November 18, 2025
Updated: February 23, 2026
Compare the best VAPT (Voluntary Product Accessibility Template) service providers in 2026 from DeepStrike’s security-grade audits to enterprise giants like Deque and Level Access.
Mohammed Khalil

In today’s cyber risk landscape, a single breach can cost an enterprise millions. For example, the IBM 2025 Cost of a Data Breach Report found the global average breach cost around $4.4 million. Rising adoption of AI and cloud services is expanding the attack surface, giving adversaries new vectors. Meanwhile, regulatory pressures GDPR, PCI DSS, ISO 27001, SOC 2 and others are mandating regular security assessments and imposing hefty fines for noncompliance. In healthcare, proposed 2025 HIPAA rules alone could drive $4.65 billion in new annual pentesting costs across the sector. The VAPT market is mature and growing: valued at about $3.4 billion in 2024 and projected at $12.35 billion by 2032. These trends mean that VAPT (the combination of vulnerability scanning and penetration testing) is a strategic necessity, not optional. This ranking of Top VAPT Service Providers is based on an explicit methodology (see below) and is not sponsored. It highlights leading vendors by technical depth, automation vs manual testing balance, compliance support, and domain fit, so buyers can confidently shortlist candidates by objective criteria.
VAPT (Vulnerability Assessment and Penetration Testing) is a structured security validation methodology that combines automated vulnerability discovery with manual exploit validation to identify real world attack paths and reduce breach probability.
We used a procurement style evaluation framework, scoring vendors on multiple technical and business criteria:
This framework allowed objective scoring across providers. Each vendor’s section below highlights how they performed on these criteria, with Best For tags signaling their target market or specialties.
Selecting a VAPT vendor involves key trade offs and common pitfalls. First, beware scan only providers that promise fast turnarounds but skip manual validation. A checklist driven scan may find obvious flaws but miss real world attack chains. Instead, look for ethical hackers willing to exploit chained vulnerabilities. Avoid under scoping: clearly define all in scope assets and test depth (e.g. do not just test a network perimeter scan without in depth web/mobile analysis).
Other mistakes include excluding retesting. If a test identifies fixable issues, a robust provider will verify patches without extra cost. Neglecting this means you may still harbor remediated vulnerabilities. Also beware junior only teams. Some large consultancies rotate inexperienced staff through tests. Check if the vendor guarantees senior or CREST accredited testers. A small specialized firm often places certified experts (OSCP, OSWE) on every engagement, while a big firm might assign junior analysts.
Ensure the provider’s compliance focus matches your needs. Testing for certification requirements (ISO 27001, PCI DSS, etc.) is different from testing for actual security posture. Some firms speak ISO language (offering checkbox reports) rather than demonstrating attacker techniques. A good provider balances compliance and realistic exploits.
Finally, align on delivery and scope: clarify reporting format, retesting, and any integration with development workflows. Look for transparent methodology (we recommend reviewing sample reports or dashboards). In sum, verify the people and process, not just the brand. A selective shortlist driven by expertise and methodology, not marketing hype, will yield a more reliable partner. For more on related topics, see our guides on penetration testing vs vulnerability scanning, VAPT service cost analysis, and compliance readiness planning.
Headquarters: Los Angeles, USA
Founded: 2016
Company Size: ~50 employees (principal consultants)
Primary Services: Penetration Testing (cloud, API, web, mobile), Red Teaming, Continuous/DevSecOps Testing
Industries Served: Financial Services, Healthcare, Technology, E Commerce, Fintech, SaaS
Why They Stand Out: DeepStrike is a boutique offensive security firm noted for deep manual testing across cloud and microservices. They exclusively staff senior, certified experts (OSCP, OSWE) on engagements. The team has produced notable research and open source tools, evidencing their technical leadership. Clients praise their agile, customer friendly approach and actionable reporting. The company’s focus on continuous testing aligns with DevSecOps, and their reports emphasize prioritized remediation guidance.
Manual vs Automated Depth Analysis: DeepStrike is committed to manual penetration testing. They eschew assembly line automated scans in favor of real attacker simulations. Testers manually verify and chain vulnerabilities to demonstrate full attack paths (e.g. exploiting an API through pivoting). Automation is used only to support testers; the core of the work is human led exploitation. This maximizes exploit chaining accuracy and realistic threat emulation.
Key Strengths:
Potential Limitations:
Best For: Cloud and API first enterprises, fintech and SaaS companies, or any organization seeking deep, expert led testing and detailed remediation guidance.
