March 16, 2026
Updated: March 16, 2026
A checklist-driven, compliance-literate guide to scoping, executing, and documenting penetration testing for VARA-regulated virtual asset businesses without overstating regulatory requirements.
Mohammed Khalil
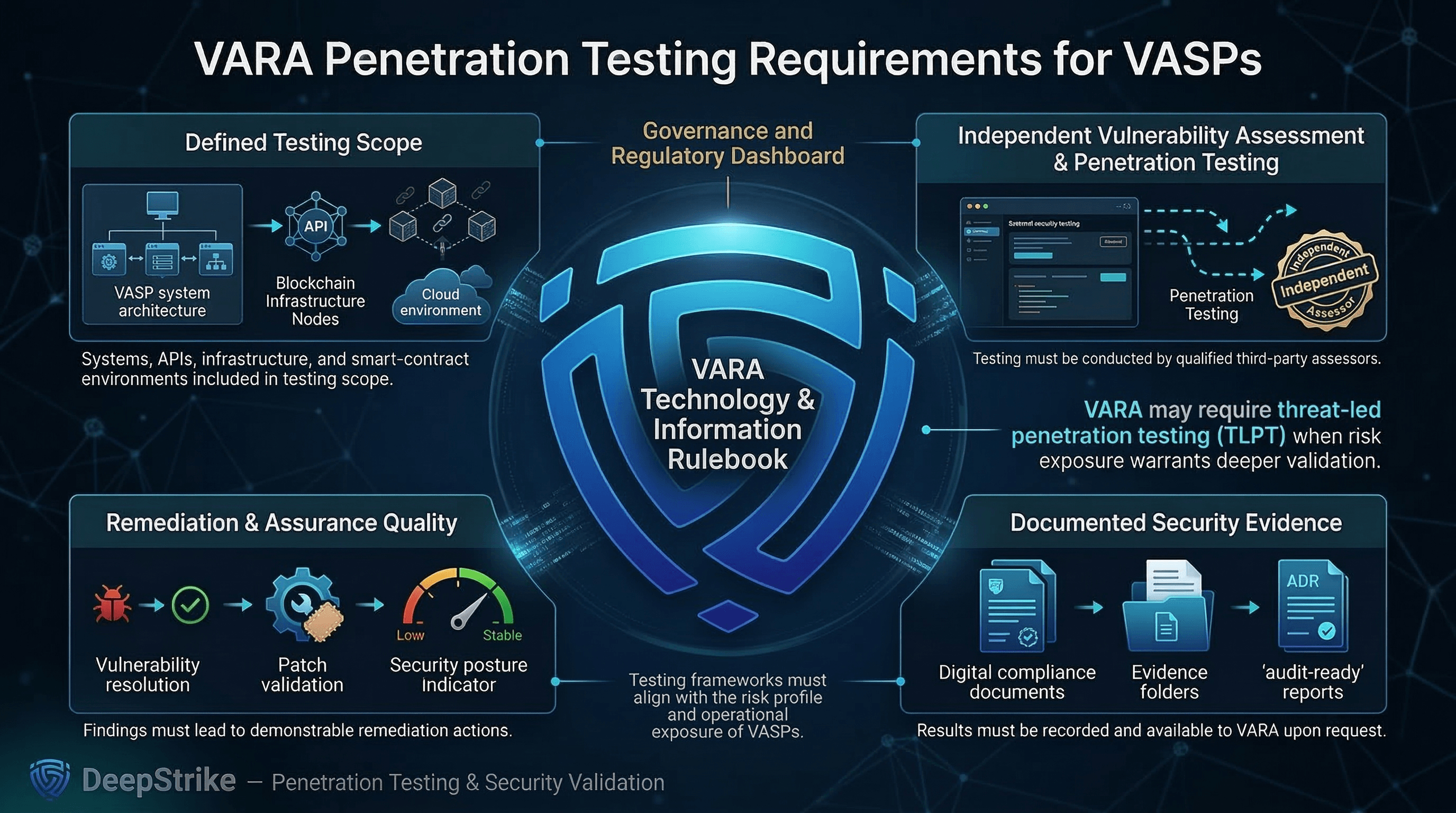
VARA’s Technology and Information Rulebook creates a clear testing baseline for VASPs: independent third-party vulnerability assessments and penetration testing, documented evidence, and results availability upon request. In practice, a VARA penetration testing checklist is not just a request to perform a penetration test; it is a way to define scope, evidence, remediation, and assurance quality before testing starts. It also gives VARA a mechanism to require threat-led penetration testing (TLPT) where necessary and proportionate.
