June 3, 2025
Updated: March 29, 2026
A practical guide to PHI-focused security testing, realistic attack paths, remediation, and healthcare risk validation.
Mohammed Khalil

HIPAA penetration testing is a high-assurance validation activity that goes beyond checklists to actively probe healthcare systems for PHI exposure. It’s not enough to “run a pentest” as a one-off task; organizations must carefully scope the right systems, simulate realistic attack paths, document evidence, and drive defensible remediation. In practice, healthcare environments combine web applications, APIs (including FHIR/HL7), cloud services, identity and access controls, and third-party integrations in ways that can significantly affect PHI. Testing must cover patient portals, EHR-connected applications, mobile apps, authentication/MFA flows, remote access pathways, privileged admin interfaces, cloud misconfigurations, and more. Effective HIPAA pentesting focuses on how real attackers could exploit identity compromise, API abuse, or workflow flaws to access or exfiltrate PHI. Done properly, it helps validate whether key safeguards actually hold up under realistic attack conditions and whether PHI exposure paths have been meaningfully reduced.
Definition
HIPAA penetration testing refers to the structured security assessment of applications, APIs, identity pathways, privileged workflows, and supporting infrastructure used in healthcare environments that create, receive, maintain, or transmit protected health information, with the goal of identifying exploitable weaknesses, validating realistic attack paths, and supporting more defensible technical risk reduction.
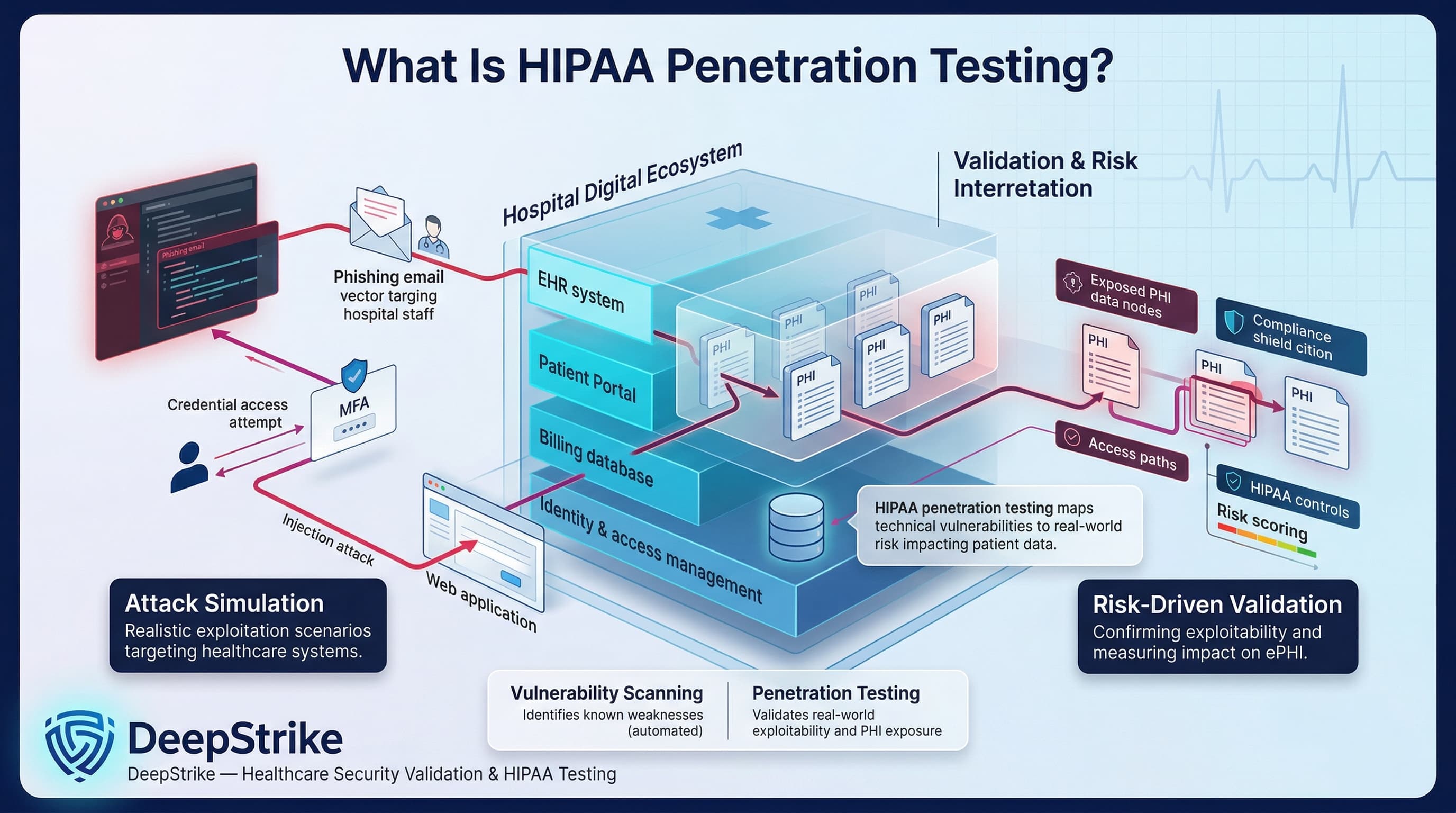
HIPAA penetration testing is the practice of simulating realistic cyberattacks on healthcare systems that handle PHI, in order to find and confirm security weaknesses. It differs from a generic pentest in its focus on PHI exposure and healthcare workflows. For example, a standard pentester might find a SQL injection vulnerability on a web server; a HIPAA-focused test would take it further by demonstrating how that flaw could expose patient records in an EHR or billing database. Vulnerability scanning (automated tools) can identify known issues, but penetration testing goes deeper. As NIST explains, security testing (including pentests and scans) is used to find vulnerabilities and verify compliance with security policies. HIPAA-oriented pentesting interprets