April 28, 2026
Updated: April 29, 2026
A procurement-focused comparison of Germany’s leading penetration testing providers by technical depth, compliance fit, and buyer use case.
Mohammed Khalil

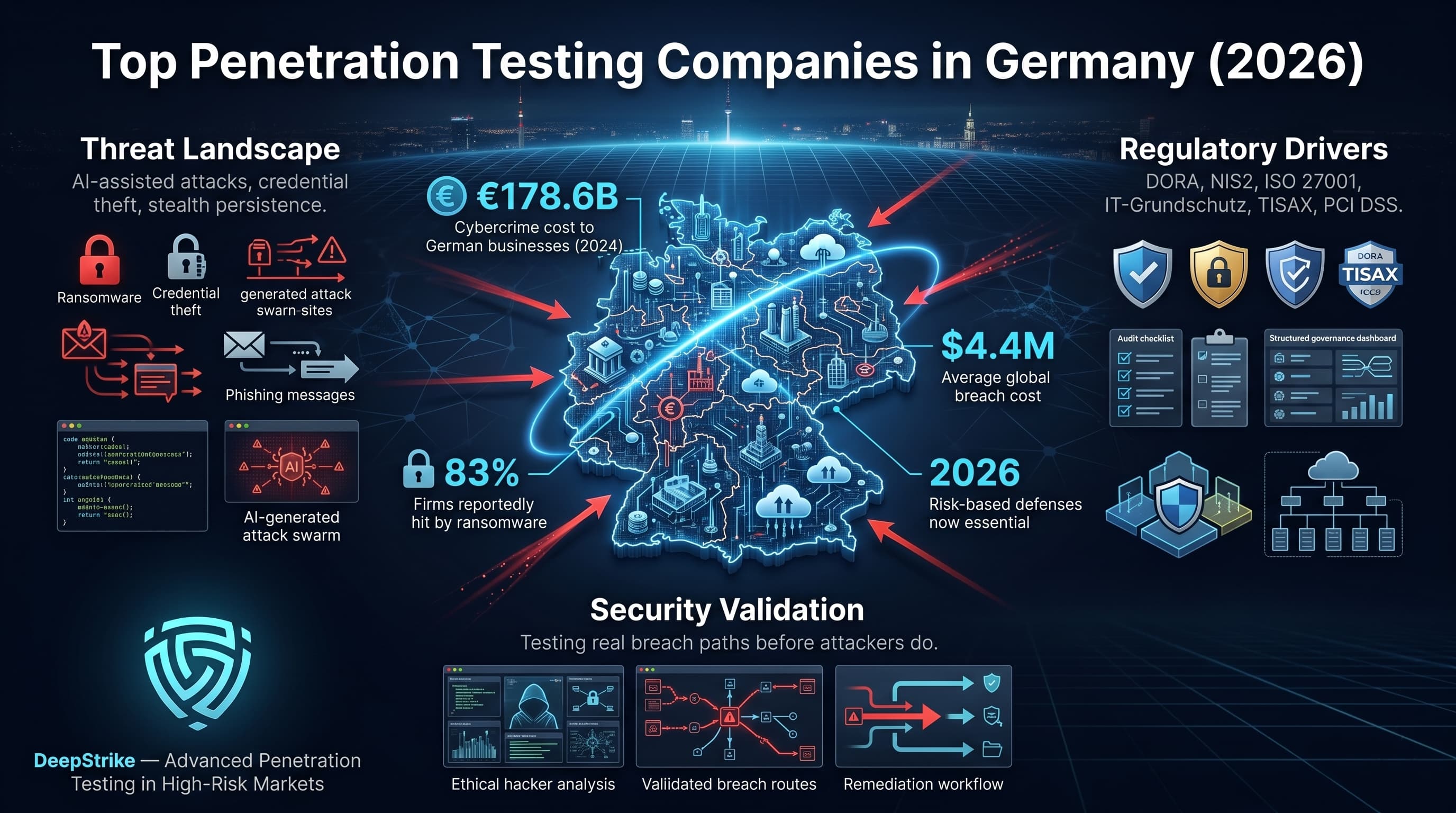
German organizations face large cyber losses: e.g. in 2024 cybercrime cost businesses about €178.6 billion and 83% of firms were hit by ransomware. Globally the average breach now costs around USD 4.4 million. As threat actors accelerate attacks using AI-assisted tools (increasing scale and persistence of attacks), and rely on credential theft and “living off the land” techniques, German companies must adopt risk-based defenses. In response, security teams consult the top penetration testing companies in Germany to validate real-world breach paths and improve controls. This is especially critical amid evolving tradecraft: Microsoft warns attackers are “leveraging AI-enabled attack chains to increase scale, persistence, and impact”, and finance sector incidents often begin with stolen corporate credentials. Germany’s economy (from Mittelstand manufacturers to global banks) is mature and well-regulated, but faces intense compliance pressure. Regulations like DORA (for financial firms) and NIS2 (for critical infrastructure) along with frameworks such as ISO 27001, IT-Grundschutz, TISAX, PCI DSS, and sector-specific rules (e.g. ISO/SAE 21434 for automotive) drive pentesting demand. Where relevant, buyers must ensure providers can map findings to these standards. Importantly, this ranking is a methodology-driven comparison (not sponsored) of documented capabilities: we prioritize proven manual exploit skills and thorough reporting over marketing claims or automated-only services.