Headquarters: New York City, USA
Founded: 2006 (LLC formed 2008)
Company Size: ~200 (global, includes training business)
Primary Services: Advanced Penetration Testing, Red Teaming, Threat led Attack Simulations, Security Training & Certification (OSCP, etc.)
Industries Served: Government, Financial Services, Healthcare, Manufacturing, Technology
Why They Stand Out: OffSec, creator of Kali Linux and the OSCP certification, fields one of the most elite pentest teams worldwide. They accept only a small client roster each year (about 10), ensuring top tier focus. All assessments are performed by the same experts who develop widely used tools and training content. Their approach is highly customized and advanced attack simulation, targeting very hardened environments with novel exploits. Customers benefit from unparalleled expertise and complete engagement alignment (OffSec works with clients one at a time).
Manual vs Automated Depth Analysis: OffSec’s services are primarily manual. They explicitly avoid routine scanning and checklists. Tests are led by experts behind Kali Linux and ExploitDB, meaning human driven discovery is core. Automated tools (e.g. meta sploit) may assist, but OffSec prides itself on manual exploit development and in depth analysis for highly secure networks.
Key Strengths:
Potential Limitations:
Best For: Large organizations (government, critical infrastructure, Fortune enterprises) with the most stringent security requirements, wanting leading edge adversary emulation by a world class team.
Headquarters: Manchester, United Kingdom
Founded: 1999
Company Size: ~2,140 employees (2025)
Primary Services: Cybersecurity Consulting, Penetration Testing, Managed Security Services, Software Escrow, Code Review, Incident Response.
Industries Served: Worldwide (15,000+ clients) including Finance, Tech, Government, Telecom, Healthcare
Why They Stand Out: NCC Group is a global cybersecurity firm with deep roots in compliance and assurance. They offer a full suite of security services beyond VAPT, from managed detection to software escrow. As a FTSE 250 company, NCC has the scale to handle very large engagements. They have longstanding CREST accreditation and a strong presence in regulatory heavy sectors. Buyers note NCC’s extensive compliance expertise (PCI, ISO 27001, FedRAMP) and broad security consulting background.
Manual vs Automated Depth Analysis: NCC uses a hybrid model. For large scale corporate clients, they deploy automated scanning tools to ensure coverage, complemented by manual validation by consultants. With 2,000+ employees, the tester skill levels can vary. Senior testers handle critical findings, but lower grade scanning or tool output sometimes form the first pass. Overall, they balance automation efficiency with manual steps for prioritized issues.
Key Strengths:
Potential Limitations:
Best For: Large enterprises and regulated organizations (finance, insurance, government) needing a full service provider that covers both technical testing and compliance consulting.

Headquarters: New York, USA (global network)
Founded: 1845
Company Size: ~345,000 employees (Deloitte global, 2024)
Primary Services: Audit, Consulting & Advisory, Cyber Risk Services (including VAPT, Red Teaming, SOC implementation, Incident Response)
Industries Served: All major industries worldwide (Financial Services, Healthcare, Tech, Energy, Government, etc.)
Why They Stand Out: Deloitte Cyber is a global brand with one of the largest security practices. They integrate vulnerability assessments into broader risk management, often combining governance, compliance, and technical security consulting. Their threat led penetration testing (TLPT) frameworks and industry specific playbooks cater to enterprise use cases. Deloitte’s huge bench of consultants and global footprint allow them to support very large, dispersed projects and leverage cross practice expertise (e.g. linkages with audit and legal). The firm also invests in cutting edge methods like adversary emulation in alignment with regulations (e.g. EU DORA).
Manual vs Automated Depth Analysis: Deloitte typically employs a hybrid approach. Given the scale, they use automated scanning tools extensively to cover infrastructure and applications, then apply manual techniques on prioritized vulnerabilities. However, buyer feedback often notes that test teams can include junior members handling routine scans, while senior experts focus on complex issues. Deloitte emphasizes process adherence and certifications, which can mean less informal creativity but more consistent methodology.
Key Strengths:
Potential Limitations:
Best For: Very large, multinational enterprises and financial institutions that require an integrated risk based approach and extensive audit/compliance support alongside testing.
Headquarters: Reston, Virginia, USA
Founded: 2004
Company Size: ~2,300 employees (2021)
Primary Services: Incident Response, Threat Intelligence, Red Teaming, Adversary Emulation, Vulnerability Assessments (VAPT), M&A Security, Managed Detection & Response.
