November 10, 2025
Updated: November 10, 2025
Understand the difference between Red, Blue, and Purple Teams how offense, defense, and collaboration build stronger cybersecurity in 2025.
Mohammed Khalil
In cybersecurity, Red Team vs Blue Team refers to an exercise where one group of professionals attacks red and another defends blue an organization’s systems. The goal is simple: find out if your security can hold up against a real world adversary. Red Team members imitate hackers using phishing, exploiting vulnerabilities, and trying anything to breach defenses while Blue Team members strive to detect and stop them in real time. This head to head practice matters now more than ever. The average cost of a data breach has climbed to $4.88 million globally, a 10% jump in a year, and global cybercrime is projected to hit $10.5 trillion by 2025. In this high stakes environment, organizations can’t just hope their security works; they need to prove it through realistic testing. Red/Blue team exercises provide that proof by actively probing your defenses and showing you where the cracks are before actual attackers do.
Why this matters: Traditional security audits often leave blind spots. A Red Team vs Blue Team engagement turns security into a proactive sport instead of waiting for an incident, you’re actively finding and fixing weaknesses. And it’s not about one side winning in the end. It’s about learning. The real enemy isn’t your internal red or blue team; it’s the malicious actors out there. By the end of a well run exercise, both teams come out wiser and your organization is safer.
![Create a cinematic, visually engaging scene that illustrates [Red, Blue, and Purple Teams Explained] — an [animated, color-coded cyber operations infographic / immersive tri-lane visualization] that represents [how offensive (Red), defensive (Blue), and collaborative (Purple) security teams interact to strengthen an organization’s cybersecurity posture.]](/_next/image?url=https%3A%2F%2Fcdn.sanity.io%2Fimages%2Fa3jopls3%2Ftestdataset%2Ff83c699266c15f1bb59c65502305a78703a77e80-1536x1024.jpg&w=3840&q=100&dpl=dpl_4qw1FBaG5B7tvqPoXvPFvjyPD7u4)
To start, let’s clarify what each team means in this context:
Why the colors? The terms originate from military war games where red forces simulate the enemy and blue forces defend. Cybersecurity borrowed this concept to create realistic training scenarios. Over time, the industry realized red and blue shouldn’t operate in silos, hence the rise of purple, a mix of red and blue to emphasize collaboration.
Both teams share a common goal strengthening the organization’s security but they approach it from opposite sides. The table below highlights the core differences in their focus and methods:
| Aspect | Red Team Offense | Blue Team Defense |
|---|---|---|
| Primary Mission | Simulate real world attacks to find and exploit vulnerabilities before attackers do. Focus on achieving specific objectives e.g. data access to test if a breach is possible. | Protect systems and data by preventing, detecting, and responding to threats in real time. Maintain a strong security posture and minimize damage from any attacks. |
| Mindset | Adversarial & creative think like a hacker. Use unconventional approaches, stealth, and patience to bypass defenses. Always ask how could I break this? | Defensive & systematic think like a guardian. Use structured processes, monitoring, and analysis to catch and block attacks. Always ask how could I detect or stop this? |
| Typical Activities | Reconnaissance, penetration testing and exploitation of vulnerabilities, social engineering phishing, baiting, developing custom malware or scripts to evade security, and full scope attack simulations often called red team exercises. | Continuous monitoring of logs and network traffic using SIEM/IDS/EDR tools, investigating alerts, threat hunting for signs of intruders, incident response containment and eradication, and security hardening patching, configuring defenses, training users. |
| Timeframe | Time boxed engagements e.g. a red team might operate covertly for a few weeks or months per assignment to reach its goal, then stop and report findings. Often work under defined Rules of Engagement and deadlines. | Continuous operations the blue team is on duty 24/7/365. Security is an ongoing process, so they monitor and defend in perpetuity. There is no finish line, just continuous vigilance and improvement. |
| Success Metrics | Success = breach achieved without detection. Did the team meet their objective e.g. gain domain admin, exfiltrate data? How many critical vulnerabilities were uncovered that were unknown? A win for red is finding a gap the company didn’t know about. | Success = attacks detected and stopped. Key metrics include Mean Time to Detect MTTD and Mean Time to Respond MTTR to incidents, percentage of attacks blocked or contained, and reducing damage if breaches occur. A win for blue is quickly spotting and nullifying the red team or any attacker before they cause serious harm. |
Red Teamers often operate under the radar, mimicking advanced threat actors APTs and trying to avoid being caught by the Blue Team. They might, for example, use a port scanner like Nmap to quietly find an open door into the network. Meanwhile, Blue Teamers use that same tool to scan for open ports so they can close those doors or monitor them. The toolkit can overlap it’s the intent that differs. One side is looking to break in, the other to secure. Ultimately, these exercises aren’t about crowning a winner internally. If the red team wins by staying undetected and compromising data, it reveals blind spots for the company to fix. If the blue team consistently wins by catching every move, it validates that their defenses are effective and usually the red team will ramp up their stealth to push the blue team even further. Either way, the organization wins by learning something new.