In this guide, regulatory statements are separated into explicit rulebook requirements, supervisory expectations, and broader best practices.
A VARA penetration testing checklist is a structured set of scoping, validation, reporting, remediation, and evidence criteria used to ensure security testing for a virtual asset business meaningfully covers exploitable risk across applications, APIs, privileged workflows, wallet and transaction controls, cloud exposure, and supporting operational systems while producing audit-ready outputs.
A VARA penetration testing checklist is not just a list of web vulnerabilities. It is a control mechanism that forces a penetration test to answer five practical questions:
The reason this matters in virtual assets is that “platform compromise” is often a chain: an attacker rarely needs to own everything only enough to move value or alter critical state. In practice, that usually means exploiting weaknesses in authentication, session management, API authorization, admin tooling, workflow approval logic, cloud privileges, and/or custody controls.
From a regulatory standpoint, the checklist should reflect explicit VARA testing obligations, evidence-retention expectations, and any change-triggered testing needs that apply to the operating model.
A checklist matters because it makes penetration testing decision-grade instead of “report-grade.”
A checklist also prevents a common failure mode: treating penetration testing as a checkbox that “proves compliance.” VARA-aligned testing should be treated as one evidence stream inside a broader governance and control environment, not as a substitute for security architecture, monitoring, change control, incident readiness, or custody controls.
| Attribute | Penetration Testing | Vulnerability Scanning | Compliance Review |
|---|---|---|---|
| Primary Goal | Prove exploitability and attacker outcomes | Identify known vulnerabilities/misconfigurations at scale | Validate control design, governance, and evidence against obligations |
| Depth of Validation | Deep, manual, scenario-based | Broad, automated | Clause/control-evidence focused |
| Exploitability Focus | High: chains and impact are demonstrated | Low: mostly detection and heuristics | Low: typically no exploitation |
| Output | Attack narratives, PoC evidence, prioritized remediation | Vulnerability list, severities, asset inventory mapping | Findings mapped to requirements, gaps, evidence requests |
| Business Value | Validates real risk in critical paths | Baseline hygiene and continuous visibility | Regulatory defensibility and governance clarity |
| Main Limitation | Time-bound; can miss out-of-scope assets | False positives/negatives; weak on business logic | Can “pass” while exploitable paths still exist |
For VARA-relevant businesses, these three activities serve different assurance functions: penetration testing validates exploitability, scanning supports coverage and hygiene, and compliance review supports governance and evidence readiness.
Rulebook-aligned scope discipline starts with two artifacts: (1) an asset and trust-boundary map, (2) a list of “critical or important functions” (customer identity, admin privilege, transaction approval/signing, withdrawals/settlement).
Include, as applicable to the business model:
Scope must also state constraints: environments (prod vs staging), test accounts and roles, data restrictions, rate-limit boundaries, and incident handling during testing.
Use threat scenarios that map to likely attacker outcomes in virtual assets:
Where you include examples, label them explicitly as hypothetical unless backed by a cited public source.
A defensible penetration testing methodology for VARA-aligned environments should satisfy both technical reviewers and governance stakeholders:
A defensible penetration testing report structure must be usable by engineers and legible to governance:
VARA’s testing and evidence requirements mean your report structure should assume downstream scrutiny: results may need to be produced on request, and test evidence should be documented and inspection-ready.
