October 12, 2025
Updated: March 29, 2026
A practical guide to testing in-scope systems, validating control effectiveness, and strengthening trust through risk-based security assurance.
Mohammed Khalil
SOC 2 penetration testing is a targeted validation activity for systems that store, process, or protect customer data within the audit boundary. Its purpose is not merely to identify vulnerabilities, but to test whether security controls hold up under realistic attack conditions across applications, APIs, identity flows, administrative pathways, cloud infrastructure, and relevant integrations.
When scoped correctly and paired with remediation evidence, penetration testing can strengthen technical assurance, support risk discussions, and provide useful evidence for SOC 2 review. It is particularly valuable in modern SaaS and cloud environments where trust boundaries extend across user roles, APIs, third-party services, and shared infrastructure.
SOC 2 penetration testing is a structured security assessment of in-scope applications, APIs, identity pathways, privileged workflows, and supporting infrastructure to determine whether technical controls can be bypassed under realistic attack conditions.
SOC 2 penetration testing is an adversarial security assessment of the systems within the SOC 2 boundary. It is used to evaluate whether applications, APIs, identity workflows, administrative paths, and supporting infrastructure can be exploited in ways that affect customer data, service integrity, or trust commitments.
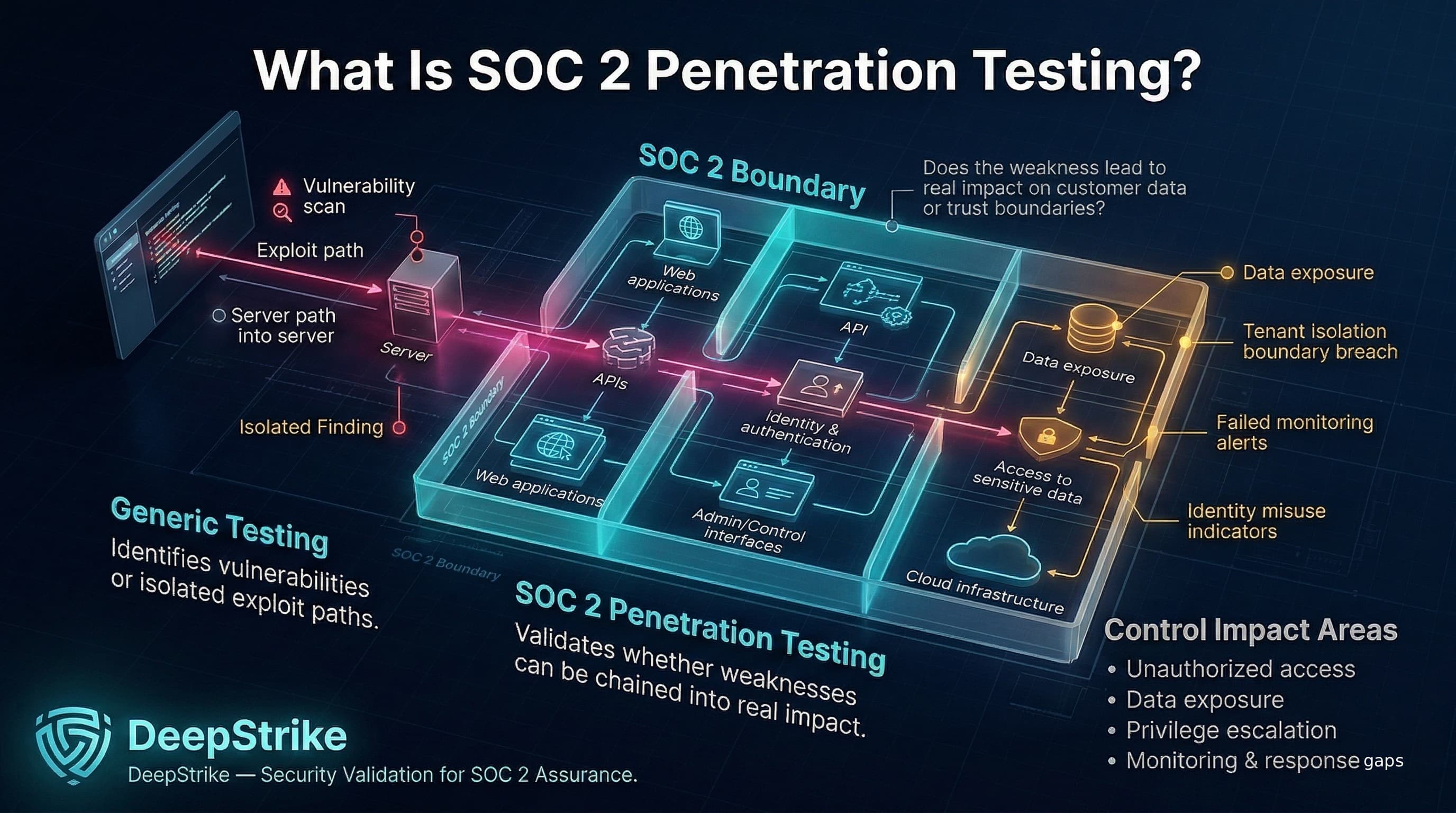
Unlike a generic pentest or an automated scan, a SOC 2-relevant test is shaped by control context. It does not stop at identifying a flaw. It asks whether a weakness can be chained into unauthorized access, data exposure, privilege escalation, breakdown of tenant isolation, or failure of monitoring and response processes.
