August 25, 2025
Updated: April 19, 2026
Enterprise-grade cost breakdown, compliance pricing, and risk-based ROI modeling for 2026 security budgets.
Mohammed Khalil

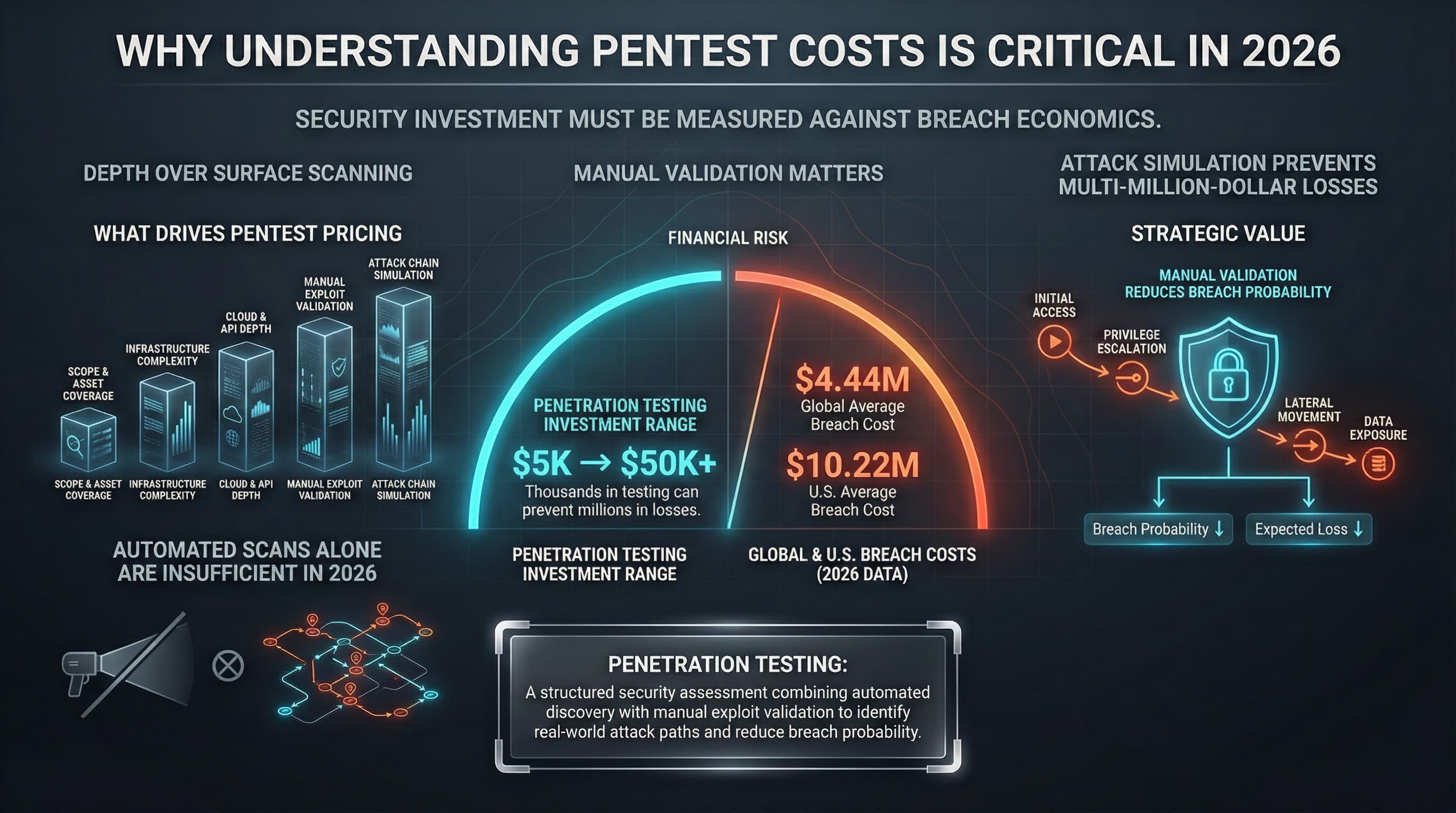
If you ask how much does a penetration test cost, you’ll get a wide range: roughly $5K for a simple test up to $50K or more for a complex one. However, the more important question is what drives that price. In today’s threat environment, the real value of a test depends on depth and breadth. Automated scans alone are insufficient in 2026; skilled experts must perform manual validation, logic checks, and attack simulations to identify exploitable vulnerabilities. In short, pentesting should be viewed as a strategic control that can prevent costly breaches. For example, IBM reports average data breach costs of $4.44M globally and $10.22M in the U.S.. Investing in robust testing (even if it costs tens of thousands of dollars) is often justified when measured against these multi‑million‑dollar losses.
