March 5, 2026
Updated: March 5, 2026
How automated pentesting works, where it excels, and why human-led testing still matters for discovering complex attack paths.
Mohammed Khalil
Automated penetration testing is now essential in defending rapidly evolving infrastructures. IBM’s 2025 breach report notes the global average cost of a data breach at $4.4 million a 9% drop driven by faster detection, while industry data show 40,009 new software vulnerabilities were disclosed in 2024 alone. In this landscape of rampant ransomware. see recent ransomware attack statistics and sprawling cloud/microservices/API environments and mounting cloud security compliance challenges, security teams must validate defenses continuously. Automated pentesting tools can shorten the time to find and contain bugs, but they do not eliminate the need for skilled attackers emulation or guarantee that no breach will occur. Instead, they complement traditional testing by accelerating discovery across complex, dynamic attack surfaces.
Automated Penetration Testing is a security validation approach that uses automated tools to simulate attacker techniques, identify exploitable vulnerabilities, and validate potential attack paths across applications, networks, and cloud environments.
Modern development and infrastructure changes have outpaced annual manual testing. In DevOps environments, code and configurations change daily, yet traditional pen tests run only periodically quarterly or annually. By contrast, automated pentesting can be performed on every build or on demand, giving security teams an “always on” view of risk. Cloud adoption and the API economy have vastly expanded the attack surface: every new microservice or container can introduce misconfigurations or secrets leakage. Automated tools can continuously enumerate cloud assets and scan containers or APIs as they spin up. Identity based attacks are also on the rise: for example, tools can automatically check Active Directory configurations and exposed credentials across on prem and cloud directories, a task too laborious for manual testers alone.
Frameworks and guidelines underscore this need. NIST SP 800 115 notes that “no one technique can provide a complete picture of the security of a system”, urging organizations to combine automated scanning with manual techniques for a robust assessment. OWASP likewise highlights that scanners typically find only common vulnerabilities, missing complex logic flaws or chained exploits. In practice, that means automation is critical for breadth and speed, but must be supplemented by human creativity. In fast moving environments, automated pentesting keeps pace with releases, while scheduled manual tests lag far behind if a vulnerability is introduced on day one of a sprint, waiting six months for the next pen test can leave an organization exposed to attack.
Automated penetration testing aligns with several widely recognized cybersecurity frameworks that emphasize continuous security validation.
NIST National Institute of Standards and Technology recommends combining automated and manual testing techniques to obtain a comprehensive security assessment. NIST SP 800-115 notes that no single testing method provides a complete view of system security.
OWASP highlights the limitations of automated scanning in identifying complex application vulnerabilities. The OWASP Testing Guide recommends combining automated scanning with manual penetration testing to uncover business logic flaws and chained exploit paths.
MITRE ATT&CK provides a knowledge base of adversarial tactics and techniques that many automated pentesting platforms emulate when validating security controls.
CISA and other government security agencies increasingly emphasize continuous monitoring and automated vulnerability management as part of modern security programs.
By aligning automated penetration testing practices with these frameworks, organizations ensure their testing methodology follows widely recognized security standards.