Industries Served: Fortune 100 corporations, Governments, Defense, Finance, Energy, Technology
Why They Stand Out: Mandiant is legendary for incident response and threat intel. Its team pioneered the first public attribution of APT attacks and maintains one of the world’s largest threat research groups. As of 2022, Mandiant is part of Google Cloud, combining its massive threat dataset with Google’s resources. They offer adversary emulation exercises modeled on advanced persistent threats, making them ideal for organizations with top level security maturity. Mandiant’s M Trends reports and community trust add to its reputation.
Manual vs Automated Depth Analysis: Mandiant’s testing is manual and intelligence driven. They emphasize human analysts replicating real adversary tactics (e.g. nation state APT tools). Vulnerability scanning is secondary to detailed red teaming. Their approach is essentially a premium red team underpinned by threat intel. Mandiant also offers automated capabilities via the Google Cloud platform, but the consulting engagements themselves rely on hands-on expertise.
Key Strengths:
Potential Limitations:
Best For: Global Fortune 100 enterprises, government agencies and technology companies needing top tier adversary emulation and incident response expertise.
Headquarters: Tempe, Arizona, USA
Founded: 2005
Company Size: ~300 employees
Primary Services: Continuous Penetration Testing, Red Teaming, Attack Surface Management, Cloud & Application Security, Product Security, Mobile Security, Physical Security.
Industries Served: Fortune 100 Tech, Finance, Healthcare, Retail, Automotive, and more (global client base)
Why They Stand Out: Bishop Fox is a leading authority in offensive security. They pioneered continuous pentesting programs, where tests are part of a subscription rather than one offs. The firm has published numerous open source tools and research, reinforcing technical credibility. Bishop Fox’s clients include a significant portion of top tech and enterprise companies, and they emphasize a forward defense mindset. They blend deep hands-on testing with developer collaboration.
Manual vs Automated Depth Analysis: Bishop Fox employs a hybrid approach. They offer managed pen testing pods that combine periodic manual assessments with continuous automated scanning to catch new findings. Their strength lies in manual, expert testing of web, mobile, APIs, and cloud. Tools assist efficiency (especially in continuous mode), but skilled consultants lead major tests.
Key Strengths:
Potential Limitations:
Best For: Growth and enterprise tech companies (especially cloud native/SaaS businesses) that want ongoing, aggressive testing to integrate security into development lifecycles.
Headquarters: San Francisco, California, USA
Founded: 2013
Company Size: ~500 employees
Primary Services: Pentest as a Service (PTaaS), Application & API Security Testing, Vulnerability Management, Continuous Testing, Mobile App Assessment.
Industries Served: Thousands of customers across finance, tech, retail, health, and more (multinational reach)
Why They Stand Out: Cobalt is a pioneer in pentesting as a service. Their SaaS platform connects clients with a curated community of over 500 pentesters on demand. Thousands of companies use Cobalt to kick off tests instantly, collaborate with testers in real time, and get integrated reports in the platform. They emphasize speed and scalability organizations can launch pentests in hours rather than weeks. The model democratizes expert testing through technology.
Manual vs Automated Depth Analysis: Cobalt’s model is PTaaS hybrid. Clients submit assets via the Cobalt platform, which then automatically assigns qualified testers. While Cobalt uses automation and AI to match assets to pentester skills and to streamline reporting, the actual finding of vulnerabilities is done by human testers. They also offer continuous scanning complements to periodic manual assessments.
Key Strengths:
Potential Limitations:
Best For: Tech forward enterprises, DevOps teams, and mid market firms that want continuous, on demand pentesting and rapid visibility into risk via a streamlined platform.
Headquarters: Seattle, Washington, USA
Founded: 1998
Company Size: ~100 (51 200)
Primary Services: Full Stack Penetration Testing (network, web, cloud), OT/ICS & SCADA security, IoT/Automotive security, Hardware Hacking, Red Teaming, Chip to Code Assessments.
Industries Served: Power & Utilities, Gaming, Hardware/IoT, Retail, Finance, Automotive, Aerospace, Healthcare, High Tech
Why They Stand Out: IOActive is known for deep technical expertise. Their specialists tackle everything from embedded firmware and automotive systems to industrial control environments. They pride themselves on a research fueled approach and even offer a 100% satisfaction guarantee. The team has a track record of pioneering work in hardware reverse engineering and SCADA security. They serve a majority of Global 500 companies, indicating trust in highly critical sectors.