Penetration testing is a structured security assessment that combines automated vulnerability discovery with manual exploit validation to identify real world attack paths and reduce breach probability.
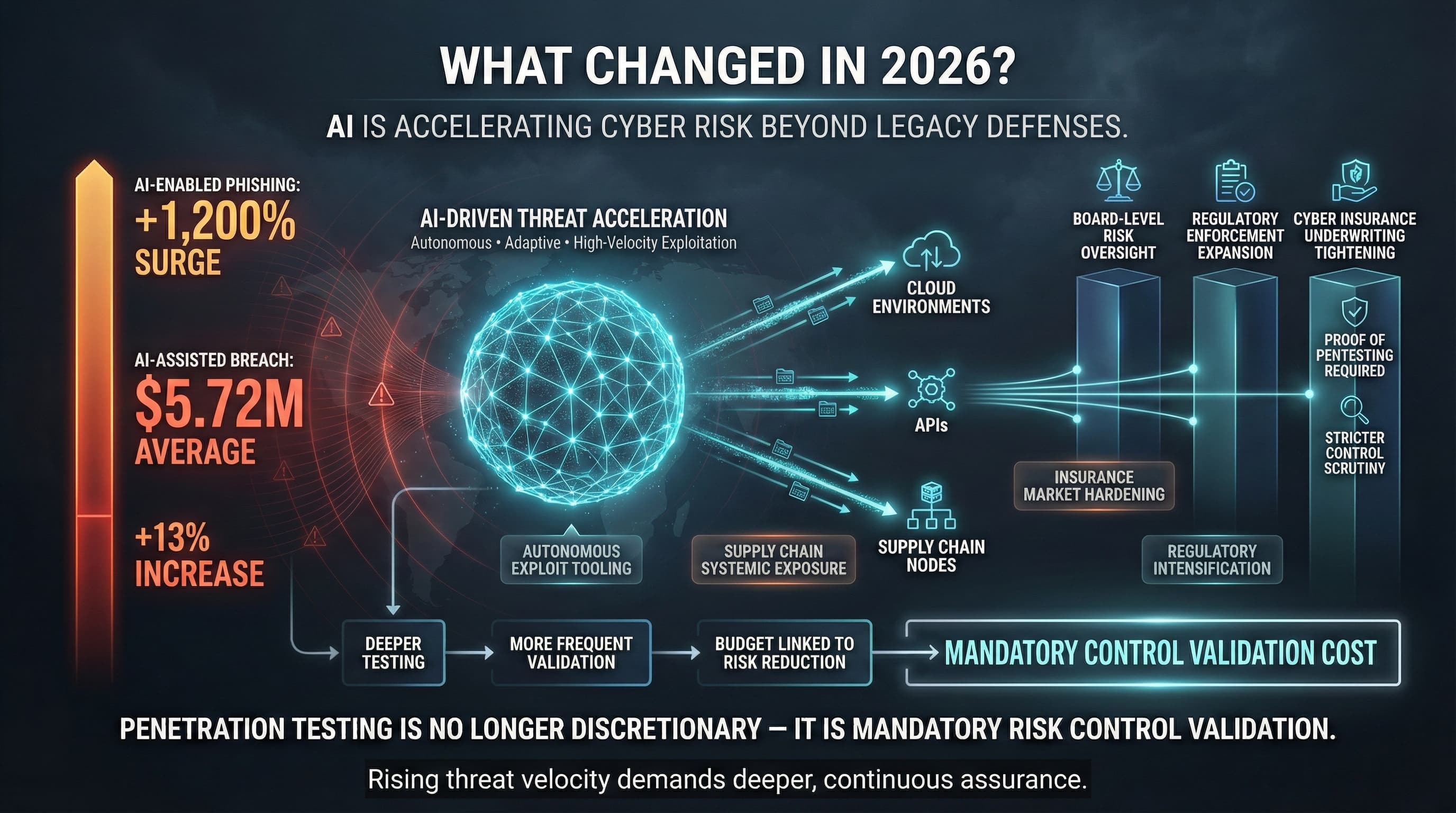
The landscape continues to evolve in 2026. Rapid advances in AI have accelerated cyber risks; attackers now deploy autonomous, adaptive tools to probe and exploit targets with unprecedented speed. For example, DeepStrike reports that AI enabled phishing attacks surged over 1,200% in 2025, and the average cost of an AI assisted breach is now higher ($5.72M on average, a 13% increase). In response, cyber risk is firmly a board level issue, as leaders recognize that AI driven threats and complex supply chain vulnerabilities can trigger systemic events.