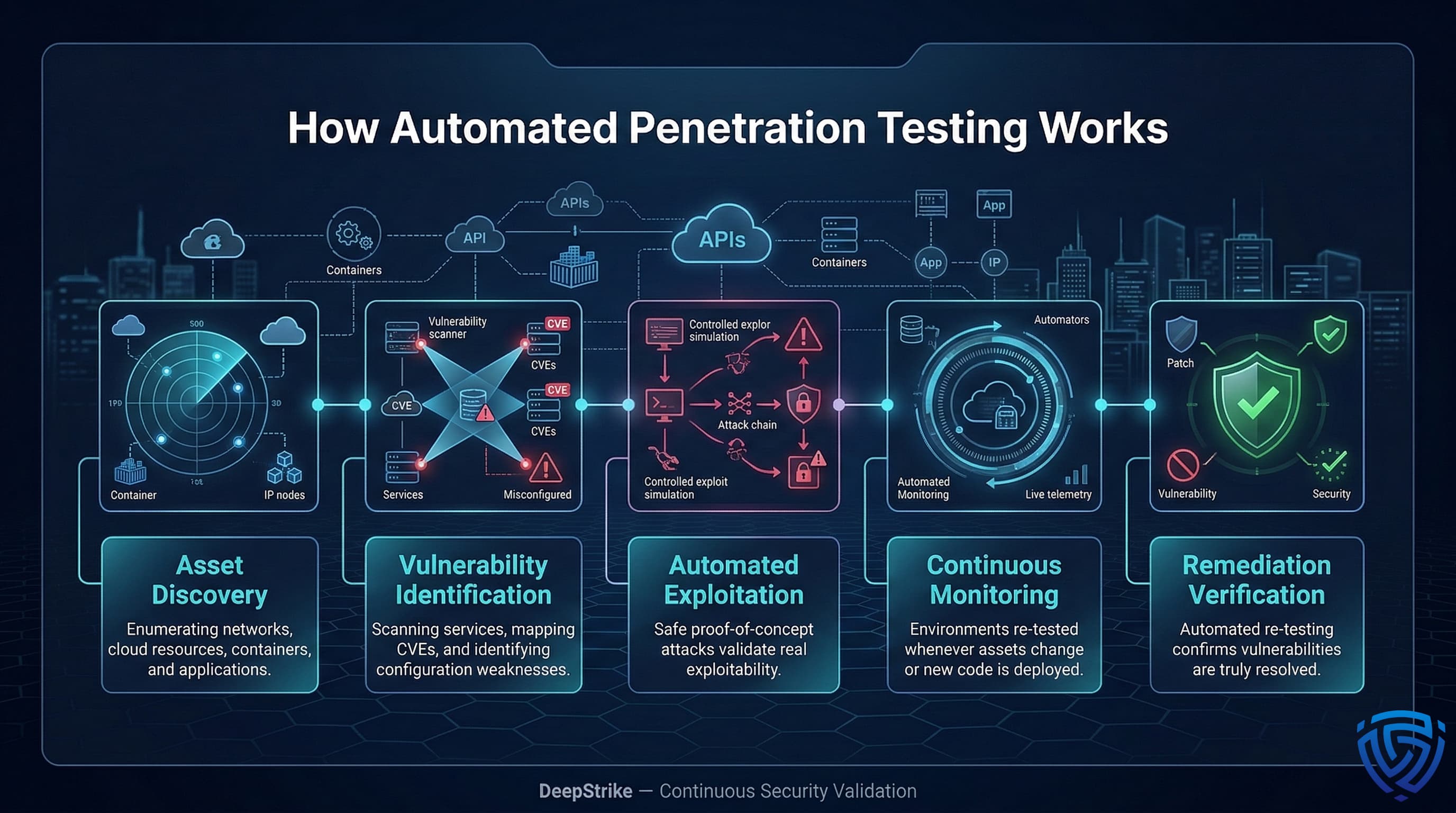
Automated penetration testing platforms perform a sequence of offensive security tasks, much like a scaled red team. The workflow typically includes:
The first step is to discover all assets in scope. Automated scanners enumerate networks, subnets, cloud accounts, containers, and applications. They may integrate with cloud APIs or asset inventories to find ephemeral workloads. For example, modern platforms automate reconnaissance and scanning to maintain “always on” visibility rather than one off snapshots. Automated tools can run Nmap style scans, query cloud tags, or leverage orchestration data to keep an up to date inventory of live targets.
Next, the system runs vulnerability scanners and checks against known weakness databases. This includes CVE lookups, misconfiguration checks, and compliance tests. Automated engines parse service banners, run web scans, and check for missing patches. The advantage is speed and coverage: tools provide “accelerated discovery of issues” with continuous, broad coverage. Automated pentesting often uses fuzzers and static/dynamic analysis to trigger common flaws. Integration with frameworks like MITRE ATT&CK allows mapping detected vulnerabilities to known attack techniques, guiding which exploit steps to attempt.
Where a vulnerability is found, automated tools often attempt proof of concept exploits in a controlled manner. They may launch safe versions of attacks like simulated payloads or credential stuffing to verify exploitability without causing damage. For example, one platform advertises “safe, automated exploit verification” under guardrails. Pentera and similar tools simulate multi-step attacks end to end, such as exploiting a misconfigured VPN to pivot internally. These exploit attempts are carefully contained to avoid disrupting production: successful exploits generate clear evidence of risk, while failures may indicate the issue is harder to exploit manually or requires further review.
