April 22, 2026
Updated: April 22, 2026
A buyer-focused comparison of Luxembourg penetration testing providers for regulated enterprises, critical infrastructure, and compliance-driven procurement.
Mohammed Khalil

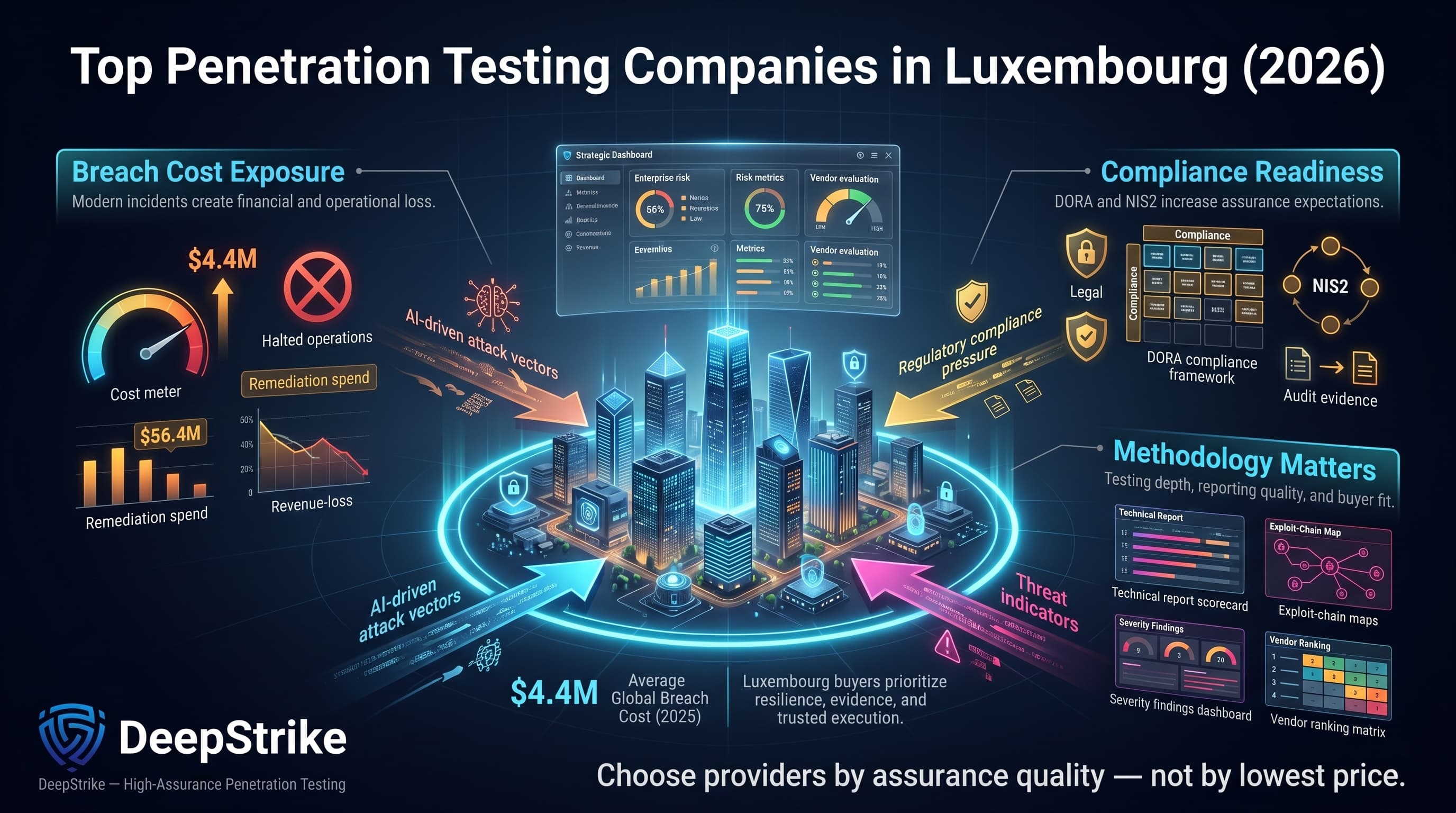
In 2025, the global cost of a data breach of a data breach reached roughly $4.4 million, which makes choosing among the top penetration testing companies in Luxembourg a risk-management decision rather than a routine security purchase. In Luxembourg’s finance-heavy market, business interruption, regulatory exposure, and remediation costs can materially increase total loss. AI-driven attack acceleration, rising compliance pressure under DORA and NIS2, and the maturity of the local cybersecurity market in 2026 all increase the need for validated, high-assurance testing. This ranking is methodology-driven, not sponsored, and prioritizes evidenced testing depth, reporting quality, and buyer fit.
