September 2, 2025
Updated: May 14, 2026
An enterprise, multi-cloud guide for mapping requirements to controls and audit-grade evidence.
Mohammed Khalil

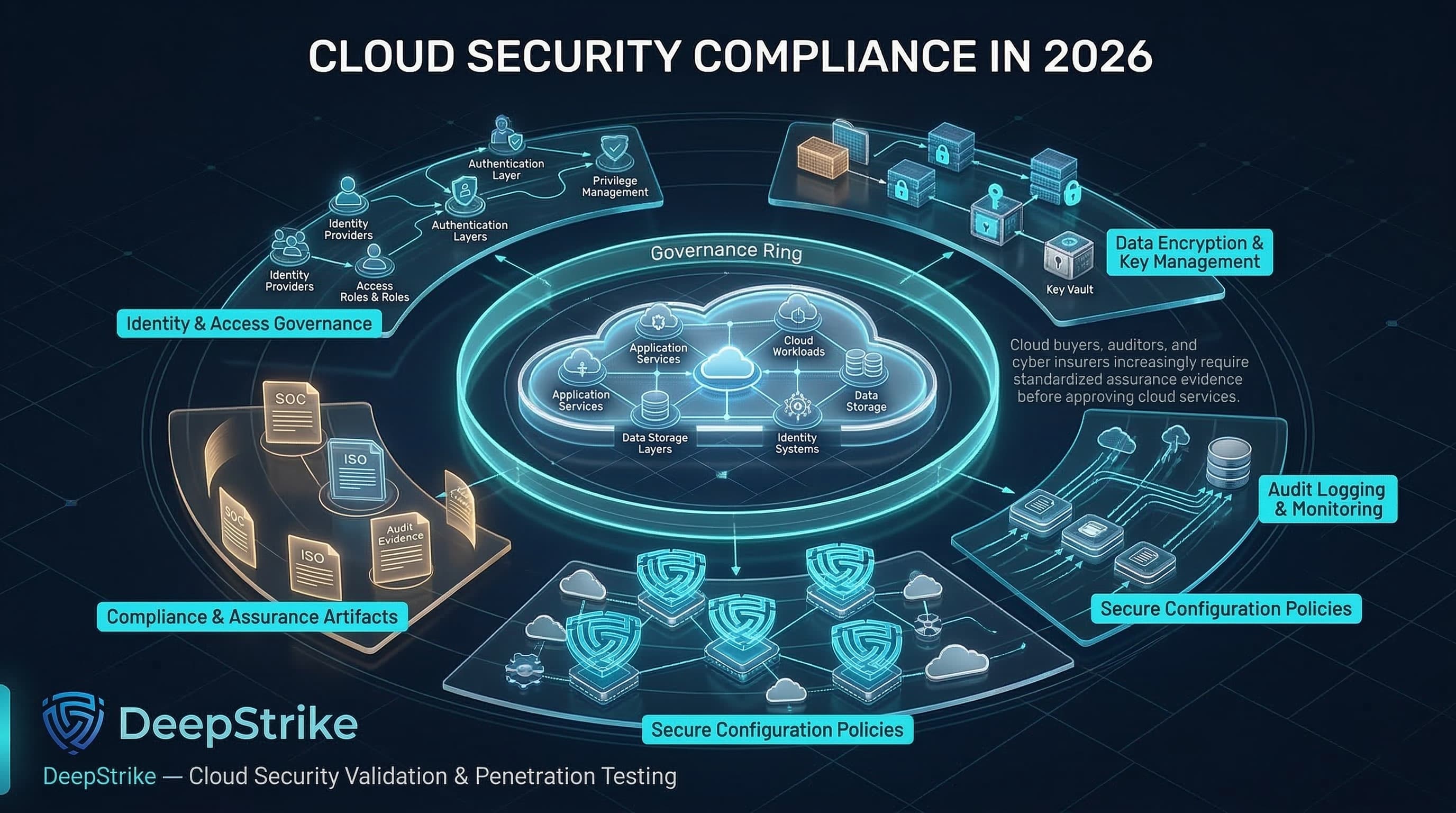
Cloud security compliance is an operational discipline that shapes identity boundaries, encryption designs, logging retention, configuration guardrails, and auditability. In 2026, buyers, auditors, and cyber insurers increasingly expect standardized assurance artifacts (for example SOC reports, ISO certifications, and control evidence) as a condition for doing business in cloud-delivered operating models.
