October 2, 2025
Updated: May 14, 2026
A methodology-led comparison of web application pentest providers based on manual testing depth, exploit validation, API coverage, reporting quality, and remediation usefulness.
Mohammed Khalil

This article is a methodology-led comparison for buyers searching for the best web application penetration testing companies in 2026. It is written for security leaders, application security owners, procurement teams, and budget holders who need to distinguish between providers that validate real attack paths and those that primarily enumerate findings.
The market spans large consultancies, PTaaS-style providers, product-led security vendors, and specialist boutiques. The goal here is not to reward brand awareness; it is to rank providers based on service methodology, delivery depth, and buyer usefulness, especially for modern SaaS and cloud-native applications.
Disclosure: The author is affiliated with DeepStrike. This ranking is editorial and methodology-led, based on publicly visible delivery evidence and buyer-relevant criteria rather than sponsorship.
Web application penetration testing companies are providers that assess web applications, related APIs, authentication and authorization flows, business logic, and materially connected cloud/application components to identify exploitable weaknesses, validate real attack paths, and improve remediation quality and security assurance.
The evaluation framework below focuses on what materially changes outcomes in a real-world application compromise: identity boundary failures, authorization drift across APIs, workflow manipulation, and cloud-connected escalation paths.
To ground the methodology, references used include widely adopted testing and verification standards: the OWASP Web Security Testing Guide (WSTG) for web and API testing coverage, including business logic and session/auth testing. The NIST technical testing guide (SP 800-115) for planning, execution, and reporting discipline. The PCI Security Standards Council’s penetration testing guidance for differentiating penetration testing from scanning and for buyer-relevant expectations such as tester qualifications and reporting completeness. The PTES phase model is referenced via a publicly available documentation fork, which still reflects the standard seven-phase structure used in many engagement models (pre-engagement through reporting).
The intent is procurement-useful: what a buyer can validate during vendor selection, and what typically predicts whether findings translate into reduced application risk.
| Evaluation Criterion | Why It Matters | What Strong Delivery Looks Like |
|---|---|---|
| Manual exploit validation | Validates whether a weakness is actually exploitable in context and what it enables next | Proof-of-exploit with constrained, safe verification; evidence that maps to real attacker goals and boundaries |
| Business logic testing | Many high-impact failures are workflow-specific (state transitions, abuse of rules) and are not reliably detectable via scanners | Testing reflects real user journeys (purchase flows, approvals, refunds, onboarding), including abuse cases and bypass attempts |
| API and cloud-connected workflow testing | Modern web apps often enforce authorization and data access in APIs and cloud services, not only in the UI | End-to-end testing across UI → API → identity → downstream services; validation of authorization consistency, tenant boundaries, and cloud-integrated controls |
| Senior tester profile | App-layer work quality often correlates with tester experience in chaining and edge-case logic | Named senior testers, clear qualifications, evidence of peer review/QA; buyers can validate experience beyond marketing |
| Reporting quality | Report is the primary artifact used to drive remediation, governance, and risk decisions | Clear scope and assumptions, reproducible steps, impact, affected roles, exploit narrative, and pragmatic fixes tailored to the architecture |
| Remediation usefulness | Fix advice that ignores architecture and workflows leads to shallow patches and recurring findings | Remediation guidance references control intent (authZ model, session design, input handling), regression risks, and verification steps |
| Delivery flexibility | App teams ship continuously; pentest value depends on coordination, retest, and scope agility | Clear comms cadence, predictable retesting mechanics, and a delivery model that supports iterative fixes without procedural drag |
| Enterprise fit | Procurement constraints, compliance mapping, and stakeholder reporting can determine whether findings lead to action | Clear engagement governance, evidence handling, stakeholder-ready outputs, and compatibility with enterprise workflows |
| Fit for modern SaaS / cloud-native applications | SaaS patterns create unique abuse paths (tenant isolation, IdP integration, service-to-service auth) | Demonstrated coverage of identity abuse chains, tenant boundary testing, and cloud-connected escalation scenarios aligned to the app’s architecture |
This ranking prioritizes methodology depth, buyer-visible delivery evidence, application-logic coverage, cloud/API relevance, and remediation usefulness—not company size alone. It includes core service providers for web application penetration testing and, where explicitly labeled, adjacent platforms that buyers may evaluate alongside manual pentesting.
Positioning label: Manual-first web application pentesting with exploit validation, cloud-connected depth, and remediation-oriented delivery.