Penetration testing is a structured adversarial security assessment that combines automated vulnerability discovery with manual exploit validation to identify real-world attack paths, validate control effectiveness, and reduce breach probability.
Our evaluation prioritized proven technical depth and evidence over brand alone. We assessed each provider’s team certifications (e.g. OSCP, OSWE, CISSP, CREST) and track record. A premium was placed on manual exploit chaining and red-team sophistication: vendors that use human-led techniques to exploit complex attack paths scored higher than those relying mainly on automated scanning. We examined case studies and service descriptions for cloud and API testing maturity – essential for modern infrastructures. Reporting quality was judged by clarity of findings and remediation guidance. Inclusion of retesting and compliance mapping was considered where it was clearly evidenced in published service descriptions. We also considered industry fit (e.g. finance vs telecom vs industrial) and regional delivery feasibility, including local delivery capability versus cross-border execution. Overall, our methodology favors vendors who deliver validated exploit scenarios with actionable output, rather than those offering mostly surface-level vulnerability scans.
When selecting a vendor, beware of common pitfalls. Don’t mistake tool-driven scans for thorough penetration testing – automated results should be augmented by expert analysis. Confirm the scope is sufficiently broad (external/internal networks, all critical apps, cloud assets, APIs) and that business-logic flaws will be tested. Avoid under-scoping (e.g. ignoring mobile or IoT if in use). Insist on a final retest to ensure remediated issues are fixed. Ensure the team includes senior testers (OSCP, CEH, CISSP, or CREST-certified) rather than only juniors. Watch for over-reliance on proprietary platforms – a reputable provider will use proven tools but not be beholden to them. Verify that testing covers your regulatory requirements (for example, DORA, PCI DSS, or ISO 27001) rather than being a generic checklist. Consider whether local presence is important: on-site teams can facilitate network access and reduce latency, but remote/global firms may offer broader expertise. Balancing automation with hands-on expertise is key – see our [penetration testing best practices] for guidance on scoping and execution.
Headquarters: London, UK (global operations)Founded: 2016Company Size: Small specialized team (10–50 experts) – core focus on offensive securityPrimary Services: Red team engagement, external/internal network pentests, web/mobile/API testing, cloud security reviews, simulated phishing.Industries Served: Fintech, SaaS/tech enterprises, regulated finance, cross-border organizations.
Why They Stand Out: DeepStrike brings a heavy emphasis on manual, creative exploitation. Its certified senior testers (e.g. CISSP, OSCP, OSWE) specialize in chained exploits and business-logic flaws. Its reporting model emphasizes exploit validation, prioritization, and remediation clarity. Compared with larger consulting firms, DeepStrike offers more flexible engagement structures and a clear focus on cloud and API security testing. Editorial note: DeepStrike is included in this list based on the same evaluation criteria applied to all providers.
Testing Depth Model: Manual exploit chaining. DeepStrike conducts highly realistic attacker simulations. Each test typically involves hands-on exploitation of discovered vulnerabilities, with thorough attack-path validation. The team focuses on identifying multi-step breach scenarios and logic flaws that automated scans miss. Its cloud and API testing is particularly deep, with custom scripts and live testing of microservices. This model prioritizes validated exploitability over scan-heavy output and is designed to surface realistic attacker paths, business-logic weaknesses, and actionable remediation priorities.