![Create a cinematic, visually engaging scene that illustrates [Tools and Techniques: How Each Team Works] — an [immersive data-driven cyber operations visualization] that represents [how Red, Blue, and Purple Teams use specialized tools and tactics to simulate attacks, defend systems, and collaborate for continuous improvement.]](/_next/image?url=https%3A%2F%2Fcdn.sanity.io%2Fimages%2Fa3jopls3%2Ftestdataset%2F7a95f97a19d0bdef13147033e3835e5717a1f489-1536x1024.jpg&w=3840&q=100&dpl=dpl_4qw1FBaG5B7tvqPoXvPFvjyPD7u4)
Both teams leverage a wide array of cybersecurity tools, sometimes even the same tools but for opposite purposes. Here’s a look at how their arsenals differ:
Overlap: Interestingly, some tools serve both sides. For example, PowerShell is a legitimate administrative tool that Blue Teams use for automation but Red Teams abuse PowerShell to run malware in memory. Likewise, vulnerability scanners Qualys, Nessus might be run by Blue Teams for routine assessments, but also by Red Teams to enumerate weaknesses during an engagement. The security community recognizes this and has started to explicitly build bridges: in 2023, Kali Linux the popular offensive toolkit released Kali Purple, a special edition loaded with defensive tools for Blue Teams. It contains over 100 tools spanning asset discovery, network monitoring, incident response, etc., organized around the NIST security framework categories. This highlights a key point: red and blue are two sides of the same coin. Understanding one side inherently improves the other. That’s why some of the best Red Teamers have Blue Team experience and vice versa each knows how the other thinks.
![Create a cinematic, visually engaging scene that illustrates [Real World Case: Red Team vs Blue Team in Action] — an [immersive tactical cyber battle visualization / animated data simulation] that represents [a live security exercise where an offensive Red Team launches simulated attacks against an organization while the Blue Team detects, responds, and neutralizes threats in real time.]](/_next/image?url=https%3A%2F%2Fcdn.sanity.io%2Fimages%2Fa3jopls3%2Ftestdataset%2F1dd4d1d8fd09c30c9cecc111dce37b6f1a394547-1536x1024.jpg&w=3840&q=100&dpl=dpl_4qw1FBaG5B7tvqPoXvPFvjyPD7u4)
To illustrate how these exercises play out, let’s walk through a simplified example inspired by real engagements:
Scenario: DeepStrike’s Red Team is tasked with a full scope attack simulation on a mid size financial company, FinSecure Corp, while FinSecure’s Blue Team their internal SOC will try to detect and respond. Both teams know the rules of engagement, but the Blue Team isn’t given specifics of the planned attack.
Red Team exercises turn theoretical risks into tangible lessons. In this case, the organization learned exactly how an attacker might string together small weaknesses an unpatched server, a phish, a weak internal password into a major breach. The Blue Team improved their processes as a result. It’s far better to learn from an authorized test now than from a criminal later. As one cybersecurity motto goes, Let’s get hacked by friends so we don’t get hacked by enemies.
For more on real life attack scenarios, check out our related deep dive on an account takeover case study where a single phishing email led to domain wide compromise and how it was detected and contained. This is where we would internally link to an account takeover case study blog post.
