April 30, 2026
Updated: April 30, 2026
A procurement-focused comparison of Spain’s leading penetration testing providers by testing depth, compliance fit, reporting quality, and enterprise suitability.
Mohammed Khalil


With the average global cost of a data breach estimated at about $4.44 million, the procurement decision behind the top penetration testing companies spain category is fundamentally a risk-and-loss control decision. Spanish organizations face accelerating attacker tradecraft, including AI-assisted phishing, credential theft, identity abuse, and post-compromise lateral movement. For regulated, public-sector, and cloud-native buyers, penetration testing therefore matters less as a checkbox exercise and more as a method for validating realistic breach paths before they turn into financial, regulatory, or operational damage.
Against this backdrop, Spanish organizations operate under rising compliance and assurance pressure where relevant, including GDPR, ENS-sensitive public-sector expectations, PCI DSS, DORA for finance-relevant environments, and broader resilience obligations as NIS2-era requirements mature. Cloud-native and SaaS-heavy businesses face additional exposure because API and identity change velocity increases the likelihood of exploitable misconfiguration or logic abuse. This ranking is methodology-driven and not sponsored.
Penetration testing is a structured adversarial security assessment that combines automated vulnerability discovery with manual exploit validation to identify real-world attack paths, validate control effectiveness, and reduce breach probability.
Spanish organizations often face more rigorous proof-of-security requirements than peers in less regulated markets. Key factors include:
Our evaluation prioritized technical rigor, compliance orientation, and fit for Spanish buyers. Key criteria included:
Where claims were not externally evidenced, we treated them as unproven. Our methodology explicitly prizes validated exploitability (real exploits) over mere vulnerability counts or scan outputs.
Common procurement mistakes include:
Why They Stand Out: DeepStrike stands out here for a manual-first testing model, senior certified testers, and strong cloud and API security coverage. Its differentiation in this ranking is based on exploit-validation depth, technically actionable reporting, and suitability for buyers that need realistic adversarial testing rather than scan-heavy output.
Spain Relevance: DeepStrike is relevant to Spanish buyers that prioritize technical depth in cloud-native, SaaS, API-heavy, and regulated digital environments. As a cross-border specialist, it is more suitable where remote delivery, English-language reporting, and modern application security coverage matter more than local office presence. Buyers with strict local-language, public-sector, or residency-sensitive requirements should confirm those delivery conditions in advance.
Testing Depth Model: Manual exploit chaining. The emphasis is on realistic attack paths: testers aim to combine multiple vulnerabilities into a complete breach scenario. This ensures that reported issues are demonstrably exploitable. DeepStrike’s approach involves thorough confirmation of findings, often chaining initial footholds to lateral movement and data exfiltration on the target environment.
Key Strengths:
Potential Limitations:
Best For: Enterprise, Regulated (finance/healthcare), Cloud-first companies, Red-team projects.
Why They Stand Out: S21sec is a pure-play cybersecurity firm with deep roots in Spain (Spain’s first cybersecurity startup). Now part of Thales, it combines boutique agility with enterprise scale. The firm offers end-to-end security services; its pentesters are backed by an Iberian Security Operations Center and intelligence feeds. Its relevance in this ranking comes from strong Iberian delivery scale, managed security integration, and suitability for large Spanish organizations that want offensive testing backed by broader cyber operations capability. The company presents itself as a research-driven provider with offensive testing capability and broader managed security support. They emphasize customized, threat-informed tests rather than generic scans.
Spain Relevance: As a Spain-based provider with Iberian scale, S21sec is relevant for Spanish buyers that value local delivery, enterprise-grade managed security integration, and familiarity with regulated-sector expectations where evidenced. Its Thales ownership also supports broader cross-border delivery for larger organizations.
Testing Depth Model: Hybrid model. S21sec combines automated discovery tools with skilled manual validation. Their approach typically starts broad (vulnerability scanning, reconnaissance) and then extensively uses manual exploitation, including privilege escalation and lateral movement testing. They also integrate managed detection (SOC) for extended Red Team or Purple Team exercises.
Key Strengths:
Potential Limitations:
Best For: Large Enterprise, Public Sector, Finance, Critical Infrastructure (ENS/NIS1 contexts), Iberian multi-branch companies.