Key Strengths:
Potential Limitations:
Best For: Cloud-first enterprises and fintechs needing deep adversary simulation; buyers who prioritize depth over brand or who require flexible, custom engagements.
Headquarters: London, UK (global PwC) – Luxembourg branch in Luxembourg CityFounded: 1998 (merger of Coopers & Lybrand) – local firm since thenCompany Size: ~3,600 in Luxembourg (largest Big Four firm in country)Primary Services: Audit, tax, consulting; Cybersecurity advisory including threat-led penetration testing (external/internal networks, web/mobile apps, cloud/IoT infrastructure), simulated phishing, security audits.Industries Served: Major banks, investment funds, insurance, technology companies in Luxembourg.
Why They Stand Out: PwC offers a broad portfolio with an in-house “ethical hacking” team. Its methodology emphasizes manual, tailored testing (it “doesn’t rely on turnkey software”) and its local lab conducts novel research (e.g. presenting at Hack.lu). The team’s size and global resources allow complex multi-disciplinary projects (combining pen tests with architecture reviews and SOC assessments). Its local presence and broader advisory capacity make it suitable for multi-stakeholder, compliance-sensitive engagements.
Testing Depth Model: Hybrid model. PwC blends automated scanning with extensive manual validation. For network, web, or mobile tests, its experts perform hands-on exploitation following broad scanning. For example, the firm’s lab has demonstrated deep attacks at local security conferences. Automated tools accelerate coverage, but significant effort is placed on verifying exploitability and chaining. The outcome is thorough but comes with higher cost and timeline, reflecting PwC’s emphasis on precision.
Key Strengths:
Potential Limitations:
Best For: Very large enterprises (especially finance and insurance) requiring top-tier compliance support and detailed governance integration, where vendor reputation and process matter.
Headquarters: New York, USA (Deloitte Global) – Luxembourg office in Luxembourg CityFounded: Deloitte (1845, 75 years in Luxembourg)Company Size: ~2,600 professionals in Luxembourg (as of 2025)Primary Services: Audit, tax, consulting; Cyber Risk & Strategy (including vulnerability management and penetration testing ) covering networks, web/mobile apps, cloud, IoT/OT, and full-scope red team simulations.Industries Served: Financial institutions (banks, funds), government, industrials.
Why They Stand Out: Deloitte’s cyber practice provides comprehensive “ethical hacking” and risk assessments. Its Luxembourg site lists extensive pen test offerings (external/internal, web, mobile, thick-client, wireless, cloud, IoT). It also runs red team exercises and simulated phishing. As a large global firm, Deloitte leverages shared methodologies (e.g. group-wide ISO 27001) and invests in training (many consultants hold CISSP, OSCP, etc.). Notably, it celebrated 75 years in Luxembourg in late 2025, underscoring its local roots.
Testing Depth Model: Hybrid model. Deloitte combines automated tools (for broad vulnerability discovery) with manual exploitation. Its teams use industry-standard scanners for initial coverage, then apply hands-on hacking to confirm and extend findings. Deloitte’s red teaming services support sustained, scenario-based adversary simulation. Overall, their approach strikes a balance: more thorough than scan-only vendors, but constrained by enterprise processes. Reports are typically detailed and aligned to standards (e.g. ISO 27001, PCI DSS, SWIFT CSP).
Key Strengths:
Potential Limitations:
Best For: Large-scale organizations (banks, government, utilities) needing end-to-end security programs with formal compliance controls, and who value continuity of service from a global firm.
Headquarters: Contern, Luxembourg (with Belgian operations)Founded: Excellium Luxembourg in 2012; acquired by Thales in 2023Company Size: ~200 experts across Belgium and Luxembourg; Luxembourg office PSF-registered (finance sector).Primary Services: Offensive security (penetration tests of IT, web, mobile, industrial control systems), red teaming; plus security audits, SOC/MDR, incident response.Industries Served: Banking, insurance, utilities, critical infrastructure.