For example, a vulnerability scan may identify an outdated component, and a generic pentest may exploit it to gain access to a server. A SOC 2-focused pentest goes one step further by determining whether that access can be used to reach customer data, bypass trust boundaries, or demonstrate weakness in relevant access, monitoring, or system operation controls. That distinction is what makes the exercise useful for assurance rather than just vulnerability discovery.
SOC 2 does not prescribe penetration testing as a universal standalone requirement. The Trust Services Criteria are outcome-based and allow organizations flexibility in how they evaluate and demonstrate control effectiveness.
That said, penetration testing is commonly used as one form of technical validation because it can help show whether relevant controls were challenged under realistic conditions. In practice, it is often considered alongside other evidence such as vulnerability management records, internal reviews, monitoring outputs, access control evidence, and remediation tracking.
Its role is often more persuasive in Type II environments because the review considers whether controls operated over time, not merely whether they were designed appropriately at a point in time. The exact importance of penetration testing still depends on system risk, exposure, auditor judgment, and the organization’s broader evidence strategy.
In a Type I report, the focus is whether controls are suitably designed at a point in time. In a Type II report, the focus expands to whether those controls operated effectively during the review period. Penetration testing can support either context, but it is often more persuasive in Type II environments because it provides technical evidence that controls were challenged in practice. It should still be evaluated alongside other assurance activities rather than treated as the only measure of effectiveness.
Penetration testing matters in a SOC 2 context because it helps validate whether technical controls perform as intended when challenged by realistic attack paths. Unlike documentation reviews or automated scans alone, a penetration test can show exploitability, control gaps, and attack chaining across applications, APIs, identity systems, cloud components, and administrative interfaces.
Its value is highest when findings are translated into concrete impact: what was reachable, what trust boundary was crossed, what data was exposed, whether monitoring detected the activity, and whether remediation closed the issue effectively. In that sense, penetration testing supports assurance not by replacing other controls, but by testing whether those controls work in practice.
| Attribute | Penetration Testing | Vulnerability Scanning | SOC 2 Readiness Review |
|---|---|---|---|
| Primary Goal | Actively exploit and validate vulnerabilities in-scope (real attack simulation) | Automatically identify known vulnerabilities and misconfigurations | Assess design and documentation of security controls against SOC 2 criteria |
| Depth of Validation | High manual, in-depth testing including chained exploits and logic flaws | Low to Moderate automated checks of known issues | Broad policy/procedure review, interviews, control walkthroughs |
| Exploitability Focus | High seeks proof of exploitation (e.g. PoCs, session hijack) | Low identifies potential flaws without confirming exploitation | None focuses on planned control activities rather than technical breaches |
| Output | Detailed findings with context, risk analysis, proof-of-concept artifacts | Lists of vulnerabilities (often with severity), configuration reports | Gap analysis and recommendations for control design/documentation |
| Assurance Relevance | High demonstrates control effectiveness under attack | Moderate shows some control failures but may lack context | High ensures controls exist and are documented (design/implementation) |
| Main Limitation | Resource-intensive; snapshot in time; can risk system disruption if not careful | False positives/negatives; no business context; only known issues | Does not validate actual control operation or system exploitability |
Most organizations benefit from all three activities, but they serve different purposes. Vulnerability scanning provides broad and repeatable coverage of known issues. Penetration testing provides deeper validation by confirming exploitability and attack-path significance. Readiness reviews help determine whether controls are documented and aligned to the intended SOC 2 scope. Used together, they provide stronger assurance than any single activity on its own.
