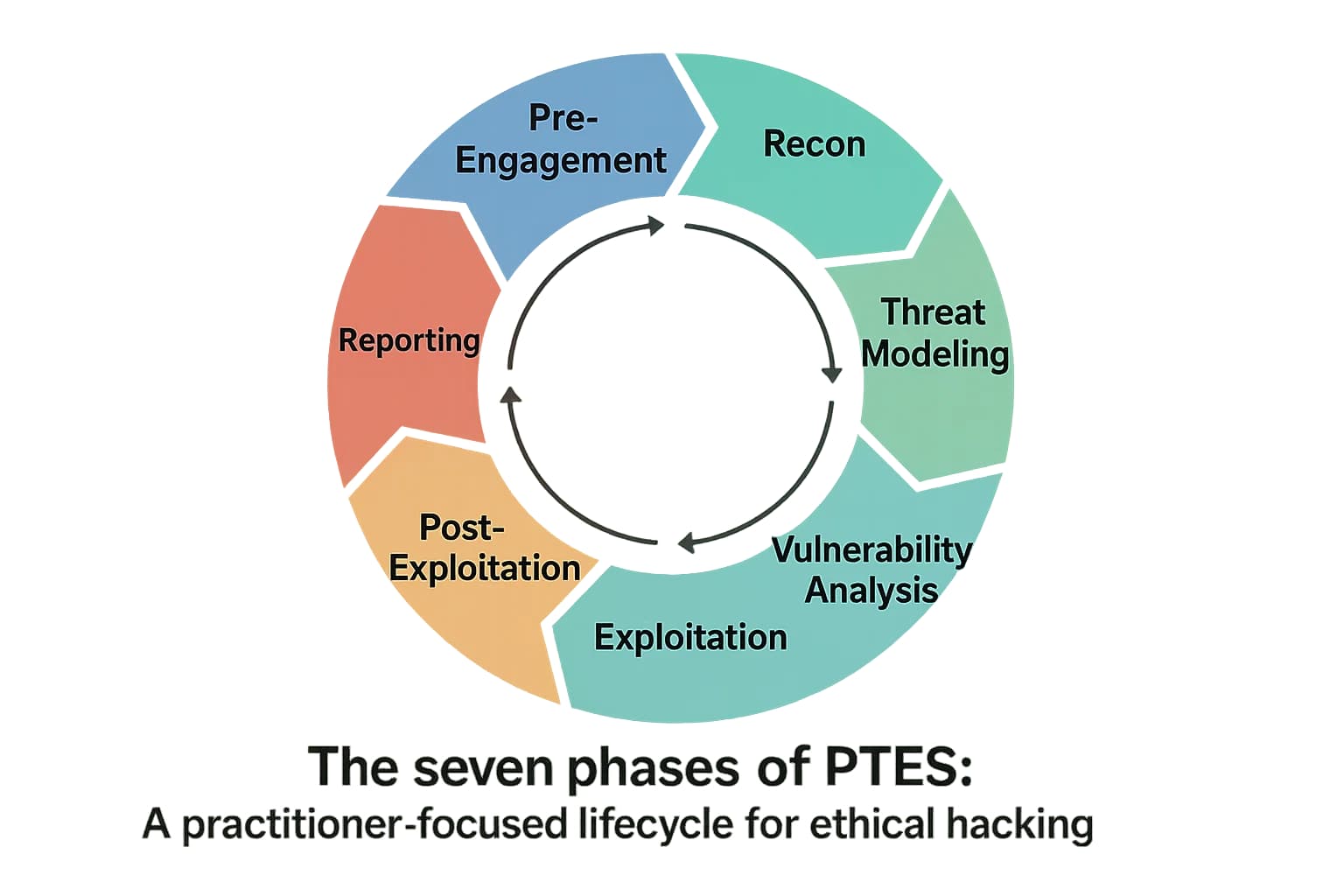
If you want to know how pentesters actually think, PTES is your guide. It was designed by and for security practitioners to provide a clear, end to end baseline for a high quality pentest. It’s less about rigid compliance and more about a practical, real world workflow that mirrors how actual attacks unfold.