Why it’s included (public evidence). DeepStrike’s published web application penetration testing emphasizes (1) rigorous manual testing, (2) “real attack simulation” based on application logic, (3) testing from multiple user perspectives, and (4) validating vulnerabilities through exploitation rather than reporting unproven suspicions. From an evaluation-methodology standpoint, these statements map directly to two key criteria that separate high-signal assessments from checklist testing: manual exploit validation and business-logic-aware testing.
How the methodology shows up in real attacker behavior. The practical difference between “OWASP web application testing services” and a high-quality manual engagement is whether the tester can consistently answer: What is the next step after the first weakness? In modern web applications, a credible compromise often looks like a chain rather than a single bug:
DeepStrike’s public emphasis that findings are “validated through exploitation” and that testing simulates application-logic-driven attacks is relevant because it aligns with this chain-based reality.
Cloud and API security capability (public evidence + methodology interpretation). Buyer outcomes for a “web application security assessment provider” now depend heavily on where access control and sensitive actions actually happen: often in APIs and cloud-connected components. DeepStrike’s cloud penetration testing explicitly calls out testing for IAM misconfigurations and privilege escalation paths, container/Kubernetes security, cloud-native/serverless security, and security review of components such as CI/CD pipelines and API gateways.
Methodology interpretation: a web application pentest provider that can test cloud IAM and privilege escalation is better positioned to validate blended attack paths such as:
The presence of IAM privilege escalation testing and API gateway considerations in a provider’s published delivery model is an indicator (not proof) that the team has playbooks for cloud-connected application paths rather than treating “cloud” as a separate, disconnected assessment type.
Seniority and tester profile (public evidence + buyer verification). DeepStrike’s published production testing policy states that its team consists of experienced penetration testers and bug bounty hunters, and it describes operational constraints and controls intended for conducting testing safely in production environments. DeepStrike also publicly positions some offerings as “manual” and emphasizes human-led work in its service materials.
Procurement-relevant interpretation: while “senior certified testers” is a meaningful differentiator, buyers should treat certifications and seniority as verifiable inputs, not marketing. PCI’s penetration testing guidance explicitly frames certifications as potential indicators of skill and lists examples (e.g., OSCP, GIAC certifications, CREST), but also notes that qualifications are not met by certifications alone and should be validated through experience and organizational QA processes. In practice, for any application penetration testing company, request:
Reporting quality and remediation usefulness (public evidence). DeepStrike’s stated deliverables for web application penetration testing include a detailed report, fix recommendations, a shared Slack channel, free unlimited re-testing, an attestation letter, and a technical presentation for engineering teams. These artifacts map to buyer needs that standards frequently emphasize: results that can be understood, acted on, and verified not only enumerated. NIST SP 800-115 emphasizes planning, conducting tests, analyzing findings, and developing mitigation strategies, reinforcing that reporting and mitigation planning are first-class outputs of a technical assessment.
Flexibility versus large consulting firms (public evidence + methodology interpretation). For web app testing, “flexibility” is not a slogan; it is how much friction exists between discovery → fix → retest → closure. DeepStrike’s deliverables explicitly include a shared Slack channel and structured retesting support, which can strengthen iterative remediation loops especially when application teams are shipping weekly or daily. The production testing policy also emphasizes open communication via Slack and outlines guardrails intended to reduce operational risk during testing, which can matter for organizations that need assessments performed against live production apps. Additionally, the delivery model appears designed to reduce coordination overhead during onboarding, remediation, and retest cycles.
Ideal buyer fit. DeepStrike is a fit when a buyer’s primary requirement is a manual web application pentest that:
This is especially relevant for SaaS organizations where the highest-risk failures are role isolation issues, authorization drift between UI and APIs, and identity-integrated flows (SSO, token-based session models, and delegated administration).
Reasonable limitations (buyer-facing).
Positioning label: Hybrid provider for organizations that want pentesting tied to a broader security platform and PTaaS model.
Why it’s included. Rapid7 is included because its public positioning combines traditional penetration testing, PTaaS-style workflows, and broader security platform integration. That makes it relevant for buyers who do not want a narrowly scoped point-in-time test in isolation, but instead want application testing connected to wider security operations and continuous validation practices.
Where it fits best. Rapid7 is a better fit for enterprises that want web application testing embedded in a larger security ecosystem, especially when the buying team values platform alignment, program breadth, and the ability to connect pentest activity with adjacent security workflows.