Cloud provider attestations help, but they do not replace a practical cloud security compliance program for tenant-side controls. This is why cloud security compliance must be treated as an operating model for control ownership, evidence production, and continuous control validation rather than as a document collection exercise.
Your organization remains accountable for how identities are governed, how data is handled, how monitoring is configured, and whether you can prove control operation during audits and after incidents.
Cloud security compliance refers to the process of meeting legal, regulatory, contractual, and standards-based security requirements across cloud environments through documented controls, governance processes, technical safeguards, and verifiable evidence.
Cloud security compliance translates external requirements into controls that operate in cloud control planes and workloads, with repeatable evidence. The deliverable is controlled operation plus proof: policies, configurations, logs, approvals, and test outcomes that show controls are implemented and maintained.
Cloud differs from on-prem compliance because the control plane is identity-driven and change is continuous. Mismanaged privilege can reconfigure exposure, disable logging, or weaken encryption without touching traditional network boundaries. Managed services also change the evidence model: the provider may operate controls for underlying infrastructure while the customer must evidence tenant-side controls (identity, data governance, monitoring, configuration governance).
Example boundary: in object storage, the provider secures facilities and core service operation; the customer must restrict public access, define policies, enable logging, and enforce encryption and retention for the data they store. That distinction is why provider certifications cannot, by themselves, prove that a customer has implemented compliant identity, data handling, logging, and retention controls inside the tenant.
Organizations pursue cloud compliance to meet legal and regulatory obligations, satisfy customer and procurement requirements, improve governance maturity through explicit control ownership, and reduce audit friction with repeatable evidence.
Compliance should be treated as a minimum baseline, not a substitute for penetration testing for compliance. A cloud program can still be fragile against credential theft, misconfiguration, or supply-chain compromise if controls are not continuously enforced and validated.
| Attribute | Cloud Security Compliance | Cloud Security |
|---|---|---|
| Primary Goal | Demonstrate conformity to defined requirements | Reduce real-world risk from threats and failures |
| Main Driver | Regulation, contract, audit scope, customer assurance | Threat modeling, risk appetite, business impact |
| Evidence Needed | Policies, control proofs, logs, tickets, audit artifacts | Telemetry, test results, incident learnings, attack-path validation |
| Success Measure | Audit readiness and deficiency closure | Measurable resilience and risk reduction over time |
| Failure Mode | Paper controls and weak operation | Strong engineering without governance or proof |
| Operational Focus | Ownership, evidence retention, repeatability | Prevention, detection, response, and hardening |
Mature organizations align both: compliance establishes governance and evidence discipline; security engineering and validation ensure the controls actually reduce risk. This is consistent with risk-management framing in NIST CSF 2.0 and with control catalogs that expect evidence of operation and assessment.
Under the AWS shared responsibility model, the provider secures the cloud infrastructure, while the customer remains responsible for tenant-side configuration, identity, data protection, and evidence generation.
| Service Model | Provider Responsibility | Customer Responsibility | Shared Areas |
|---|---|---|---|
| IaaS | Facilities, physical hosts, virtualization layer, core service operation | OS hardening, IAM/PAM, network policy, logging config, data protection | IR coordination, responsibility handoffs |
| PaaS | Managed runtime, platform patching, service availability controls | Identity, data classification, access policy, service config, monitoring | Key boundaries, shared telemetry |
| SaaS | Application stack operation and platform security controls | User lifecycle, admin roles, tenant config, data governance | Audit reporting, incident communications |
Organizations most often misread the boundary in identity, logging retention, key governance, and third-party integrations that introduce new admin pathways or data flows. In practice, most audit gaps appear not because the provider failed its platform controls, but because the customer could not demonstrate consistent tenant-side operation, ownership, and evidence across those shared areas.
The practical challenge is not framework enumeration; it is reconciling overlapping requirements into one defensible cloud control model with clear evidence outputs.
Cloud compliance succeeds when requirements are mapped to implementable domains with clear owners and reproducible evidence.
