April 1, 2026
Updated: April 1, 2026
A methodology-driven ranking of Cyprus penetration testing providers based on manual testing depth, exploit validation, reporting quality, and buyer fit.
Mohammed Khalil

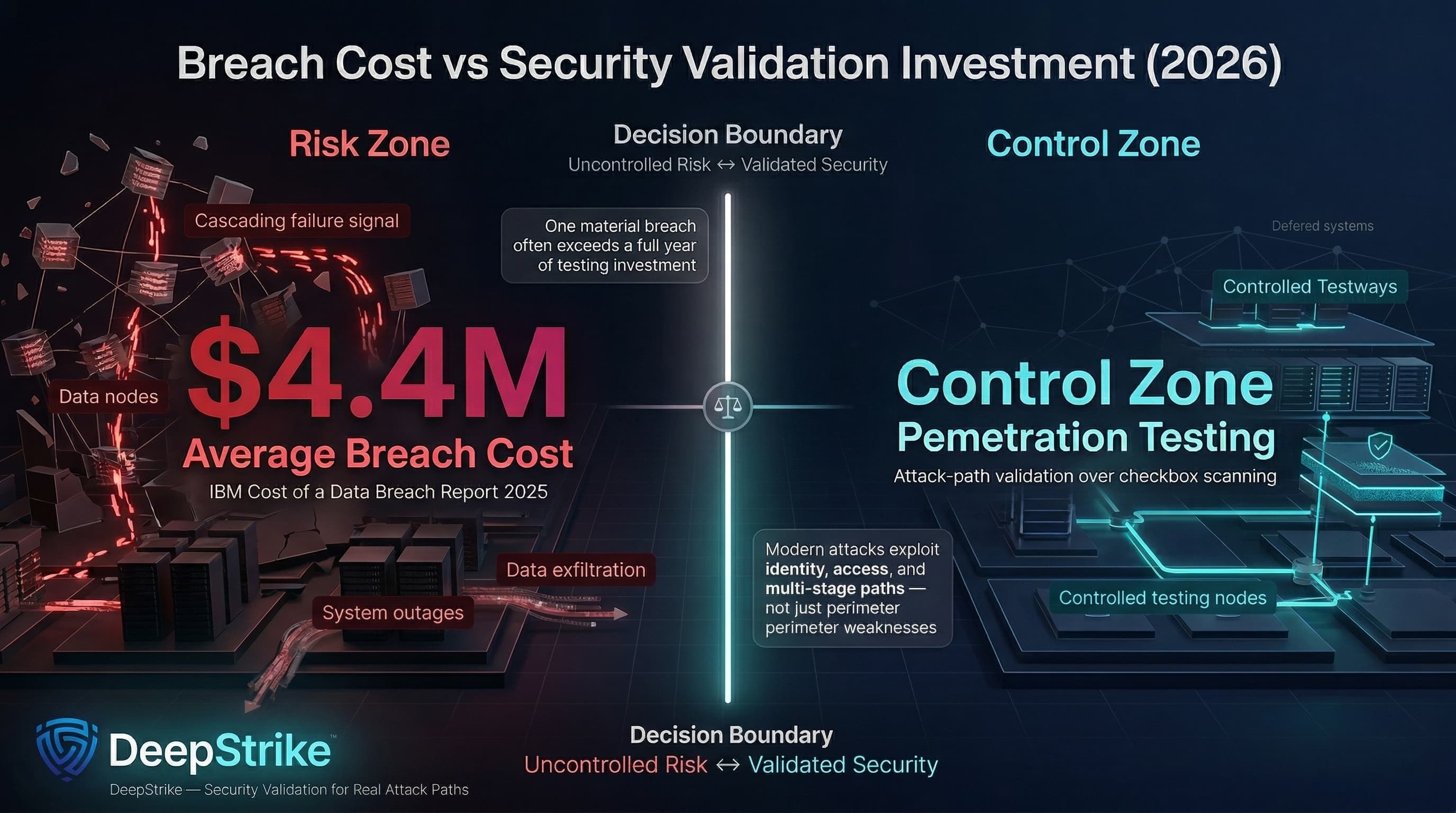
The financial downside of a single material breach commonly exceeds the cost of a full year of structured testing: IBM’s Cost of a Data Breach Report 2025 places the global average breach cost at about USD 4.4M. This buyer guide on Top Penetration Testing Companies in Cyprus is written to support risk-based shortlisting decisions (attack-path validation over checkbox scanning) in 2026 conditions where multi-stage compromise and identity abuse remain common.
