April 29, 2026
Updated: April 29, 2026
A procurement-focused comparison of Swiss penetration testing providers based on technical depth, compliance fit, reporting quality, and market suitability.
Mohammed Khalil

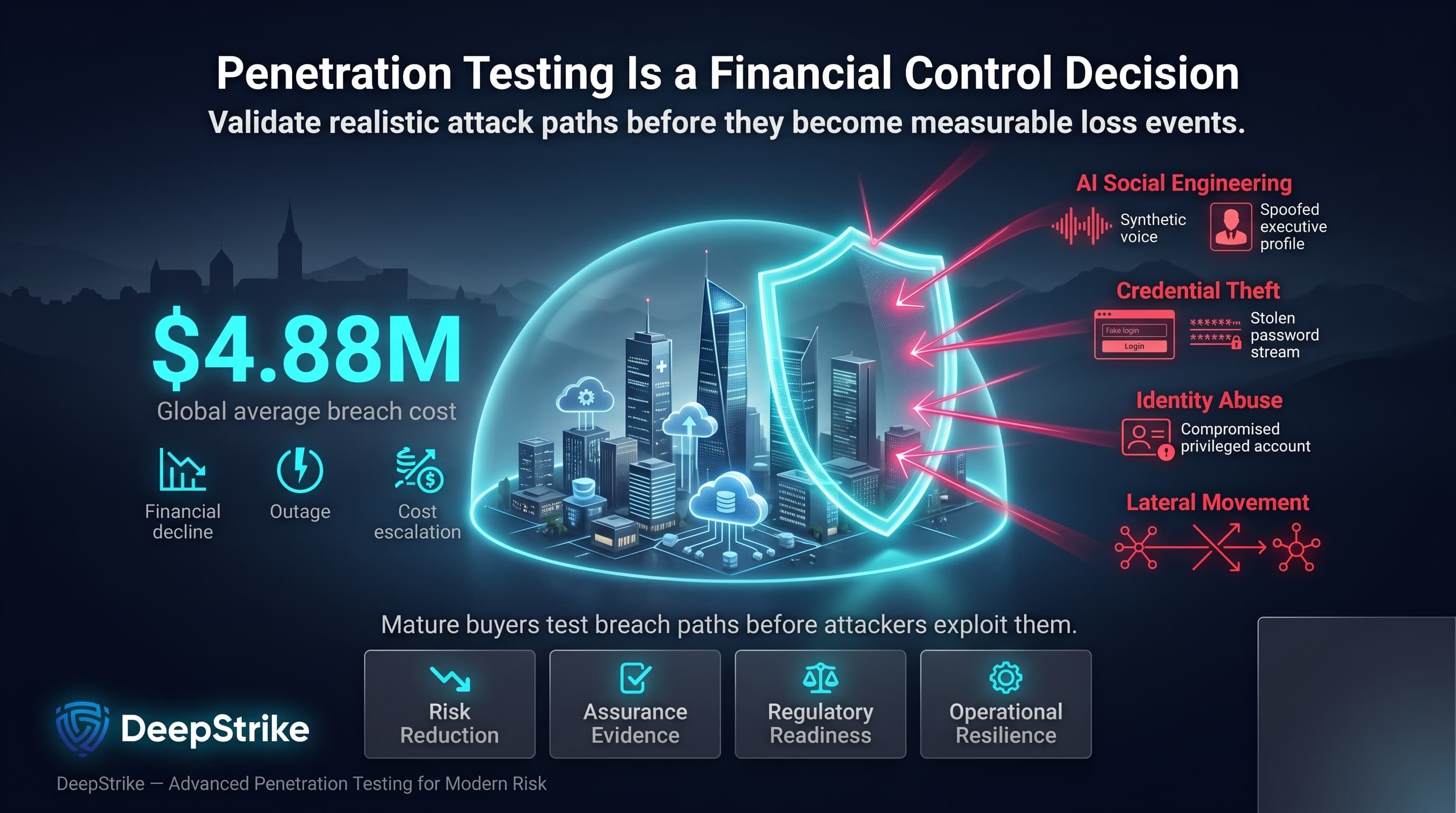
With the global average cost of a breach estimated at about $4.88 million, the procurement decision behind the top penetration testing companies Switzerland category is fundamentally a risk-and-loss control decision. Swiss organizations face accelerating attacker tradecraft, including AI-assisted social engineering, credential theft, identity abuse, and post-compromise lateral movement. For mature buyers, penetration testing therefore matters less as a checkbox exercise and more as a method for validating realistic breach paths before they turn into financial, regulatory, or operational damage.