| Control Domain | Why It Matters | Common Evidence | Common Failure Pattern |
|---|---|---|---|
| IAM and privileged access | Identity governs the control plane | MFA/JIT/PAM configs, role catalogs, access reviews, audit logs | Excess privilege, unmanaged service accounts |
| Configuration governance | Prevents drift; enforces baselines | Policy-as-code repos, compliance dashboards, remediation tickets | Advisory-only policies, exceptions without expiry |
| Logging and monitoring | Auditability depends on logs | Audit logs, SIEM ingestion proof, retention configs | Logging disabled, short retention, blind spots |
| Data protection and keys | Limits exposure impact | KMS policies, rotation records, encryption enforcement evidence | Shared key admin, weak key policies |
| Vulnerability governance | Standards expect vuln management | Scan cadence, patch SLAs, backlog evidence, test reports | Unscoped scanning, unclear patch ownership |
| Resilience and recovery | Restoration is frequently required | Backup configs, restore tests, DR runbooks | Backups untested, retention mismatched |
| Third-party risk | Cloud is a supply chain | Vendor reviews, assurance reports, DPAs/BAAs | Provider reports treated as sufficient |
Across audits, these domains tend to fail for the same reason: control ownership is diffuse, enforcement is inconsistent, and the evidence generated by cloud operations is incomplete or not readily reproducible.
Governance and ownership
Asset and account inventory
IAM and privileged access
Encryption strategy
Logging and monitoring
Policy enforcement
Third-party controls
Backup and resilience
Incident response and audit readiness
Excessive access. Broad roles are often granted during delivery pressure, incident response, or early platform build-out, but formal deprovisioning and periodic access review lag behind. Audit consequence: weak least privilege and segregation of duties. Security consequence: a single compromised identity can expand into control-plane abuse across multiple services.
Missing or short-retained administrative logs. Teams frequently rely on provider defaults without aligning retention, export, and integrity requirements to audit or investigation needs. Audit consequence: inability to evidence change history or privileged actions over the required period. Security consequence: weak investigations, poor incident defensibility, and loss of forensic visibility.
Unenforced baselines and uncontrolled drift. Policies may exist in documentation or advisory dashboards, but they are not consistently enforced through blocking controls, automated remediation, or exception workflows. Audit consequence: inconsistent control operation across environments. Security consequence: long-lived misconfigurations remain exploitable.
Storage exposure from misconfiguration. Public access settings, inherited permissions, replication paths, or weak bucket and container policies are often introduced through speed, template reuse, or poor review discipline. Audit consequence: failures in data protection, access governance, and scope control. Security consequence: direct data exposure, unauthorized access, or exfiltration.
Weak key governance. Organizations often enable encryption but fail to separate key administration from workload administration, monitor policy changes, or define when customer-managed keys are required. Audit consequence: inability to demonstrate encryption governance and controlled key lifecycle management. Security consequence: unauthorized decryption paths, unsafe key policy changes, or weakened separation of duties.
Shadow cloud and unmanaged projects. New accounts, subscriptions, projects, and third-party integrations are created outside approved landing zones, tagging requirements, or governance workflows. Audit consequence: incomplete scope control and inaccurate asset inventory. Security consequence: unknown attack surface, unmanaged privilege, and unmonitored data movement.
Evidence that is not attributable or reproducible. Screenshots, ad hoc exports, and manually assembled artifacts often lack timestamps, ownership context, or a repeatable collection method. Audit consequence: sampling failures and weak audit defensibility. Security consequence: control decay cannot be measured reliably, and management cannot prove that a control operated consistently over time.
Continuous compliance moves from periodic audit preparation to continuous control operation, proof, and continuous security validation, using cloud APIs and continuous monitoring.
Establish the program baseline: a unified control catalog, clear ownership, and defined evidence requirements per control. Then enforce baselines through policy as code, CSPM tooling, and configuration governance (evaluate posture, detect drift, and remediate). Azure Policy is designed to enforce organizational standards and assess compliance at scale; AWS Config can evaluate resources against rules and flag noncompliance.
Automate evidence capture for high-friction artifacts such as privileged access records, audit log retention settings, encryption/key governance proofs, and baseline policy results, and store them in a controlled evidence repository. Cloud provider compliance portals can support provider-side evidence acquisition (e.g., provider audit reports), but customer-side evidence must be generated from your tenant configuration and operations.
Institutionalize exceptions with risk acceptance, compensating controls, and expiry. Finally, validate beyond automation: continuous compliance reduces audit friction, but periodic expert review, cloud penetration testing, and tabletop exercises remain necessary to confirm controls hold under realistic conditions.
A mature program also defines measurable signals for control health, such as privileged review completion, log export coverage, remediation time for policy drift, backup test success rates, and exception aging.
Multi-cloud complicates compliance because identity services, policy engines, and log systems differ, and retention defaults are not uniform. For example, AWS CloudTrail event history is time-limited unless you create trails; Azure Activity Logs require export for long-term storage; Google Cloud Logging uses default buckets with defined retention periods.