Manual vs Automated Depth Analysis: IOActive’s testing is manual and research intensive. They do not offer basic scanning; instead, expert analysts manually dissect each asset. For example, their assessments of ATM or medical device security rely on original exploit development. They may incorporate automated discovery to surface obvious issues, but the core of the engagement is manual verification and novel attack development.
Key Strengths:
Potential Limitations:
Best For: Organizations in sectors with unique technology stacks e.g. automotive, industrial, IoT/embedded devices, and utilities where cutting edge technical penetration testing is required.
Headquarters: Westminster, Colorado, USA
Founded: 2001
Company Size: ~1,000 employees
Primary Services: Cybersecurity Advisory, Compliance & Risk Assessments, Penetration Testing, Cloud Security, Incident Response (DivisionHex).
Industries Served: Highly regulated sectors (Financial Services, Government, Healthcare, Retail, Cloud providers); 1000+ enterprise clients.
Why They Stand Out: Coalfire is a cybersecurity firm deeply rooted in compliance and certification testing. The company navigates 85+ regulatory frameworks in its assessments, making it a go-to for FedRAMP, PCI DSS, HIPAA and other high stakes audits. Their elite DivisionHex team offers advanced offensive/defensive services for clients at the maturity frontier. They emphasize efficiency: one marketing banner touts coordinated assessments across 85+ frameworks for compliance efficiency. Enterprises trust Coalfire for meeting stringent cyber risk mandates.
Manual vs Automated Depth Analysis: Coalfire provides a blended approach. For compliance driven projects, automated vulnerability scanning and checklists are heavily used to cover required controls. They then apply manual penetration testing to key assets (especially on high risk projects). The DivisionHex group, however, offers full manual red teaming if requested. Overall, Coalfire balances thorough compliance scanning with manual expertise where it matters.
Key Strengths:
Potential Limitations:
Best For: Regulated enterprises and cloud service providers needing compliance driven testing, such as financial institutions pursuing PCI DSS, federal agencies building FedRAMP, or healthcare systems with HIPAA/SOC2 obligations.
Headquarters: Chicago, Illinois, USA
Founded: 1995
Company Size: ~800 employees
Primary Services: Managed Security Services (MSS), Managed Detection & Response (MDR), Offensive Security (Penetration Testing, Red Teaming), Database & Cloud Security, SIEM.
Industries Served: Mid market and enterprise organizations worldwide (leveraging Singtel’s global MSSP network).
Why They Stand Out: Trustwave (now rebranded as part of LevelBlue) is a leading managed security provider with a strong penetration testing arm. They combine traditional consulting with continuous security operations. Trustwave is recognized as a leader in MDR, MSS, and pen testing. Their global Security Operations Centers and large toolset (including partnership with Tenable for vulnerability scanning) offer clients integrated defense strategies. They cater to organizations that want a single vendor for 24/7 monitoring and periodic offensive assessments.
Manual vs Automated Depth Analysis: Trustwave’s testing tends toward the automated/managed model. They leverage advanced scanning (e.g. integrated Tenable tools) for asset discovery and vulnerability identification, then follow up on findings. Their red teaming service exists but is one part of a larger MSSP portfolio. In short, they rely heavily on tooling and platform driven workflows, with a manual team reviewing key results.
Key Strengths:
Potential Limitations:
Best For: Companies (especially mid sized) that want combined MDR/MSSP services with complementary penetration testing e.g. regional banks, healthcare providers, or retailers looking for an all in one security provider.