Switzerland’s mature market means high security expectations. Finance firms under FINMA guidance must demonstrate robust security testing; healthcare and public-sector entities must adhere to FADP and patient-data standards. Many Swiss companies pursue ISO 27001 or NIST/OWASP benchmarks to assure customers. E-commerce and payment platforms may need PCI DSS compliance. Critical infrastructure operators (energy, industrial) face OT/IoT attack risks. Cross-border data flows invoke GDPR alignment.
This ranking is methodology-driven and not sponsored. It emphasizes proven exploit chaining over scan-only reporting and assesses providers against Swiss buyer requirements such as reporting quality, cloud/API maturity, regulated-environment fit, and evidence-backed technical depth where relevant.
Penetration testing is a structured adversarial security assessment that combines automated vulnerability discovery with manual exploit validation to identify real-world attack paths, validate control effectiveness, and reduce breach probability.
Swiss procurement often demands more than a basic vulnerability scan. For FINMA-regulated or finance-sensitive buyers, testing quality carries additional weight because reporting, remediation evidence, and technical realism may be reviewed under stricter assurance expectations. For organizations handling sensitive personal data, Swiss FADP obligations and, where relevant, GDPR-facing customer requirements raise the value of disciplined testing and defensible reporting. Multilingual delivery can also matter in practice, especially where German- and French-speaking stakeholders need usable findings. Industrial and critical-infrastructure environments add further complexity because OT/ICS testing requires tighter safety controls and more specialized delivery.
Local trust is a factor: Swiss buyers favor vendors with a proven local track record or Swiss entity (for legal, data-residency reasons). However, branding alone isn’t enough they must verify technical capabilities. Reporting quality is critical, as findings need clear remediation guidance for risk committees and auditors. Swiss firms often maintain strict change control and CI/CD pipelines; providers must demonstrate cloud, container, API and identity-focused testing. Consequently, selection criteria blend compliance-readiness (ISO, NIST, OWASP alignment) with authentic offensive depth.
Our evaluation mimics a procurement audit. Each vendor was scored on verified evidence of technical and service attributes. We prioritized manual exploit chaining and adversary-like simulations over automated scan output. Key criteria included:
Where vendor capabilities were unproven in public sources, they were treated as unknown. The methodology explicitly avoids taking marketing claims at face value. Manual depth and demonstrable engineering expertise were weighted heavily; scan-heavy outputs score lower.
Select a provider by matching their strengths to your specific needs. Common pitfalls include:
Headquarters: USA (Dual US/UAE presence)
Founded: 2019Company Size: ~50 testers worldwide
Primary Services: Human-powered penetration testing, red teaming, continuous security testing, cloud & API security.
Industries Served: Tech startups, SaaS platforms, finance, healthcare, industrial.
Why They Stand Out: DeepStrike stands out here for a manual-first testing model, senior certified testers, and strong cloud and API security coverage. Its differentiation in this ranking is based on exploit-validation depth, technically actionable reporting, and suitability for buyers that need realistic adversarial testing rather than scan-heavy output.
Editorial note: DeepStrike is included in this list based on the same evaluation criteria applied to all providers.