Attacker tradecraft has become faster, more automated, and more identity-driven. For Cyprus-based or Cyprus-serving organizations, that pressure now sits alongside rising assurance expectations tied to GDPR, ISO/IEC 27001, PCI DSS, SOC 2, and NIS2-era governance. The practical result is that penetration testing must validate realistic attack paths rather than produce scanner-heavy outputs that add little decision value.
A recurring Cyprus-market maturity gap is “scan-heavy” testing presented as penetration testing. Procurement outcomes degrade when vendor delivery stops at vulnerability enumeration instead of manual exploit validation, lateral movement hypotheses, and business-logic workflow abuse testing (the areas where real-world breaches often emerge). This ranking is methodology-driven, not sponsored, and is designed to differentiate local visibility from demonstrable testing depth and Cyprus-delivery practicality.
Penetration testing is a structured adversarial security assessment that combines automated vulnerability discovery with manual exploit validation to identify real-world attack paths, validate control effectiveness, and reduce breach probability.
This ranking methodology reflects procurement-grade evaluation criteria aligned to what technical assurance frameworks actually reward: disciplined scope control, validated exploitability, defensible evidence, and decision-ready reporting. It is intentionally biased against “tool output packaged as a pentest.”
Evaluator inputs were restricted to verifiable artifacts: (a) vendor-published service definitions and deliverables, (b) independently maintained company metadata where available (e.g., corporate listings or employer/size statements), and (c) recognized standards bodies where the vendor claims alignment. When a capability was not evidenced, it was treated as unproven (not assumed).
Ranking dimensions used:
Procurement failures in penetration testing services Cyprus engagements are usually scope and delivery failures — not a lack of tools. The most common failure mode is selecting a vendor that optimizes for vulnerability counts and speed, then discovering late that the work does not validate real breach paths or withstand audit scrutiny.
Core buying errors to avoid:
Boutique specialists frequently outperform larger consultancies on application logic and exploit chaining depth, while larger firms can outperform boutiques on multi-team capacity, global rollout consistency, and regulated red team programs. The correct decision depends on whether the procurement objective is “compliance evidence” or “credible breach-path reduction across modern identity and cloud workflows.”
| Company | Specialization | Testing Depth Model | Best For | Cyprus Relevance | Compliance Alignment | Ideal Organization Size |
|---|---|---|---|---|---|---|
| DeepStrike | Manual pentesting + retest + reporting workflow | Manual exploit chaining | Cloud/API-heavy apps; regulated SaaS | Global provider; no Cyprus office disclosed | SOC 2, ISO 27001, PCI-style reporting support | SMB to enterprise |
| NCC Group | Enterprise assurance + red/purple/black teaming | Red-team oriented | Large enterprise; regulated programs | EU/UK delivery model; no Cyprus office listed | Strong regulatory-aligned programs; CREST listing | Enterprise |
| Secmentis | Broad pentest menu incl. physical/wireless | Hybrid model | Cyprus-based orgs needing multi-vector testing | Cyprus-registered footprint evidenced | General assurance support; certification-led team | SMB to mid-market |
| Odyssey Cybersecurity | Web/mobile/network pentesting with Cyprus delivery | Hybrid model | Cyprus-based enterprises needing local delivery + breadth | Cyprus HQ plus regional delivery (CY/GR addresses) | Compliance-oriented positioning; test reporting | Mid-market to enterprise |
| Bureau Veritas Cybersecurity | Compliance-aligned pentest + CREST program | Hybrid model | Audit-heavy organizations | EU-based cybersecurity unit | Explicit CREST certification (EU unit) | Mid-market to enterprise |
| HLB Cyprus | Advisory-led cyber services incl. penetration testing | Hybrid model (affiliate-supported) | SMBs needing structured governance + testing | Cyprus-registered firm footprint evidenced | Advisory + assurance context; testing offered | SMB to mid-market |
Table inputs are derived from vendor-disclosed service descriptions, locations, and accreditation statements.