| Company | Specialization | Testing Depth Model | Best For | Region | Compliance Alignment | Ideal Org Size |
|---|---|---|---|---|---|---|
| DeepStrike | Cloud/API, application, red teaming | Manual exploit chaining | Cloud native tech firms, fintech | Global | ISO 27001, SOC 2, HIPAA | Mid–Large |
| Offensive Security | Advanced attacks, adversary emulation | Manual (no scan only) | High security government, defense | Global | N/A (focus on IR scenarios) | Large |
| NCC Group | Broad consulting, compliance driven | Hybrid (scans + manual) | Regulated enterprises (finance, gov) | Global | PCI DSS, ISO 27001, FedRAMP | Large |
| Deloitte | Risk advisory & compliance, enterprise IT | Hybrid | Multinational corporations | Global | SOC 2, ISO 27001, NIST | Large |
| Mandiant | Incident response, threat intelligence | Manual (adversary emulation) | Fortune 100 companies, defense | Global | NIST, FedRAMP, Intel sharing | Large |
| Bishop Fox | Continuous pentesting, DevSecOps integration | Hybrid (manual + continuous scan) | Tech startups, SaaS and SMBs | Global | SOC 2, ISO 27001, PCI DSS | Mid–Large |
| Cobalt | Pentest as a Service (platform + pentesters) | Crowdsourced PTaaS (auto + manual) | DevOps centric teams, continuous testing | Global | ISO 27001, SOC 2, PCI DSS | SMB–Mid |
| IOActive | IoT/OT/Automotive/hardware security, research | Manual (deep manual testing) | IoT/industrial/automotive sectors | Global | NIST, industry specific regs | Mid–Large |
| Coalfire | Compliance & cloud security, FedRAMP, HIPAA | Hybrid | Highly regulated enterprises (cloud) | Global | FedRAMP, PCI DSS, HIPAA, ISO | Large |
| Trustwave | Managed security, SIEM, and penetration tests | Automated heavy (scans + review) | SMB to mid size (with managed security) | Global | PCI DSS, GDPR, SOC 2 | SMB–Mid |
The choice between an enterprise focused VAPT provider and a boutique partner often comes down to cost vs depth and risk profile. Large consultancies or MSSPs (like Deloitte or Trustwave) bring broad capabilities and compliance muscle but usually charge higher rates and may apply less manual rigor on each test. They scale well for hundreds of targets at once, but smaller companies might overpay for resources they don’t need. In contrast, specialized firms (DeepStrike, Bishop Fox, IOActive) tend to focus on technical depth. They often operate on hourly or engagement pricing that, while competitive for expert testing, may require smaller scopes to keep projects affordable.
For enterprises, the ability to cover a global asset base and meet complex compliance demands is crucial. Big firms or any provider with global offices might be better equipped here. SMBs and agile teams may prefer the flexibility of a smaller vendor’s subscription model or PTaaS, which can fit faster timelines and iterative development.
In terms of risk exposure, larger organizations usually need to minimize it across a vast infrastructure, so even if penetration testing is costly, it’s justified by higher absolute risk. SMBs might target their most critical apps or cloud workloads first.
Boutique firms often provide deeper manual testing per hour, which is a trade off: more thorough results but requiring realistic project budgets. Automation focused services reduce costs but might miss logic or chain exploits (hence the emphasis on truly penetration testing).
In summary, an enterprise should plan on investing more for comprehensive coverage and compliance assurance, accepting longer lead times. An SMB might optimize for faster, agile testing (even if somewhat narrower in scope) and consider PTaaS or smaller providers. Always verify that the chosen model (e.g. automated scans vs manual pentests) aligns with the organization’s security maturity and regulatory obligations.
FAQs :
Costs vary by scope, vendor, and delivery model. A basic network or web app test might run from tens of thousands to low six figures for an enterprise. Subscription models (continuous testing) might be structured monthly. Automated only scans can cost much less, but true penetration tests with skilled consultants command higher fees. Always ensure the price quote covers all desired assets, retesting, and deliverables.
Enterprise engagements usually include an initial scoping meeting, on premise or remote testing of agreed systems (e.g. networks, servers, apps), both internal and external scans. It often covers automated scans, manual vulnerability validation, exploitation of critical issues, and a comprehensive report with risk analysis. Additional services may include social engineering (phishing), physical testing, or specific standards validation if requested.
ISO 27001 does not explicitly require penetration testing, but a mature Information Security Management System will include regular testing. PCI DSS requires quarterly external scans and annual penetration tests of the cardholder data environment. For SOC 2 (Type II) audits, penetration testing is recommended to demonstrate controls. Regulatory standards increasingly expect VAPT or equivalent assessments; consult your certifying body or framework guidance.
Typical external network or web app tests run 2–4 weeks from kickoff to final report. Larger enterprise projects can last 1–3 months, especially with extensive internal networks or many assets. Continuous testing programs run indefinitely with periodic check-ins. Factoring in scheduling, briefings, testing, remediation time, and retesting is important. Never rush critical tests; building buffer time for fix verification is wise.
As a rule of thumb, conduct a full penetration test at least annually, or after any major changes (new network segments, big software releases, cloud migrations). Many companies test quarterly or biannually when compliance mandates or high risk justifies. Continuous scanning or more frequent automated tests (monthly/weekly) are becoming best practice, with full manual tests less often but triggered by significant changes or threat alerts.