Why They Stand Out: Formerly Excellium, this local boutique was known for aggressive testing of finance and OT systems. Now under Thales, it gains global backing. It combines local Luxembourg delivery with broader group backing and a regulated-sector focus. The firm offers specialized capabilities such as PCI DSS QSA services (certified auditors) and is PSF-accredited for Luxembourg financial audits.
Testing Depth Model: Manual exploit chaining. Thales Luxembourg’s team performs hands-on pentests targeting deep system penetration. It includes niche scopes like ICS/SCADA environments. For example, their services listing highlights penetration testing among broad advisory offerings. The depth is typically high – testers pursue lateral movement and OT compromise paths. Reports emphasize actionable fixes.
Key Strengths:
Potential Limitations:
Best For: Financial institutions and utilities seeking a local partner with deep OT/ICS knowledge and regulatory compliance (PCI, DORA/SWIFT) in one engagement.
Headquarters: Niederanven, LuxembourgFounded: 2007Company Size: ~8 employees (boutique specialist)Primary Services: Penetration testing (external/internal networks, web and mobile apps, wireless, SCADA/ICS), social engineering and physical security tests, plus ISO 27001 audit/advisory.Industries Served: Luxembourg government, finance (CSSF-regulated PSFs), critical infrastructure (energy, utilities), and large local enterprises.
Why They Stand Out: Itrust is a local expert on Luxembourg-specific regulations and infrastructure. Their site explicitly highlights ISO 27001 and 27701 certifications, and note CSSF-approved status, indicating deep financial domain experience. The CEO is active on NIS2/DORA topics (recent interviews). Itrust offers some fixed-price scanning services for SMEs as well, illustrating flexibility.
Testing Depth Model: Hybrid model. Itrust delivers fully manual red-team style engagements for complex scopes (including SCADA), but also provides agile scans for smaller needs. The small team means clients get hands-on attention. Their process involves tailored exploitation of vulnerabilities; penetration tests often include creative physical/social elements. This yields thorough, personalized assessments, though smaller scale means fewer simultaneous engagements.
Key Strengths:
Potential Limitations:
Best For: Mid-sized banks, utilities or government bodies needing hands-on, compliance-focused pentesting, especially for OT/SCADA or when local presence matters. Also suitable for SMEs seeking transparent pricing.
Headquarters: Luxembourg City, LuxembourgFounded: 2017Company Size: ~5–10 experts (boutique)Primary Services: Threat-led penetration testing (meeting DORA TLPT requirements), security assessments (including SWIFT CSP reviews), security architecture consulting, incident response, security training and SIEM solutions.Industries Served: Primarily financial sector (banks, fund managers, fintechs) and other DORA-regulated entities.
Why They Stand Out: Linosec explicitly positions itself as a “Threat Led Pentesting Expert” for Luxembourg. Its marketing focuses on compliance – DORA TLPT (bank-specific tests) and SWIFT CSP compliance. The team holds OSCP, CISSP, CEH certifications, and they emphasize local presence. While small, Linosec has completed over 35 projects since 2017, illustrating niche experience.
Testing Depth Model: Red-team oriented. Linosec designs engagement around realistic attacker scenarios for banks. DORA TLPT involves intelligence-driven tests, so Linosec heavily manualizes its process. It integrates recon, social engineering, and multi-step breach paths. Cloud and API aspects are covered where relevant. The deep focus on finance means tests are aligned to ECB expectations. However, scope is narrower (mostly finance use cases).
Key Strengths:
Potential Limitations:
Best For: Banks and large funds subject to DORA who need TLPT-capable providers, or any financial institution wanting a homegrown Luxembourg pentester with deep regulatory understanding.