On the risk management side, cyber insurance trends are also shifting. After years of a buyer friendly market, insurers are beginning to tighten underwriting criteria again as losses mount. Carriers now scrutinize security controls more strictly, and some require proof of rigorous pentesting to qualify for coverage. These dynamics underline why penetration testing remains a critical investment: the potential losses from a successful exploit are climbing, while insurers expect proactive controls.
Overall, the 2026 update reinforces the message that pentesting isn’t optional. AI is speeding up exploits, regulators are imposing new controls, and the cyber insurance market is less forgiving of gaps. Security teams must adapt by planning deeper, more frequent tests, and by explicitly linking test budgets to risk reduction and compliance outcomes.
As regulatory enforcement intensifies globally, penetration testing budgets are increasingly classified as mandatory control validation costs rather than discretionary security spending.
The significant variation in pentest pricing comes down to a few key factors:
The size and intricacy of your environment are the single biggest drivers of cost. More assets and complex systems require more tester time. Vendors typically quantify scope by metrics like:
There is also a complexity multiplier effect. Testing two standalone apps is one thing; testing two apps that interact multiplies the effort. The tester must examine each app plus the communication channel and potential pivot paths between them, which can create multi stage attack scenarios.
The information you provide to the tester defines the methodology and thus the effort required:
Both cost and value increase as methodology depth increases.
For example, in depth engagements might include manual exploit chaining across multiple vulnerabilities, business logic abuse detection, and specialized authentication bypass testing as part of a multi stage attack simulation. Each of these activities requires additional time from senior testers (often $200–$300+/hour) and possibly custom tools, which raises the price. Tests that include these advanced, multi stage assessments deliver deeper risk visibility, but the higher labor intensity is reflected in higher cost tiers.
Based on market benchmarks, typical price ranges by asset type are:
Web and network tests are generally at the lower end of enterprise ranges, while comprehensive mobile or multi cloud audits push higher. Exact quotes depend on the total number of apps, nodes, and their criticality.
When buying a penetration test, you are purchasing an expert’s time and creativity. Hourly rates for skilled testers typically range from $100 to $300, with experienced consultants commanding premium rates. Look for teams with respected certifications (e.g. OSCP, CISSP) and a strong track record. Senior testers can uncover complex business logic flaws and chaining issues that junior or automated tests miss. While their hourly rates are higher, their findings often deliver a much greater return on investment by preventing serious breaches.
These experts follow established methodologies from authoritative bodies like the OWASP Web Security Testing Guide and NIST SP 800 115. In procurement, you should validate that the vendor’s process includes manual validation steps (e.g. logic testing, exploitation) beyond just automated scanning.
To help with budgeting, here is an overview of typical cost ranges grouped by category:
These are illustrative ranges; actual budgets should be tailored to the organization’s size and risk profile.
Compliance driven tests typically cost more than purely technical assessments. Mandated tests become formal audit exercises with strict documentation. For example:
Beware of compliance checkbox tests. A narrowly scoped, cheap test may satisfy auditors but leave you vulnerable to real attacks outside the compliance framework.
Larger, more complex organizations need more extensive testing programs. Here are common annual security testing budgets by size:
As your organization grows, you should shift from one off tests to a programmatic approach where continuous or periodic testing is integrated into the security lifecycle.
