April 1, 2026
Updated: April 1, 2026
A methodology-driven ranking of Malta penetration testing providers based on manual testing depth, reporting quality, compliance alignment, and buyer fit.
Mohammed Khalil

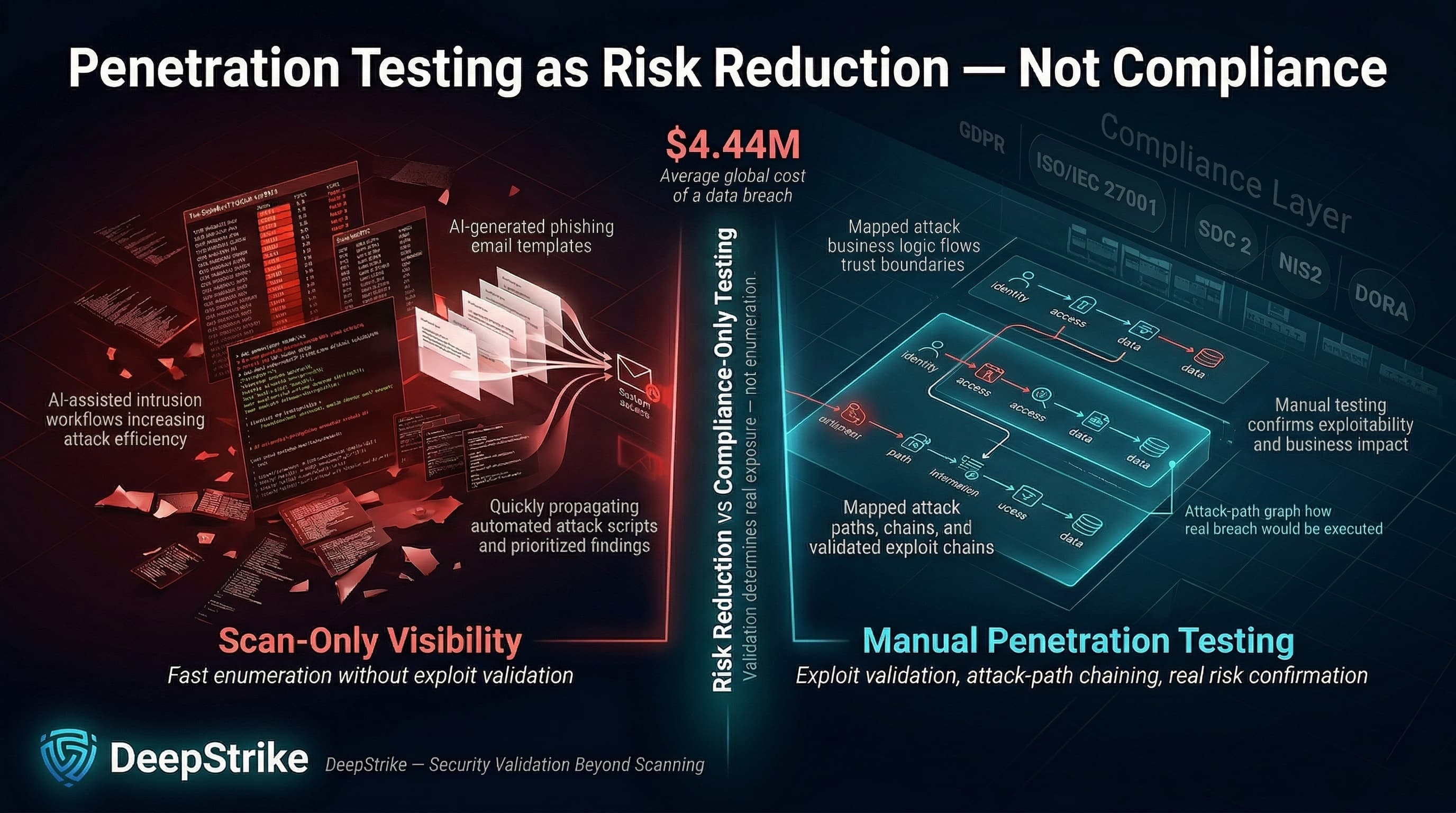
With the global average cost of a data breach estimated at about USD 4.44 million, penetration testing procurement is best treated as a risk-reduction and loss-control decision rather than a routine compliance purchase. AI-assisted tradecraft is reducing attacker effort for social engineering content and intrusion workflows, increasing the value of manual validation over scan-only outputs. Malta-based and Malta-serving organizations also operate under EU-aligned compliance pressures, including GDPR, and commonly procure testing to support ISO/IEC 27001 programs, PCI DSS validation, SOC 2 assurance, and EU resilience requirements such as NIS2 and DORA (particularly in finance). A persistent market gap remains: scan-heavy vendors can enumerate issues quickly, but manual penetration testing is required to validate exploitability, chained attack paths, and business logic failures.