Here's the deal. The PTES methodology is broken down into seven distinct phases:
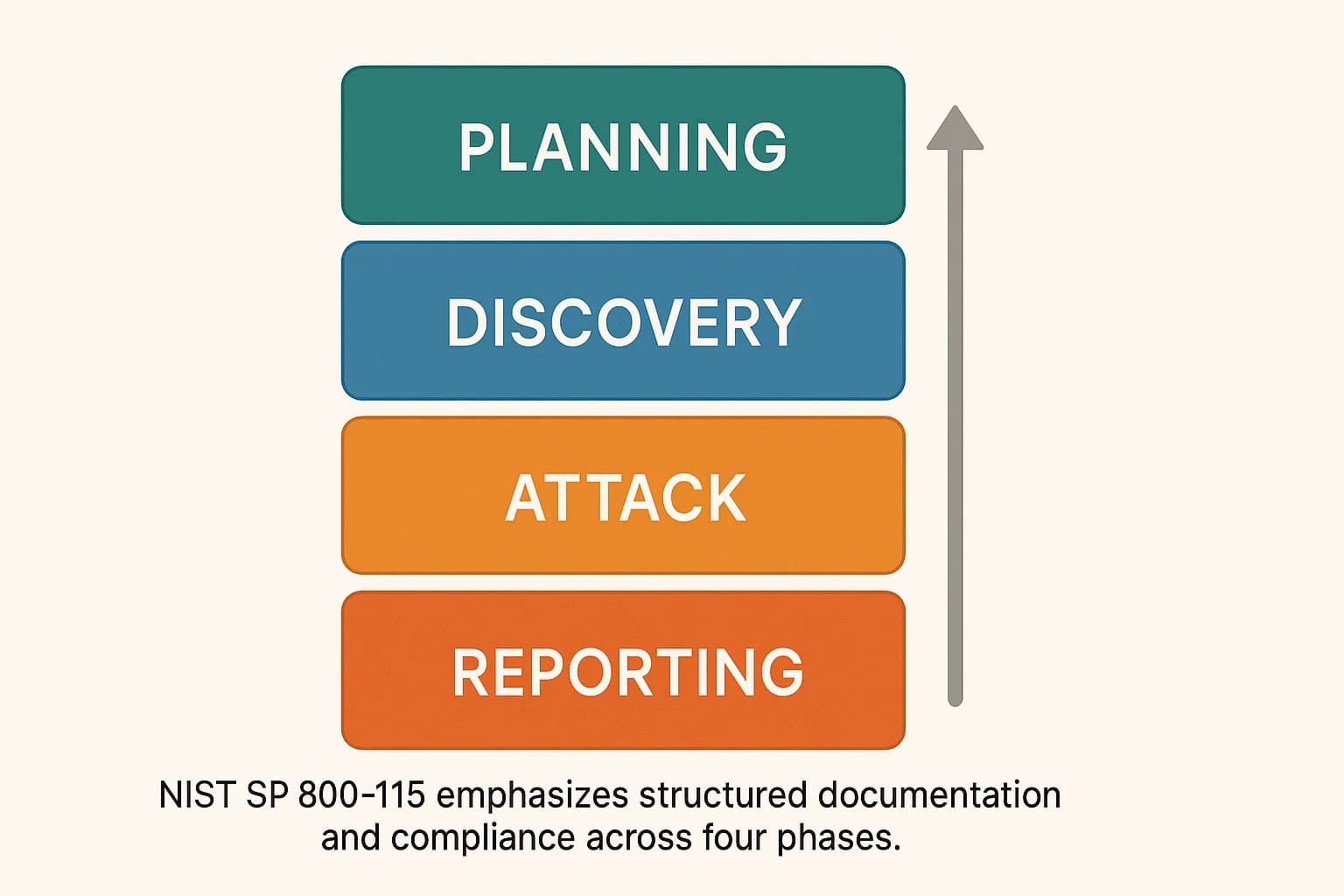
If PTES is the practitioner's field guide, think of the Technical Guide to Information Security Testing and Assessment (NIST SP 800 115) as the official, government issued manual. It’s a formal, structured methodology widely adopted by federal agencies and large enterprises that require a rock solid audit trail and comprehensive documentation of security testing activities.
We often use the NIST framework when a client's primary driver is compliance, such as for FedRAMP penetration testing explained. Its structure is also a great fit for Penetration Testing for DevOps environments.