findings through the lens of the Security Rule’s risk framework. In other words, rather than a simple checklist, HIPAA penetration testing is a risk-driven activity tailored to the healthcare environment. It might involve scenario-based attacks on patient portals, phishing attempts against hospital staff to test MFA, or exploiting EHR integration points to confirm how much PHI could be accessed. In a strong HIPAA pentest, testers validate exploitability of vulnerabilities rather than just listing them, and they explain the impact on ePHI. This approach aligns with risk management: finding out how an attacker could gain PHI and determining how that scenario maps to HIPAA controls.
HIPAA’s Security Rule does not explicitly say “you must perform an annual penetration test.” Instead, it mandates broad risk management obligations. For example, HIPAA requires covered entities and business associates to conduct an accurate and thorough risk analysis of all e-PHI, and to implement safeguards to reduce those risks. It also requires a periodic “technical and nontechnical evaluation” of security policies (45 C.F.R. §164.308(a)(8)). These provisions imply that organizations must review their security controls, but they do not prescribe specific methods. In practice, penetration testing is often treated as a strong way to satisfy these requirements. Organizations should distinguish regulatory requirements from best practices: under today’s HIPAA, current rule language does not explicitly prescribe penetration testing as a fixed standalone requirement, but regulated organizations are required to document their risk analysis and control evaluations. Conversely, a pentest is widely regarded as a risk-based best practice that provides evidence of control effectiveness, not a free ticket to compliance on its own. Recent guidance underscores this view: NIST’s HIPAA Guide notes that organizations should consider penetration testing “if reasonable and appropriate” during security evaluations. Moreover, in late 2024 HHS proposed a rule that, if adopted, would explicitly require regulated entities to conduct vulnerability scans semi-annually and penetration tests at least annually. (This NPRM is not final law yet, but it signals the increasing emphasis on testing.) In summary, HIPAA requires risk analysis and control evaluation; penetration testing is a practical method to meet those goals, but not an explicitly prescribed action in the current rule.
