October 17, 2025
Updated: February 22, 2026
A risk-adjusted executive guide to enterprise penetration testing budgets, ROI modeling, and procurement strategy.
Mohammed Khalil
Penetration testing pricing in 2026 is a financial decision as much as a technical one. Budgets for security testing must be set against potential loss exposures for example, IBM reports that a single data breach now costs an average of over US$10.22 million in the U.S.. Even a six figure pentest that prevents one breach can justify its cost many times over. Yet prices vary widely from a few thousand dollars to over $150,000 per engagement because each engagement’s scope, complexity, and required rigor can differ dramatically. This executive guide dissects the cost drivers behind Penetration Testing Pricing, showing how to allocate capital for testing in proportion to risk exposure.
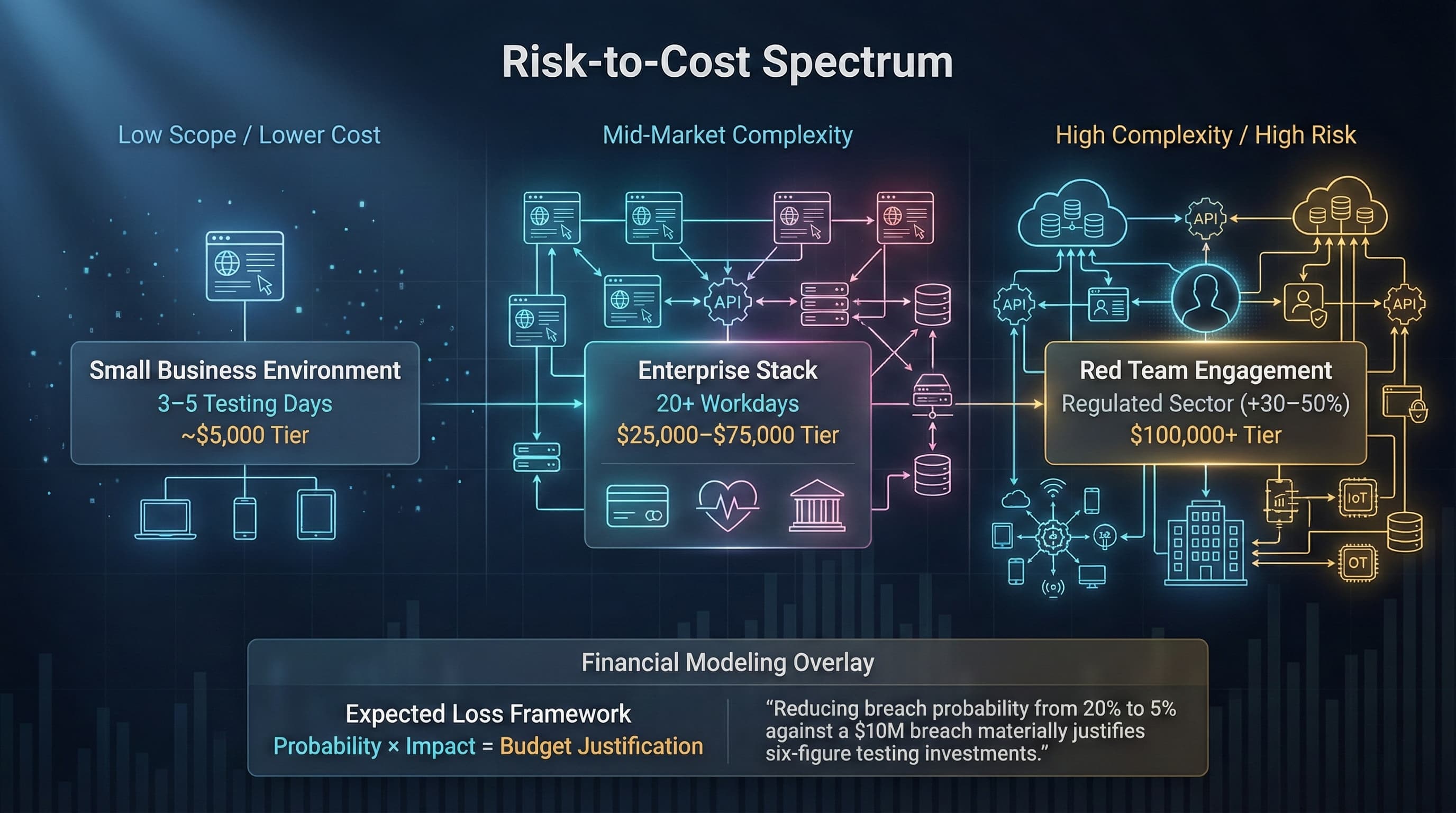
Penetration Testing Pricing is inherently complex because every environment and testing requirement differs. In broad strokes, costs track directly with risk exposure: the more valuable or numerous the assets, the higher the potential breach impact, the more justification for a thorough and thus costly test. For example, an online retailer handling credit card data faces compliance mandates PCI DSS and high breach costs, so a comprehensive test is essential. In contrast, a small intranet site with no sensitive data may need only a basic check.