Switzerland Relevance: DeepStrike is relevant to Swiss buyers that prioritize technical depth in cloud-native, SaaS, API-heavy, and regulated digital environments. As a cross-border specialist, it is more suitable where remote delivery, English-language reporting, and modern application security coverage matter more than local office presence. Buyers with strict local-language, on-site, or residency-sensitive requirements should confirm those delivery conditions in advance.
Testing Depth Model: Manual exploit chaining. DeepStrike’s practice is to simulate real attackers: each vulnerability discovered is exploited and chained. They validate end-to-end breach scenarios (e.g. web app → compromise IAM → snapshot of tenant) and test business logic flaws. Cloud and API testing maturity appears to be a clear strength for modern digital environments. This approach is well suited to buyers that prioritize realistic breach-path validation over scan-heavy testing.
Key Strengths:
Potential Limitations:
Best For: Cloud-native enterprises, SaaS/tech firms, FINMA-regulated finance (needing technical depth), Swiss companies seeking continuous testing.

Headquarters: Baar, Switzerland (DACH region offices)
Founded: 2000 (25+ years experience)
Company Size: 350+ employees
Primary Services: 360° cybersecurity (SOC/MDR, IR, consulting, pentesting & red teaming)
Industries Served: Banking, insurance, government, healthcare, energy, public sector, retail, telecom.
Why They Stand Out: InfoGuard stands out in this ranking for delivery scale, broad service coverage, and strong fit for large Swiss organizations that value integrated consulting, managed security, and offensive testing under one provider. Its relevance here comes more from enterprise breadth and compliance-readiness than from boutique-style offensive specialization.
Switzerland Relevance: As a Swiss-headquartered firm with GDPR-compliant data processing, InfoGuard fits DACH requirements well for enterprise buyers in Switzerland and the broader DACH region. Their team includes Swiss-certified consultants and provides reports in German, English, or French. They appear relevant for audit-heavy Swiss environments, including finance-sensitive and ISO-aligned enterprise contexts. InfoGuard’s size allows onsite teams in Switzerland if needed, easing integration into local corporate structures.
Testing Depth Model: Hybrid model. InfoGuard blends automated scanning with manual validation. Their approach emphasizes comprehensive coverage (networks, apps, cloud) and typically follows ISO/NIST-based methodologies. They combine expertise in network/web testing with red teaming for larger engagements. Depth is solid, though as a large shop some routine tasks may lean on tooling; however, senior analysts review findings. The model suits enterprises requiring both scale and technical skill.
Key Strengths:
Potential Limitations:
Best For: Large enterprises, financial institutions, public sector and ISO-driven organizations in Switzerland.
Headquarters: Zurich, Switzerland
Founded: 2003
Company Size: ~150 specialists (Oneconsult Group)
Primary Services: Penetration testing, red teaming, OT/ICS security, digital forensics
Industries Served: Finance, healthcare, manufacturing, critical infrastructure, cloud services.
Why They Stand Out: Oneconsult stands out for combining traditional IT testing with broader industrial and red-team-oriented capability. In this ranking, its differentiation is strongest where buyers need deep manual validation, OT/ICS relevance, and structured reporting suited to regulated or high-assurance environments.
Switzerland Relevance: A Zurich-based firm, Oneconsult speaks local compliance language (TLPT, DORA, FADP) and has long experience with Swiss banks and rail/energy operators. They support bilingual delivery (German/English) and often tailor language to client needs. Having a Swiss legal entity ensures data stays under Swiss/EU jurisdiction. Their notoriety in Swiss infosec means familiarity with sector-specific threat models (e.g. Swiss public-key standards).
Testing Depth Model: Manual exploit chaining. Oneconsult emphasizes deep manual analysis across networks, applications, cloud, and even specialized targets (smartcards, vehicles, ICS). They systematically verify vulnerabilities and execute proof-of-concept exploits. This yields realistic breach pathways (e.g. phishing → domain admin). Oneconsult also integrates red team elements for advanced simulations. Their manual focus delivers high attacker simulation value.