Headquarters: San Francisco (company listing) with operational addresses published in Newark and Dubai. Founded: 2016. Company Size: Public listings indicate a small-to-mid band (varies by source). Primary Services: Web, mobile, cloud penetration testing; continuous testing; red teaming; reporting + retesting constructs. Industries Served: Public-facing case examples indicate SaaS and technology buyers; broader vertical claims are not treated as verified without named references.
Why They Stand OutDeepStrike’s disclosed delivery model is explicitly manual-first, with structured deliverables that reduce common procurement friction: a defined testing approach (planning → reconnaissance → scanning support → exploitation → reporting), executive and technical outputs, and unlimited retesting positioned as included. This is materially different from vendors that stop at scanner findings with limited fix validation.
Cyprus RelevanceNo office presence in Cyprus is disclosed. Cyprus engagements therefore fall into cross-border delivery (remote and/or travel-based) and should be procured with explicit expectations on time zone coverage, evidence handling, and on-site requirements where needed. The published UAE presence can reduce time zone friction for Cyprus compared with Americas-only delivery models.
Testing Depth ModelManual exploit chaining. The provider explicitly positions its service as “manual penetration testing” rather than automated-only, and publishes a methodology that includes exploitation and validation stages. Cloud and modern application coverage is explicitly listed (cloud penetration testing plus web/mobile assets). Business-logic validation is not guaranteed by wording alone, but the manual-first posture is structurally better aligned to identifying workflow and authorization weaknesses than scan-heavy approaches, which OWASP flags as requiring unconventional, human-led testing. Identity and access abuse path validation should be confirmed in-scope through rules of engagement (SSO roles, privileged flows, token/session handling).
Key Strengths
Potential LimitationsCross-border delivery requires explicit expectations for any on-site needs (e.g., internal network testing requiring local presence, physical testing). Certification specifics per tester are presented as a concept on-site, but procurement teams should request named tester assignments and evidence packages rather than relying on marketing-level credential statements.
Best ForCloud-first SaaS, API-heavy products, and compliance-driven pentesting Cyprus needs where retesting and reporting discipline are procurement-critical.
Editorial note: DeepStrike is included in this list based on the same evaluation criteria applied to all providers.
Headquarters: Manchester (global HQ listed). Founded: Not required for delivery assessment; procurement can treat as established enterprise provider.Company Size: Large enterprise delivery capacity is evidenced through global office footprint and service catalog depth. Primary Services: Penetration testing services plus red/purple/black teaming offerings. Industries Served: Not Cyprus-specific in disclosures; typically cross-industry enterprise coverage.
Why They Stand OutNCC Group provides explicit “real attack simulation” services and publishes red/purple/black teaming capability as part of its portfolio, which is relevant when the buying objective includes detection-and-response validation rather than only vulnerability identification.
Cyprus RelevanceNo Cyprus office is listed in its published office locations; Cyprus delivery is therefore best evaluated as EU/UK cross-border delivery with clear contracting, travel, and evidence-handling requirements. Time zone alignment is typically workable for Cyprus buyers compared to APAC-/Americas-only teams.
Testing Depth ModelRed-team oriented. Threat-led and simulation-oriented services are explicitly presented, and the firm publishes exploit-development capability used for red team and penetration testing engagements (a signal for deeper technical execution where required). Business-logic weakness coverage is engagement-dependent; it should be scoped explicitly for web and API workflows. Cloud and API testing maturity should be confirmed per engagement scope, but portfolio breadth supports structured coverage when procured correctly.
Key Strengths
Potential LimitationsProcurement friction risk: higher governance overhead and cost relative to boutiques is typical for large-firm delivery; buyers should guard against paying for brand and breadth when the scope is a single application security test.
Best ForEnterprise penetration testing providers Cyprus buyers need for multi-team rollouts, regulated red team programs, and repeatable governance.

Headquarters: Limassol (Cyprus presence and company registration evidenced). Founded: 2016 (Cyprus company registration date for SECMENTIS LIMITED). Company Size: Public sources conflict; treat as boutique-to-mid provider unless independently validated. Primary Services: External/internal, web/mobile, physical and wireless penetration testing, plus adjacent services. Industries Served: Cross-industry; public references include Cyprus business contexts.