Practically, scope is the most direct cost driver: each additional web application, API, or endpoint adds testing days and effort. Complex enterprise systems with dozens of apps can require 20+ workdays, whereas a small business’s 1–2 apps might need only 3–5 days. Similarly, test type matters: an external black box scan no internal info takes more effort than a scoped white box review, and red team exercises targeting people, physical sites, etc. require multiple specialists and run long. Industry and compliance demands add another layer: regulated sectors healthcare, finance, government demand audit ready documentation and sometimes specialized techniques, typically boosting cost 30–50%.
In 2026, pentests span the spectrum from ~$5,000 to well over $150,000. That range reflects everything from a quick vulnerability scan by a junior analyst to a multi week assessment by senior consultants. For budgeting, focus on risk management: an insurer would call this the expected loss framework. As shown later, even modest probability reductions say 20% → 5% against a US$10M breach can justify six figure testing budgets.
Penetration Testing Pricing refers to the structured cost modeling of security testing engagements based on scope, asset complexity, depth of testing, regulatory requirements, and remediation validation cycles. In practice, it’s not just a line item on a quote it’s an entire risk management investment. The price you pay reflects a basket of factors: how many servers and apps will be tested, what assumptions credentials, architecture diagrams, etc. are provided, and how deeply testers will probe. It also incorporates the quality of deliverables detailed evidence vs. checklist reports and the inclusion of follow up retesting.
Beneath the covers, a higher price usually means more manual work by experienced analysts rather than automated tools. Leading testers e.g. OSCP/OSWE/CREST certified command higher day rates. For example, hiring an OSCP certified consultant can cost ~$300/hour vs ~$100/hour for a junior. The extra cost buys expertise: seasoned testers can uncover complex business logic flaws and chained exploits that a scan misses. Similarly, enterprise engagements often build in formal project management and compliance workflows, which add to the fixed cost.
In short, penetration testing pricing is best viewed as allocating capital to minimize future loss. That investment covers the tester’s time, the tools and processes used, and the quality of reporting. Budget owners CISOs, CFOs should see it as buying guaranteed reduction in breach probability and dwell time, not merely a service to cut a check. As an example, even a one time pen test that costs US$30k can offer an ROI of 340:1 if it prevents a breach worth ~US$10M.
Key cost components that break down any pentest quote include:
Each factor above can multiply baseline costs. Below is a simplified range table to illustrate typical enterprise vs. SMB costs by test type all in USD:
| Test Type | SMB Range | Enterprise Range | Key Driver |
|---|---|---|---|
| Web Application | $4,000 $8,000 | $15,000 $30,000 | # of apps, complexity |
| Mobile Application per OS | $5,000 $10,000 | $20,000 $40,000 | OS count, API coverage |
| Cloud Infrastructure | $8,000 $15,000 | $30,000 $60,000 | # of cloud assets, config complexity |
| Internal Network | $7,000 $20,000 | $25,000 $50,000 | Hosts, segmentation |
| External Network | $5,000 $12,000 | $12,000 $25,000 | Perimeter devices, scope |
| Red Team Exercise | $30,000 $50,000 | $100,000 $200,000 | Duration, social engineering |
| Continuous Program annual | $10,000 $30,000 | $50,000 $150,000 | Ongoing tests, subscription model |
For example, SMB budgets often allocate $5K–$15K/year to basic penetration testing covering one web app and external network. In contrast, large enterprises may invest $50K–$150K+ annually for comprehensive programs covering multiple assets and red teaming.
| Model | Cost Predictability | Scope Risk | Long term Efficiency | Operational Fit | Under scope Risk |
|---|---|---|---|---|---|
| Fixed Bid | High set project price | High if initial scope is tight | Low need new contract for changes | Good for well defined, one off needs | High if scoping is off |
| Time & Materials T&M | Low hours billed as used | Low scope can flex | Moderate flexible but unpredictable | Fits ambiguous or evolving projects | Moderate may expand scope overrun |
| PTaaS Subscription | Medium annual fee tiers | Low continuous coverage | High streamlined retesting & triage | Aligns with DevOps/Agile, continuous dev | Low broad recurring tests |
| Continuous Pentesting Managed | Medium yearly contract | Low regular updates | High avoids rebidding each test | Best for critical/high compliance environments | Low programmatic scope |
Each model allocates financial risk differently. Fixed projects shift scope risk to the buyer, while subscription models absorb some uncertainty for broader protection. Procurement should weigh which model aligns with organizational cadence and risk appetite.