Hybrid architectures add integration boundaries (identity federation, network connectivity, CI/CD and secrets distribution) that must be included in scope, ownership, and monitoring.
The governance objective is not to force identical tooling across AWS, Azure, and GCP. It is to standardize control intent, ownership, evidence schema, and exception handling while allowing provider-specific implementations underneath. In practice, that means one common control taxonomy, one responsibility model, and one evidence model even when the technical enforcement path differs by platform.
A workable pattern is to centralize identity strategy, logging retention requirements, tagging standards, and control reporting, then map each provider's native services to those common requirements. This lets the organization normalize evidence and reporting without pretending that Entra ID, AWS IAM, Google Cloud IAM, CloudTrail, Activity Logs, and Cloud Logging behave the same way.
For risk committees, cloud compliance improves defensibility by tying risk statements to observable control conditions: who has privilege, what administrative actions are logged, what policy drift exists, how quickly issues are remediated, and whether exceptions are time-bound and approved. This converts cloud assurance from abstract statements into evidence-backed governance.
For procurement teams, cloud compliance is not satisfied by a provider badge or a generic attestation summary. The practical questions are whether the vendor can define shared responsibility boundaries clearly, provide scoped assurance artifacts, explain tenant-side configuration responsibilities, disclose subprocessors and data locations, and commit contractually to incident notification, logging support, and evidence availability.
For security leadership, cloud compliance helps prioritize investments that reduce both audit exposure and operational risk: centralized IAM and PAM, defensible logging and retention, encryption governance, policy enforcement, vendor oversight, and repeatable evidence collection. These are not separate audit tasks; they are durable control investments.
For engineering leadership, compliance affects platform design decisions: landing zones, identity federation, secrets handling, CI/CD guardrails, backup protection, and the separation of regulated workloads. Good compliance architecture reduces both rework and audit friction because controls are embedded into the operating model rather than retrofitted later.
For audit stakeholders, the central question is not whether a control was described; it is whether it operated consistently, under clear ownership, for the required period, with evidence that is attributable and reproducible. That is why cloud compliance has direct implications for vendor selection, contract language, incident defensibility, and long-term enterprise penetration testing pricing.
Least privilege and privileged access governance: time-bound elevation, standardized privileged roles, routine access reviews, and monitoring of privileged actions.
Centralized logging with defensible retention: enable control-plane logs everywhere, export beyond default retention, and monitor ingestion health as a control.
Encryption governance: define when customer-managed keys are required, separate key administrators from workload admins, and review key policy changes.
Policy-as-code guardrails with drift closure: enforce high-risk baselines (public storage, disabled logging, weak encryption) and measure remediation time; keep exceptions time-bound.
Landing zones and scope isolation: standardize account/project structure, networking, identity, and logging; isolate regulated scope into separate environments with stricter controls.
Evidence automation and reproducibility: prefer API exports and configuration proofs over screenshots; store evidence with versioning and access control.
For UK organizations validating cloud compliance controls, continuous validation and reporting should combine scanning, periodic penetration testing, tabletop exercises, and measurable evidence that controls operate as intended. (policy compliance rates, drift remediation time, privileged review completion, logging coverage).
Taken together, these practices reduce audit risk because they improve consistency and traceability, and they reduce security risk because they narrow privilege, increase visibility, and shorten the lifespan of misconfigurations.
Cloud security compliance is meeting applicable security requirements in cloud environments through implemented controls, governance processes, and verifiable evidence.
Because cloud is identity-driven and changes rapidly; without enforced controls and retained evidence, organizations fail audits and cannot defend incidents.
Common sources include CSF, SP 800-53, SP 800-171 (when handling CUI), ISO/IEC 27001, ISO/IEC 27017, CSA CCM, CIS Benchmarks, SOC 2 Trust Services Criteria, PCI DSS, and applicable laws such as GDPR or sector rules.
No. Compliance proves adherence to defined requirements; security reduces real-world risk. They overlap but are not substitutes.
Responsibility is shared. Providers operate controls for underlying infrastructure and services; customers own tenant configuration, identity, data governance, and the evidence needed to demonstrate control operation.
They enforce baselines through code, monitor for drift, automate evidence capture, manage time-bound exceptions, and validate controls through testing and reviews.
Continuous compliance is maintaining and proving control operation continuously, using automated evaluation and evidence collection, rather than preparing only for periodic audits.
Control objectives are similar, but implementations differ: each provider has distinct identity services, logging systems, policy enforcement mechanisms, and retention defaults.