The checklist should require a closed-loop lifecycle:
This closes the gap between “we found issues” and “we can demonstrate control improvement,” which is the real purpose of a mature security validation program.
VARA’s Technology and Information Rulebook requires VASPs to conduct vulnerability assessments and penetration testing and, to the extent relevant, comprehensive audits of smart contracts’ effectiveness, enforceability, and robustness. That “to the extent relevant” clause is the practical reason one universal scope does not fit every business model.
| Business Model | Minimum Scope Priorities | High-Risk Areas Often Missed | Notes |
|---|---|---|---|
| Exchange / Trading Platform | Auth + sessions; trading + withdrawal APIs; admin/risk tooling; wallet integration boundary; cloud IAM | Order-state manipulation; privileged withdrawal overrides; API object-level auth gaps; support tooling abuse | Define whether custody is internal or via provider; scope must reflect where signing/approval actually occurs |
| Custody / Wallet Custody | Key access control paths; signing services; approval workflow/policy engine; admin + key-holder ops; audit logs | “No single point of failure” violations; key-holder offboarding gaps; privileged access drift; weak backup/seed controls | Custody-specific wallet management rules include detailed expectations for key/seed backups, multi-sig, and operational controls (where applicable) |
| Broker / OTC / Dealer | Client onboarding + auth; trade capture/RFQ; settlement instructions; approvals; counterparty tooling | Settlement address manipulation; privilege escalation into approvals; API authorization on trade objects | Often integrates with third parties for settlement and pricing test trust boundaries explicitly |
| Non-custodial Wallet Provider | Mobile app security; local key storage assumptions; signing flow; dApp browser/deep links; backend APIs | Seed phrase exposure via logs/clipboard; insecure deep links; transaction confirmation UI bypass; backend auth flaws | Scope depends on whether any backend can influence transaction construction or approvals |
| Token Issuer / VA Issuance | Smart contracts + admin keys; mint/burn/upgrade paths; issuance portal; signing controls; monitoring | Privileged key compromise; upgrade abuse; missing access controls; insufficient contract testing | If smart contracts are in scope, align testing depth to “to the extent relevant” obligations |
| Transfer / Settlement Services | Transaction construction; routing/bridging logic; address management; monitoring; admin controls | Replay/out-of-order transaction handling; address substitution; weak anti-abuse controls | Ensure scope reflects operational transaction batching and approval realities |
VARA’s broader technology rulebook also makes wallet/key governance a formal area of control expectation, which is why custody and wallet workflows must be treated as first-class test targets in most virtual asset models.
Because VARA places formal weight on independent third-party testing, provider quality is not a procurement detail; it directly affects assurance value and should outweigh headline pricing comparisons. In practice, “qualified” should translate into demonstrated capability against your true attack surface, not generic web testing claims.
Use the evaluation criteria below as a practical provider-evaluation framework to avoid providers who can generate findings but cannot validate attacker outcomes in virtual asset workflows.
| Evaluation Criterion | Why It Matters | What Good Looks Like | Warning Sign |
|---|---|---|---|
| Virtual asset platform competence | Virtual assets have unique critical paths (approval/signing/withdrawal) | Demonstrates prior work on exchange/custody/wallet patterns and can explain expected attack paths | Only generic web-app narratives; no workflow specificity |
| API + business-logic testing depth | Most high-impact exploits are API authorization/state issues | Method includes object-level/function-level authorization testing, tampering, replay, and state-transition abuse | Focuses on scanning and “common CVEs” only |
| Privileged workflow testing | Admin/support tools frequently become the attacker’s goal | Clear plan for staff portals, support tooling, and privileged approvals with safe-testing controls | Refuses or de-prioritizes internal tooling |
| Wallet/key workflow understanding | Funds movement risk is rooted in signing and approvals | Can map key custody model and test “bypass approval / force signing” pathways safely | Treats wallets as “out of scope by default” |
| Cloud/IAM exploitation capability | Cloud privilege escalation often bridges to crown jewels | Tests IAM permissions, secret exposure, CI/CD, and segmentation assumptions | Stops at perimeter testing; no cloud control-plane coverage |
| Reporting and evidence quality | Defensibility requires reproducible proof and clarity | Clear scope, PoC steps, impact narratives, remediation options, retest plan | Vague severities, no repro steps, no asset mapping |
| Retesting support | Closure requires verified fixes | Includes retest window and clear closure criteria | “Retesting is a new engagement” with no structure |
| Data handling and confidentiality discipline | Testing involves sensitive client and security data | Strong NDA/data handling approach; controlled evidence storage | Casual evidence handling; unclear data retention practices |
| TLPT readiness (if notified) | VARA may require TLPT under certain conditions | Can support TLPT conditions: external tester model, controlled live testing plan, documentation outputs | No capability to scale beyond standard pentest |
If TLPT is in scope (because VARA notifies that it is required), VARA’s rulebook includes additional conditions around external testers, including certification/code-of-conduct adherence and professional indemnity insurance requirements do not assume those TLPT-specific requirements automatically apply to every standard penetration test engagement unless TLPT is actually required.