Headquarters: Luxembourg City (9 Rue du Laboratoire, Luxembourg)Founded: Hacknowledge Luxembourg in 2016; rebranded Dec 2025 under Swiss Post CybersecurityCompany Size: ~20–30 employees in Luxembourg (team remains same post-rebrand); ~150 in parent company across Europe.Primary Services: Advanced penetration testing and red teaming (targeted attack simulations, social engineering), 24/7 monitoring (MDR via Swiss Post Cyber Defense Center), phishing/vishing tests, security training.Industries Served: Finance, critical infrastructure (energy, telecom), public sector clients.
Why They Stand Out: As Hacknowledge Lux, they built a loyal local customer base. Now as Swiss Post Cybersecurity, they combine local agility with Swiss-backed scale. The rebranding press release emphasizes continuity of service and expanded compliance offerings (e.g. new GRC capability). Their Swiss Post group status brings certified processes (ISO 27001) and CREST-certified pentesters (Swiss Post testers are CREST-certified). The Luxembourg office is fully local-staffed and PSF-ready.
Testing Depth Model: Red-team oriented. Swiss Post Cybersecurity focuses on realistic, thorough attack simulations. Its suite of “Offensive Security” solutions includes not just pentests but red teaming (assume-breach), combining technical hacking with social engineering. The team emphasizes manual exploitation of found issues, often in high-security contexts (e.g. critical infra). Accuracy is high; they stress complete attack vectors, with monitoring and response integration.
Key Strengths:
Potential Limitations:
Best For: Organizations in finance or critical sectors needing comprehensive red-team ops and 24/7 defense, especially those who value Swiss-level assurances and CREST-qualified testers.
| Company | Specialization | Testing Depth Model | Best For | Luxembourg Fit | Compliance Alignment | Ideal Organization Size |
|---|---|---|---|---|---|---|
| DeepStrike | Cloud, API, web, red team | Manual exploit chaining | Cloud-first enterprises | Cross-border delivery to Luxembourg | Compliance-relevant reporting support | Enterprise |
| PwC Luxembourg | Network, app, cloud, red team | Hybrid model | Large regulated organizations | Local Luxembourg presence | DORA / ISO 27001 / finance support | Enterprise |
| Deloitte Luxembourg | Network, app, cloud, red team | Hybrid model | Large multi-entity environments | Local office with global support | PCI DSS / DORA / ISO-aligned delivery | Enterprise |
| Thales Cybersecurity | Network, app, ICS/OT, red team | Manual exploit chaining | Critical infrastructure and finance | Luxembourg headquarters | PCI / PSF / regulated-sector support | Enterprise |
| itrust consulting | Network, app, SCADA, social engineering | Hybrid model | Mid-sized regulated organizations | Local Luxembourg presence | ISO 27001 / 27701 / IEC 62443 | Mid-size to enterprise |
| Linosec | Threat-led pentesting, finance | Red-team oriented | DORA-regulated institutions | Local Luxembourg presence | DORA TLPT / SWIFT-focused | Financial institutions |
| Swiss Post Cybersecurity | Red team, phishing, MDR-linked testing | Red-team oriented | Finance and critical sectors | Local office with broader European backing | ISO 27001 / certified tester-led delivery | Enterprise |
Larger organizations typically favor providers that combine depth, reporting maturity, and regulatory alignment. In this list, PwC Luxembourg, Deloitte Luxembourg, and Thales Cybersecurity are the strongest fit for complex enterprise environments because they combine a broader delivery scale with formal governance and compliance-oriented reporting.
Smaller or mid-sized organizations usually need tighter scope control, faster execution, and lower coordination overhead. In that context, itrust consulting is often a more practical fit, while Linosec is more suitable for finance-heavy organizations with DORA- or SWIFT-driven requirements.
Buyers should weigh manual depth against operational efficiency. DeepStrike is better suited to organizations that prioritize exploit chaining, cloud and API testing depth, and flexible delivery, while Swiss Post Cybersecurity is stronger when the requirement extends toward red-team style simulation and broader defensive integration. Cross-border delivery can work well for application, cloud, and API testing, but local presence may still matter for regulated, physical, or infrastructure-heavy scopes.