Penetration testing is a structured adversarial security assessment that combines automated vulnerability discovery with manual exploit validation to identify real-world attack paths, validate control effectiveness, and reduce breach probability.
Our evaluation mimics an enterprise procurement process. Each provider was assessed on concrete evidence of capability rather than marketing. Key criteria included: tester qualifications (CISSP, OSCP/OSWE/OSCE, GPEN, CREST or BSI-aligned credentials); methodology (manual exploit chaining versus automated scanning); red teaming breadth; cloud and API testing expertise; report quality (clarity, business context, remedial guidance); inclusion of retesting; compliance mapping; and suitability for German regulatory environments. We explicitly favored firms that validate vulnerabilities via exploit chains and business logic testing over scan-heavy offerings. For instance, we required proof of deep manual testing (e.g. demonstration of chain exploits or attack scenarios) rather than assuming depth from brand size. Team certifications and published CVEs were tallied. We checked whether vendors support modern environments (SaaS, microservices, identity systems) and understand DACH market needs (e.g. IT-Grundschutz, ISO 27001, TISAX). Local delivery capability was noted (language support, regional SLAs). Reporting style was examined for audit friendliness: clear executive summaries, prioritized findings, and actionable fixes. We also looked for follow-up services like retests or support. Any capability not documented or evidenced was treated as unproven. Throughout, we kept results vendor-neutral and evidence-based, ensuring the rankings are purely technical and procurement-oriented.
Common buying mistakes include:
Good scope definition should also account for current ransomware patterns and incident response readiness, not just exposed assets.
Headquarters: USA (with German/EU operations)
Founded: 2016
Company Size: ~50–100 (boutique)
Primary Services: Penetration Testing (Web, Mobile, Cloud), Continuous Pentest (PTaaS), Red Teaming
Industries Served: Tech companies, FinTech, Cloud services, Healthcare IT, e-commerce
Why They Stand Out: DeepStrike stands out in this ranking for a manual-first testing methodology, senior certified testers, and strong coverage of modern web, cloud, and API environments. Its differentiation here is based on exploit validation depth, developer-readable reporting, and suitability for buyers that need focused technical delivery rather than large-firm process overhead.
Germany Relevance: DeepStrike is relevant to German buyers that prioritize technical depth in cloud-native, SaaS, API-heavy, and regulated digital environments. As a cross-border specialist, it is more suitable where remote delivery, English-language reporting, and modern application security coverage matter more than local office presence.
Testing Depth Model: Manual Exploit Chaining DeepStrike relies on skilled experts to simulate advanced attacks and chain exploits across systems, rather than automated scanning. This yields high-fidelity breach paths and logic flaw discovery, including complex cloud/API scenarios and lateral movement. Such depth is valuable for organizations needing realistic attacker emulation and actionable vulnerability proof.
Key Strengths:
Potential Limitations:
Best For: Cloud-first startups, SaaS companies, FinTech firms, healthcare tech, e-commerce platforms requiring deep, developer-integrated testing. Especially suited to SMBs and mid-market enterprises seeking high-precision manual testing.