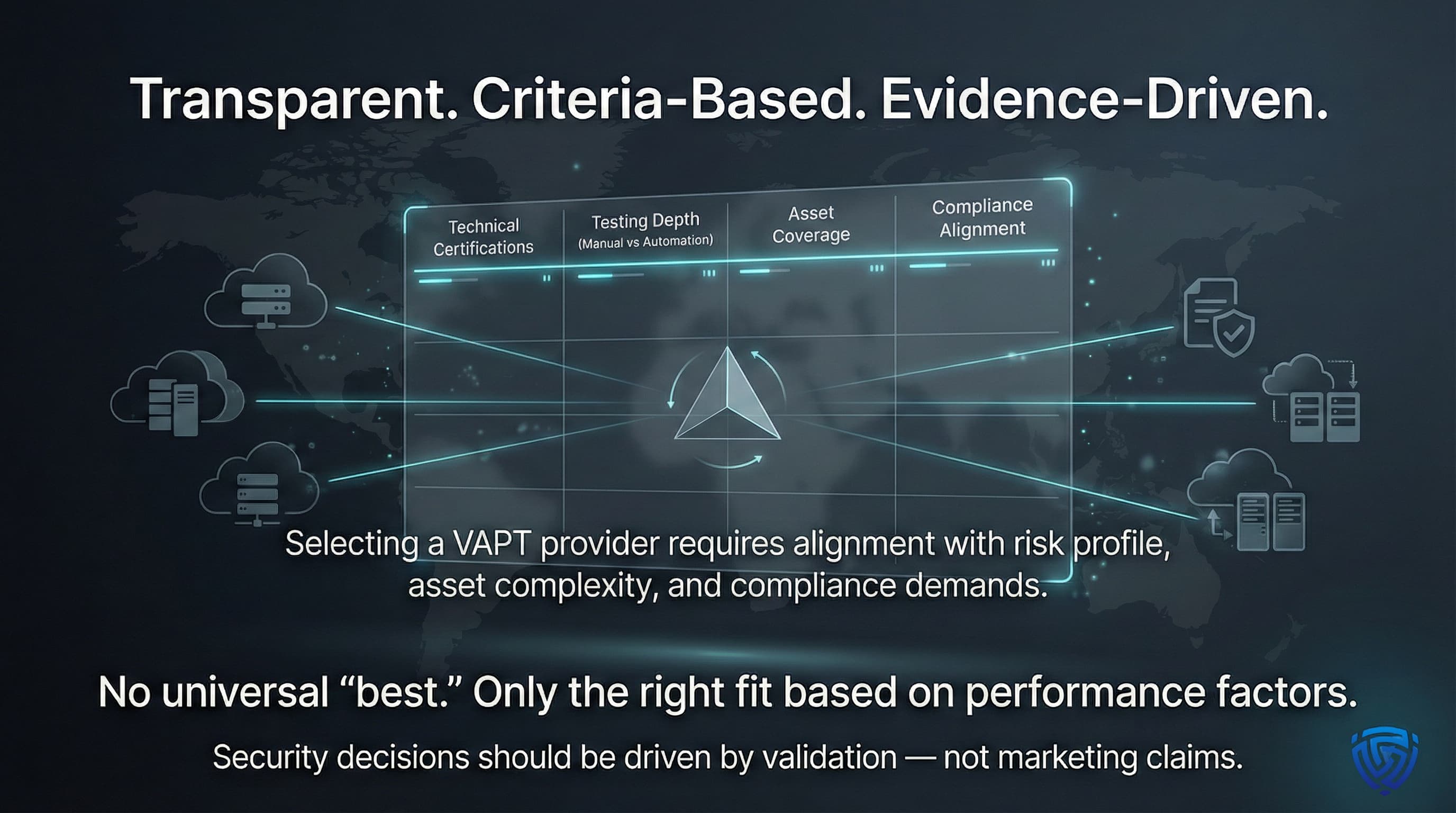
This analysis presents a transparent, criteria based comparison of the top VAPT service providers worldwide. By focusing on technical certifications, testing depth (automation vs manual), coverage of assets, and compliance alignment, we have highlighted providers that excel in different scenarios. Readers should select among the Top VAPT Service Providers above by matching their organizational needs (e.g. enterprise vs SMB) and risk profile. Ultimately, no single vendor is universally best; instead, this structured vendor comparison empowers security leaders to identify the right cybersecurity partner based on clear performance factors, not marketing claims.
About the Author: Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.
Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us