A penetration test does not prove full HIPAA compliance on its own. It does not replace required risk analysis, workforce training, policy development, vendor oversight, incident response planning, or administrative and physical safeguards. It validates selected technical attack paths within the defined scope and test window. Findings should therefore be interpreted as one input into broader HIPAA-aligned security governance, not as stand-alone proof of compliance.
Penetration testing is one component of a broader healthcare security program. It does not replace policy controls, logging, continuous monitoring, training, or formal HIPAA risk analysis, but it adds technical validation that those safeguards are working as intended.
| Attribute | Penetration Testing | Vulnerability Scanning | HIPAA Risk Analysis |
|---|---|---|---|
| Primary Goal | Actively exploit weaknesses to assess real impact on PHI | Identify known security issues across systems | Identify and prioritize risks to e-PHI |
| Depth of Validation | In-depth manual testing of business logic and chaining attacks | Automated, broad sweep for missing patches, CVEs | Broad organizational review (assets, threats) |
| Exploitability Focus | High attempts actual exploit to prove impact | Low reports vulnerable components without exploit | Not directly evaluates likelihood/impact |
| Output | Validated vulnerabilities with attack paths, evidence (screenshots, logs) | List of flagged vulnerabilities and misconfigurations | Risk findings, risk levels, and recommended safeguards |
| Compliance Relevance | Demonstrates control effectiveness and supports technical evaluation requirement | Supports some policies (e.g. network scans) but lacks proof of fix | Required by HIPAA (45 CFR 164.308(a)(1)(ii)(A)); informs all other safeguards |
| Main Limitation | Resource-intensive, limited coverage (often targeted scope) | False positives, no business context, may miss logic flaws | High-level; may lack technical depth or missed blind spots |
Healthcare organizations often need all three. Vulnerability scans provide regular breadth, risk analysis ensures all PHI is accounted for in policy, and penetration testing provides depth by confirming what an attacker can actually do. Each serves a different role in a compliant security program.
| Scope Area | Why It Matters | Typical Test Focus | Common Weakness Pattern |
|---|---|---|---|
| Patient Portals & Web Apps | Entry point for e-PHI (scheduling, records, billing) | Authentication bypass, input validation, IDOR, session hijacking | Broken access controls (IDOR), SQL/XSS allowing PHI read |
| EHR & Administrative Interfaces | Contains core patient records and admin functions | Credential brute force, privilege escalation, business logic | Default/weak admin credentials; excessive privileges |
| APIs (FHIR/HL7, REST) | Exposes data and services between systems | API key/token misuse, broken object level authorization, parameter tampering | Excessive data exposure, token replay, lack of rate limiting |
| Mobile Apps | Patient and clinician access to PHI | Local storage encryption, insecure network calls, code tampering | Hard-coded secrets, weak SSL/TLS, jailbreak/root detection bypass |
| Authentication & MFA Flows | First line of defense for system access | Multi-factor bypass, session fixation, reset/forgot password | No MFA on critical accounts, predictable password reset logic |
| Remote Access (VPN, RDP, Citrix, etc.) | Bridges internet to internal network (often PHI stores) | Open ports scanning, credential stuffing, misconfigured gateways | Unpatched VPN, missing two-factor on RDP, open SSH/RDP to internet |
| Cloud Infrastructure & Identity | Hosts data and services (IaaS, PaaS, container) | IAM roles and permissions review, storage bucket access, metadata API | Over-permissive IAM policies, public S3 buckets, exposed keys |
| Third-Party Integrations & BAs | External partners may handle PHI or access systems | Testing of vendor systems, federation trusts, API endpoints | Trust assumptions, lack of strong authentication (e.g. open trust lines) |
| Email & Collaboration Tools | e-PHI often flows in messaging and document sharing | Phishing simulations, misconfigured sharing permissions | Open mail forwarding, public document links, no MFA |
Penetration testing must address all interfaces where PHI resides or travels. The scope should reflect the organization’s environment: a hospital network with local EHR servers will differ from a SaaS telemedicine platform in the cloud, but in each case the above areas will be adapted to the specific architecture.