This ranking is methodology-driven and not sponsored. It focuses on providers that can realistically serve Malta: Malta-based firms, EU-delivering firms, and global providers with delivery models compatible with Malta engagements.
Penetration testing is a structured adversarial security assessment that combines automated vulnerability discovery with manual exploit validation to identify real-world attack paths, validate control effectiveness, and reduce breach probability.
Scoring used only publicly verifiable evidence; where evidence was absent, scoring was conservative.
Procurement-grade criteria emphasized: tester competence signals (skills-based offensive certifications such as OSCP/OSWE, senior security leadership such as CISSP, and assurance alignment signals such as CREST), manual depth versus automated-heavy delivery, exploit validation (evidence of exploitation or post-exploitation reasoning), red team maturity where required, capability to test modern environments (web, mobile, API, cloud, identity workflows), reporting utility (executive plus technical outputs with remediation clarity), retesting terms and closure criteria, and Malta market fit (EU/GDPR expectations, time-zone practicality, and cross-border delivery maturity).
Scoring favored evidence of senior-led testing rather than junior-only execution, because business logic testing requires human reasoning.
The highest-cost mistake is buying a scan-only engagement. Security buyers should distinguish scan output from real penetration testing. Manual exploit validation is what turns findings into evidence of realistic attacker paths, especially where business logic, identity workflows, and chained exploitation matter.
High-risk under-scoping patterns include omitted APIs, privileged admin paths, SSO and password reset flows, and cloud identity permissions. These omissions are common when buyers procure “network penetration testing Malta” as a standalone line item, but operate cloud-first systems.
Retesting should be treated as a deliverable with closure criteria. Providers in this ranking vary materially, including explicit retesting inclusion versus conditional or proposal-dependent retesting.
Junior-only delivery teams and over-reliance on automated platforms create predictable failure patterns: broad findings lists, weak exploit validation, limited business logic coverage, and shallow identity abuse testing.
Local presence reduces coordination friction but does not guarantee technical depth; conversely, remote-first delivery can be commercially practical when collaboration and evidence handling are well-defined.
Comparison table for triage. “Testing Depth Model” reflects each provider’s public positioning on manual vs automated work and realistic attacker simulation.
| Company | Specialization | Testing Depth Model | Best For | Malta Relevance | Compliance Alignment | Ideal Organization Size |
|---|---|---|---|---|---|---|
| DeepStrike | Manual pentesting, cloud, API, red team | Manual exploit chaining | Cloud-first, SaaS, regulated | Global delivery model; no Malta office claimed | SOC 2, ISO 27001, PCI-DSS reporting positioning | SMB to enterprise |
| PwC Malta | Enterprise cyber programs, offensive security | Red-team oriented | Regulated enterprises | Malta-based | DORA, MFSA ICT, GDPR plus PCI-DSS and ISO 27001 gap assessments | Mid-market to enterprise |
| BMIT Technologies | Security testing + managed services | Hybrid model | SMB and mid-market | Malta-based | Testing supports broader security programs | SMB to mid-market |
| Forvis Mazars in Malta | Risk consulting + technical testing | Hybrid model | Governance + technical reporting | Malta-based | Confirm exact mappings | SMB to enterprise |
| BDO Malta | Technology assurance and penetration testing | Hybrid model | Multi-scope testing with defined phases | Malta-based | Confirm exact mappings | SMB to enterprise |
| CyberAudit | Boutique testing, PCI focus | Hybrid model | Smaller scopes, PCI and segmentation | Malta-focused | PCI DSS positioning | Micro to SMB |
Headquarters: San Francisco Founded: 2016 Company Size: 11–50 employees Primary Services: Web, mobile, cloud penetration testing; red team engagements; social engineering; continuous testing Industries Served: Cross-sector; positioned for SOC 2 / ISO 27001 / PCI-DSS evidence needs
Why They Stand OutDeepStrike is explicit about manual execution and lists procurement artifacts that reduce delivery friction, including a shared Slack channel, an attestation letter, and a real-time dashboard. Retesting is listed as “Free Unlimited Re-testing,” reducing closure risk.