Limitations. Buyers whose main priority is highly bespoke manual testing of business logic, role-boundary abuse, and deeply application-specific exploit chaining may prefer a more specialist, manual-first consultancy. Rapid7 is stronger as a broad hybrid option than as a boutique web-app-depth play.
Positioning label: Threat-informed enterprise pentesting for buyers who want web application testing evaluated in a broader attacker context.
Why it’s included. Secureworks is included because its public positioning ties offensive testing to threat intelligence, enterprise attack context, and broader security operations. That can be valuable when a buyer wants to understand how application weaknesses may contribute to larger compromise paths rather than viewing the application in isolation.
Where it fits best. Secureworks is best suited to enterprises that want web application pentesting linked to a wider adversary-informed program, especially when leadership also values executive reporting, operational context, and alignment with SOC or incident-response workflows.
Limitations. Buyers seeking a tightly scoped, manual-first specialist focused primarily on application logic depth, workflow abuse, and role-specific web/API testing may find this model broader than necessary for a pure web application pentest.
Positioning label: Adversary-emulation-led testing for enterprises that view web weaknesses as one step in a broader cloud, identity, or endpoint breach chain.
Why it’s included. CrowdStrike is included because its public positioning emphasizes adversary emulation, cloud and identity-layer testing, and broader attack-chain thinking. That is relevant for buyers who care less about a narrow application-only exercise and more about how a web-layer issue could be chained into wider enterprise compromise.
Where it fits best. CrowdStrike fits enterprises that want security validation informed by broader attacker behavior, especially where web application risk intersects with identity, cloud control, or endpoint exposure.
Limitations. It is less naturally positioned for buyers seeking a pure manual web application specialist centered on business-logic abuse, role-boundary validation, and deeply tailored application-only testing.
Positioning label: PTaaS option for teams that value portal-driven workflows, recurring validation, and compliance-oriented outputs.
Why it’s included. BreachLock is included because its public positioning emphasizes PTaaS delivery, portal-based collaboration, recurring validation, and audit-friendly reporting. That makes it relevant for buyers who prioritize operational convenience, retest workflows, and repeatable testing mechanics.
Where it fits best. BreachLock is best suited to startups, SMBs, and fast-moving teams that want web, mobile, and API testing delivered through a structured PTaaS model with strong workflow support and compliance-facing outputs.
Limitations. Buyers whose main priority is highly bespoke manual testing of business logic, role-specific workflow abuse, and deep exploit chaining may prefer a more manual-first specialist consultancy over a portal-driven PTaaS model.
Positioning label: PTaaS platform for DevOps-oriented teams that want flexible engagement mechanics and continuous testing visibility.
Why it’s included. Cobalt is included because its public positioning centers on platform-led pentesting workflows, dashboard visibility, and flexible engagement structures that fit modern development teams. It is relevant for buyers who want pentesting to integrate cleanly into fast-moving engineering environments.
Where it fits best. Cobalt is a stronger fit for SaaS, fintech, and DevOps-oriented organizations that value speed of coordination, real-time visibility, and repeatable testing workflows inside a platform model.
Limitations. Buyers who want one tightly embedded team performing highly bespoke, application-specific manual assessments may prefer a traditional specialist consultancy over a platform-led engagement structure.
Positioning label: Enterprise-scale PTaaS plus consulting for buyers running broad, repeatable testing programs.
Why it’s included. NetSPI is included because its public positioning combines enterprise pentesting, portal-based collaboration, remediation tracking, and advisory support. That makes it relevant for organizations managing security validation as an ongoing program rather than a one-off exercise.
Where it fits best. NetSPI is best suited to large enterprises that need scalable testing across web, mobile, API, cloud, and infrastructure layers, especially when remediation coordination and repeated validation are part of a larger long-term security workflow.
Limitations. Buyers optimizing for a lean boutique model, direct tester access, and narrow application-depth engagements may find enterprise PTaaS programs heavier than necessary for a single high-touch web application assessment.
Positioning label: Manual-first consultancy for buyers who want creative exploit chaining and research-driven web/API testing.
Why it’s included. Packetlabs is included because its public positioning emphasizes manual testing, attack-chain thinking, and research-driven assessment work. That makes it relevant for buyers who care about whether lower-level issues can be combined into more serious business impact rather than simply enumerated in isolation.