The WSTG isn't a full lifecycle methodology. Instead, it's the definitive, open source checklist of technical security controls for any web application penetration testing services or API assessment, OWASP Web Security Testing Guide (WSTG).
During the "Vulnerability Analysis" and "Exploitation" phases, my team uses the WSTG as our technical guide. If we're testing for Broken Access Control (OWASP Top 10 A01:2021), we follow the specific test cases outlined in the WSTG. As threats evolve, so does OWASP, with new projects like the OWASP Top 10 for Large Language Models, which tackles emerging AI cybersecurity threats in 2025.
The Open Source Security Testing Methodology Manual (OSSTMM) from ISECOM focuses on measuring operational security as a whole, going far beyond just digital assets.
OSSTMM structures its testing across five "channels": Human Security, Physical Security, Wireless Communications, Telecommunications, and Data Networks.
The MITRE ATT&CK framework is not a testing methodology itself. It's a globally accessible knowledge base of adversary tactics, techniques, and procedures (TTPs) based on real world observations.
We use ATT&CK to make our tests more realistic. Instead of random exploits, we emulate the exact TTPs used by threat actors who target our client's industry, such as specific lateral movement techniques (T1021). This is fundamental to a true red team vs blue team explained engagement.
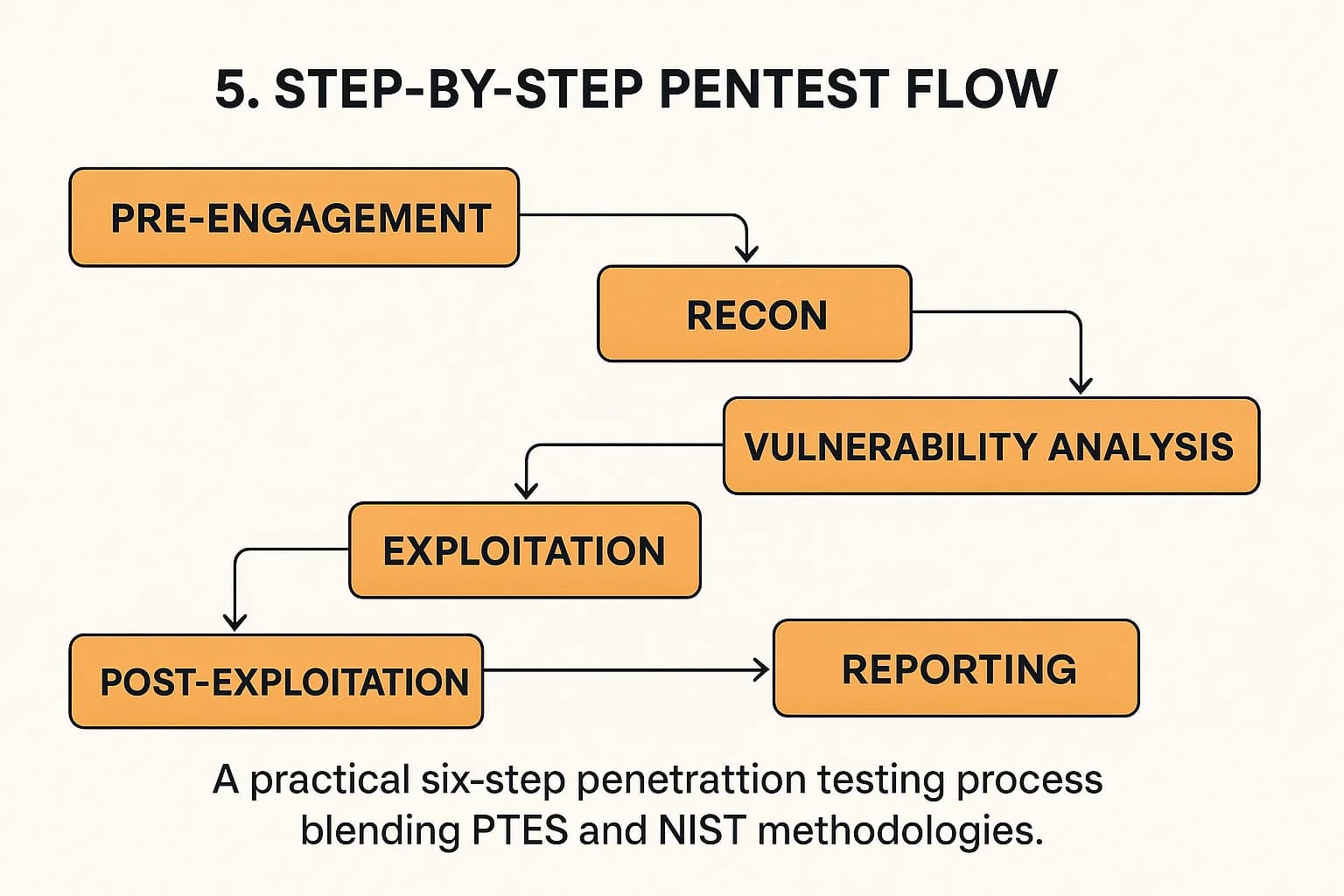
Here’s a practical, step by step look at how a typical engagement works, combining the best of PTES and NIST.