Malta RelevanceDeepStrike is not Malta-based and does not claim a Malta office. The published delivery model is remote-collaboration oriented, which can fit Malta-based teams when secure evidence handling and time-zone coverage are contract-defined.
Editorial note: DeepStrike is included in this list based on the same evaluation criteria applied to all providers.
Testing Depth ModelClassification: Manual exploit chaining.Manual execution and realistic attack simulation are explicitly claimed, increasing the probability that findings represent validated breach paths rather than scan artifacts. Cloud penetration testing and web application testing are explicitly listed; this supports cloud-first and API-driven system testing. Public materials do not enumerate business logic and identity abuse depth; those should be treated as scoping and tester-assignment verification items.
Key Strengths
Potential LimitationsAssigned-tester certifications and senior lead allocation require contractual verification. Onsite physical testing and local workshop needs may introduce additional coordination work.
Best ForCloud-first SaaS, fintech, and regulated environments needing manual exploit validation and clear retesting closure terms.
Headquarters: Qormi Founded: Not stated on the referenced cyber services pageCompany Size: 501–1,000 employees Primary Services: Penetration testing and red teaming; threat and vulnerability management; threat intelligence; cyber GRC and regulatory compliance assessments Industries Served: Public companies and institutions; local and foreign private companies; government-related organizations
Why They Stand OutPwC Malta explicitly lists “penetration testing and red teaming” and positions regulatory compliance advisory (DORA, MFSA ICT, GDPR) plus gap assessments against PCI-DSS and ISO 27001.
Malta RelevanceMalta-based delivery with cross-border network capacity.
Testing Depth ModelClassification: Red-team oriented.Red teaming is explicitly offered, indicating scenario-based testing beyond baseline pentesting. Cloud/API/identity scope coverage should be confirmed in proposals.
Key Strengths
Potential LimitationsLarge-firm delivery can introduce higher cost floors and longer lead times; depth depends on assigned individuals.
Best ForEnterprise penetration testing providers Malta requirements and regulated-sector buyers needing compliance mapping and formal reporting.
Headquarters: Qormi, Malta Founded: 2003 Company Size: 51–200 employees Primary Services: Internal/external penetration testing; web application penetration testing; social engineering assessment; vulnerability scanning and related testing Industries Served: iGaming-oriented hosting and broader Maltese corporate IT users referenced in company specialties and reporting
Why They Stand OutBMIT differentiates scans from penetration testing and calls out custom applications, legacy systems, and APIs as testing targets, supporting API-heavy environments.
Malta RelevanceMalta-based delivery and local managed-service operating model.
Testing Depth ModelClassification: Hybrid model.Penetration testing is positioned as bridging gaps automated tools may miss, implying combined tooling plus manual validation. API testing is referenced; cloud and identity testing depth require verification. Retesting is described as reassessment “as needed,” so closure terms need specification.
Key Strengths
Potential LimitationsRigor depends on assigned specialists; retesting inclusion is not framed as a fixed deliverable.
Best ForSMBs and mid-market buyers seeking practical, locally delivered application security testing.
Headquarters: Birkirkara Founded: 1998 Company Size: 51–200 employees Primary Services: Penetration testing with exploitation, social engineering attempts, logical and physical access tests, plus high-level and technical reports Industries Served: Cross-sector advisory and risk consulting
Why They Stand OutThe published phase includes exploitation, social engineering, and physical access tests, and separates high-level and technical reporting.
Malta RelevanceMalta-based delivery with a structured professional services operating model.