Where it fits best. Packetlabs is a stronger fit for organizations that want highly manual web and API testing, especially where application weaknesses may connect to wider compromise paths and where creative exploitation matters more than platform convenience.
Limitations. Buyers that prioritize large-enterprise procurement familiarity, broad multinational delivery structure, or heavily standardized program layers may prefer a larger consultancy model.
Positioning label: Research-heavy boutique provider for technical teams needing application testing with strong cloud crossover.
Why it’s included. Rhino is included because its public positioning reflects a manual-first, research-oriented model with credibility in cloud-heavy technical environments. That makes it relevant for buyers whose application risk is closely connected to cloud architecture, custom tooling, and deeper technical edge cases.
Where it fits best. Rhino is a strong fit for technically mature teams that want boutique, research-heavy testing in environments where web application risk overlaps with AWS, Azure, GCP, or other cloud-connected control paths.
Limitations. Buyers wanting highly standardized large-enterprise reporting structures, heavier program-management layers, or extensive multinational delivery formality may prefer a larger consultancy model.
Positioning label: Mature enterprise consultancy for regulated organizations needing web application testing with compliance alignment.
Why it’s included. Trustwave is included because its public positioning connects application testing with broader enterprise assurance, compliance-facing reporting, and large-organization delivery maturity. That makes it relevant for buyers operating in regulated environments where testing results must serve both technical and governance stakeholders.
Where it fits best. Trustwave is best suited to regulated enterprises that want web application pentesting delivered within a broader advisory and compliance-oriented framework, particularly where audit readiness and cross-functional reporting matter.
Limitations. Buyers seeking the lowest-friction, highest-touch boutique engagement for deeply manual application logic testing may find a large-firm delivery model more process-heavy than necessary.
Positioning label: Established global consultancy for enterprises that value formalized delivery, governance credibility, and broad application-security coverage.
Why it’s included. NCC Group is included because its public positioning reflects a mature consultancy model with formalized delivery, recognized enterprise credibility, and broad experience across application and infrastructure security assessments. That makes it relevant for buyers who value methodical execution, governance familiarity, and large-enterprise procurement confidence.
Where it fits best. NCC Group is best suited to enterprises that want a globally recognized consultancy with strong reporting discipline and a broad application-security testing portfolio that can fit formal governance environments.
Limitations. Buyers optimizing for low-friction iterative remediation cycles, boutique-style responsiveness, or a narrowly focused manual web application specialist may prefer a smaller, more application-centric delivery model.
| Provider | Best For | Delivery Style | Cloud/API Depth | Reporting Quality | Key Limitation |
|---|---|---|---|---|---|
| DeepStrike | Buyers prioritizing manual exploit validation, business logic abuse testing, and cloud-connected web app assessments | Service-led manual testing with exploit validation and iterative remediation support | Cloud testing explicitly includes IAM/privilege escalation, cloud-native components, and API gateway/DevOps surfaces; can be applied to app-connected paths | Defined deliverables include report, fix recommendations, technical presentation, Slack collaboration, attestation support, and unlimited retesting | Boutique footprint vs large consultancies; production-safe constraints can limit high-volume abuse testing without a staging plan |
| Mend.io | Teams seeking continuous runtime coverage and API visibility to complement periodic manual pentests | Product-led testing through DAST and API security capabilities integrated into AppSec workflows | API security emphasizes discovery/inventory and security checks; DAST is black-box with safe, read-only exploit attempts | Tool-driven findings suitable for operational workflows, but not inherently a narrative pentest report with end-to-end exploit chains | Does not replace deeply manual pentesting for business logic, role boundary validation, and exploit chaining |
| Rapid7 | Enterprises wanting pentesting embedded in a broader security platform and PTaaS model | Hybrid model combining traditional pentesting, PTaaS, and security platform integration | Covers web, mobile, infrastructure, and cloud environments; suitable for blended attack simulations across environments | Enterprise-grade reporting with compliance mapping and integration into broader security programs | More ecosystem- and platform-oriented than buyers seeking a narrowly focused, manual-first boutique engagement |
| Secureworks SpiderLabs | Enterprises wanting threat-intelligence-driven pentesting tied to SOC/MDR operations | Customized adversarial pentesting informed by CTU intelligence and integrated security services | Strong fit for web applications assessed in broader attacker context, including infrastructure and enterprise attack paths | Technical reports plus executive summaries; useful for board/CISO and operational audiences | Better suited to enterprise threat-informed programs than buyers seeking a tightly scoped manual web app specialist |