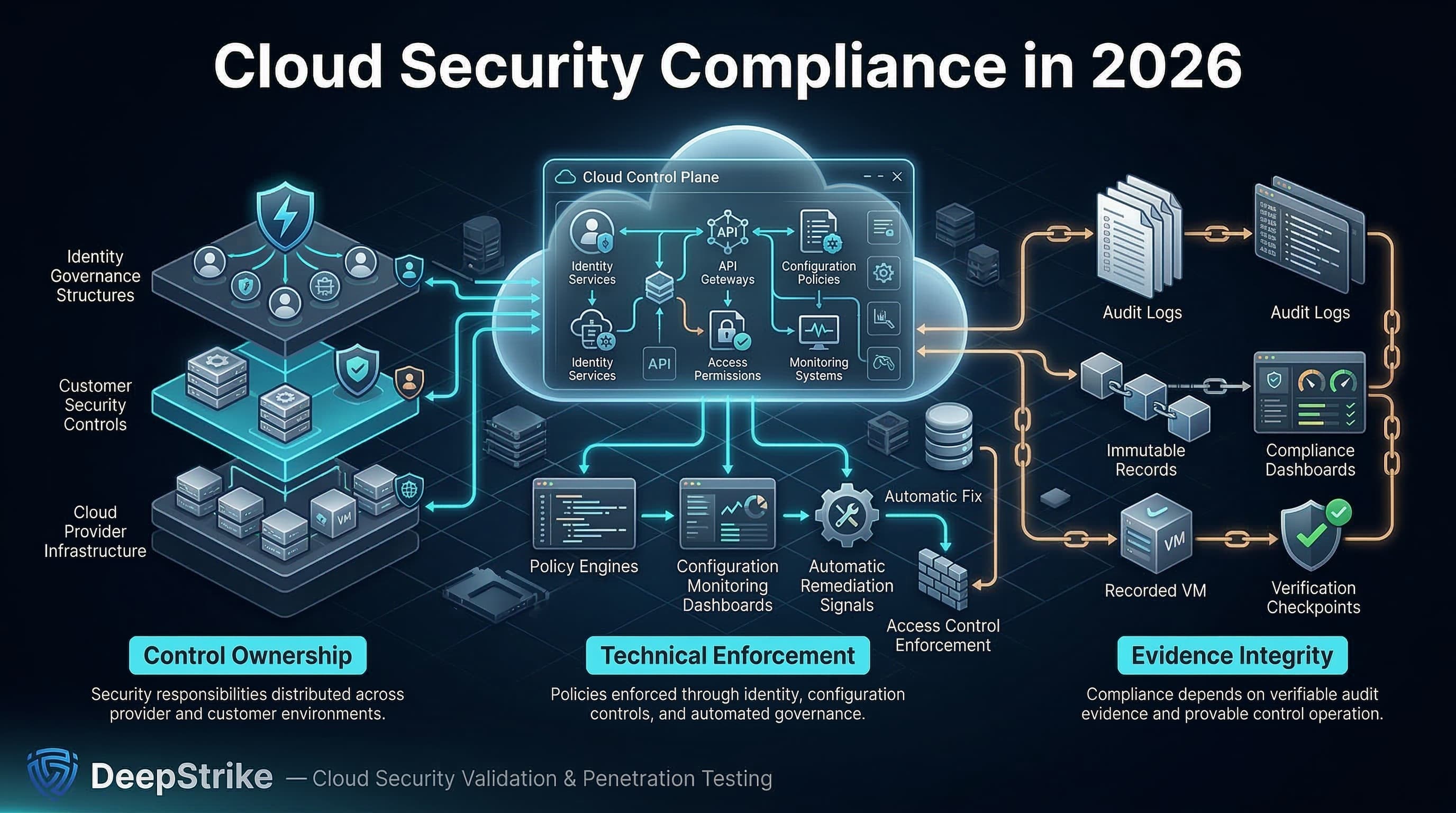
Cloud security compliance in 2026 is about control ownership, technical enforcement, and evidence integrity. Requirement sources vary (laws, standards, contracts), but cloud reality is consistent: identity governs the control plane, configuration drifts quickly, and audit outcomes depend on what you can prove.
Mature organizations treat cloud security compliance as a continuous program: baseline controls are enforced through code, drift is detected and remediated, evidence is automated and retained, and controls are validated through testing.
The organizations that perform best are those that translate requirements into enforced cloud controls, clear ownership, and evidence that can withstand both audit scrutiny and post-incident review.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us