The location and reputation of your provider also matter:
In summary, don’t assume cheaper always means bad or good. Focus on proven methodology, references, and the scope of work.
How you procure testing can also affect cost:
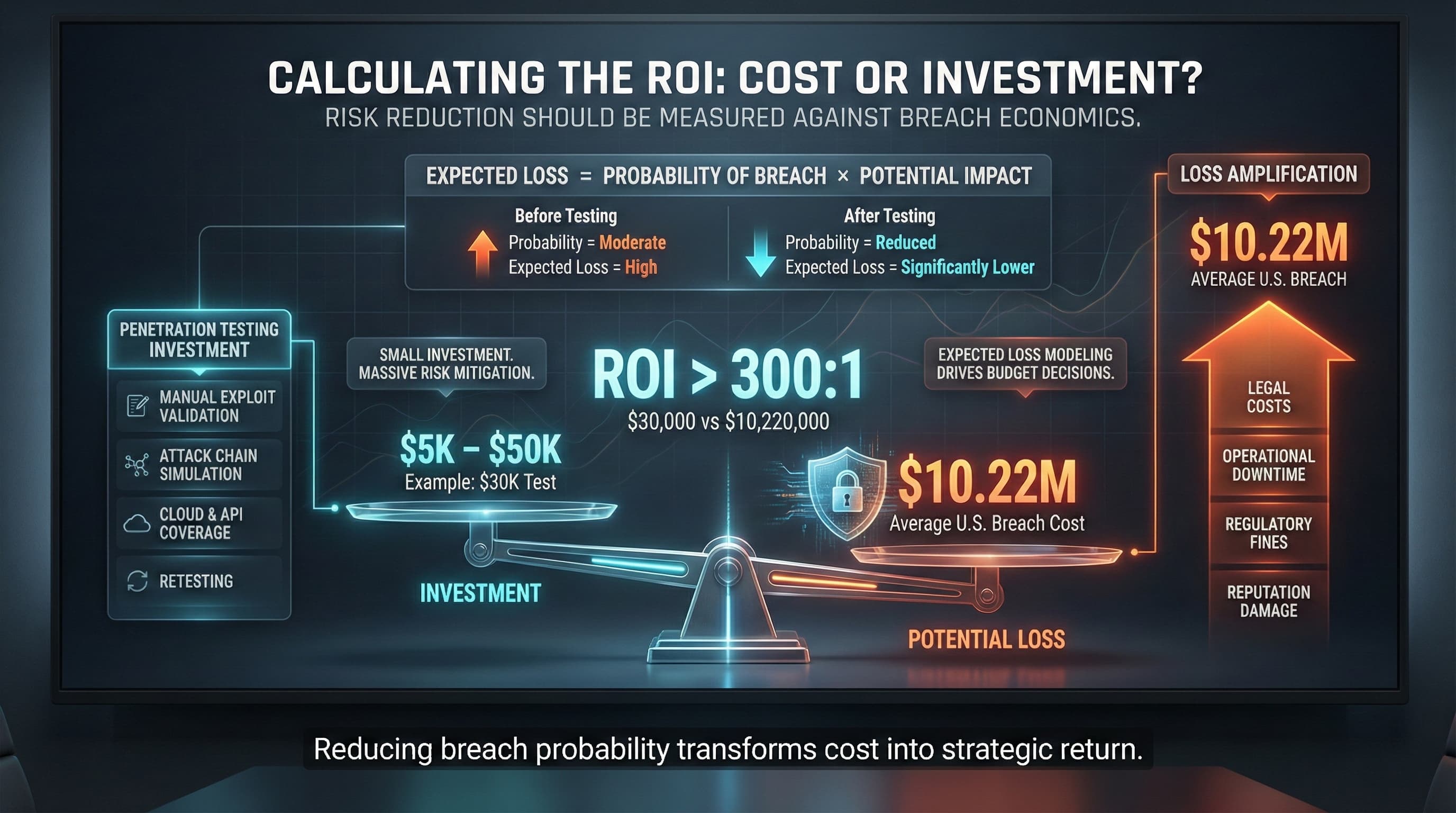
Frame pentest cost as an investment in risk reduction. IBM’s data makes the case: the average U.S. breach now costs about $10.22M, compared to a test that typically costs $5K–$50K. For example, a $30K test that prevents one breach yields an ROI over 300:1 (30,000 vs 10,220,000).