Automated pentesting is not a one shot exercise. Modern tools run continuously or on a schedule, watching for changes. They re scan environments whenever new code is deployed or when new assets appear. According to vendor sources, automation “maps large, complex environments, including cloud, hybrid, APIs, and web apps,” ensuring “broad, consistent coverage” without overwhelming testers. In practice, this means every pull request or configuration change can trigger a quick pen test pipeline, alerting teams to regressions or newly exposed paths. Some systems also feed alerts into SIEMs or ticketing systems for real time visibility.
After findings are remediated, automated testers can re-run checks to verify fixes. This closes the loop on each issue. As one source notes, once a patch is deployed, the system “automatically reruns checks and provides immediate confirmation”. This ensures that fixes truly resolved the vulnerability and that no new weakness was accidentally introduced. The automated feedback helps maintain up to date security evidence for auditors.
By integrating into CI/CD pipelines and DevSecOps workflows, automated pentesting becomes part of the normal release process. Each code merge or nightly build can invoke security tests via Jenkins, GitLab CI, etc., ensuring vulnerability scanning and limited exploitation run early. Developers then get quick feedback, and the security team sees alerts through dashboards. This continuous testing approach contrasts sharply with point in time manual pentests, and helps enforce the principle of “shifting security left” in fast moving development environments.
The ecosystem of automated pentesting tools includes several categories:
These tool types differ in approach: attack simulators Pentera, AttackIQ aim to mimic human like chained attacks; scanners Nessus, Prowler rapidly enumerate and report issues; frameworks Metasploit provide a library for targeted exploitation. Automated pentesting platforms often combine elements of all three to varying degrees. Importantly, even the most sophisticated automation is still based on known techniques. As one analyst notes, current automated pentesting primarily targets detectable security weaknesses, but it cannot fully replicate a human attacker’s creativity or business context intuition.
Automated pentesting platforms are typically licensed as enterprise security products rather than one time services. Pricing varies depending on asset coverage, deployment model, and enterprise scale.
| Tool | Typical Annual Cost | Pricing Model |
|---|---|---|
| Pentera | $50,000 $200,000 | Enterprise license |
| Horizon3.ai NodeZero | $40,000 $150,000 | Platform subscription |
| AttackIQ | Enterprise pricing | Attack simulation platform |
| Prowler open source | Free / enterprise support available | Cloud security scanner |
| ScoutSuite | Free open source | Configuration auditing |
Enterprise automated pentesting platforms can require significant investment, especially when deployed across large cloud or hybrid environments. As a result, organizations often evaluate whether automated pentesting tools should supplement or replace periodic manual penetration testing.
In practice, most mature security programs combine automated testing with manual validation to ensure exploitability is properly assessed.
| Attribute | Automated Testing | Manual Penetration Testing |
|---|---|---|
| Speed | High runs continuously or on demand | Moderate periodic engagements |
| Coverage | Broad entire network/cloud in scope | Targeted specific systems/apps |
| Exploit Validation | Limited basic exploit attempts | Deep thorough chain exploitation |
| Business Logic Flaws | Rarely detected | Often found through custom scenarios |
| False Positives | Higher needs human triage | Lower manual verification |
| Attack Chain Discovery | Limited few step attacks | Extensive complex multi step chains |
Automated testing excels in speed and scale, catching many low hanging vulnerabilities across large environments. Manual tests, by contrast, dive deep into critical assets. They discover subtle business logic issues and weave together multi stage attack chains that tools miss. In practice, a hybrid model is best. Automated scans and exploit checks handle routine aspects, while human testers focus on high value targets and creative attack paths. As one expert notes, automation “amplifies researcher efficiency” by handling mechanical tasks so security professionals can focus on complex logic flaws and exploit chains. This synergy yields the most effective security assurance.