| Organization Type | Typical Testing Priorities | Common Scope Pitfalls | Notes |
|---|---|---|---|
| Covered Entities (Health Systems, Providers) | Internal medical networks, EHR databases, clinical apps, staff devices, patient portals, remote access | Failing to test legacy or specialized medical systems; overlooking third-party services (e.g. cloud labs); incomplete asset inventory | Must test all ePHI flows. Often share responsibility with IT vendors; healthcare regulations (e.g. Meaningful Use) also drive risk assessments. |
| Business Associates (Vendors, Insurers) | Customer-facing platforms (SaaS EHR, billing systems), development environment, APIs handling client PHI | Assuming covered entity handles all security; not testing data separation in multi-tenant apps; ignoring subcontractors | BAs must align with CE’s risk analysis. Contracts/BAAs usually require security assurance. Proposed HIPAA rules would require annual security reviews by experts. |
| Cloud-hosted Healthcare Software (SaaS/EHR) | Cloud IAM, API endpoints, tenant isolation, orchestrated services | Overlooking cloud platform config (relying on provider defaults); not testing onboarding flows for new customers; ignoring underlying shared services | In shared models, ensure pentest includes provider-managed layers as allowed. Verify encryption, backups, and failover processes. |
| Hospital/Clinical Operations (Large Facilities) | Network segmentation, OT/IoT devices (e.g. infusion pumps), remote telehealth systems, clinical admin apps | Only testing public-facing apps but not network seg or wireless; ignoring medical device interfaces that handle PHI | Unique focus on operational continuity. Test emergency access scenarios and integration points to medical equipment if they interact with EHR. |
Scope planning must account for shared responsibilities. For instance, a hospital IT team (Covered Entity) might focus on clinical networks and user access, while a cloud-based EHR vendor (Business Associate) focuses on multi-tenant data controls. Testing must ensure that when PHI passes between these domains, the interfaces are secure.
Each of these scenarios focuses on an attacker goal (typically unauthorized PHI access or exfiltration) and shows a likely path through healthcare-specific systems. Understanding them helps define realistic pentest activities and highlights why protecting PHI requires more than just standard IT security measures.
| Security Domain | Why It Matters | Typical Evidence of Weakness | Business / Compliance Consequence |
|---|---|---|---|
| Authentication & Session | Compromised logins are a common breach vector; protecting login flows prevents unauthorized PHI access | Missing MFA on critical systems; default or weak passwords; session tokens not invalidated on logout or idle timeouts | Unauthorized data access; non-compliance with MFA/addressable specs |
| Authorization & Privilege | Fine-grained access control ensures users only see allowed PHI | Users granted excessive roles; lack of role separation; “Admin” rights misassigned | Insider data leaks; HIPAA minimum necessary violations |
| API Security | APIs often handle large-scale PHI transfer; any flaw can magnify breach impact | Broken Object Level Authorization (BOLA); insecure default API credentials; missing encryption in transit | Bulk data breach; non-compliance with transmission and integrity rules |
| Application Logic & PHI Exposure | Business workflows (patient lookup, referral) must enforce controls | Predictable patient IDs; verbose error messages revealing PHI; logic that combines unrelated data | Silent data exposure; difficulty meeting audit requirements for access logs |
| Cloud Identity & Access Management | Cloud misconfigurations (e.g. IAM roles) can leave PHI unprotected | Overly permissive IAM roles or groups; lack of MFA for cloud accounts; no logging of admin actions | Data breach via cloud tenant; failure of access control implementation |
| Remote Access | Remote connections often bridge to on-prem PHI systems | Open RDP/SSH without controls; VPN split-tunneling; no network-level MFA | Unauthorized network intrusion; exposure of internal data |
| Network Segmentation & Data Flow | Proper segmentation limits impact of breach (e.g. isolating EHR network) | Flat network allowing unrestricted access to servers; misrouted traffic between patient care and admin networks | Lateral movement in breach; complicates incident containment |
| Logging & Detection | Even the best defenses fail; logs help spot or forensically analyze breaches | Missing or incomplete audit logs; no alerting on abnormal access patterns; disabled logging on critical systems | Late breach discovery; inability to prove compliance during audits |
| Secrets Management & DevSecOps | Leaked credentials or keys let attackers bypass security entirely | API keys or DB passwords in code repositories; no key rotation; insecure CI/CD pipelines | Full system compromise; broad e-PHI exposure |
| Configuration Management | Misconfigurations often introduce new vulnerabilities (e.g. open ports) | Insecure default settings; outdated middleware/plugins; unpatched systems | Known exploits available to attackers; regulatory findings for poor patching |
| Third-Party Trust Boundaries | Trusting external systems or partners expands the attack surface | Open trust relationships (e.g. unconstrained cross-origin calls); lack of contractually enforced audits | Breach via vendor; joint responsibility issues, increased liability |
A robust HIPAA penetration test should systematically cover these domains because weakness in any one of them can materially affect PHI exposure. Coverage across these areas produces stronger technical assurance, but it should still be interpreted alongside broader risk analysis and governance activities.