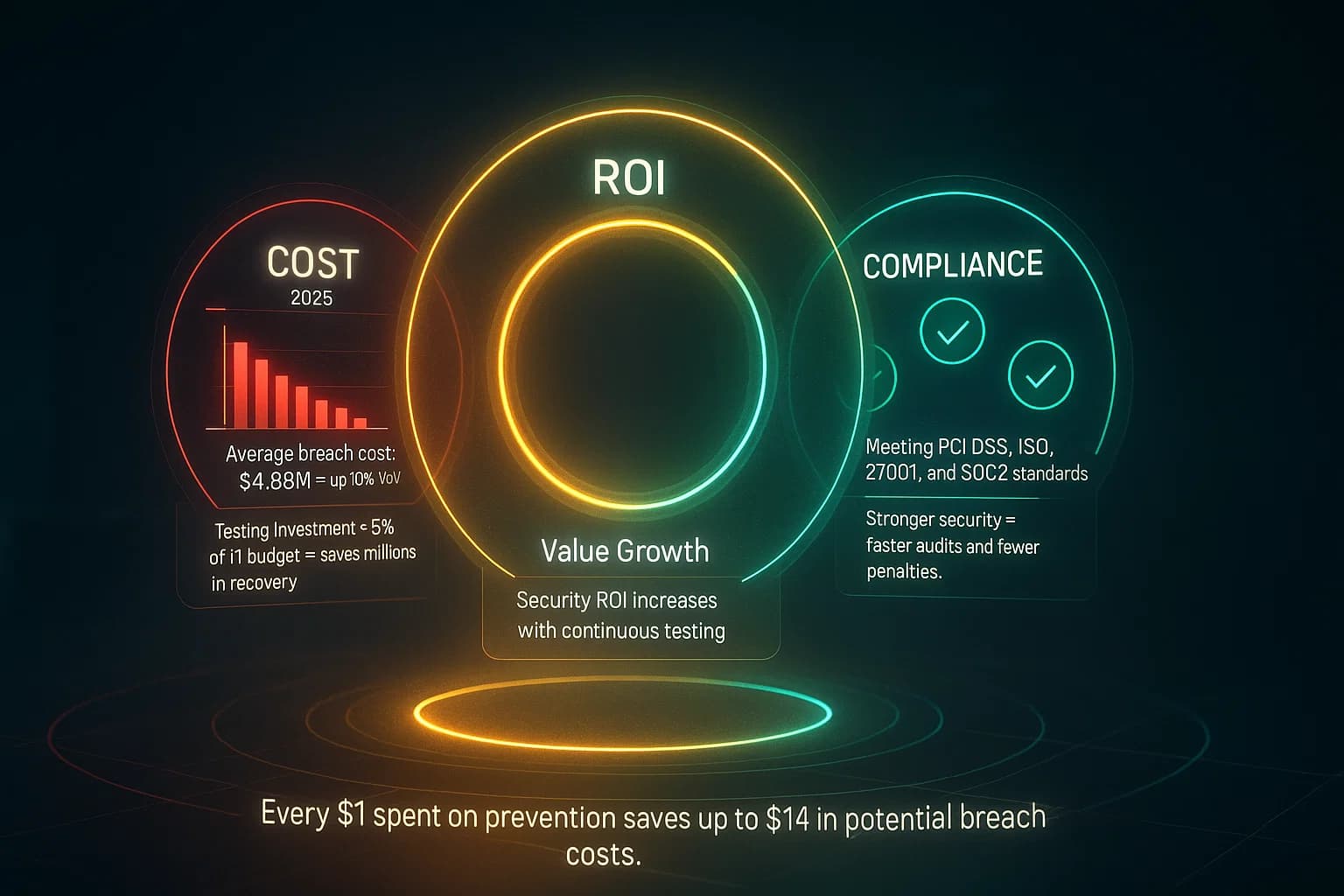
Engaging in Red vs Blue Team exercises is not just a technical decision it’s a business one. Let’s address some practical considerations:
Cost of Red Teaming vs Blue Teaming: By design, Red Team engagements are intense and resource heavy, often spanning weeks of work by highly skilled professionals. This means they cost more than a basic penetration test or vulnerability scan. A full scale red team exercise lasting a few weeks and including social engineering, etc. might range from $40,000 to $100,000+ depending on scope. In comparison, a straightforward network penetration test for a small business could cost a fraction of that e.g. $5k- $15k range. Blue Team costs, on the other hand, are usually the ongoing investments in security personnel, tools, and services like maintaining a SOC or paying for managed detection. For a small company, hiring an external Penetration Testing Service or a one time red team test might feel expensive but consider the alternative: a single data breach can easily cost millions in damages and fines. In fact, the latest data shows a $4.88M average breach cost globally and over $9M in sectors like healthcare. The ROI of a red team engagement becomes clear when it prevents a breach of that magnitude. It’s like paying for a fire drill today so you don’t lose the building to a fire tomorrow.