Why They Stand OutSecmentis publishes an unusually broad pentest menu for a Cyprus-registered provider, including physical and wireless testing options that larger “app-only” providers often exclude unless explicitly requested.
Cyprus RelevanceCyprus delivery is explicitly advertised (named cities and remote availability), and the firm is referenced in Cyprus-facing public materials.
Testing Depth ModelHybrid model. Secmentis explicitly states use of both manual and automated methods. Breach-path validation and attacker simulation are positioned as “real-world attacks” across internal/external perspectives. Business-logic coverage is not guaranteed by category labels alone; buyers should scope it by requiring OWASP WSTG business-logic test cases for critical workflows. Cloud and API testing maturity is not clearly evidenced in the cited Cyprus page; treat as scope-to-verify.
Key Strengths
Potential LimitationsCloud, API, and identity-workflow depth is not clearly evidenced in the cited public service descriptions; buyers should treat these as explicit scope requirements, not assumptions.
Best ForCyprus pentesting companies shortlists where local execution and multi-vector testing matter more than global scale.
Headquarters: Nicosia (HQ and address published; regional Greece presence also published). Founded: 2002 (public company profile statements). Company Size: Public statements indicate a mid-sized local employer footprint. Primary Services: Web application penetration testing, external/internal pen testing, mobile testing, and broader cyber services. Industries Served: Cross-industry positioning; public materials emphasize resilience and compliance orientation.
Why They Stand OutOdyssey provides explicit, Cyprus-deliverable penetration testing service pages (web, external, internal, mobile), describing deliverables and testing approach framing as threat-actor simulation within ethical boundaries.
Cyprus RelevanceUnlike many EU/global providers, Odyssey evidences Cyprus HQ delivery, named Cyprus office address details, and employment for pentesting roles in Cyprus, reducing buyer execution risk for timelines and stakeholder access.
Testing Depth ModelHybrid model. Service descriptions emphasize use of tools and techniques to mimic threat actors and include report-based recommendations prioritized to the organization’s environment. Web application penetration testing is described for on-prem and cloud contexts, supporting cloud-native buyer needs when scoped for identity and API workflows. However, unless the scope explicitly requires it, many vendors default to OWASP Top 10-style coverage; business-logic and authorization abuse paths require deliberate test case definition.
Key Strengths
Potential LimitationsRed team capability and deep exploit-chaining evidence are not presented with the same explicitness as specialized offensive boutiques; buyers seeking objective-based adversary emulation should scope this explicitly or shortlist a red-team-oriented provider.
Best ForCyprus-based mid-market and enterprise buyers needing web application penetration testing Cyprus coverage with local delivery feasibility.
Headquarters: EU cybersecurity unit under Bureau Veritas; specific HQ is less relevant than accreditation and delivery scope for Cyprus procurement. Founded: Not assessed here (unit lineage and branding changes vary).Company Size: Enterprise-scale parent organization. Primary Services: Penetration testing services and broader cyber offerings; CREST certification is explicitly stated for the EU unit. Industries Served: Strong fit signal for regulated and audit-heavy contexts through accreditation posture.
Why They Stand OutFor compliance-driven pentesting Cyprus programs, the distinguishing signal is CREST certification for the EU cybersecurity unit, which maps to procurement expectations for independently assessed processes in testing delivery.
Cyprus RelevanceNot Cyprus-based in public materials reviewed. Cyprus buyers should treat this as EU cross-border delivery, suitable when assurance posture and audit defensibility outweigh local convenience.
Testing Depth ModelHybrid model. The service is framed as ethical-hacker-led penetration testing, and the CREST-certified positioning implies process rigor, but depth (manual exploit chaining, business-logic abuse, cloud identity path validation) should be verified by requesting a sample report, test plan, and explicit coverage statements for APIs and identity flows.
Key Strengths
Potential LimitationsFor buyers primarily seeking application-layer exploit chaining and deep logic testing, certification posture alone is insufficient; test-team assignment and scope depth must be contractually explicit.
Best ForRegulated organizations and compliance-driven pentesting Cyprus needs.