A more structured way to quantify this is enterprise risk modeling. The fundamental formula is:
Expected Loss = Probability of Breach × Potential Impact.
By reducing the probability of a breach, even a modest investment can dramatically lower expected losses.
Expected Loss = Probability of Breach × Breach Impact.
The table below shows an illustrative example comparing scenarios: The following model assumes a constant breach impact to isolate the financial effect of probability reduction.
| Scenario | Annual Breach Probability | Breach Impact | Expected Annual Loss |
|---|---|---|---|
| No Testing | 20% | $4,000,000 | $800,000 |
| Annual PenTest | 5% | $4,000,000 | $200,000 |
| Continuous Validation | 2% | $4,000,000 | $80,000 |
Illustrative Example: Even this simple model shows that reducing breach probability (from 20% to 5% or 2%) cuts expected losses by hundreds of thousands of dollars. (In this example, continuous testing reduces expected loss from $800K to $80K.) By continuously testing and fixing vulnerabilities, you drive down the probability P, which in turn dramatically lowers the annualized risk. Over multiple years, those savings compound. For instance, dropping annual breach chance from 20% to 5% not only saves $600K this year, but also means far fewer breaches over time.
Instead of focusing solely on the 340:1 ROI number, enterprise leaders should emphasize risk reduction and quantified loss avoidance when justifying budgets.
Remember, the vendor’s invoice is only part of the total. Budget also for:
In planning, add about 20% extra budget (or more) for these internal and follow up costs beyond the vendor quote.
To obtain comparable quotes, provide vendors with a clear, detailed scope. Use our Pentest Cost Estimator Checklist to gather essential info. Key steps include:
A well scoped RFP reduces guesswork and ensures all bidders quote on the same basis.
Penetration test pricing typically ranges from about $5,000 to $50,000, depending on the scope and complexity. The lower end covers small, straightforward tests; more complex tests (multiple apps, networks, or specialized environments) go toward the higher end.
Engaging an external firm generally falls in the same $5K–$50K+ range. These prices assume hiring an experienced third party consultant or service, which is standard practice for unbiased security assessments.
UK penetration testing services are often billed by day. Typical daily rates are around £800–£1,500. The final project cost equals the daily rate multiplied by the number of days needed (based on scope). A complex engagement can run into the tens of thousands of pounds.
Very low priced offerings (e.g. under $4K) usually aren’t full pentests. They are often just automated vulnerability scans with little or no manual validation. Such quick scans will miss many issues that a true pentest would catch. Always verify that a low quote includes comprehensive manual testing.
Becoming a certified pentester requires training and exams. For example, the Certified Ethical Hacker (CEH) certification currently costs on the order of $1,700–$2,000 in exam and training fees. Other certifications (OSCP, CISSP, etc.) have their own costs (usually in the $500–$1,000 range plus training).
An external network test (internet facing infrastructure) typically costs $5,000–$20,000, depending on size and complexity. An internal network test (testing from inside the firewall) is more involved (credential based access, more machines, segmentation), often running $7,000–$40,000. The internal test’s higher end accounts for larger environments and additional authentication focused testing.
Yes. When you compare pentest cost to breach cost, the investment becomes clear. The average U.S. breach now costs around $10 million. A $10K–$50K test that prevents even one breach provides a huge return on investment in terms of losses avoided. Pentesting is a proactive risk management expense, often paid back many times over by preventing high cost incidents.
In short, penetration testing should be viewed as a financial and strategic decision at the board or CISO level, not just an IT expense line item.
Ready to Strengthen Your Defenses? The threats of 2026 demand more than just awareness; they require readiness. If you're looking to validate your security posture, identify hidden risks, or build a resilient defense strategy, DeepStrike is here to help. Our team of practitioners provides clear, actionable guidance to protect your business. Explore our Penetration Testing Services to see how we can uncover vulnerabilities before attackers do. Drop us a line, we’re always ready to dive in.
About the Author: Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.
Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us