Small Business Approach: If you’re a smaller organization without a formal Blue Team or SOC, you might wonder if red teaming is overkill. It’s true that a full red team exercise yields the best value when there’s a Blue Team to test otherwise it’s like staging a mock break in with no one watching the cameras or responding. For many small and mid sized businesses, a sensible approach is to start with regular vulnerability assessments and penetration tests to shore up basic defenses, and invest in some foundational Blue Team capabilities like a managed detection service or at least basic log monitoring. Once those are in place, a targeted red team exercise can be extremely valuable to test your incident response and uncover any sneaky gaps. There are also more affordable ways to get red team value, such as Continuous Penetration Testing platforms or Penetration Testing as a Service PTaaS solutions that provide ongoing, smaller scope testing throughout the year acting like mini red team engagements spread over time. These can help organizations with limited budgets get a taste of adversary simulation without the big one time cost.
Compliance and Regulatory Drivers: An increasing number of standards and regulations are requiring or explicitly encouraging red team or advanced penetration testing exercises. For example, PCI DSS 4.0 for payment card industry now mandates annual internal and external penetration testing, plus segmentation tests, for compliant organizations. Healthcare regulations under HIPAA expect regular security evaluations, which many hospitals fulfill via periodic third party penetration tests. In the EU, the new Digital Operational Resilience Act DORA requires major financial institutions to conduct annual threat led penetration testing, essentially regulated red team exercises. Even if it’s not mandated, regulators view favorably any evidence that an organization is proactively testing its own defenses. It shows due diligence. Additionally, frameworks like MITRE ATT&CK and NIST’s cybersecurity framework are widely used to align red blue activities with best practices, and many cyber insurance providers ask whether you conduct such tests when underwriting policies. Investing in red and blue teams can also mean staying compliant and competitive. It demonstrates to auditors, customers, and insurers that you take security seriously and verify it in practice.
From a business perspective, one often overlooked benefit of Red/Blue exercises is the cultural shift. These exercises break down silos between offense focused and defense focused staff. They foster a culture of continuous improvement and vigilance. When employees, even non IT staff, hear that the company did a red team exercise, it often raises security awareness: If our own team could phish us, so could a real attacker I better be on my toes. Many companies use sanitized findings from red team reports as training material for the broader workforce for example, showing how a bad email fooled even a tech savvy user, to emphasize why phishing training is critical. In that sense, the return on red teaming also comes in the form of human risk reduction, not just technical fixes.
![Create a cinematic, visually engaging scene that illustrates [Red and Blue Together for Resilience] — an [immersive flowing infographic / cyber symbiosis visualization] that represents [the unification of offensive (Red) and defensive (Blue) cybersecurity teams to create a stronger, adaptive, and resilient defense posture.]](/_next/image?url=https%3A%2F%2Fcdn.sanity.io%2Fimages%2Fa3jopls3%2Ftestdataset%2Fcd80bb0ae9713c8f78b957ec0e75cee0deed6611-1536x1024.jpg&w=3840&q=100&dpl=dpl_4qw1FBaG5B7tvqPoXvPFvjyPD7u4)
In the world of cybersecurity, pitting red vs blue is not about declaring a winner it’s about leveraging the tension between offense and defense to drive improvement. Red Teams are invaluable for challenging assumptions, finding that one weakness everyone else missed, and showing what a determined adversary could do. Blue Teams are the unsung heroes who keep organizations safe day after day, stopping countless attacks and minimizing damage when something does get through. In 2025 and beyond, the key lesson is that offense and defense must collaborate. The rise of Purple Teaming reflects this shift: it’s no longer attackers vs defenders internally, but allies against the real enemies out there. When red and blue share data, co create fixes, and treat each exercise as a learning opportunity instead of a gotcha game, the organization’s security posture grows exponentially stronger.
From a business perspective, these exercises provide hard evidence to justify security investments and build trust with stakeholders. It’s one thing to claim your security is good; it’s far more convincing when you can say, We regularly test ourselves and here’s what we learned and fixed. Over time, a mature Red/Blue team program helps cultivate a security first culture where everyone from IT to development to execs is aware of threats and prepared to respond. Breaches aren’t 100% preventable, but by incorporating red and blue team practices, you greatly increase your chances of detecting incidents early and handling them effectively, turning potential disasters into minor blips.
To sum up, Red Team vs Blue Team isn’t an internal battle, it’s a partnership. The ultimate goal is a unified, adaptive defense that keeps improving. Cyber threats in 2025 are more sophisticated than ever, but by continuously testing and training ourselves like fire drills for cyber, we stand a much better chance at thwarting even the most determined adversaries. Remember: the real opponent is out there on the internet, not in the next room. By fostering a purple team mentality of shared mission, we ensure that when that opponent strikes, we’re ready to beat them at their own game.