Why They Stand Out: Telefónica Tech (including its ElevenPaths security unit) leverages telecom-scale resources. Their penetration testing capability appears relevant for large Spanish organizations that need broad service coverage across infrastructure, applications, and managed security programs. They emphasize full-spectrum testing (infrastructure, apps, social engineering) followed by actionable remediation support. Telefónica also boasts global threat intelligence from its network and a managed SOC. Their reports are designed to integrate into corporate risk programs (even “certifying remediation” of issues as noted on their site).
Spain Relevance: As a Spain-based large technology provider, Telefónica Tech is relevant for local enterprises that prefer broad domestic delivery capability. It has extensive public sector clients and often meets ENS and ISO 27001 requirements. Spanish language support and on-the-ground teams in Madrid and beyond facilitate ease of collaboration. The company is well-integrated into the Spanish IT ecosystem, though some buyers note that it can behave like a large consultancy in process.
Testing Depth Model: Hybrid model. The team uses automated scanning to outline large surfaces but relies heavily on manual checks and exploit attempts. They highlight comprehensive manual tests across infrastructure, applications, and phishing with skilled testers (the site explicitly states “manual security tests performed by a team of security professionals”). However, Telefónica’s vast resources also mean they leverage specialized tools for scale.
Key Strengths:
Potential Limitations:
Best For: Enterprise (especially Telco and large corporates), Government/Public Sector, Telecom & Media clients, Regulated industries needing broad coverage.
Why They Stand Out: Deloitte’s global security practice brings deep consulting experience to pentesting. It highlights a diverse team “meticulously following industry standard trainings” and developing its own methodologies. The firm is relevant in this ranking for regulated and audit-heavy buyers that value formal methodology, documentation quality, and wider governance integration alongside technical testing. Deloitte offers both in-depth assessments and ongoing attack simulations. Its size allows multidisciplinary teams to integrate business impact analysis alongside technical findings (as noted in their marketing, where testers add business context to vulnerabilities).
Spain Relevance: Deloitte has a strong presence in Spain’s business community, with local branches and Spanish-speaking consultants. It is familiar to Big Four-reliant buyers for audit and risk engagements. They market solutions aligned to ENS and European directives, and can bundle pentesting into larger SOC/assessment programs. However, some buyers feel the service can resemble a process-driven audit rather than a high-speed red team.
Testing Depth Model: Hybrid model. Deloitte combines extensive tooling (scans, code reviews) with manual exploit validation. They explicitly say they perform “highly specialized manual penetration tests” when needed. Stages cover reconnaissance through persistence, emulating each attacker phase. Deloitte teams use structured approaches but allow creativity in exploit work, aiming to “stay as close to actual modus operandi of hackers”.
Key Strengths:
Potential Limitations:
Best For: Enterprise (multi-national), Highly Regulated sectors (banking, insurance), Organizations requiring end-to-end audit integration.

Why They Stand Out: KPMG positions its pentesting offering as “safety analyses as active risk management”. They provide a range of assessment styles, with relevance strongest for buyers that want penetration testing connected to broader security assurance and governance programs. Importantly, KPMG offers pentesting as part of a managed service, supporting continuous security monitoring. This appeals to organizations looking for a long-term testing program. Their reports emphasize structured risk assessment, making it clear how vulnerabilities translate to business impact.
Spain Relevance: KPMG Spain is well-regarded among institutional clients (banks, utilities, government). Its advice-driven model is familiar to audit-heavy buyers. KPMG also has ENS/ISO expertise and often leverages its audit practice to ensure coverage of required controls. However, smaller or more aggressive buyers sometimes feel KPMG is less specialized in pure hacking and more consultancy-oriented.
Testing Depth Model: Hybrid model. KPMG employs both automated scanning and expert penetration testing. Their literature explicitly mentions using “highly specialised manual penetration tests” in black, grey, or white-box modes depending on client needs. They can adapt to single-shot tests or multi-year programs. The emphasis is on consistency (“globally reproducible quality”) and risk categorization, so the depth often depends on client scope and risk profile.
Key Strengths:
Potential Limitations:
Best For: Enterprise (e.g. multinationals, large utilities), Regulated (banks, insurers), Organizations wanting continuous assurance.