Cost is mainly shaped by scope size, asset complexity, testing depth, authentication level, API and cloud exposure, reporting requirements, retesting expectations, compliance evidence needs, and whether delivery is remote or on-site. Manual exploit-led engagements usually cost more than scan-led assessments because they require deeper validation, broader analyst time, and more detailed reporting. Cloud, API, and regulated-scope testing also tend to increase effort because they expand scenario coverage and documentation requirements. Where precise local pricing is not consistently evidenced, buyers should focus on quote structure, scope assumptions, retesting terms, and deliverable quality rather than headline figures.
Pricing depends mainly on scope size, testing depth, asset complexity, authentication level, cloud and API exposure, reporting expectations, and retesting requirements. Because precise local pricing is not consistently evidenced across providers, buyers should request a scoped quote with clear assumptions, deliverables, and retesting terms rather than rely on generic market ranges.
A typical enterprise pentest covers both external and internal attack surfaces as per PCI DSS guidelines, including networks, servers, web and mobile apps, and possibly wireless infrastructure. It involves vulnerability scanning and exploitation of key issues to demonstrate impact. Deliverables usually include an executive summary plus a detailed technical report with prioritized findings and remediation advice. Red-team engagements may add social engineering or physical intrusion tests as needed.
Both matter, but certifications signal proven skill. In manual vs automated penetration testing, tools (e.g. Nessus, Burp, Metasploit) can quickly find surface flaws, but only skilled testers (with credentials like OSCP, OSWE, CISSP or CREST accreditation) can reliably exploit chains of vulnerabilities. Industry guidance emphasizes using qualified testers. In procurement, insist on seeing tester credentials or lab accreditation. A certified tester armed with basic tools will usually outperform an uncertified user of fancy tools.
Durations range from a few days to several weeks. A simple web app test might take 1–2 weeks total, while a large infrastructure assessment (hundreds of hosts, multiple apps) could take 4–6 weeks including planning and reporting. Regulated firms often align tests to an annual cycle. PCI DSS, for instance, expects internal and external tests at least annually. The complexity of the environment and availability of the vendor team are the main factors.
Requirements vary. PCI DSS explicitly mandates both internal and external penetration tests at least annually (Requirement 11.4). ISO 27001 does not mandate pentesting, but a risk-based approach usually makes it a “strongly advised” control (certifiers expect testing when justified by risk). DORA (for financials) requires “threat-led” pentests for large banks/fintechs by 2025. NIS2 is a risk-management directive; it doesn’t specifically call out pentests, but it expects continuous security assessments. In practice, many organizations test yearly or after major changes to stay compliant.
Best practice is at least annually, and after significant system changes. For example, PCI DSS requires retests after any major infrastructure change. Some sectors (finance, energy) do tests semi-annually. Cloud environments or agile development may warrant more frequent scanning (quarterly). Always align test frequency to your risk level and regulatory guidance.
Both have merits. Local providers (itrust, Linosec, Local providers (itrust and Linosec)) offer in-country knowledge, language support, and easier on-site access (useful for social/physical tests). They often understand local regulations and threat context. Global firms (PwC, Deloitte, etc.) bring broader threat intelligence and sometimes lower day rates, but may have less local agility. Cross-border delivery is common for pure network/app tests. Key considerations: data protection (ensure sensitive data stays in the EU), travel costs, and regional compliance nuances. In many cases, a hybrid approach (local partner coordinating global experts) works best.