Penetration testing feeds into risk management and security governance by providing concrete evidence of how technical controls perform under realistic attack conditions. Findings can help leadership prioritize remediation, validate assumptions in the risk analysis, and track whether critical weaknesses were actually fixed. The value of a penetration test in governance comes from evidence quality, scope discipline, and follow-through on remediation, not from treating the test itself as proof of compliance.
A high-quality HIPAA penetration testing program avoids these failures through disciplined scope design, manual validation, and clear reporting tied to patient-data risk.
A strong penetration testing report turns technical findings into actionable insight aligned with HIPAA. Key elements include:
NIST guidance also emphasizes documentation: “Document each evaluation finding, as well as remediation options, recommendations, and decisions”. In practice, a weak report undermines even real security testing. Without clear scope, evidence, and impact analysis, stakeholders cannot act confidently on the findings. A high-quality HIPAA pentest report becomes an input into the organization’s security governance and compliance evidence.
Testing frequency should be risk-based rather than fixed to a single universal schedule. Many organizations test critical healthcare environments at least annually, with additional testing after major application changes, cloud migrations, new integrations, or material shifts in PHI exposure. Vulnerability scanning, configuration review, and change-driven testing can occur more frequently, but penetration testing should be scheduled where it provides meaningful validation of real attack paths.
HIPAA itself does not currently prescribe a fixed annual penetration testing requirement. Organizations should therefore base testing frequency on exposure level, sensitivity of e-PHI, pace of change, and the results of formal risk analysis. Proposed HHS rulemaking has signaled increased emphasis on regular testing, but current practice should still be framed as risk-driven governance rather than a single mandated calendar rule.
These practices keep penetration testing focused on real healthcare risk rather than broad but low-value technical coverage.
For senior stakeholders, HIPAA penetration testing is as much a governance issue as a technical one. Procurement teams should include explicit security testing requirements in RFPs and contracts with IT and healthcare vendors. A qualified penetration test provider should have healthcare domain expertise (understanding EHR systems, PHI flows, regulatory needs) this ensures they scope tests correctly and interpret findings in a compliance context. Certifications like CISSP, OSCP, or healthcare-specific training can be indicators of credibility.
CISOs and compliance leaders can use penetration test results in board reports to demonstrate due diligence. A well-structured report (with executive summary highlighting PHI risk) provides clear metrics on security gaps and progress over time. This transparency can support more credible governance reporting to partners, customers, and oversight stakeholders by showing that security is being actively measured and managed.
From a risk committee perspective, test outcomes become part of enterprise risk assessments. Critical findings (e.g. a flaw that exposes large volumes of e-PHI) might trigger shifts in risk appetite or new investments (such as additional encryption or monitoring tools). Conversely, clean results can justify focusing resources elsewhere.
Procurement and legal teams will also use penetration test policies in business associate agreements and supplier evaluations. For example, they may require evidence that cloud services undergo regular pen tests. This turns technical quality (the thoroughness of testing) into a business criterion.