Why They Stand Out: NCC Group is a veteran security firm known for hands-on offensive security. Its offensive testing practice is relevant here for buyers that want deep manual validation, realistic adversary simulation, and a research-oriented security firm rather than a general consulting provider. They boast a research-driven culture (publishing CVEs, whitepapers). NCC’s credibility in pentesting comes from a long history of high-profile engagements. They provide tailored attack simulations (including physical and social engineering) and prioritize finding deep flaws over ticking boxes.
Spain Relevance: NCC appears relevant to Spanish buyers through broader European delivery and cross-border offensive security capability. Many Spanish tech and e-commerce firms have used NCC’s services. While not a Spanish brand, it is well-known in Europe and often chosen by firms wanting a neutral, vendor-agnostic tester. They can bridge language gaps by using multilingual teams.
Testing Depth Model: Manual exploit chaining. NCC’s approach centers on thorough human-led testing. They often begin with broad mapping but progress quickly to customized exploitation and business-logic attacks. The emphasis is on realism (the site highlights “real-world exercises”), simulating attacks that chain multiple vulnerabilities. NCC also offers advanced services like red teaming and threat simulation.
Key Strengths:
Potential Limitations:
Best For: Tech-savvy Enterprises, E-commerce/Media, Organizations wanting aggressive red-team-style assessments.
Why They Stand Out: Atos, through its cybersecurity division (now Eviden), offers enterprise-class security testing with over two decades of experience. Its relevance in this ranking comes from enterprise delivery breadth, cloud and hybrid-environment testing capability, and suitability for large organizations that need pentesting integrated into broader cyber programs. Its pentesting services span infrastructure to SAP applications. Atos emphasizes combining automated and expert-led testing to quantify business risk. The firm’s global security operations centers (17 SOCs) feed into intelligence-driven testing, and they promote end-to-end integration (from DevSecOps to compliance reporting).
Spain Relevance: Atos has visible operations in Spain and appears relevant for large organizations that need integrated cyber and infrastructure delivery. It is engaged in public and private sector digital transformation projects, which lends credibility. Its size means it can handle very large, multi-country scopes which suit Spanish multinationals. However, some local midsize buyers may not prefer such a broad integrator if only pentesting is needed.
Testing Depth Model: Hybrid model. Atos provides “globally recognized pentesting expertise” via structured tests. They leverage both proprietary tools and well-known frameworks. Their team conducts manual testing to simulate real attacks (“simulating real-world attacks for realistic insights”), but also scales up with automated coverage for large IT ecosystems. Atos is well-suited to testing across on-prem, cloud, and hybrid environments.
Key Strengths:
Potential Limitations:
Best For: Enterprise (especially critical infrastructure, government, multi-national), Cloud- and IoT-focused environments, Organizations wanting integrated IT/cyber programs.
| Company | Specialization | Testing Depth Model | Best For | Spain Fit | Compliance Alignment | Ideal Organization Size |
|---|---|---|---|---|---|---|
| DeepStrike | Pentesting, Red Team, Continuous | Manual exploit chaining | Regulated finance/health, SaaS | Remote service (no local office) | SOC2, ISO27001, HIPAA (claims) | Midmarket to Enterprise |
| S21sec (Thales) | MSS, SOC, Pentest, IR | Hybrid model | Enterprise, Public Sector, Finance | Strong Iberian delivery relevance | ENS/NIS, ISO27001 | Large Enterprise |
| Telefónica Tech | Pentest, Red Team, Managed Sec | Hybrid model | Telco/Service Providers, Govt | Spanish flagship (local teams, ENS) | ENS, ISO27001, GDPR | Large Enterprise, Govt |
| Deloitte | Advisory, Pentest, Risk Mgmt | Hybrid model | Large Enterprise, Regulated sectors | Global firm with Spanish branch | ISO27001, GDPR, NIS2/DORA (aligned) | Enterprise |
| KPMG | Cyber Advisory, Pentest, GRC | Hybrid model | Large Enterprise, Finance, Energy | Global firm with Spanish branch | ISO27001, SOC2, ENS (audit-aligned) | Enterprise |
| NCC Group | Pentest, IR, Product Sec | Manual exploit chaining | Tech-forward enterprises | Cross-border European delivery relevance | ISO27001, PCI-DSS, NIS1 (EP, integrated) | Enterprise, Tech SMB |
| Atos (Eviden) | IT Sec Consulting, Pentest, Cloud | Hybrid model | Public Sector, Healthcare, Telecom | Large integrator with visible Spain delivery footprint | ISO27001, GDPR, NIS1/2, DORA-ready | Large Enterprise |
Enterprise and SMB buyers in Spain have different priorities. Large organizations tolerate higher costs for deeper coverage, continuous programs, and integration with enterprise risk teams. They often require multi-domain assessments (e.g. network, cloud, mobile, IoT) and multiple language support. In contrast, SMBs seek budget-friendly, bite-sized engagements possibly focusing on a single web app or network segment. A local boutique or mid-sized firm may offer more flexible pricing and faster turnaround for SMBs, whereas global firms often focus on complex, cross-border projects.