Enterprises must recognize hidden costs of ultra cheap pentests. Common low cost pitfalls include under scoped fixed bids, scan only assessments, and insufficient expertise. Each shortfall carries financial and security implications:
Each red flag above correlates with a financial cost: either wasted budget on ineffective tests, or outsized losses from undetected breaches. For example, a $5K bargain test that misses critical flaws can result in a breach costing $1–10M, dramatically outweighing any upfront savings.
Ultimately, penetration testing cost must be justified against potential breach impact. Use an expected loss model:
Expected Loss=Probability of Breach×Impact (Loss per Breach)
IBM’s 2025 breach report finds a US breach averages $10.22M global ~$4.4M. Suppose an organization’s breach impact is $10M. If a low end test or none corresponds to a 20% breach probability, the expected loss is $2.0M. Upgrading to a rigorous enterprise pentest might cut probability to 5%, dropping expected loss to $0.5M. The 15 percentage point reduction saves $1.5M in expected losses.
| Scenario | Breach Probability | Expected Loss at $10M impact |
|---|---|---|
| Baseline/Low Cost Test | 20% | $2.0 million |
| Mid Tier Testing | 10% | $1.0 million |
| Enterprise Grade Testing | 5% | $0.5 million |
In this example, moving from a minimal test to an enterprise grade test reduces expected losses by $1.5M. Even after paying for the higher end test, the net financial benefit is massive. This is analogous to insurance: spending $100K to avoid an additional $1.5M in risk makes fiscal sense.
Dwell time time attackers remain undetected compounds exposure. IBM reports mean dwell ~181 days, meaning breaches can fester for months. Frequent testing and continuous validation shorten dwell, catching issues sooner. This dynamic effectively lowers the probability term in the expected loss equation.
In summary, comparing low cost testing vs enterprise grade testing may look like this:
This numeric comparison highlights why organizations invest more: the reduction in expected loss far exceeds the incremental testing cost.
A concrete financial model clarifies the value:
| Metric | Value |
|---|---|
| Cost of Pentest Engagement | $100,000 |
| Breach Probability pre test | 20% |
| Breach Probability post test | 5% |
| Impact of Breach Loss | $10,000,000 |
| Expected Loss Before | $2,000,000 |
| Expected Loss After | $500,000 |
| Reduction in Expected Loss | $1,500,000 |
| Net Gain Reduction Cost | $1,400,000 |
| ROI Gain/Cost | 1400% |
In this scenario, spending $100K on a thorough engagement cuts breach probability by 15 points. The expected loss drops by $1.5M, so even after subtracting the test cost, there’s a net benefit of $1.4M. In ROI terms, that’s 14× the investment. By comparison, an anecdote in industry showed a $25K test yielding over $565K in risk reduction a 2260% ROI.
This example frames penetration testing spend as a quantifiable insurance premium. Procurement teams can present similar models: if the cost of a breach and the probability reduction are estimated, the expected gain often justifies premium testing. Success metrics like reduced cyber insurance premiums or avoided fines can also be included to bolster justification.