SOC 2 pentests usually focus on all systems that process or protect customer data. Common scope areas include:
Each scope area matters because weakness in any of them can materially affect security, confidentiality, and overall assurance within the SOC 2 boundary. Effective testing ensures none of these domains are overlooked in the SOC 2 environment.
Scope should be aligned to the documented system boundary so the engagement reflects what the organization is actually asserting within its SOC 2 environment.
| Environment Type | Typical Testing Priorities | Common Scope Pitfalls | Notes |
|---|---|---|---|
| Cloud-based SaaS Platform (multi-tenant) | Tenant isolation; API auth; cloud configs; business logic flows. Test both front-end and backend (e.g. APIs) under different user roles. | Assuming cloud vendor covers all security; omitting internal APIs or customer data stores from scope. | In SaaS, shared-responsibility applies: cloud infra is inherited, but application logic must enforce data segregation. High priority on RBAC and per-tenant data checks. |
| Customer-facing Web/Mobile Services | Login/recovery flows; session management; input validation on forms/APIs; secure transport (TLS). | Only testing the GUI superficially, missing deeper API calls; ignoring mobile-specific flows (if any). | Often public, so exposure risk is high. Ensure payment flows, data upload/download features, and SSO paths are covered. |
| API-First Products | All API endpoints (even undocumented/internal); proper auth (tokens, scopes); error handling. | Overlooking headless services with no UI; failing to enumerate hidden endpoints; missing API gateway logic. | APIs may bypass typical UI-level controls. Test with tools or custom scripts to simulate real API clients, including authorization grants. |
| Internal Enterprise Systems | Network segmentation; internal ports/servers; employee-facing apps; unpatched internal tools. | Assuming internal network is safe or out-of-scope; skipping tests of intranet services or developer tools. | Often lower external risk but still handle sensitive data. Include internal admin panels, support ticket systems, and legacy interfaces. |
| Third-Party Integrations | Webhooks, third-party SSO, partner APIs; validate data sharing and token security. | Not scoping endpoints managed by partners; not verifying vendor's access controls (when allowed). | Treat integration endpoints as extensions of your system. For example, test how data flows via SSO providers or cloud proxies, since a flaw there can bypass your own controls. |
Each environment has distinct trust boundaries. In cloud/SaaS platforms, for instance, failing to properly test cloud IAM or missing a tenant-hopping scenario can completely undermine data confidentiality. In internal systems, missing a key on-prem host could leave the SOC 2 environment incomplete. The table above highlights how priorities shift: SaaS and API-centric systems demand a focus on multi-user isolation and business logic, whereas internal systems call for network segmentation and legacy app checks. Common pitfalls include missing scope alignment (e.g. not including a newly added microservice) and assuming security by design (e.g. believing that AWS configurations never change). Security and compliance teams should carefully define the SOC 2 system boundary to include all relevant assets, noting any shared responsibility with cloud providers or customers.
Below are several high-impact scenarios that often matter in SOC 2-relevant environments:
In each case, the key question is not only whether the weakness exists, but whether it can be used to cross a trust boundary, expose customer data, bypass intended restrictions, or evade operational detection.
A penetration test is more useful in a SOC 2 context when it is supported by an evidence package that is easy to review. In practice, useful materials often include:
This kind of evidence helps connect the technical engagement to operational follow-through rather than treating the test as a standalone event.
Even when organizations perform penetration testing, program quality varies significantly. Common failure patterns include:
These weaknesses do not just reduce the value of the engagement. They also make it harder for security, audit, and leadership stakeholders to understand what was tested, what was proven, and what still requires action.