Ultimately, high-quality penetration testing affects vendor selection and security assurance. A vendor that restricts meaningful testing or produces weak, generic reporting should raise concern. By contrast, well-executed testing can strengthen security defensibility and demonstrate that technical safeguards were actively evaluated. In breach scenarios, a documented history of testing and remediation may support a more credible governance posture, but it should not be framed as guaranteed protection from regulatory scrutiny or enforcement.
HIPAA penetration testing is a security assessment tailored to healthcare. It involves simulating attacks on systems that create, receive, or transmit protected health information (PHI) such as patient portals, EHR platforms, mobile apps, and APIs. The goal is to find and exploit vulnerabilities in the context of healthcare workflows, thereby validating how exposed PHI could be. Unlike a general pentest, it specifically focuses on the risk to patient data and regulatory controls.
No, HIPAA’s Security Rule does not explicitly mandate an annual or periodic penetration test. Instead, it requires covered entities and business associates to conduct a thorough risk analysis and to periodically evaluate their security controls. Penetration testing is a recognized risk-based practice to satisfy those evaluation requirements, but it is not the only way to comply. (Notably, a 2024 HHS proposal would require annual penetration tests in the future, but that is not yet law.)
Vulnerability scanning uses automated tools to quickly identify known software flaws, missing patches, and misconfigurations. It’s broad and fast but can only report potential issues. Penetration testing, on the other hand, is a manual, targeted process where testers actually exploit vulnerabilities to demonstrate impact. In other words, a scan might tell you about a weak TLS version; a pentest will show if that weakness can be chained to steal patient data. For HIPAA, pentesting adds value by confirming which vulnerabilities can truly lead to PHI exposure.
Any system that processes or stores electronic PHI (e-PHI) is in-scope. Common targets include web application security testing and mobile apps, EHR and healthcare applications, APIs (e.g. FHIR/HL7 interfaces), user authentication and SSO systems, remote access services (VPN, RDP), privileged admin portals, cloud-hosted infrastructure (servers, databases, storage), and interfaces with third-party vendors (labs, billing partners). Email systems or collaboration tools may also be included if they carry PHI. The specific scope depends on the organization’s environment, but it must reflect the flow of PHI through all relevant digital systems.
Testing frequency should be risk-based. Many organizations test critical systems at least annually, with additional testing after major application changes, new integrations, cloud migrations, or material changes in PHI exposure. The right schedule should follow the organization’s risk analysis rather than a single fixed rule.
A penetration test can support HIPAA compliance by validating technical safeguards, but it does not prove compliance on its own. It should be treated as one input into risk analysis, control evaluation, remediation, and broader security governance.
A strong report will have clear scope and rules of engagement, a summary of tested assets, and for each finding it should include the evidence (e.g. exploit screenshots or logs) and a description of PHI risk. It should explain the business impact (for example, “this flaw could allow access to X patient records”). Remediation guidance should be provided for each issue, prioritized by risk. An executive summary (focusing on PHI exposure and overall risk level) should be separated from the technical details so that both leaders and engineers can act on it. Importantly, findings should be tied back to HIPAA concerns: for example, noting which security control was violated.
A HIPAA risk assessment (risk analysis) is a mandatory process that identifies all threats and vulnerabilities to e-PHI across the organization. It is a broad review (including administrative, physical, and technical safeguards) and must be documented to comply with the Security Rule. Penetration testing is a narrower, technical activity that attempts to exploit vulnerabilities to confirm their impact. In short, risk analysis decides what needs protection and how big the risks are, while penetration testing actively tests whether the protections work in practice. They complement each other: pentest findings should feed into the overall risk assessment, but a risk analysis covers many additional factors (like policy gaps) that a pentest does not.