A VARA-ready evidence pack should let a third party answer: “What was tested, what failed, what was fixed, and what proof exists?”
At minimum, maintain:
This structure aligns with VARA’s evidence-availability expectations and with established testing guidance that prioritizes planning, analysis, and actionable mitigation outputs over raw tool output alone.
VARA sets an explicit testing baseline for VASPs through third-party vulnerability assessments and penetration testing, but decisions about how often to perform penetration testing should still account for minimum cadence language, change-triggered testing, and results availability upon request.
Additional cadence and coverage language in technical guidance should be described as supervisory expectation where the wording is framed as “expected,” rather than presented as a universal hard mandate.
Best-practice trigger model (recommended even when cadence is fixed):
The checklist is most valuable when it is used not only “because it’s time,” but because the risk profile changed.
Procurement and leadership should use the checklist to prevent three predictable failures: buying a generic pentest, accepting a report that cannot drive remediation, and treating testing as proof of compliance.
Procurement should insist on:
Leadership and risk committees should ask:
For many VASPs, the board-level risk is not “a vulnerability exists” but “a vulnerability exists in a path that moves value, and we cannot demonstrate we tested, fixed, and verified closure.”
Yes. VARA’s rulebook includes explicit penetration testing and vulnerability assessment obligations for VASPs, tied to independent third-party testing, minimum cadence language, and evidence availability.
No. A penetration test is evidence about exploitability and control effectiveness in scoped systems. Compliance depends on a broader set of obligations, including governance, policies, controls, monitoring, incident readiness, and evidence. Penetration testing should therefore be treated as one evidence stream inside a broader control environment. VARA’s own rulebook language ties testing to evidence availability and broader auditing processes, which underscores that pentesting is one element of a larger control environment.
VARA’s rulebook sets an explicit minimum cadence and a change-trigger requirement. Broader technical guidance may express additional expected testing frequencies, but those should be presented as supervisory expectation rather than as a universal hard mandate.
At minimum: authenticated customer flows, trading and withdrawal APIs, admin/support tooling, wallet integration boundaries, approval/limits logic, and cloud/IAM paths that can reach those systems. Use the business model table to tailor scope and avoid missing high-risk areas.
Yes. VARA’s testing language places formal weight on independent third-party assessment, and independence also improves credibility, report defensibility, and separation of duties.
In the VARA context, TLPT is an advanced testing mechanism that VARA may require where necessary and proportionate. It comes with additional execution, tester, and documentation conditions beyond a standard penetration test.