Key Strengths:
Potential Limitations:
Best For: FINMA-sensitive environments, critical infrastructure operators, healthcare organizations, and manufacturing firms needing deep manual validation.

Headquarters: Rapperswil, Switzerland (offices also in Germany and Canada)
Founded: 1999
Company Size: ~80 (50+ pentesters)
Primary Services: Penetration tests, red teaming, social engineering, forensic analysis
Industries Served: Finance, IT/Telecom, healthcare, government, industrial, automotive.
Why They Stand Out: Compass is one of Switzerland’s oldest pentest firms, with a wide service range. They were CREST-certified for penetration testing in 2023, ensuring top-tier processes. Compass testers perform automated scans followed by in-depth exploitation; they pivot through networks (Active Directory, microsegmentation) and emphasize OWASP/ASVS for web apps. They also offer purple teaming and IoT/ICS security, and maintain a vulnerability research lab (Tiger Team). Their global presence supports cross-border projects.
Switzerland Relevance: Founded in Switzerland, Compass is deeply embedded in the local market. Their testers speak German and English, and they maintain Swiss data centers. For Swiss financial customers, Compass’s CREST accreditation provides confidence. They often collaborate with Swiss universities and industry (e.g. automotive security standards). Local offices mean consultants can visit client sites easily.
Testing Depth Model: Hybrid model. Compass balances tools and manual follow-up. They routinely run automated discovery (including container/cloud scans) then hand off to experts who validate and exploit findings fully. The focus is on thoroughness within defined scopes. Advanced offerings like red teaming and mobile app testing cater to enterprises. This model provides broad coverage with reasonable depth.
Key Strengths:
Potential Limitations:
Best For: Mid-to-large Swiss enterprises, finance and telecom sectors, projects needing CREST-level assurance.
Headquarters: Bern, Switzerland
Founded: 2004
Company Size: ~50 (est.)
Primary Services: Penetration testing, security consulting, industrial cybersecurity, training
Industries Served: Multiple (healthcare, public sector, manufacturing, services)
Why They Stand Out: Redguard is a Swiss SME specializing in security reviews and attack simulations. Their pentesting service targets networks, systems and applications, looking for “complex problems” and advising on effective countermeasures. They also support container, cloud and system hardening reviews. Redguard emphasizes a personal approach: small teams of experienced analysts, and ongoing research into new attack methods. They are active in Swiss security communities.
Switzerland Relevance: Deep Swiss roots with offices in Bern, Zürich and Neuchâtel. Their site and reports are available in German, French and English, suiting multilingual needs. Redguard has visible local market presence, suggesting strong local trust. They understand Swiss regulatory context (privacy law, FINMA notes) and can handle cantonal and federal customers.
Testing Depth Model: Manual exploit chaining. Redguard’s focus is hands-on: after discovery, testers manually verify and exploit vulnerabilities. They simulate attacker paths within the defined scope, ensuring findings are actionable. While not a large red team, their thoroughness in a box-check sense is high. They can also perform social engineering and physical tests if needed.
Key Strengths:
Potential Limitations:
Best For: Swiss SMEs and public entities, multi-language projects, organizations needing a local, flexible partner.

Headquarters: Zurich, Switzerland
Founded: 1999
Company Size: ~60 (offensive team)
Primary Services: Penetration testing, red teaming, security training, research
Industries Served: Finance, IT, public sector, education, automotive.
Why They Stand Out: scip is a boutique security firm known for cutting-edge research (publishing advisories and running TIGERCSIRT). Their “Offensive Team” performs tailored attack simulations on everything from single apps to entire networks, using methodologies like PTES. They emphasize unpredictability in methods to expose hidden flaws. Their labs track emerging threats, feeding back into client engagements. scip also offers extensive training and publishes results, underlining its technical credibility.