Security teams often confuse three different security validation models: automated pentesting platforms, Penetration Testing as a Service PTaaS, and Continuous Penetration Testing CPT. While they share similar goals identifying exploitable weaknesses their operational models and security outcomes differ significantly.
| Model | Testing Cadence | Depth of Validation | Typical Use Case |
|---|---|---|---|
| Vulnerability Scanning | Continuous | Low | Compliance monitoring |
| Automated Pentesting | Scheduled / automated | Medium | Routine vulnerability validation |
| PTaaS | On demand engagements | Medium–High | Operational pentesting with collaboration |
| Continuous Penetration Testing | Event driven / continuous | High | Attack path discovery |
Automated pentesting focuses on speed and repeatability, validating known vulnerabilities at scale.
PTaaS platforms combine automated discovery with human tester involvement, typically allowing organizations to request tests on demand through a platform.
Continuous penetration testing extends further by validating how vulnerabilities chain together into a real attack path. Instead of simply identifying weaknesses, CPT continuously evaluates exploitability as systems change.
For organizations with large attack surfaces and frequent deployments, automated pentesting provides baseline coverage, while PTaaS or continuous pentesting delivers deeper validation of exploit chains.
| Model | Testing Frequency | Depth | Typical Use |
|---|---|---|---|
| Vulnerability Scanning | Continuous | Low | Compliance monitoring, asset inventory |
| Automated Pentesting | Scheduled/On demand | Medium | Routine security validation |
| Continuous Pentesting | Event driven/Always on | High | Attack path discovery, red team simulations |
Automated penetration testing above is typically scheduled or triggered by significant changes, providing ongoing validation of discovered vulnerabilities. Continuous penetration testing also known as Continuous Attack Surface Pen Testing goes further: it embeds testing directly into the development lifecycle for high risk assets. In CASPT, tests run continuously or on events new deployments, infra changes to find emerging gaps. As described by industry sources, CASPT involves “ongoing, automated assessment of an organization’s systems to identify vulnerabilities”. Importantly, this approach also integrates expert analysis it is “not limited to automated tools” and includes human expertise to probe sophisticated, context dependent vulnerabilities. The key distinction is depth and proactivity: Continuous pentesting aims to uncover how vulnerabilities can chain together into an attack path, rather than merely alerting on individual weaknesses.
Being transparent about these limits is crucial. Automated pentesting provides valuable scale and speed, but it does not replace the deep context and judgement a human provides.
Despite its advantages, automated pentesting is not always the best testing model.
Organizations should avoid relying solely on automated testing in scenarios such as:
Applications with intricate workflows such as fintech systems or custom authorization models often contain vulnerabilities that require human reasoning to discover.
Critical systems such as payment platforms, healthcare systems, or financial infrastructure often require manual penetration testing to ensure exploit chains are thoroughly validated.
Automated tools cannot realistically emulate sophisticated adversaries targeting specific objectives such as data exfiltration or lateral movement across environments.
Certain compliance frameworks require manual penetration testing conducted by qualified security professionals.
In these cases, automated pentesting should be used as a complementary capability rather than a replacement for expert led security assessments.
A simple risk model is Expected Loss = Probability × Impact. Automated penetration testing affects both sides of this equation. By finding and helping patch vulnerabilities quickly, automation reduces attacker dwell time, effectively lowering the potential impact of any breach. IBM’s data breach report shows that faster breach identification correlates with lower overall breach cost. However, automation alone does not necessarily reduce the probability of a breach if vulnerabilities remain unexploited or undetected by human tests. Skilled pentesters probing business logic or unusual attack paths are still needed to truly drive down breach probability. In enterprise risk terms, automation is a key tool for reducing expected loss especially by mitigating impact, but it must be combined with human led exploit validation to minimize the chance of compromise.
Security investments are often evaluated using an expected loss model:
Expected Loss EL = Probability of Breach × Impact of Breach
Where:
For example:
| Scenario | Breach Probability | Breach Impact | Expected Loss |
|---|---|---|---|
| No automated testing | 20% | $4.4M | $880,000 |
| With automated pentesting | 12% | $4.4M | $528,000 |
By reducing vulnerability discovery time and shrinking exposure windows, automated pentesting lowers the expected loss associated with security incidents.
However, automation primarily reduces time to detect, not necessarily the probability of exploitation. Manual penetration testing and adversary simulation remain essential to uncover complex attack chains that automated tools may miss.