A strong SOC 2-relevant pentest report should function as both a technical record and a usable assurance artifact.
Weak reports often lack this structure. Without business context or confirmed exploits, even true findings can be dismissed by auditors or executives. A complete report turns a penetration test from a one-time exercise into a governance asset by clearly demonstrating what was tested, how, and why it matters.
There is no universal SOC 2 requirement for pentest frequency, so timing should be driven by risk, system exposure, and rate of change. Many organizations align full-scope penetration testing to an annual cycle, with additional targeted testing after major architectural, application, or integration changes.
Factors influencing cadence include:
Penetration testing should be treated as one component of a broader security program rather than the only validation activity. Between formal tests, organizations should rely on practices such as vulnerability scanning, code review, change review, and monitoring. The most defensible cadence is one that reflects actual risk and operational change, not a fixed checkbox schedule.
To get the most from penetration testing in a SOC 2 context, adopt these practices:
These practices improve the quality of technical validation and make the resulting evidence more useful for remediation, governance, and assurance review.
SOC 2 penetration testing is an adversarial security assessment targeted at the systems within the SOC 2 boundary. It is used to evaluate whether applications, APIs, identity workflows, administrative paths, and supporting infrastructure can be exploited in ways that affect customer data, service integrity, or trust commitments.
SOC 2 does not mandate penetration testing in every case. However, many organizations include it as part of a broader control evaluation strategy because it can provide useful technical evidence, particularly when customer-facing systems, APIs, cloud services, or multi-tenant workflows are in scope.
Vulnerability scanning is an automated tool-based process to find known flaws (e.g. unpatched software, misconfigurations). Penetration testing is a human-driven, exploit-focused process. Scans identify potential issues but do not prove exploitability or measure business impact. Pentests attempt to actually exploit chains of vulnerabilities (for example, chaining a scanner-found flaw with a logic bug to breach data). In essence, scanning casts a wide net for possible problems, whereas pentesting conducts targeted “what-if” attacks. Both are valuable: scanning helps with continuous monitoring, and pentesting provides depth by uncovering issues scanners miss.
In-scope systems typically include any asset that processes or stores customer data within the SOC 2 boundary. Common examples are: customer-facing web and mobile applications, backend APIs, authentication services (logins, MFA, password reset), administrative consoles, support tools, and cloud infrastructure (servers, storage, networks). The pentest scope should match the SOC 2 system description. Multi-tenant environments must include checks for cross-tenant access. Often, both external (internet) and internal (behind firewall) systems are tested if they fall under SOC 2’s purview.
There is no one-size-fits-all cadence. Many organizations perform a full-scope test annually and add targeted testing after material changes. The appropriate frequency should reflect system exposure, pace of change, and the organization’s broader assurance strategy.
Yes, in the sense that it can provide useful evidence that technical controls were evaluated under realistic conditions. However, penetration testing is only one part of a broader SOC 2 program that also depends on policy, process, monitoring, change management, and remediation discipline.
A good report includes scope definition, tested assets, methodology, and (critically) evidence-based findings. Each finding should describe the vulnerability, how it was exploited, the data or controls affected, and provide proof-of-concept details (screenshots, logs, code). It should also map risks to business impact or trust criteria. A stronger report should include remediation guidance and, where available, retest results confirming whether fixes were effective. Executive-friendly summaries should clarify overall risk levels and next steps. In short, a strong report clearly answers “what did we test, what did we find, and what did we do about it” for both technical and non-technical stakeholders.
Look for experienced, credentialed testers who understand compliance context. Technical skill alone isn’t enough; they should understand SOC 2 terminology, evidence expectations, and how to translate technical findings into auditor-readable reporting. Check that they have experience testing environments like yours (e.g. cloud SaaS, APIs, multi-tenant systems). Ask for sample reports to ensure they provide detailed, practical evidence (not just generic vulnerability lists). The right provider will help you align findings with trust criteria and deliver a report that stands up to auditors. In short: choose a provider with both deep technical expertise and proven compliance knowledge.