This is the most critical phase. The goal is to define exactly what will be tested, when, and how, and to get explicit, written permission. We craft the Rules of Engagement (RoE), a document that outlines testing windows, emergency contacts, and what actions are permissible.
The goal here is to collect as much information about the target as possible from public sources. This includes:
Now, we identify specific, potential vulnerabilities.
This is where we prove that a vulnerability is exploitable. We attempt to gain an initial foothold, perhaps using the Metasploit Framework for an unpatched service or exploiting a path traversal in client-side requests.
This phase answers the critical question: "So what?". Key activities include:
The final goal is to deliver a clear, actionable report. A high quality penetration testing report includes an Executive Summary and detailed Technical Findings with remediation guidance.
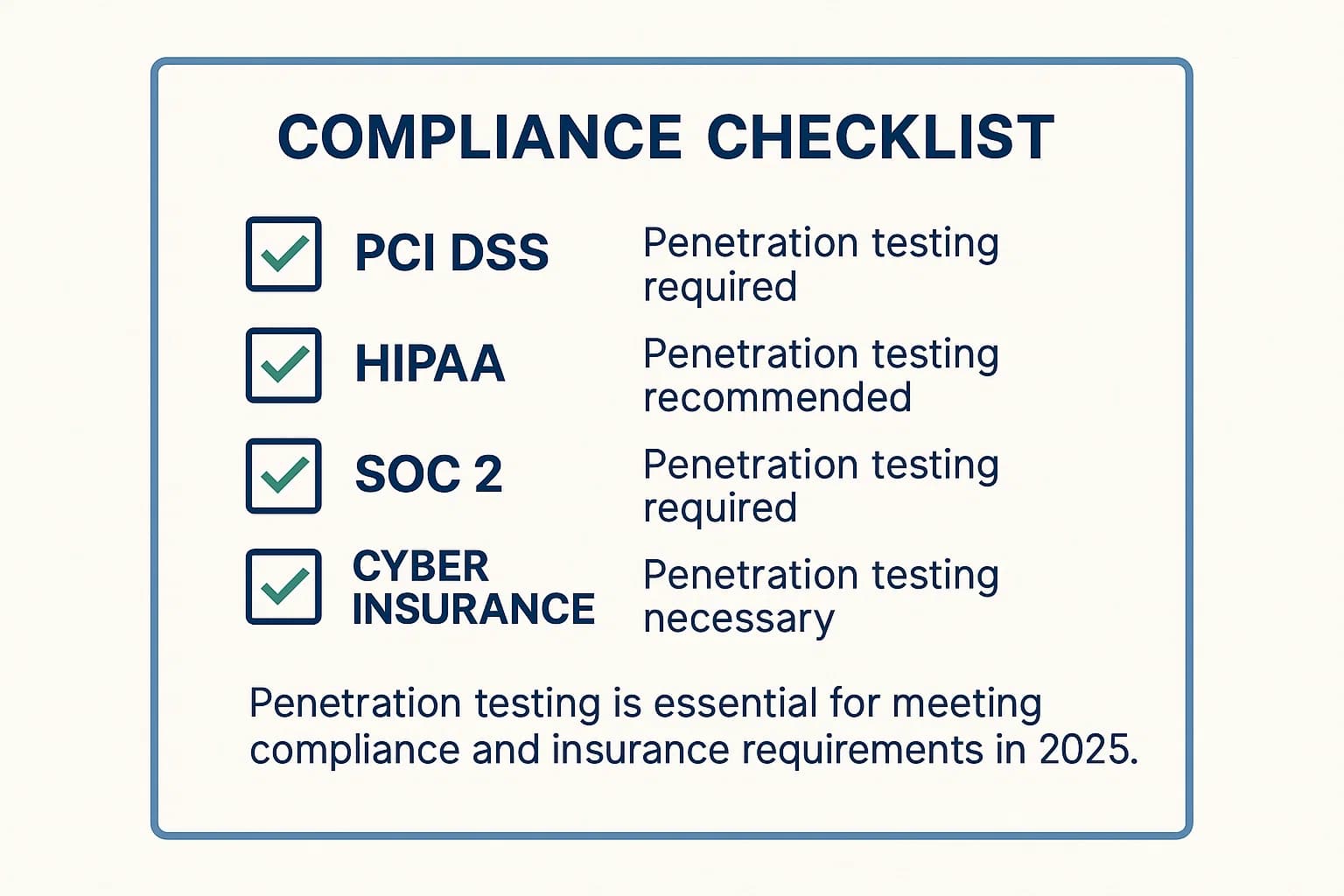
The Payment Card Industry Data Security Standard (PCI DSS) explicitly requires annual internal and external penetration testing, based on an industry accepted methodology like NIST SP 800 115. For a deep dive, see our PCI DSS 11.3 penetration testing guide 2025.
The Health Insurance Portability and Accountability Act (HIPAA) requires regular risk analysis. While it doesn't explicitly mandate penetration testing, it's strongly advised to meet the requirement for a "thorough assessment of the potential risks and vulnerabilities" to protected health information (ePHI). Our HIPAA penetration testing checklist 2025 can help.
Penetration testing has become a standard expectation forSOC 2 penetration testing requirements 2025 and a critical factor for penetration testing for cyber insurance eligibility. Insurers see regular testing as proof of due diligence and may deny coverage without it. This is especially true for penetration testing for startups and SMBs.
What are the 7 phases of penetration testing?
This refers to the Penetration Testing Execution Standard (PTES), which includes: Pre engagement Interactions, Intelligence Gathering, Threat Modeling, Vulnerability Analysis, Exploitation, Post Exploitation, and Reporting.
What is the difference between a methodology and a framework?
In this context, they are often used interchangeably. A framework (like NIST or PTES) provides the high-level structure, while the methodology is the specific application of that framework, including the tools and techniques used.