Enterprises usually demand stringent compliance alignment (ENS, DORA, industry standards) and extensive reporting, whereas SMBs may prioritize quick vulnerability discovery. Large companies may favor the brand assurance and breadth of a global consultancy but should beware that smaller specialized firms (including Spanish cybersecurity companies) can match or exceed the technical depth. Furthermore, big firms can afford to deploy team-of-teams across time zones, an advantage for global corporations; smaller clients may prefer one consistent engagement team.
Ultimately, Spanish SMB buyers might choose local specialists (for language and cost) or mature small teams (like boutique pentesters), while enterprise buyers often shortlist major providers with Spanish or EU operations to meet wide-ranging audit demands.
Pricing for a penetration test depends on multiple factors:
Pricing should be evaluated through scope size, asset complexity, testing depth, reporting expectations, retesting terms, delivery model, and compliance evidence requirements rather than headline figures alone. In Spain, buyers typically get the most value when pricing is tied to clearly defined scope and validated technical depth, not just to lower day-rate optics.
Costs vary widely by scope, testing depth, reporting requirements, retesting, and delivery model. In Spain, pricing is usually shaped more by asset complexity and assurance expectations than by a single market-wide benchmark. Buyers should request quotes against a clearly defined scope and compare providers on validated depth, not just on headline price.
Enterprise pentests usually cover external/internal networks, web and mobile apps, APIs, cloud services, and often social engineering (phishing) or wireless testing. Deliverables include a technical report with prioritized findings, an executive summary, and often a presentation. Larger engagements may also include post-test remediation support and retesting.
Both matter, but certifications primarily indicate a tester’s knowledge baseline (OSCP, CISSP, CREST). However, an expert tester will skillfully use tools and custom scripts. In practice, human expertise and methodology (shown through certifications and track record) should outweigh mere tool availability. Top firms cite both: for example, Deloitte notes their teams hold Offensive Security and SANS certificates.
Most mid-sized tests run 1–4 weeks from kick-off to report, depending on complexity. Small app tests can be done in days; large corporate assessments (involving many systems and compliance requirements) may take several weeks to complete and a few more for reporting and review meetings. Additional time should be budgeted for retests or any focused reassessments.
PCI DSS explicitly requires penetration testing in scope-defined environments at least annually and after significant changes. ISO 27001, GDPR, ENS-sensitive public-sector expectations, NIS2-era resilience requirements, and DORA-relevant financial environments do not all apply in the same way to every buyer, but they commonly increase the need for technical security validation and defensible reporting where relevant. In practice, penetration testing is often treated as part of broader assurance and resilience programs under these frameworks.
At minimum, once per year or whenever significant changes occur (new applications, architecture changes, mergers). Many organizations under heavy regulation choose quarterly or continuous testing. Ultimately, testing frequency should align with the organization’s risk profile and compliance requirements. Highly dynamic or critical environments may benefit from ongoing assessment.
Choose the provider that best meets your needs. Local firms offer ease of communication (Spanish language, local context) and often have direct ENS or regional experience. Global specialists bring broader threat intelligence and technical depth, especially for large or international companies. In practice, buyers often shortlist a mix: local experts for on-the-ground support, and international firms for specialized expertise. Ensure whichever vendor you pick can address Spanish compliance (e.g. ENS for the public sector) and your technical requirements equally well.