The threats of 2025 demand more than just awareness; they require readiness. If you’re looking to validate your security posture, identify hidden risks, or build a resilient defense strategy, DeepStrike is here to help. Our team of practitioners provides clear, actionable guidance to protect your business.

Explore our Penetration Testing Services to see how we can uncover vulnerabilities before attackers do. Drop us a line. We're always ready to dive in and bolster your security.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.
Neither role is inherently better it depends on your interests and skill set. Red Team roles ethical hackers, pentesters appeal to those who love offense: creative problem solvers who enjoy thinking like an attacker and breaking systems to understand them. Blue Team roles SOC analysts, defenders suit those who are analytical, detail oriented, and enjoy safeguarding and building secure systems. From a job market perspective, there are generally more Blue Team jobs available every company needs defenders, not every company has an in-house red team, and blue roles can be a great launching pad many top red teamers start as blue teamers to learn how defense works. On the other hand, red team specialists with strong track records are in high demand for consulting and can command high salaries for their niche expertise. If you’re undecided, consider this: Do you get more excited by figuring out how to break into something choose red or how to secure it choose blue? Also remember, careers aren’t static plenty of professionals switch from blue to red once they’ve built up defensive expertise. Tip: If you aim for red team, hands-on technical certifications like OSCP Offensive Security Certified Professional or CRTO are highly valued to prove your hacking skills, often more than a theoretical cert like CEH. For blue teamers, certifications like GCIH GIAC Incident Handler or CISSP can bolster your resume, but employers also look for experience with specific tools SIEM, EDR, etc. and incidents you’ve handled. In summary, both paths are rewarding; the best one is the one that fits your passion. In fact, having experience in both can make you a formidable cybersecurity leader many CISOs appreciate offensive testing experience even if their main job is defense.
A penetration test is typically a narrower assessment, usually a one or two week engagement focused on finding as many vulnerabilities as possible in a defined scope, say, a particular web app or network segment. Think of it like a skilled technician checking your doors and windows for weaknesses. A Red Team exercise, by contrast, is a broader and more covert operation. It simulates a full attack campaign by a determined adversary, often over a longer period multiple weeks to months. The Red Team isn’t trying to enumerate every bug; instead, they operate more like an actual threat actor with a goal for example, steal the customer database without being detected. This means they might ignore minor flaws and instead chain together a few critical ones to achieve their objective. The biggest difference is focus and depth: a pentest asks what vulnerabilities exist and can we exploit them? while a red team asks can we quietly accomplish a high value attack goal, and do the defenders notice?. Also, interaction with Blue Team: in a normal pentest, you usually don’t involve the client’s security team until you deliver the report. In a red team, the whole point is to test the Blue Team often the Blue Team isn’t told when it’s happening, so they can be truly tested. If the Blue Team detects the red team, the engagement might pivot into a purple team mode sharing info to improve, whereas in a pentest, detection isn’t usually part of the evaluation. One way to put it: all red team exercises include penetration testing, but not all penetration tests are red team exercises. The red team is the next level, focusing on goals, stealth, and detection/response, not just vulnerability discovery.
MITRE ATT&CK is like a playbook of adversary tactics and techniques, and it’s extremely useful for both teams. Red Teams use ATT&CK as a menu to ensure they’re emulating real world threats. For example, they might consult ATT&CK to plan an operation that mirrors a known threat group, following the tactics step by step initial access, execution, persistence, etc.. This helps them not to forget stages like privilege escalation or data exfiltration techniques that a real attacker would use. Blue Teams use ATT&CK as a yardstick to measure their defenses. They map their detection capabilities to the techniques in ATT&CK to see which ones they can catch and which might be blind spots. For instance, if ATT&CK lists T1566.001: Spearphishing Attachment and the blue team doesn’t have any alerting for suspicious email attachments, that’s a gap to fill. During or after an engagement, both teams might sit together purple team style with an ATT&CK matrix and mark which techniques were used by red and which were detected by blue. This gives a clear visual of where to improve. In summary, ATT&CK provides a common language. Red can say we used these five techniques from ATT&CK, and Blue can say we detected three of them let’s work on the other two. It brings coherence to planning, executing, and discussing threats and defenses.