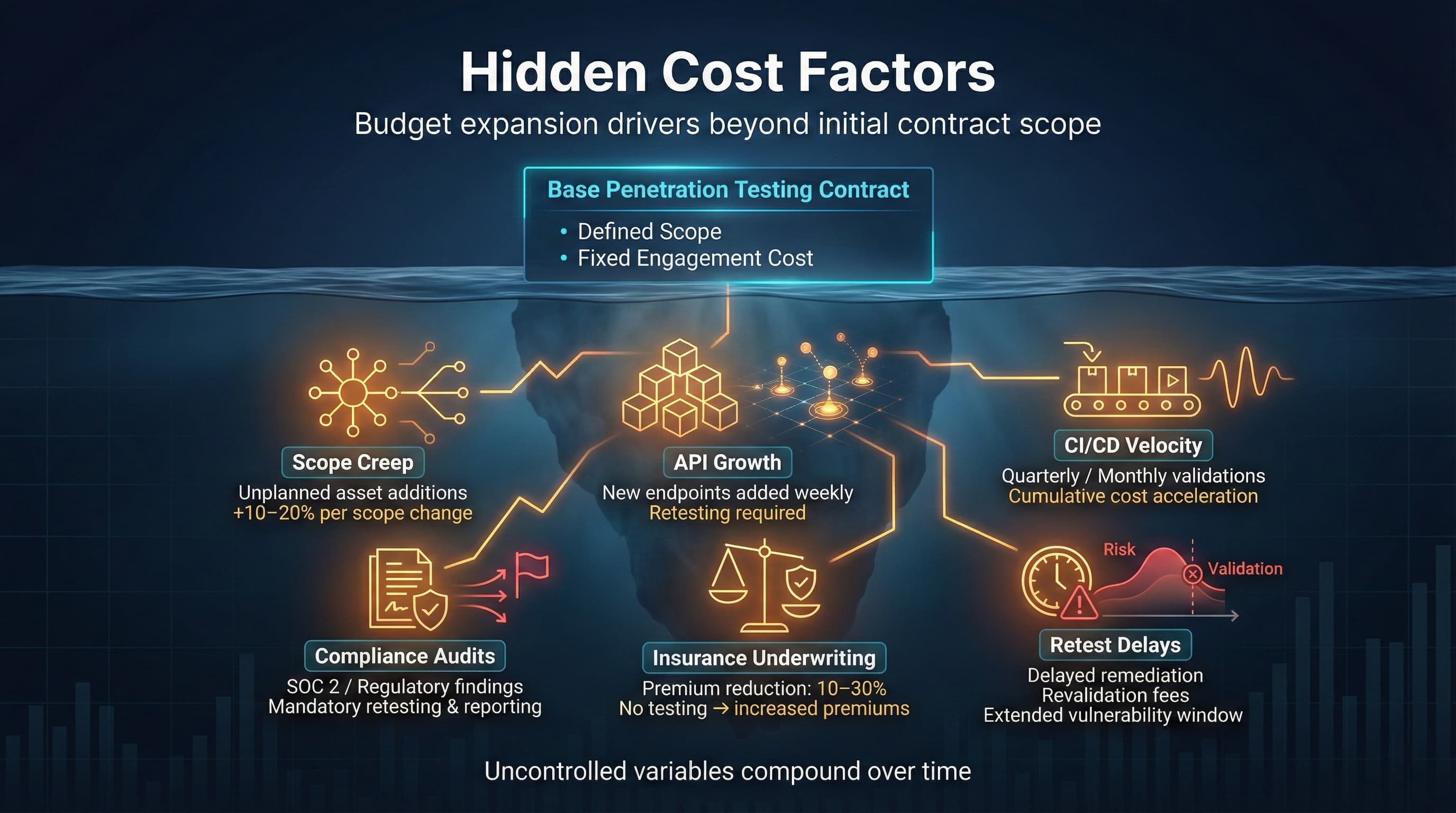
Several below the line factors can inflate penetration testing budgets over time:
These hidden factors typically emerge mid contract. Procurement should negotiate clear terms on handling scope changes, retesting timetables, and additional fees, to prevent small changes from ballooning costs.
When evaluating proposals, watch for signs of underservice that compound long term risk and cost:
Each red flag amplifies risk. For example, one buyer paid ~$5K for an automated scan disguised as a pentest and later learned that a simple SQL injection missed in the scan exposed customer data costing far more in response and remediation. Procurement should see beyond price to assess these non technical risk multipliers.
There are scenarios where a low cost test suffices:
In each case, the decision assumes the incremental risk is acceptably low relative to the cost savings. However, this should be a conscious trade off. Procurement should verify that the lower scope truly matches the organization’s risk profile. If future conditions change new app, regulatory trigger, growth, be prepared to upscale testing rigor.