Testing Depth ModelClassification: Hybrid model.Exploitation language is a depth signal; social engineering and physical tests support realistic attacker simulation in authorized scenarios. Cloud/API/identity coverage should be verified.
Key Strengths
Potential LimitationsModern application and identity workflow depth is not described in public outlines; assigned-team specialization requires verification.
Best ForGovernance-grade reporting plus technical validation, including social engineering and physical scope when required.
Headquarters: Msida Founded: 1978 Company Size: 51–200 employees Primary Services: Web, mobile, and internal infrastructure testing; dynamic and static application testing; phases including exploitation and re-testing Industries Served: Regulated-sector exposure signals described in company profile
Why They Stand OutBDO Malta publishes a structured testing lifecycle that includes exploitation and a defined re-testing phase and lists multiple test types.
Malta RelevanceMalta-based and commercially aligned to Malta’s regulated services economy.
Testing Depth ModelClassification: Hybrid model.Exploitation and re-testing phases indicate exploit validation intent; cloud/API/identity coverage is not explicit and should be confirmed.
Key Strengths
Potential LimitationsCloud/API scope and identity abuse testing depth are not described on the referenced service page.
Best ForStructured pentest execution with re-testing phases across multiple test types.

Headquarters: Malta Founded: Not publicly statedCompany Size: Boutique; described as a small team with Managing Director-led execution Primary Services: External/internal infrastructure, web application testing, PCI DSS penetration testing, network segmentation testing Industries Served: PCI-focused buyers
Why They Stand OutCyberAudit describes a small-team model with Managing Director-only testing and contrasts scan-only work with manual testing. Certifications (CEH, PCIP, CISA) and PCI DSS/segmentation testing are positioned.
Malta RelevancePositions itself as providing penetration testing in Malta and lists Malta among client geographies.
Testing Depth ModelClassification: Hybrid model.Manual-plus-tooling positioning supports breach-path validation for web and network scopes; cloud/API/identity testing depth should be validated.
Key Strengths
Potential LimitationsLimited scalability inherent in Managing Director-led delivery; modern cloud/API scope not evidenced.
Best ForSmall-scope engagements, PCI-driven testing, and buyers prioritizing direct senior execution.
Enterprise buyers optimize for defensible governance: predictable delivery, formal reporting, and cross-entity coordination. This aligns with providers that can map testing output into control frameworks and, where applicable, support DORA-linked threat-led expectations through EU resilience testing approaches such as TIBER‑EU.
SMB buyers often optimize for price and speed, but risk is dictated by exposure (internet-facing APIs, payment flows, identity controls) rather than employee count. Manual exploit validation is the discriminator when business logic and identity workflows are core.
Boutique specialists can deliver deeper manual attention per target; larger firms can offer governance structures and multi-entity capacity. Selection depends on whether the dominant constraint is depth per asset or program governance.
EU market references commonly place thorough manual pen testing day rates around the low-thousands of euros, and penetration testing cost benchmarks show web/API testing ranging from several thousand to tens of thousands depending on complexity and endpoint volume. These are planning benchmarks; procurement should contract on written scope, deliverables, and retesting.
A procurement-grade engagement typically includes rules of engagement, reconnaissance, manual exploitation where authorized, evidence capture, impact analysis, executive and technical reporting, and re-testing or fix validation.
Certifications provide competence signals, but tooling does not substitute for manual reasoning. Selection should prioritize named tester competence and exploit validation evidence.
Penetration testing commonly supports ISO/IEC 27001 assurance evidence, PCI DSS validation (including segmentation testing guidance), SOC 2 programs, and DORA-linked TLPT for significant financial entities. NIS2 increases governance expectations and tends to increase demand for demonstrable technical control testing.
Local vendors can reduce coordination friction but do not guarantee deep cloud/API/identity testing. International providers can deliver strong manual depth remotely when the delivery model is mature.