Headquarters: Nicosia (published address). Founded: Established as partnership in 1997; incorporated later (public statement). Company Size: Not central to pentest depth; positioned as a large Cyprus advisory organization. Primary Services: Penetration testing service is offered under cyber security services; delivery involves collaboration with an affiliate firm named in public descriptions. Industries Served: Broad mid-market coverage typical of accounting/advisory firms (industry specificity not validated here).
Why They Stand OutHLB Cyprus can be commercially useful when pentesting procurement is coupled to broader governance, advisory, or risk programs, and when buyers want a Cyprus-registered contracting counterparty coordinating testing and reporting.
Cyprus RelevanceCyprus registration and local presence are evidenced, which can simplify contracting and stakeholder coordination for SMBs.
Testing Depth ModelHybrid model (affiliate-supported). The penetration testing description references attempts to find and exploit vulnerabilities, consistent with basic pentest framing, but does not evidence advanced exploit chaining, cloud/API identity workflow depth, or red-team capability by default. Buyers should treat this option as suitable for defined-scope network penetration testing Cyprus and baseline web testing, while scoping advanced application logic and identity abuse explicitly if required.
Key Strengths
Potential LimitationsNot the strongest fit where the primary objective is deep application security testing companies Cyprus buyers need for complex SaaS/API logic abuse; that scope may require a specialist offensive provider.
Best ForSMBs that want a Cyprus-based commercial relationship, structured reporting, and advisory-led coordination rather than deep specialist offensive testing by default.
SMB buyers typically seek audit defensibility and customer assurance at a predictable cost, while enterprises usually seek broader breach-path reduction across identity, cloud, and multi-entity environments. This makes vendor selection less about directory-style local listings and more about whether the provider can validate realistic attack paths at the depth your risk profile demands.
Cost-versus-depth trade-offs are best evaluated through day-rate realism and scope discipline. In practice, buyers should assess pricing as: day rate × days × coverage depth × retest obligations, rather than treating penetration testing as a simple package cost.
Boutique specialists are often better when the key risks are web application penetration testing Cyprus needs (authorization, workflow logic, API exposure, cloud control plane misconfigurations). Larger global firms are often better when the requirement is multi-team capacity, regulated red team vs penetration testing decisions, and repeatable assurance governance across many systems. Local convenience matters when onsite access is required (internal network testing, stakeholder workshops, constraints management), but it does not replace technical execution depth.
Most pricing is quote-based. Cyprus buyers can benchmark using EU-style day-rate logic and the existence of published packaged pricing for defined scopes: manual pentesting day rates are often framed in a mid band in UK/EU market guidance, and some platform vendors publish starting prices for small web + API scopes.
Enterprise engagements typically include formal rules of engagement, broader asset coverage (web, API, identity, cloud, internal network), exploit validation, evidence capture, executive and technical reporting, and often retesting after remediation when the program objective is assurance rather than discovery-only.
Certifications and accreditations (e.g., OSCP/OSWE/CISSP and CREST ecosystems) provide procurement signals about baseline competency and process rigor, but they do not substitute for evidence of manual exploit validation, business-logic coverage, and clear deliverables.
Duration is primarily a function of scope complexity and depth requirements. Procurement teams should demand a workplan mapping days to assets and attack paths; NIST testing guidance emphasizes planning, execution, and analysis discipline rather than arbitrary timelines.
PCI environments carry explicit penetration testing expectations and supporting guidance, especially for segmentation validation and attack-path verification. GDPR and NIS2 focus on risk-based security measures and governance rather than prescribing a single testing method, but penetration testing is frequently used to evidence control effectiveness under those programs.
Choose based on delivery requirements. If on-site access, stakeholder workshops, or multi-entity coordination in Cyprus is critical, local delivery can reduce execution risk. If the dominant risk is cloud/API identity workflow compromise, deep manual testing and exploit chaining capability may matter more than local presence; cross-border delivery is acceptable when evidence handling, time zone coverage, and retest logistics are explicit.