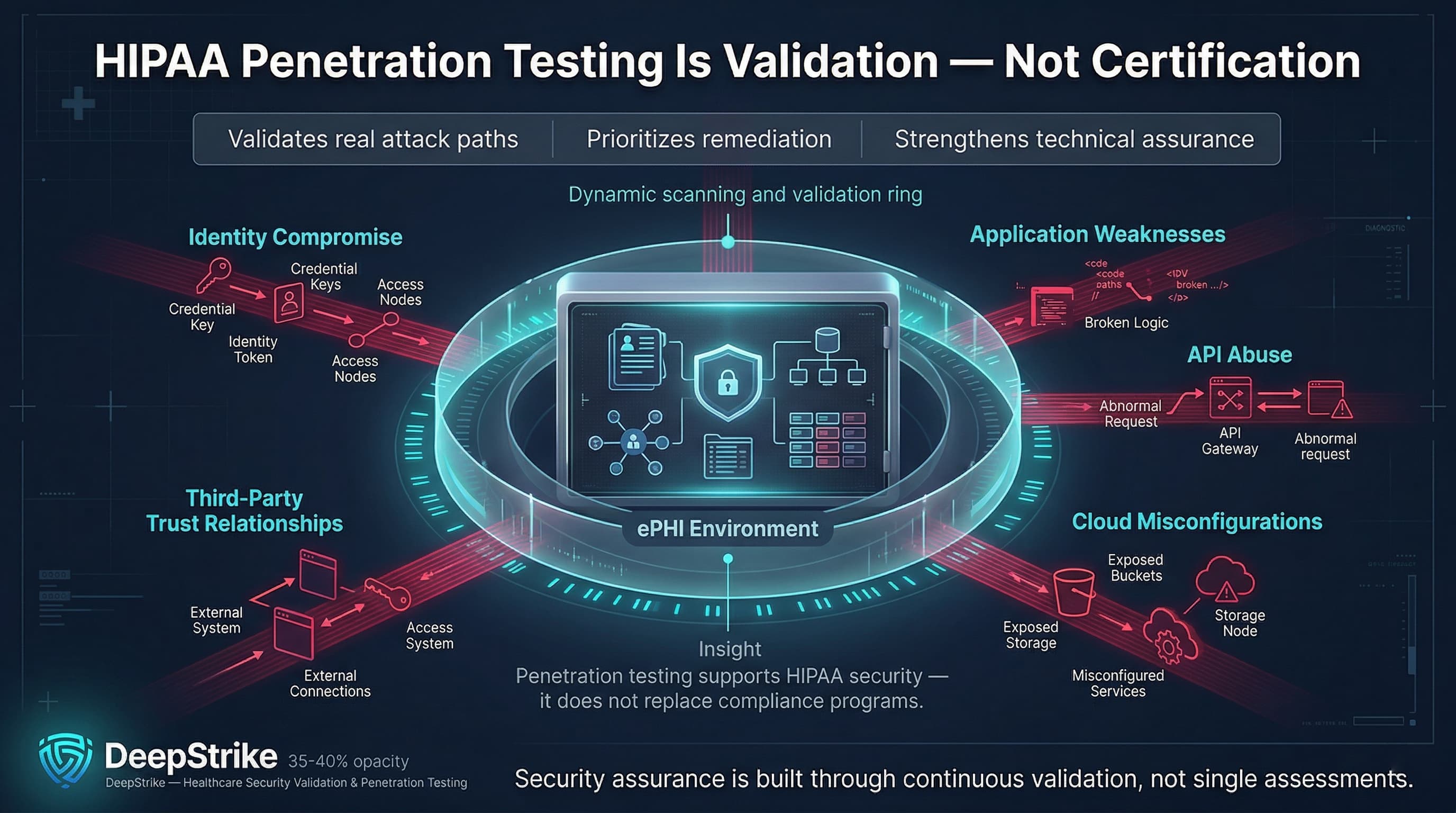
HIPAA penetration testing should be treated as a high-assurance technical validation exercise for environments that create, receive, maintain, or transmit e-PHI. Its value lies in showing how identity compromise, application weaknesses, API abuse, cloud misconfigurations, and third-party trust relationships could lead to real data exposure. A mature healthcare organization uses penetration testing to validate risk assumptions, improve remediation priorities, and strengthen technical assurance over time. Still, penetration testing should be treated as one component of HIPAA-aligned security assurance rather than a stand-alone proof of compliance.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us