For this reason, organizations often combine automated pentesting with periodic expert led testing to achieve the greatest risk reduction.
Automated pentesting is reliable for routine vulnerability scanning and baseline security checks. It excels in detecting known issues quickly and consistently. However, it may miss complex logic flaws or novel attack paths that require human insight.
No. Automation provides breadth and speed but lacks depth of analysis. Manual pentesting brings creativity and context, finding issues that scripts miss. The best strategy is a hybrid approach: automation for continuous coverage and humans for targeted, in depth testing.
Tools range from full scale simulation platforms Pentera, Horizon3.ai’s NodeZero, AttackIQ to scanners and frameworks. Open source tools like Prowler and ScoutSuite audit cloud configurations, while frameworks like Metasploit can be scripted for automation. Each tool fills a role: scanners find vulnerabilities, simulation platforms validate attack paths, and exploitation libraries execute payloads.
Ideally, automated tests run continuously or at least on every deployment. In DevSecOps, teams integrate pentesting into the CI/CD pipeline so that builds or daily/nightly jobs trigger scans and tests. At minimum, schedule regular scans after major releases or every few weeks to catch new exposures promptly.
Vulnerability scanning continuously checks systems against known CVEs and misconfigurations like a compliance scan. Automated pentesting goes further: it attempts to exploit found vulnerabilities to validate them and chains steps together. In short, scanning is about detection continuous, shallow, while automated pentesting includes verification of those findings scheduled or automated, deeper.
Selecting the right security testing model is not purely a technical decision. It is a risk-management and capital allocation decision.
Security leaders should evaluate automated penetration testing through four strategic questions:
Organizations with frequent deployments such as SaaS platforms or microservice architectures benefit most from automated pentesting integrated into CI/CD pipelines. Continuous testing ensures vulnerabilities introduced during development are discovered quickly.
High-risk systems such as payment infrastructure, healthcare platforms, and financial systems often require manual validation to confirm real attack paths.
Automation can identify vulnerabilities, but expert-led testing is often required to validate whether those weaknesses lead to meaningful compromise.
Many security frameworks require evidence of testing:
Automation can help maintain continuous evidence between formal testing engagements.
Security programs generally evolve through stages:
| Security Maturity | Recommended Testing Model |
|---|---|
| Early-stage | Vulnerability scanning |
| Growing | Automated pentesting |
| Mature | Hybrid automation + manual testing |
| Advanced | Continuous penetration testing |
Organizations with mature DevSecOps programs often combine automated pentesting for broad coverage with expert-led testing for high-risk assets.
Automated penetration testing provides organizations with scalable security validation across modern cloud and DevOps environments. However, selecting the right testing approach depends on the organization’s risk profile and security maturity.
Key decision considerations include:
In most enterprise security programs, the optimal model combines automated testing for scale with expert led penetration testing for depth.
This layered strategy ensures that vulnerabilities are discovered quickly while sophisticated attack paths are still thoroughly validated.
| Organization Profile | Recommended Provider Type | Example Vendors |
|---|---|---|
| SaaS / cloud-first startups | Manual exploit chaining pentesting | DeepStrike |
| Global enterprises with large attack surface | Hybrid enterprise pentesting providers | NCC Group |
| Highly regulated environments | Compliance-focused pentesting firms | Coalfire |
| Mature security programs testing detection capabilities | Red-team oriented providers | Bishop Fox / Mandiant |
| High-release DevOps environments | PTaaS / continuous testing platforms | Synack / Cobalt |
Automated penetration testing offers organizations a way to keep pace with modern software and infrastructure changes. It accelerates vulnerability discovery across sprawling networks, cloud, and container environments, and integrates with DevSecOps pipelines for continuous validation. However, automation is not a silver bullet. It provides speed and scale but cannot match a skilled human’s ability to uncover complex, logic based issues and multi step exploit chains. In practice, a high authority security program uses automated tests to continuously probe for low hanging vulnerabilities and then deploys expert testers to investigate the critical high risk findings. This layered approach, guided by standards like NIST and insights from reports IBM, OWASP, etc., delivers the strongest defense posture in today’s dynamic threat landscape.
About the Author: Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us