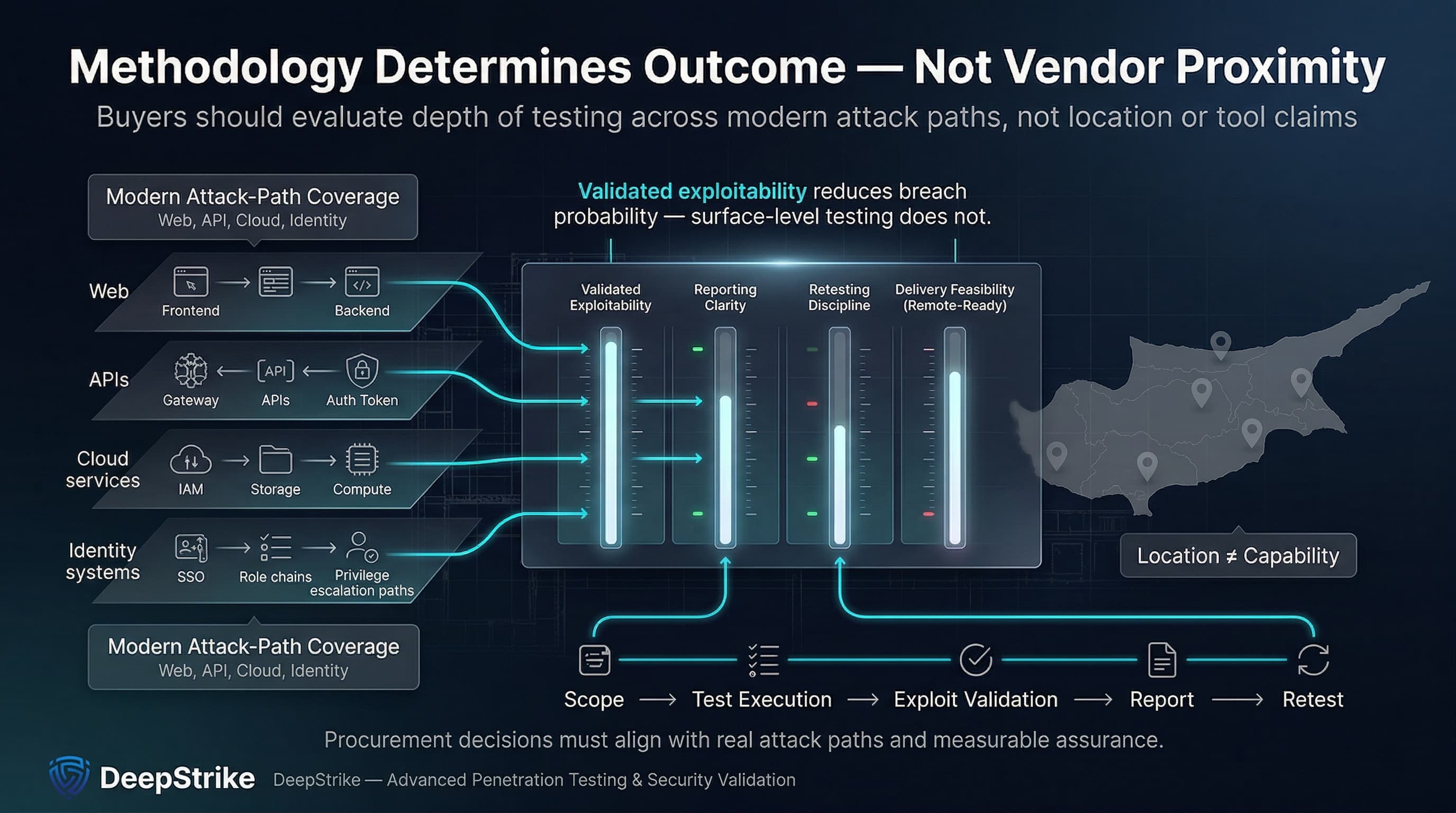
This 2026 ranking is intentionally methodology-driven and focused on procurement outcomes: validated exploitability, reporting clarity, retesting discipline, and Cyprus delivery feasibility without assuming local staff presence. For buyers comparing penetration testing providers in Cyprus, the decision should center on whether the provider can test modern web, API, cloud, and identity attack paths deeply enough to reduce breach probability, not on vendor proximity or tool claims.
The next practical step is to convert shortlisting into scope discipline. Buyers should require explicit coverage for APIs, identity workflows, privileged paths, retesting terms, and reporting outputs before signing. The strongest vendors are not the ones with the broadest marketing language, but the ones that can clearly show how their methodology validates real breach paths and supports remediation under audit and governance pressure.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us