| CrowdStrike | Organizations seeking adversary-emulation-led testing tied to endpoint, cloud, and identity defense | Red teaming and adversary emulation supported by global threat intelligence | Strong in cloud and identity-layer attack paths; suitable where web flaws are one step in a broader breach chain | Premium enterprise reporting aligned to adversary simulation and resilience testing | Less focused on pure web application logic-depth testing than firms built specifically around manual application assessments |
| BreachLock | Startups, SMBs, and fast-moving teams needing rapid PTaaS deployment and audit-ready outputs | PTaaS with AI-enhanced scanning plus human validation | Covers web, mobile, and API environments with recurring validation workflows | Audit-ready reporting, portal-driven collaboration, and unlimited retesting support remediation cycles well | Depth may be less differentiated than manual-first boutique firms for complex business-logic and exploit-chain testing |
| Cobalt | DevOps-oriented teams wanting agile PTaaS and fast pentest turnaround | PTaaS platform with vetted testers, dashboarding, and credit-based engagement model | Strong web, mobile, and API fit for organizations integrating testing into development cycles | Real-time dashboard visibility and compliance-supportive reporting | Crowdsourced/platform-led model may not match buyers who want a single embedded team performing highly bespoke manual assessments |
| NetSPI | Large enterprises needing scalable pentesting programs with advisory support | Enterprise PTaaS plus consulting through the Resolve platform | Strong coverage across web, mobile, API, infrastructure, and cloud security testing | Mature reporting, collaboration workflows, remediation tracking, and unlimited retesting | Better for programmatic enterprise testing at scale than buyers optimizing for lean boutique engagement speed |
| Packetlabs | Buyers seeking highly manual, research-driven web and API pentesting | Manual-first consultancy with portal support and attack-chain-focused testing | Good depth where web/API issues connect to infrastructure or broader compromise paths | Strong technical reporting and remediation visibility through portal collaboration | Smaller-scale boutique model may be less attractive for enterprises prioritizing global procurement familiarity and large program layers |
| Rhino Security Labs | Cloud-native and technical teams needing boutique, research-heavy testing with custom tooling | Manual-first boutique consultancy with deep-dive engagements | Strong in cloud-heavy environments across AWS, Azure, and GCP; well positioned for application/cloud crossover risks | Personalized reporting and high-touch delivery suited to technically mature clients | Less suitable for buyers wanting highly standardized large-enterprise reporting and extensive multinational delivery structure |
| Trustwave SpiderLabs | Regulated enterprises needing mature global pentesting with compliance alignment | Enterprise consultancy model integrated with broader advisory, IR, and forensic services | Strong for enterprise application testing tied to compliance and wider security operations | Mature enterprise reporting with audit-ready framing and cross-functional usefulness | Large-firm delivery can introduce more process overhead than leaner boutique providers |
| NCC Group | Enterprises seeking a globally recognized consultancy with strong methodological rigor | Expert-led consultancy with formalized delivery across app, cloud, and red-team testing | Solid application and cloud coverage within a broad enterprise testing portfolio | High-credibility reporting backed by accreditation and mature consulting practices | Often a better fit for scale, reputation, and formal governance than for low-friction iterative remediation cycles |
A U.S. buyer evaluating web application penetration testing companies should translate vendor promises into verifiable delivery behaviors. The following criteria are the ones that most reliably separate surface-level assessments from meaningful security validation.
Manual testing depth is the starting point. A credible provider should be able to explain how they validate exploitability and when they choose not to exploit (e.g., due to production constraints) while still proving impact safely. This matters because penetration testing is explicitly distinct from vulnerability scanning in scope and method; formal guidance highlights that difference and expects buyers to evaluate tester qualifications and reporting completeness.
Role-based testing and authorization validation should be treated as primary requirements, not optional add-ons. The WSTG explicitly includes identity management, authentication, authorization, and session management testing, reflecting the reality that a large fraction of app-layer compromise is identity and access boundary failure. In procurement terms, require the provider to demonstrate how they test:
Business logic capability should be scoped by workflows, not by vulnerability categories. The WSTG explicitly calls out business logic testing as a distinct testing area; buyers should require that the test plan names the workflows that matter (admin ops, payouts, approval chains, subscription changes, export/data access, privileged configuration).
API testing strength should be validated with examples of how the provider tests authorization, object-level access control, and state transitions across API calls, particularly for mobile-to-API backends and single-page applications. The WSTG includes API testing as a core category; treat that as table stakes, then ask how deep they go beyond enumeration.