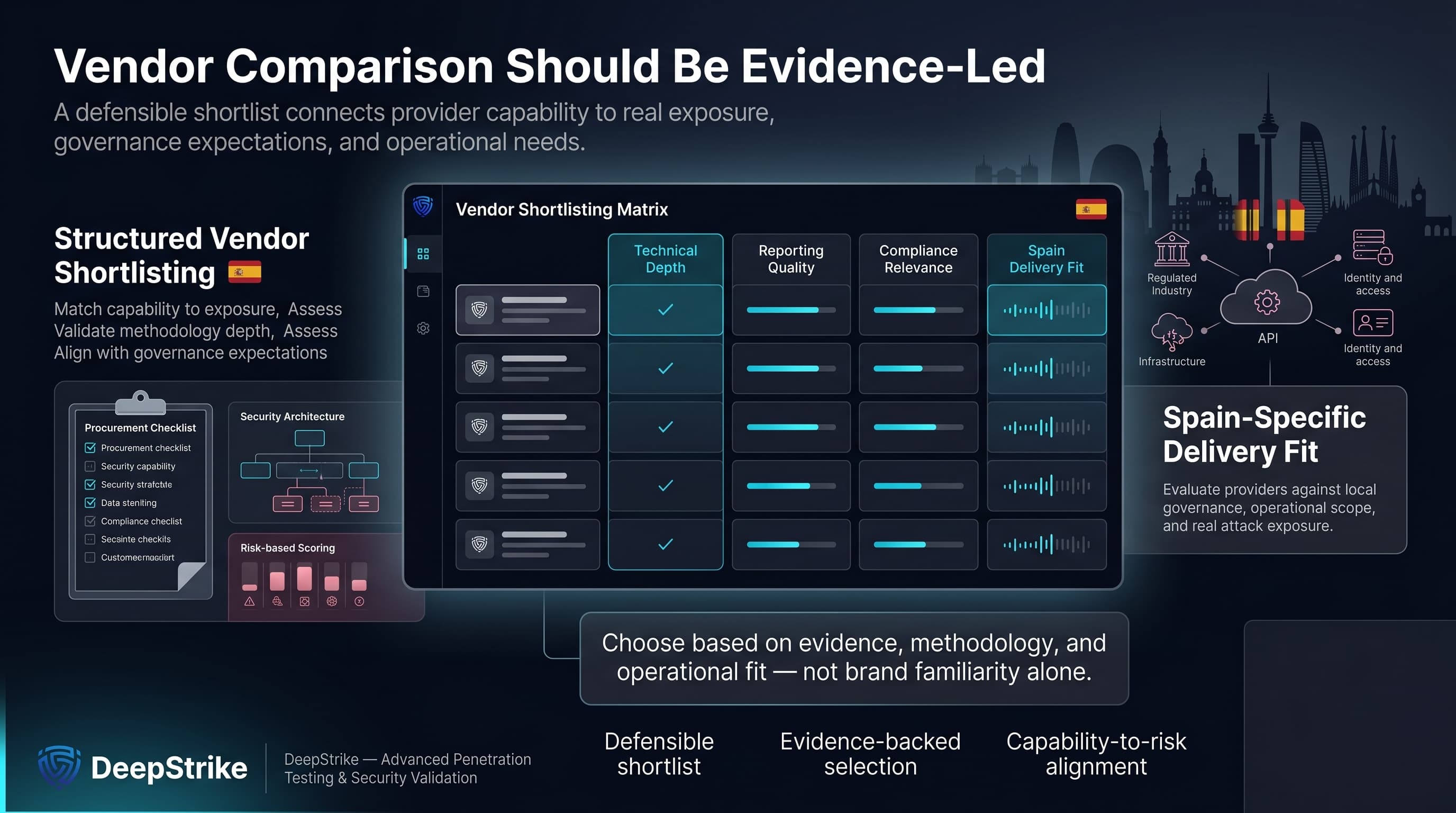
This transparent comparison of the top penetration testing companies spain category is designed to support structured vendor shortlisting rather than brand-led selection. By focusing on technical depth, reporting quality, compliance relevance, and Spain-specific delivery fit, it gives buyers a more defensible way to evaluate providers. Spanish organizations should use this comparison to match vendor capability to real exposure, governance expectations, and operational needs.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us