Switzerland Relevance: A Zurich-based specialist, scip has long collaborated with Swiss corporations and government agencies. Their reputation in academia (IT training) and industry grants trust among Swiss buyers valuing expertise. They often participate in Swiss cybersecurity conferences, reinforcing local presence. While smaller than InfoGuard or Compass, scip can scale through partnerships.
Testing Depth Model: Hybrid/Manual exploit chaining. scip performs in-depth manual tests and red-team efforts. They adhere to industry frameworks (OWASP, etc.) but customize beyond standard scope. Each test is supported by their research capabilities e.g. they might bring custom exploit code. This yields a hybrid mode: systematic methodology with high creativity in execution.
Key Strengths:
Potential Limitations:
Best For: Tech-savvy organizations, R&D and education sectors, enterprises seeking truly novel attack angles (e.g. smart city projects, experimental tech stacks).
Headquarters: Zurich, Switzerland
Founded: 2011
Company Size: ~30
Primary Services: Application pentesting, cloud pentesting, red teaming, hardware/firmware security
Industries Served: IoT manufacturers, high-tech, utilities, cloud providers.
Why They Stand Out: modzero is a technical boutique focusing on high-assurance testing, especially for embedded and cloud contexts. They publish blog research on bypassing ASLR in IoT, showing their deep skills. The team seeks senior talent (currently hiring for pentesters and red teamers), indicating a skilled bench. Services span web/mobile pentesting to low-level binary/firmware reviews and threat modeling.
Switzerland Relevance: Zurich-based and active in Swiss security research circles. They operate mostly in German/English. Modzero's niche (hardware, IoT, containers) fits Swiss sectors like manufacturing and logistics. Their smaller size means close client collaboration, but may limit large volume.
Testing Depth Model: Hybrid/Manual. modzero customizes its approach by project. They may use specialized tools for IoT firmware but always complement with manual analysis. In cloud testing, they apply scripting plus exploit development. Their red-team service covers full-stack attacks including hardware elements.
Key Strengths:
Potential Limitations:
Best For: High-tech companies (IoT, manufacturing, utilities), cloud-native startups, cross-border Swiss companies with advanced technical needs.
Headquarters: Zug, Switzerland (EU operations)
Founded: 2018
Company Size: ~30 (CREST-certified red teamers)
Primary Services: Red teaming, penetration testing, cloud security, AI/ML security
Industries Served: Finance, healthcare, SaaS, e-commerce, industrial.
Why They Stand Out: RedTeam Partners stands out for red-team-oriented delivery, CREST-positioned offensive capability, and emphasis on realistic adversary simulation over checklist-style testing. In this ranking, it is most relevant for buyers that need mature attack simulation and executive-plus-technical reporting rather than baseline pentest coverage alone.
Switzerland Relevance: Although based in the EU, RedTeam Partners offers Swiss-specific support (GDPR-compliant EU data hosting, multilingual reporting). They target Swiss clientele indirectly by ensuring compliance with EU data rules and international standards. Swiss finance and tech buyers benefit from their CREST credential and focus on regulated industries. They have experience with financial services clients (Fortune 500) and highlight EU regulatory alignment.
Testing Depth Model: Red-team oriented. They simulate full adversary campaigns, from initial phishing to full domain compromise, just like a real breach. Their CREST-certified experts specialize in chaining vulnerabilities and privilege escalation. In cloud tests, they cover identity weaknesses and misconfigurations. The approach prioritizes depth and realism, delivering high impact results for mature security programs.