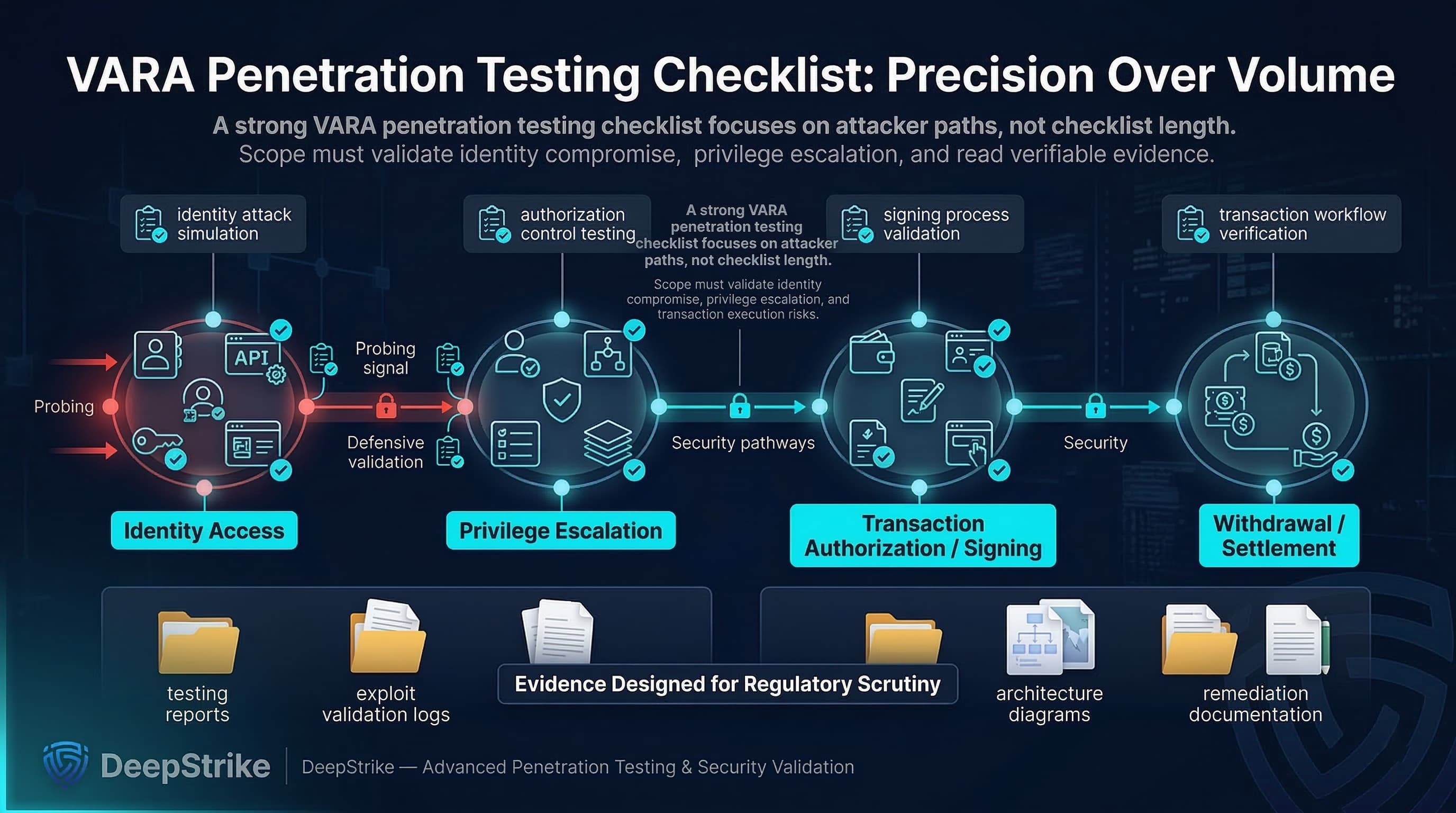
A high-quality VARA penetration testing checklist is not a longer checklist, it is a sharper one. It forces scope around real attacker paths (identity → privilege → transaction approval/signing → withdrawal/settlement), it distinguishes explicit VARA requirements from supervisory expectations and best practice, and it produces evidence that can survive scrutiny.
If you use this structure to define scope, select a provider, enforce reporting quality, and close the remediation/retest loop, you get outcomes that are both technically credible and compliance-defensible without overstating what VARA does or does not require.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us