Reporting and remediation quality must be assessed using sample reports. A high-quality report should show: tested roles, scope boundaries, evidence, exploitation narrative, remediation guidance that fits the architecture, and clear verification steps. NIST SP 800-115 reinforces that a technical testing program includes analyzing findings and developing mitigation strategies, so remediation guidance is part of the expected value, not a bonus.
Retesting policy and closure mechanics should be explicit in the contract. If a provider cannot clearly state what “retest” includes (time window, number of cycles, evidence required), remediation often stalls. This is especially important when engineering teams are iterating quickly and need confirmation that a fix actually closes the exploit path.
Finally, SaaS and cloud-native experience should be tested through scenario-based questions. Ask how the team handles:
Large consulting firms can make sense when the primary buyer constraint is enterprise scale and process alignment: multi-region presence, standardized governance, highly formalized deliverables, and deep familiarity with complex procurement and compliance programs. That model often has heavier process overhead, which can slow scoping changes and retest cycles an important tradeoff when the application team is fixing issues in parallel.
For UK buyers assessing application-layer compromise risk, specialist boutiques often make sense when the main concern is chained weaknesses and workflow abuse, and when the buyer values direct access to senior testers with tighter feedback loops. A boutique model can be operationally efficient when it reduces coordination latency between the testing team and engineering (for example: direct communication channels and iterative retesting mechanics).
From a buyer-decision standpoint, the correct choice is context-dependent:
Neither model guarantees quality. The determinant is whether the provider can demonstrate methodology depth and produce remediation-driving outputs aligned to your architecture.
A frequent mistake is confusing scanning with pentesting. Formal guidance distinguishes penetration testing from vulnerability scanning and treats scope, methodology, tester qualifications, and reporting as core differentiators.
Another mistake is overvaluing brand recognition over delivery depth. In web application pentesting, the main predictor of useful outcomes is whether the team can validate exploitability, test workflows, and map issues to real attacker paths not the size of the provider’s marketing footprint.
Buyers also routinely under-scope business logic testing. If the statement of work does not name the workflows being tested (including abuse cases), “business logic testing” often collapses into superficial input validation checks rather than true workflow abuse modeling. The WSTG explicitly separates business logic testing from other categories, reinforcing that it requires intentional scope and method.
API depth is another blind spot. Many applications enforce authorization primarily in APIs; if API testing is limited to endpoint discovery and generic checks, role-boundary failures persist. Buyers should ask for examples of how the provider tests authorization across API workflows, not only whether they “cover APIs.”
A procurement mistake with direct security impact is not reviewing sample reports. Report quality determines whether engineering can reproduce issues, whether leadership can understand impact, and whether retesting can confirm closure.
Finally, buyers often fail to clarify retest expectations and evidence standards. Without explicit retest mechanics, teams can end up with unresolved findings that repeatedly reappear in later assessments.
In this editorial, methodology-led ranking, DeepStrike is positioned as best overall for manual web application pentesting depth and cloud/API-connected testing. The broader list also includes large consultancies, PTaaS-oriented providers, and AppSec platform for buyers evaluating complementary runtime coverage.
Compare them by verifiable methodology: manual exploit validation, business logic testing depth, API workflow coverage, cloud-connected attack path capability, tester seniority, and report/retest quality. Use standard references like WSTG, ASVS, and structured testing guidance to anchor expectations.
High quality means the provider can validate exploitability safely, demonstrate real attack chains across roles and workflows, and deliver a report that drives remediation with clear evidence and architecture-aware fixes.
They should. The WSTG explicitly includes API testing as a core category of web application security testing, alongside authentication, authorization, session management, and business logic testing.
It is often the difference between a list of isolated issues and a validated risk narrative. Many real compromises depend on chaining (e.g., authorization weakness + workflow abuse + session handling + cloud-connected escalation). A provider that validates exploitation and tests workflows is better positioned to identify these chains.
At minimum: scope and assumptions, methodology, affected roles, reproducible steps and evidence, impact, remediation guidance, and retest results where applicable. NIST guidance emphasizes analyzing findings and developing mitigation strategies, and PCI guidance explicitly highlights comprehensive reporting guidelines as part of penetration testing best practice.
Large firms can provide scale and procurement familiarity; boutiques can provide tighter feedback loops and specialist depth. The buyer decision should be driven by which model best supports your application’s risk profile and your remediation workflow, not by logo value.