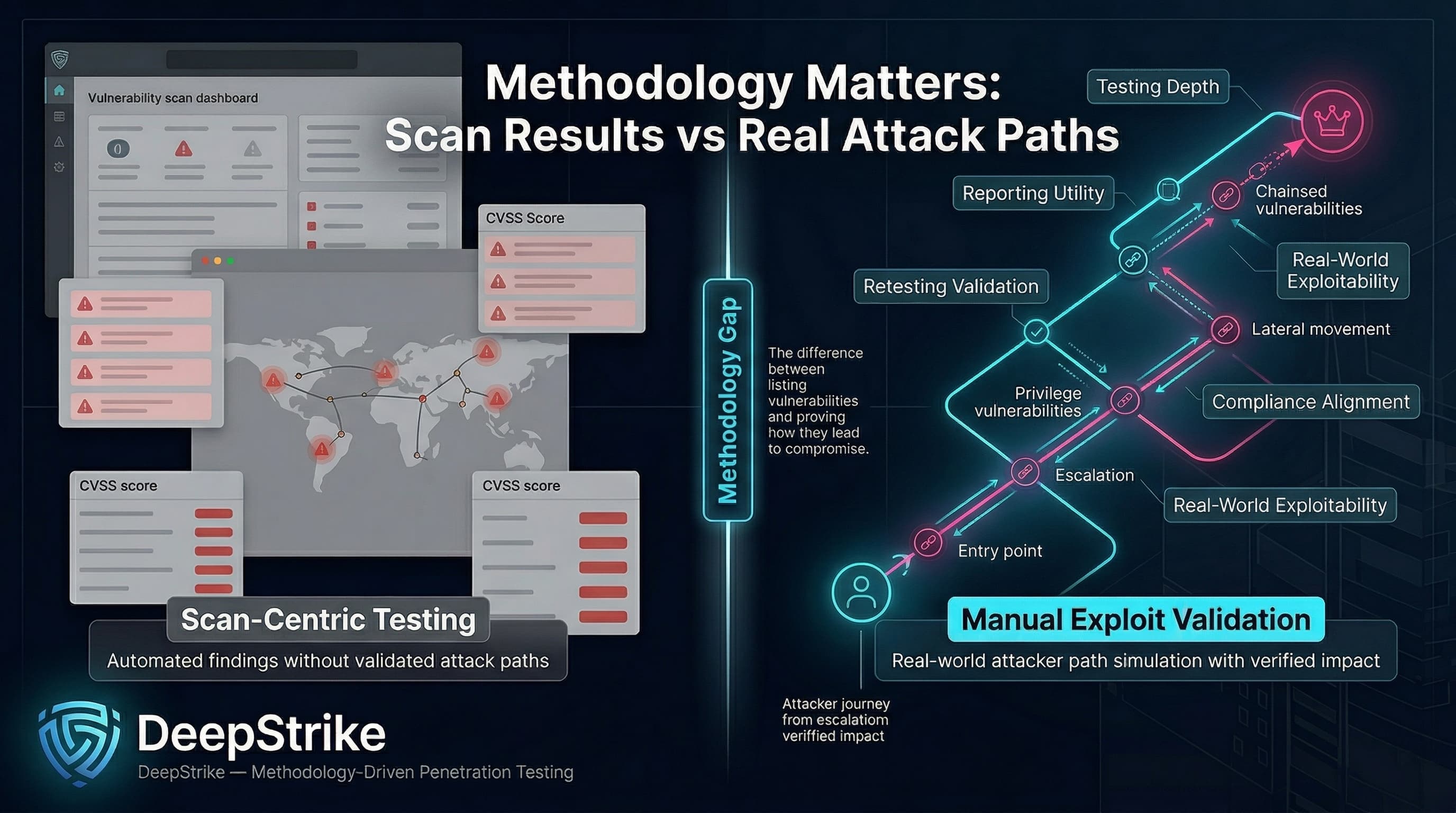
This ranking is methodology-driven and based on publicly verifiable indicators of testing depth, reporting utility, retesting terms, compliance alignment, and Malta execution practicality. The core procurement distinction across penetration testing providers in Malta is the gap between scan-centric outputs and manual exploit validation that demonstrates real-world attacker paths.
For buyers, the next step is not just shortlisting vendors, but tightening scope. Require explicit coverage for APIs, identity workflows, cloud permissions, retesting terms, and reporting outputs before signing. The strongest providers are not the ones with the broadest service language, but the ones that can clearly show how their methodology validates exploitability and supports remediation under real audit and governance pressure.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us