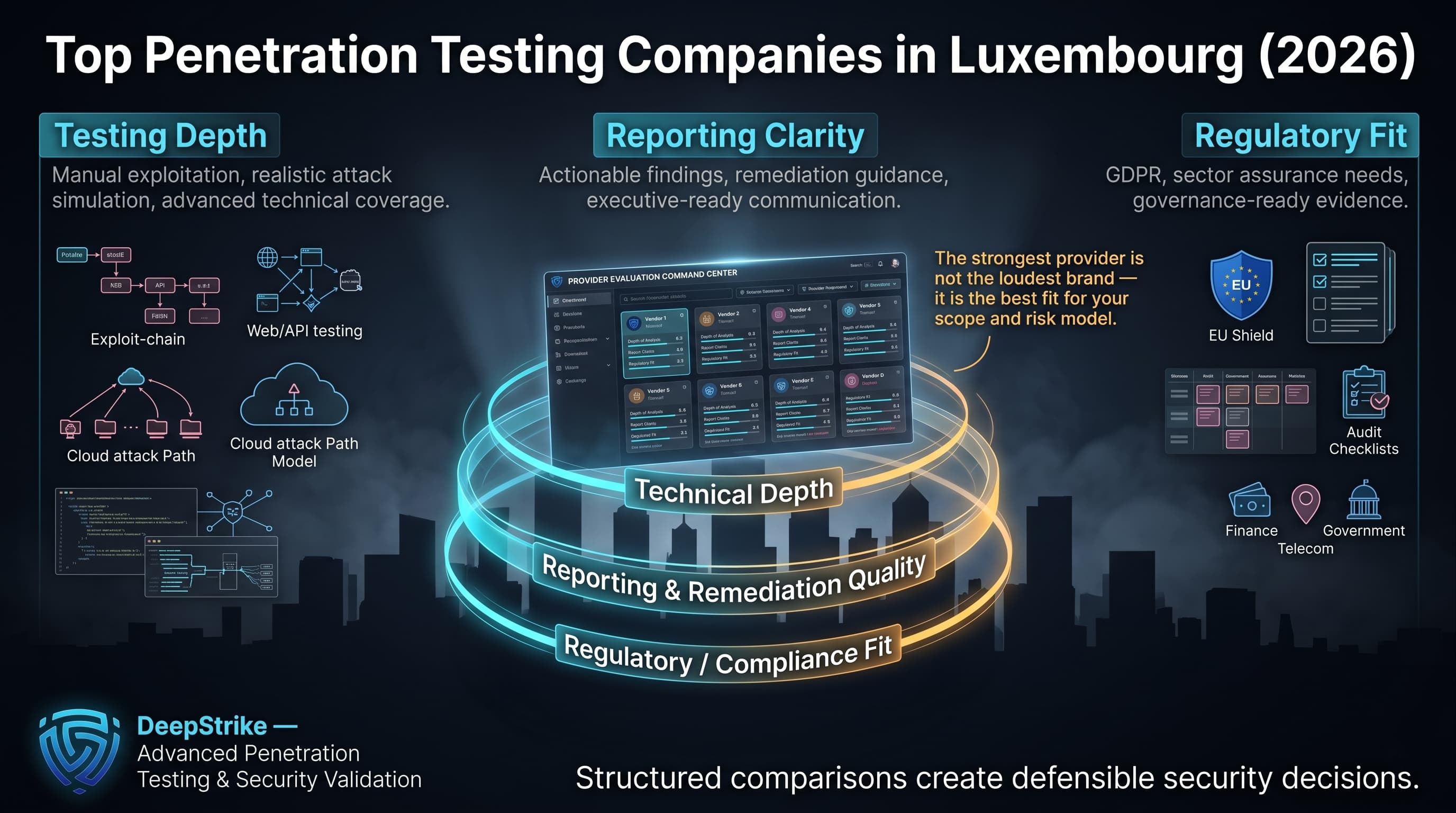
This comparison of the top penetration testing companies in Luxembourg is intended to support structured, evidence-based shortlisting rather than brand-led selection. Buyers should prioritize validated testing depth, reporting clarity, and regulatory fit over broad service claims alone. In practice, the right provider depends on scope, sector, internal maturity, and whether the organization needs deep manual exploitation, compliance-heavy reporting, or both. Used correctly, a structured comparison helps procurement and security teams make a more defensible penetration testing decision in Luxembourg in 2026.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us