How long does a penetration test take?
For buyers comparing penetration testing services in the UK, timing depends on scope. A small web application test might take one to two weeks, while a full internal and external penetration test for a large enterprise could take a month or more.
Is penetration testing required for compliance like PCI DSS or HIPAA?
Yes, for PCI DSS (Requirement 11.3), it is explicitly required annually. For HIPAA, it is considered a crucial part of the mandatory risk analysis process.
What is the most important phase of a penetration test?
While all are critical, many practitioners agree the Post Exploitation phase delivers the most value. It demonstrates the real world business impact of a breach, moving beyond a simple technical finding.
Can I perform a penetration test myself?
While you can run tools, a true penetration test requires deep expertise and an outside perspective. Many compliance standards, like PCI DSS, require the tester to be organizationally independent. You can explore the differences in our article on manual vs automated penetration testing.
How much does a penetration test cost?
Costs vary widely based on scope, complexity, and duration. For a detailed breakdown, see our guide on penetration testing cost.
A structured, repeatable penetration testing methodology is the foundation of modern security assurance. It's what transforms security testing from a guessing game into a strategic business function. Frameworks like PTES and NIST provide the roadmap, specialized guides like OWASP WSTG provide the technical depth, and threat intelligence from MITRE ATT&CK ensures the simulation is realistic. The ultimate goal is not to produce a list of CVEs, but to uncover and demonstrate tangible business risk, allowing you to prioritize your defenses effectively against the threats of 2025.
The threats of 2025 demand more than just awareness; they require readiness. If you're looking to validate your security posture, identify hidden risks, or build a resilient defense strategy, DeepStrike is here to help. Our team of practitioners provides clear, actionable guidance to protect your business.
Explore our penetration testing services for businesses to see how we can uncover vulnerabilities before attackers do. Drop us a line, we’re always ready to dive in.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us