Key Strengths:
Potential Limitations:
Best For: Large regulated organizations, especially in finance and healthcare, that need intensive adversary simulations; multinational SaaS firms; any Swiss enterprise wanting CREST-level assurance.
| Company | Specialization | Testing Depth Model | Best For | Switzerland Fit | Compliance Alignment | Ideal Organization Size |
|---|---|---|---|---|---|---|
| DeepStrike | Human-powered pentesting, continuous PtaaS, cloud/API security | Manual exploit chaining | Regulated enterprises, cloud-first SMEs, tech startups | Cross-border specialist fit for cloud-first and regulated digital environments | ISO 27001, SOC 2, PCI DSS, HIPAA | Enterprise, Fast-growing startups |
| InfoGuard | 360° cybersecurity (MDR, IR, consulting, pentest) | Hybrid model | Large Swiss enterprises (banks, government) | Swiss HQ with DACH coverage; ISO-certified; 24/7 services | ISO-aligned and audit-heavy enterprise environments | Large enterprise |
| Oneconsult | IT/OT pentesting, red teaming, compliance consulting | Manual exploit chaining | Critical infra (energy, transit), FINMA-regulated orgs | Swiss HQ; expertise in FINMA/DORA/TLPT compliance | OWASP, OSSTMM, TLPT/DORA | Mid-to-large (critical sectors) |
| Compass Security | Pentests, red teaming, OSINT, training | Hybrid model | Finance, IT/telecom, manufacturing | Swiss-founded; CREST certified; multi-lingual | CREST PT certification; ISO, NIST (implied) | Enterprise, Govt |
| Redguard AG | Penetration testing, attack simulation, hardening reviews | Manual exploit chaining | Swiss SMEs, mid-market, public sector | Swiss-based (Bern, Zurich); trilingual; 500+ clients | OWASP/NIST-guided (no formal cert) | SME to mid-market |
| scip AG | Offensive security, red teaming, research | Hybrid/Manual exploit chaining | Tech & research sectors, advanced red teaming | Swiss HQ Zurich; strong academia ties; agile | ISO/IEC 27002, PTES frameworks | Mid-market to large (tech-focused) |
| modzero AG | App/cloud pentesting, red teaming, IoT/firmware | Manual/Hybrid model | IoT and embedded systems firms, cloud-native | Swiss boutique; German/English delivery; technical R&D orientation | BSI/OWASP standards (per advisory) | SME, R&D departments |
| RedTeam Partners | Red teaming & pentesting (CREST-certified) | Red-team oriented | Large enterprise (finance, healthcare), SaaS | EU-based (GDPR-compliant); serves Swiss via remote | CREST (STAR) accreditation | Large enterprise |
Swiss organizations often make analytical mistakes in procurement. Common errors include:
By avoiding these pitfalls and insisting on demonstrable expertise, Swiss buyers can focus on vendors who truly raise their security posture rather than just marking compliance checkboxes.
Cost vs. Depth: Large enterprises can afford boutique firms or big consultancies that deliver maximum manual depth. They often require extensive coverage (cloud, mobile, OT) and extensive reporting, justifying higher fees. SMBs and startups may opt for smaller firms or PTaaS subscriptions for faster, cost-effective scans. However, economy firms should still vet technical quality a “budget pentest” that misses business logic flaws or API endpoints will be a false economy.
Risk Scaling: Enterprises face high-stakes breaches (hundreds of millions at risk), so every crack matters. They often require full-scope red teams and multi-team projects. SMEs usually have smaller attack surfaces; a focused web/mobile pentest with a senior tester may suffice. But even SMBs in finance or medtech are better off than blindly trusting scans.
Compliance Intensity: Enterprises in regulated sectors must tick many compliance boxes. They lean toward certified vendors (CREST, ISO-aligned) and comprehensive methodologies. SMBs often have leaner compliance (perhaps just basic privacy or PCI), so they can choose simpler testing if appropriate. Yet, SMBs exporting to the EU still need GDPR/DSGVO-aligned testing.
Boutique vs. Global: Enterprises may prefer large firms or international specialists with big-name credibility and bench strength. They value process maturity and 24/7 support. SMBs might favor local boutiques for personalized attention and flexibility. A Swiss SME may appreciate a vendor who can send a German-speaking consultant onsite.