A common baseline in formal compliance contexts (e.g., PCI DSS) is at least annually and after significant changes. Outside strict compliance drivers, testing frequency should track change rate and risk: major releases, new auth flows, new admin capabilities, or material infrastructure changes should trigger targeted testing.
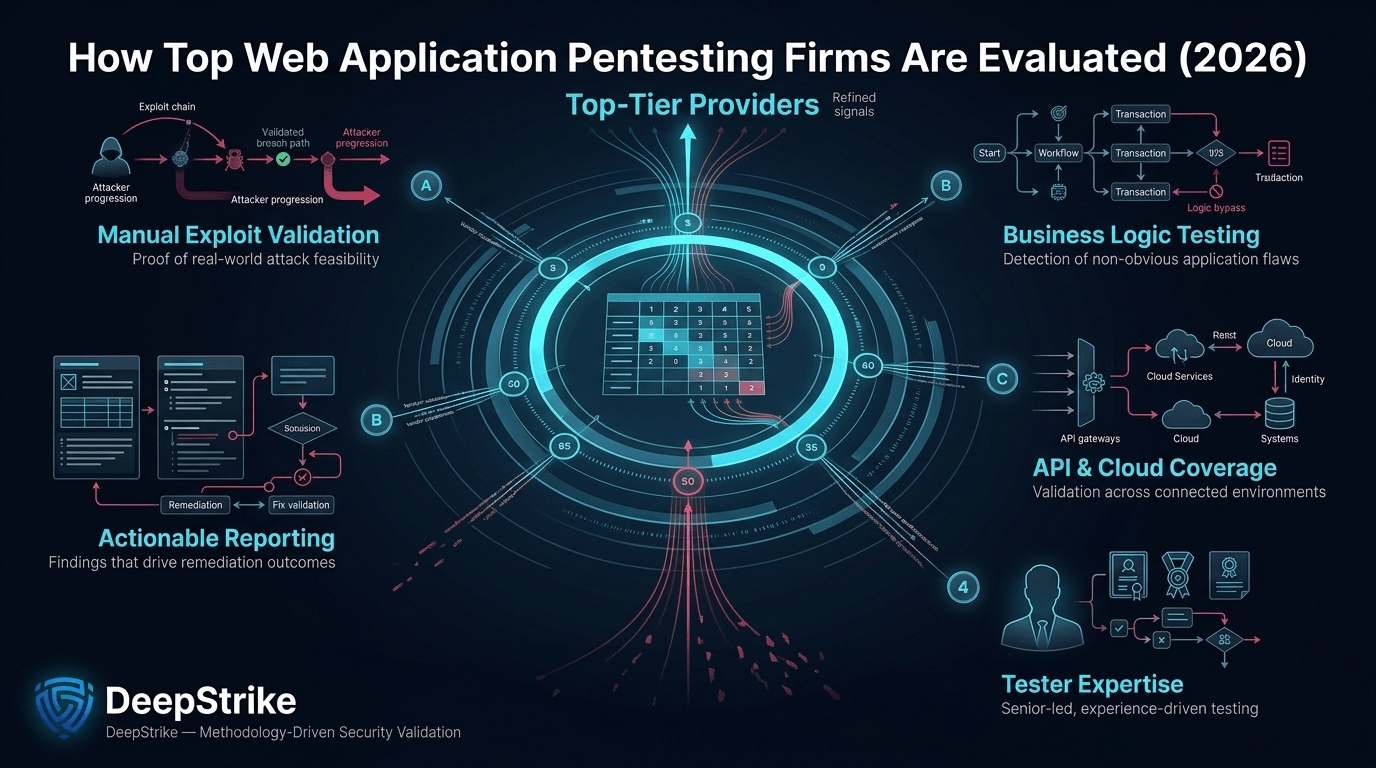
This methodology-led ranking of the best web application penetration testing companies in 2026 prioritizes what most directly changes security outcomes: manual exploit validation, business-logic depth, API and cloud-connected workflow coverage, tester seniority, and reporting that drives remediation.
Ultimately, the right provider depends on whether the buyer’s main priority is manual application-depth testing, PTaaS workflow efficiency, enterprise governance fit, or broader adversary-context validation. Buyers should evaluate providers based on demonstrable delivery behavior, tested application relevance, and remediation usefulness—not brand familiarity alone.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us