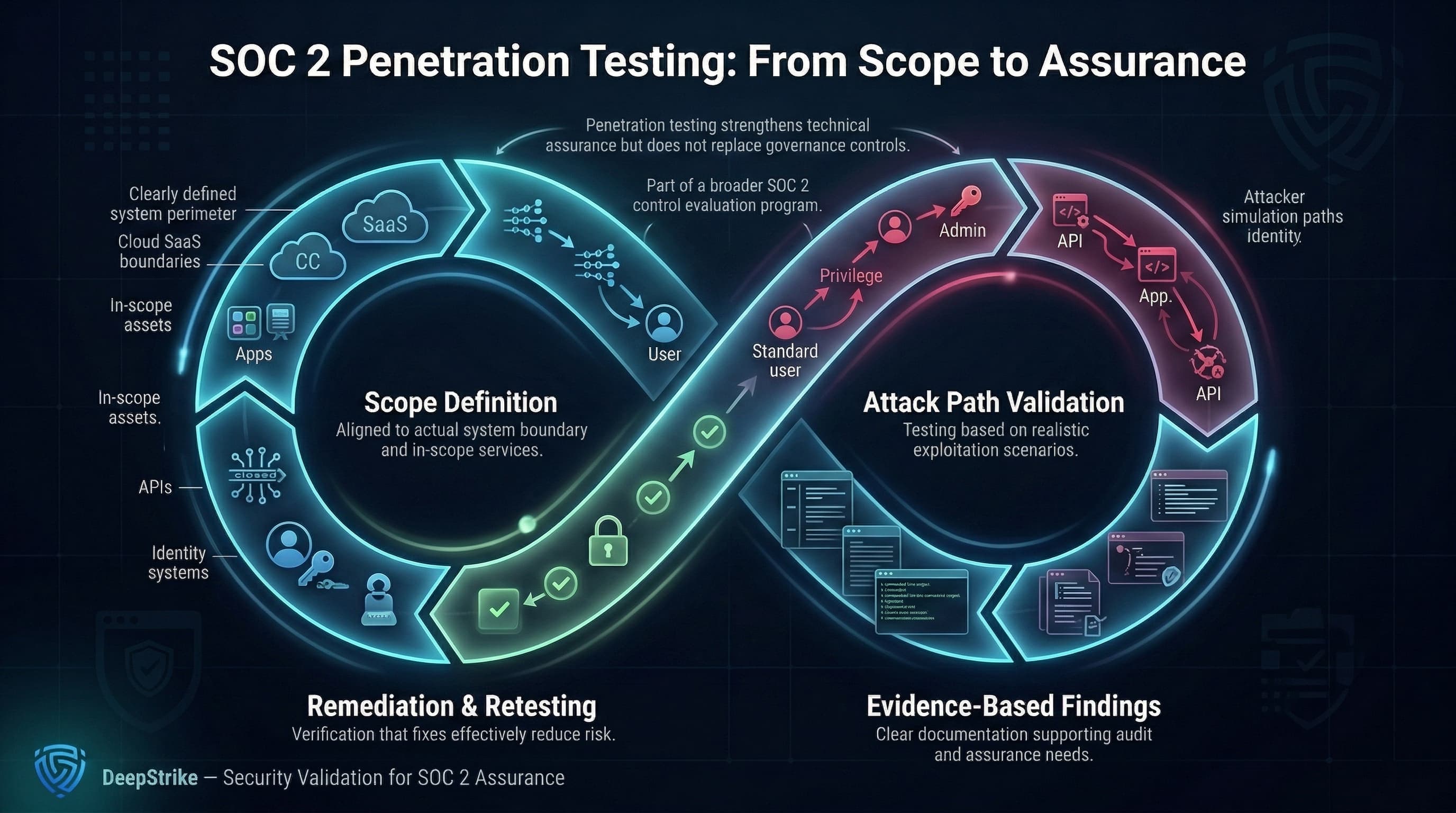
SOC 2 penetration testing is most effective when it is scoped to the actual system boundary, executed against realistic attack paths, documented with clear evidence, and followed by remediation validation. It does not replace broader security governance, but it can materially strengthen technical assurance when used as part of a disciplined control evaluation program.
The strongest programs do not treat penetration testing as a standalone checkbox. They use it to understand exploitability, validate trust boundaries, improve remediation quality, and produce evidence that is useful to engineers, leadership, and assurance reviewers alike.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us