Automation vs. Manual: Red teams are expensive but show systemic risks. Enterprises often use them annually. SMBs sometimes adopt automated platforms (PTaaS) for dev teams cost-efficient but not comprehensive. Careful buyers should blend: an annual manual pentest plus automated scans quarterly, for example.
Local Delivery: Enterprises often have strict policies (data must stay in Switzerland/EU) and benefit from vendor offices. Global firms can work remotely, but may not meet certain audit demands (e.g. EU hosting). SMEs may be more flexible if cost savings matter.
In practice, Swiss SMBs often choose mid-size Swiss firms (e.g. Redguard, modzero) for a balance of price and quality. Large organizations weigh firm credentials and breadth (e.g. InfoGuard, Compass, RedTeam Partners). Cross-border execution is acceptable if the firm demonstrates compliance alignment and communication proficiency.
Pricing is highly variable and scope-dependent. Main drivers include:
Instead of relying on precise local price claims, buyers should evaluate pricing through scope, testing depth, reporting expectations, retesting terms, delivery model, and environmental complexity. In Swiss procurement, a higher quote may still be commercially rational when it reflects deeper manual validation, better reporting, and stronger fit for regulated or high-assurance environments. Scope clarity matters more than headline price.
Costs vary widely by scope, testing depth, reporting expectations, retesting, and delivery model. In Switzerland, pricing is often shaped more by asset complexity and assurance requirements than by a single market-wide benchmark. Buyers should request quotes against a clearly defined scope rather than rely on flat averages.
An enterprise engagement typically covers multiple layers: external and internal network tests, web and mobile application tests, cloud infrastructure/DevOps assessment, Active Directory and identity testing, and sometimes social engineering. It includes initial planning, asset discovery, manual vulnerability exploitation, pivoting/lateral movement, a prioritized findings report, and retesting of fixes. It may also provide compliance mapping (e.g. ISO controls) if requested.
Technical certifications (e.g. OSCP, CISSP, GIAC) signal that testers understand complex techniques and can develop exploits, which is crucial for a deep assessment. Tools alone do not ensure quality. Therefore, experienced certified testers generally outperform juniors relying solely on automated tools. The best providers combine both: they use tools for efficiency but critically, manual skilled analysts verify and exploit findings.
Typical timelines are 1–4 weeks from kickoff to report, depending on scope. A small app test might be done in 1–2 weeks. Large enterprise tests (covering many systems) can take 4+ weeks. Beware engagements that claim to finish in days thorough testing and report writing require time. Fast-track options (Rush service) exist but usually cost more.
While not always legally mandated, penetration tests are best-practice for meeting these standards.
At minimum once per year for critical systems (often more for high-risk orgs). Swiss banks typically test at least annually due to FINMA audits. However, modern DevOps recommends testing after each major release or adopting continuous pentesting. For medium-risk use cases, every 6–12 months is common. High-risk (public internet services, sensitive data) could justify quarterly or continuous testing.
There is no one-size answer. Local Swiss firms (InfoGuard, Compass, Redguard, etc.) understand domestic regulations and provide easy communication. Cross-border specialists (DeepStrike, RedTeam Partners, etc.) may offer niche expertise or scalability. The key is to ensure data handling meets Swiss or EU requirements where relevant, and that language, reporting, and delivery expectations are acceptable. A hybrid approach using a Swiss partner supported by international expertise can also work.