It depends on your organization’s size, risk profile, and maturity. Large organizations with mature security operations often do a red team exercise annually or even more frequently as part of their security program. Some highly targeted industries finance, defense might have smaller scale red team tests or continuous adversary simulation throughout the year, supplemented by formal big exercises. If you’re still building your security fundamentals, you might start with annual penetration tests and occasional targeted red team engagements e.g. one every 2 years or after major changes. The trend in 2025 is towards more frequent testing in some form rather than one big bang test per year, companies are adopting ongoing testing via automation and purple team workshops. For example, after an annual red team, many organizations hold quarterly purple team sessions focusing on specific threats like one quarter simulate a ransomware attack, next quarter a cloud account breach, etc.. This continuous approach helps keep the defenders on their toes and integrates improvements iteratively. Also, consider triggers: you should run a fresh test after major changes like deploying a new critical application, or after a significant real incident to validate fixes. And don’t forget tabletop exercises and incident response drills in between not every test has to be a full red team; you can rehearse incident response to hypothetical scenarios too. In summary, aim for at least one comprehensive red team exercise per year if possible, but supplement it with more frequent, smaller tests or drills. The goal is to move toward continuous security validation because attackers are probing continuously too.
The White Team refers to the referees or organizers of a red/blue team exercise. They are the neutral party that sets the rules of engagement, scope, and ensures things don’t get out of hand. If Red Team are attackers and Blue Team are defenders, the White Team are the game masters. Their duties include obtaining proper legal approvals for the test, communicating with leadership, and making sure the Red Team doesn’t accidentally cause real damage for instance, if something critical breaks, the White Team might pause the exercise. They also often collect and correlate results: since red is trying to hide and blue is trying to find them, only the White Team has the full picture during the test. After the exercise, the White Team helps facilitate the debrief, making sure the findings are understood by both sides and by management. In many cases, the White Team is just a few senior folks, perhaps the CISO or an external consultant who oversee the whole thing. White Team members have to be trusted by both sides. Think of them as umpires in a sports game: they don’t play to win, but they make sure the game is fair and productive. In smaller exercises, the function of the White Team might be as simple as a project manager who says Red Team, you’re allowed to target these systems but not those, and exercise ends on X date and coordinates meetings between red and blue for interim updates. It’s an important role that keeps the exercise safe and structured.
Technically yes you can hire a red team internal or external to test your organization even if you don’t have a dedicated blue team or SOC. However, the value you get is different. A red team without a blue team to catch them effectively becomes a very advanced penetration test. They will still find vulnerabilities and demonstrate what an attacker could do, which is useful to fix prevention measures. But you won’t be exercising detection and response capabilities if those capabilities don’t exist. Many smaller companies are in this boat: they might do an annual red team style test using a third party penetration testing service and, lacking an internal SOC, rely on that report to improve security. There’s nothing wrong with that as a starting point it will help improve your preventive controls firewalls, patching, etc.. Just keep in mind the primary benefit of a full red team exercise is to assess and train the Blue Team. If you don’t have an in-house Blue Team, consider using a MDR Managed Detection and Response provider or an outsourced SOC during the test, so someone is watching for the red team’s activity. Or, scale the engagement to your reality: maybe do a targeted red team that focuses on one scenario like phishing + ransomware simulation and use it to develop your incident response process. Over time, as you build up at least a small blue capability even if it’s just IT staff with some added SOC tools, your future red team exercises will yield far more value. In short, you can do red teaming without a blue team, but you’ll be testing mostly your technology and processes, not your real time response. It’s often recommended to invest in some defensive basics first, then do a red team to truly test your organization holistically.
A SOC Security Operations Center is pure Blue Team. The SOC is the command center where analysts monitor dashboards, investigate alerts, and coordinate incident response. If you imagine your cybersecurity like castle defense, the SOC is the watchtower where guardians scan the horizon for enemies and direct the soldiers or call the cavalry, etc.. SOC analysts, threat hunters, incident responders all these roles fall under Blue Team. They are on the front lines defending against attackers day in and day out. Red Teams, on the other hand, are usually a separate group, often not even employees of the company many are external consultants that come in with an attacker mindset. In some organizations, the term Blue Team might specifically refer to the SOC, while other defensive units like the vulnerability management team or security engineering are adjacent, but broadly speaking, whenever you hear SOC, think Blue. It’s worth noting that the best SOCs take lessons from red teams to heart they often invite red teamers to help build new detections or run drills. And conversely, some companies rotate staff between SOC and red teaming to cross pollinate skills. But at any given time, if you’re in the SOC, you are wearing a Blue Team hat.
Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us