Conversely, enterprise level pricing with its higher cost is warranted when the stakes are high:
In these cases, the enterprise pentesting price is not wasted cost but necessary risk mitigation. As one security executive put it, paying for senior testers and exhaustive coverage is akin to paying for a premium insurance policy against cyber loss. The capital allocation is framed as reducing expected loss, and business leaders recognize that spending tens of thousands today can prevent multi million losses tomorrow.
| Evaluation Factor | Why It Impacts Pricing | Risk If Ignored |
|---|---|---|
| Tester Certifications | Ensures testers have advanced skills OSCP, OSWE, CISSP, CREST. Higher certs command higher rates but often find deeper issues. | Uncertified testers may miss complex flaws; hidden vulnerabilities go unaddressed. |
| Manual Testing Hours | Indicates depth of analysis. More manual hours = more thorough review beyond automated scans. | Over reliance on tools leads to superficial coverage; critical logic bugs can be missed. |
| Retest Inclusion | Includes follow up testing after remediation often 20–30% fee. Ensures confirmed fixes without new contract. | Without it, remediated flaws may persist or require new engagements, raising total cost. |
| Named Senior Lead | Accountability and expertise. A designated senior ensures methodology and quality. | Lack of oversight can lead to inconsistent depth; quality may vary if only juniors are named. |
| Scope Clarity | Defines exactly what assets are tested. Clear scope prevents surprises in cost. | Vague scope leads to hidden asset costs or untested systems; scope creep can inflate bills. |
| Compliance Mapping | Aligns testing to required standards PCI, HIPAA, ISO, etc.. Specialized tests cost more. | Ignoring compliance needs can result in audit failure, fines, and unplanned re testing. |
| Deliverable Depth | Level of report detail evidence, risk scoring, remediation. More depth requires more analysis. | Superficial reports leave teams guessing; poor guidance increases time to remediate. |
| SLA Structure | Defines timelines turnaround, retest, escalations and liability e.g. breach clauses. | Without clear SLAs, issue resolution may be delayed and accountability absent. |
The checklist above guides procurement in evaluating quotes. Each factor affects how many resources the vendor will commit and thus the price. Ignoring any of these can introduce hidden costs, either through paying again or suffering breaches.
Typical penetration testing projects range from $5,000 to $50,000+ depending on scope and complexity. A simple external test for a small business might cost ~$5–10K, whereas a comprehensive enterprise test covering apps, networks, cloud, and compliance can exceed $50K. Context matters: pricing is driven by asset count, testing depth, and compliance requirements.
Key drivers include the number and type of systems web, APIs, networks, required test methodology black box vs white box vs red team, and any regulatory mandates. For example, PCI or HIPAA tests require extensive documentation and typically add 30–50% cost. Tester experience is also a factor: certified senior testers raise cost but often find more issues.
Choose based on your organizational needs. A fixed price bid suits a well defined, one off project with the risk of scope gaps. Time and Materials works if requirements may shift mid engagement. PTaaS/Continuous subscriptions are best for active development environments, offering predictable budgets and ongoing security checks. Consider efficiency and risk: continuous models reduce blind spots, whereas fixed engagements give upfront cost certainty.
Automated scans are useful but limited. They often miss chained attacks or business logic flaws. Real pentesting involves manual expertise that uncovers complex vulnerabilities. Industry experts warn that cheap, scan only tests leave organizations exposed. While pentesting costs more, it materially lowers breach likelihood and expected loss, making it a high return investment in most cases.
Strategic penetration testing pricing is ultimately an exercise in capital risk management. Decision makers must balance the upfront cost of testing against the potentially enormous cost of undetected breaches. In dollar terms, even a thorough $25K test can deliver a multi million dollar payoff by preventing a single incident. This pricing guide has broken down how vendors charge by scope, depth, compliance, and expertise so that CISOs, CFOs, and procurement leads can budget defensively.
Enterprise grade engagements command higher fees, but they also carry the highest risk mitigation value. A well scoped penetration test is like an insurance policy with very favorable terms: pay tens of thousands now to avoid millions later. Conversely, cutting corners on cost can multiply risk; as one analysis warned, a thorough $25,000 test that identifies critical vulnerabilities provides far better ROI than a $5,000 scan that misses critical security gaps.
In 2026’s threat landscape, where average breach costs continue rising, allocating budget to mature, enterprise level testing is a prudent use of capital. Penetration testing pricing is not just a line on a procurement sheet it’s a calculated risk transfer. By understanding cost drivers and trade offs, organizations can ensure every dollar spent maximizes exposure reduction and aligns with their financial risk appetite.

Ready to Strengthen Your Defenses? The threats of 2026 demand more than just awareness; they require readiness. If you're looking to validate your security posture, identify hidden risks, or build a resilient defense strategy, DeepStrike is here to help. Our team of practitioners provides clear, actionable guidance to protect your business. Explore our Penetration Testing Services to see how we can uncover vulnerabilities before attackers do. Drop us a line, we’re always ready to dive in.
About the Author: Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us