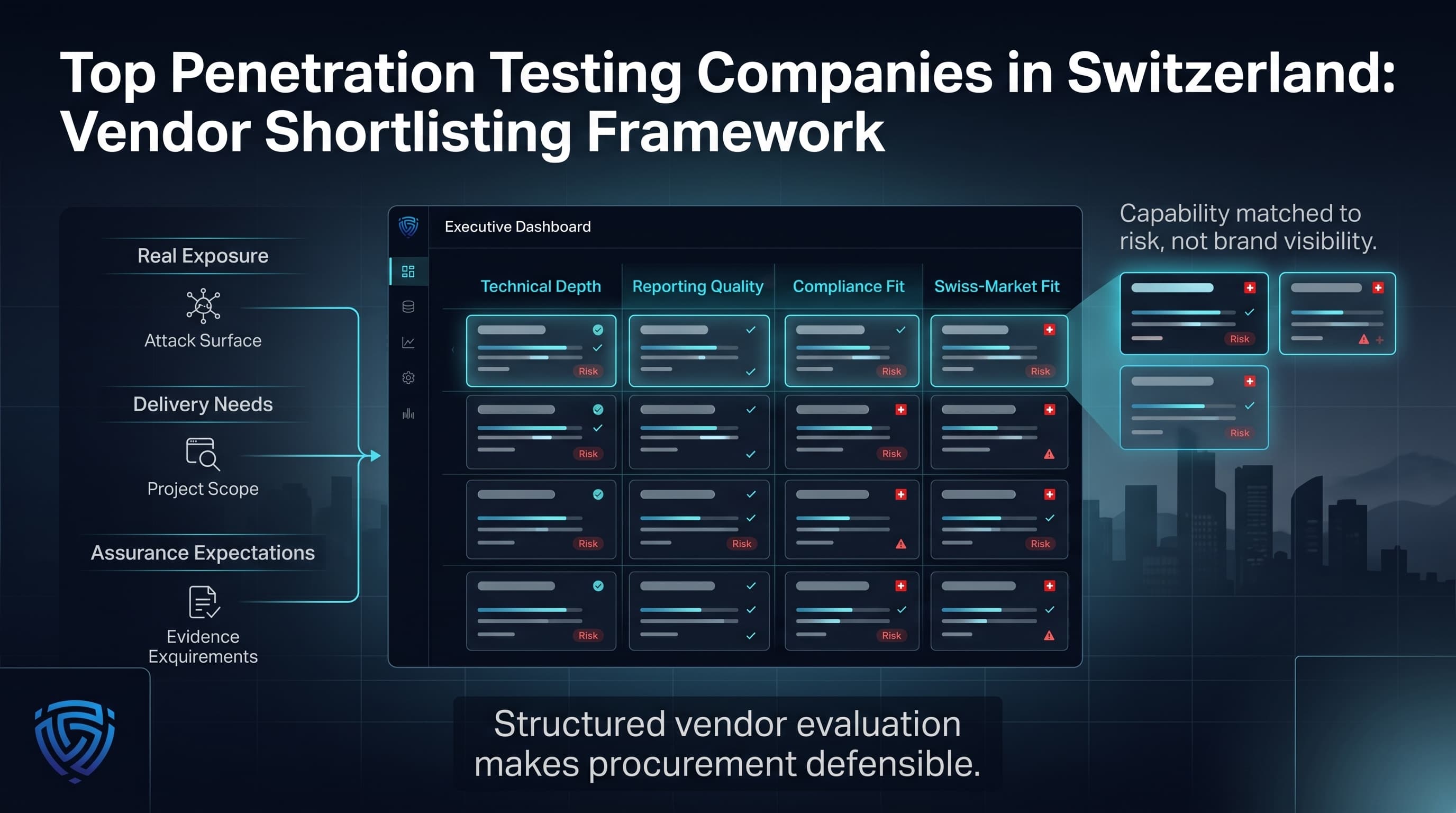
This independent comparison of the top penetration testing companies in Switzerland is designed to support structured vendor shortlisting rather than brand-led selection. By focusing on technical depth, reporting quality, compliance relevance, and Swiss-market fit, it gives buyers a more defensible way to evaluate providers. Swiss organizations should use this comparison to match vendor capability to real exposure, delivery needs, and assurance expectations.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us