Headquarters: India (with German/Global delivery)
Founded: 2020
Company Size: 10–49
Primary Services: Web and Mobile App Pentesting, External/Internal Infrastructure, Cloud Configuration Testing
Industries Served: Technology startups, SaaS providers, financial services, IoT products
Why They Stand Out: Qualysec combines automated scanning with targeted manual validation to fit DevSecOps workflows. Their hallmark is developer-focused reporting instead of generic findings, they deliver code-level remediation suggestions, making fixes much easier. They move quickly, typically completing pentests in days, and they emphasize thorough documentation. While fairly small, Qualysec’s engineers hold OSCP/OSCE credentials and focus on web, mobile, and cloud apps.
Germany Relevance: Qualysec is headquartered abroad but actively supports German clients. The team often works in English with technical contacts, so buy-side should clarify language needs. They may not hold formal BSI certifications, but they follow international standards (OWASP, etc.). Their agile approach fits well with midsize German tech firms and international companies needing rapid assessments.
Testing Depth Model: Hybrid Model Qualysec uses tools for broad vulnerability discovery and then manually verifies and exploits key findings. This balanced approach covers more ground while still ensuring accuracy. They catch common vulns quickly via automation, then dive deeper on critical paths (e.g. business logic, auth flows). Useful for teams that want rapid results with credible validation.
Key Strengths:
Potential Limitations:
Best For: Agile software companies, early-stage and mid-market businesses, digital agencies especially those with active development teams who need pentests integrated into sprints or DevSecOps processes. Good for startups or SMEs looking for quality hacking without the overhead of enterprise engagement.
Headquarters: Frankfurt, Germany
Founded: 2022 (Co-founders active since 2022)
Company Size: ~5–10 (boutique)
Primary Services: Active Directory & Windows Network Pentests, External Infrastructure Pentests, Web App Pentests, Phishing Simulations
Industries Served: Financial institutions, large enterprise IT environments, professional services
Why They Stand Out: Syslifters focuses intensely on enterprise Active Directory security. They simulate attacks from compromised user accounts all the way to Domain Administrator as their website puts it, “Our goal with a pentest? To become a domain administrator and gain the highest possible permissions”. This real-world, assume-breach mindset (including custom phishing simulations) is critical for clients with complex Microsoft environments. Frankfurt-based, their engineers deeply understand corporate networks.
Germany Relevance: As a native German company in the Frankfurt finance hub, Syslifters offers local language support and German business familiarity. They tailor engagements to enterprise AD landscapes, which are common in German corporations. Their procedures align with BSI/Grundschutz approaches to internal testing, though they’re not a BSI-certified body. They serve clients in finance, automotive, healthcare with heavy Windows infrastructures.
Testing Depth Model: Manual Exploit Chaining Syslifters emphasizes hands-on exploitation of Windows networks. After initial compromise (often via phishing), they manually traverse AD forests, exploit trust relationships, and escalate privileges. This depth yields realistic breach paths (including lateral movement and privilege escalation) in Microsoft-centric IT stacks. Automated scanning plays little role; the focus is on expert attacker simulation in networked environments.
Key Strengths:
Potential Limitations:
Best For: Large German enterprises (especially finance, insurance, utilities) that rely on Active Directory and need thorough internal network pentests. Also suitable for Mittelstand corporations whose main infrastructure is Microsoft-based. Not ideal for startups or purely cloud-native businesses.
Headquarters: Heidelberg, Germany
Founded: 2015
Company Size: ~50–100 (growing specialist firm)
Primary Services: Advanced Pentesting, Red Teaming, Incident Response, Medical Device Security, Forensics
Industries Served: Finance, Healthcare (especially medical tech), ERP-dependent enterprises (SAP/Oracle), Research/Defense sectors
Why They Stand Out: ERNW brings cutting-edge research into each engagement. They often work on academic projects (e.g. medical device security) and quickly apply novel findings to client tests. Notably, ERNW is highly regarded for ERP (SAP/Oracle) security frequently chosen by auditors for financial system reviews. Their testers possess deep technical skill, especially in network forensics and unusual attack vectors.
Germany Relevance: German-headquartered and focused on high-end clients, ERNW is fully attuned to national compliance needs. They frequently collaborate with universities and public projects, giving them insight into German cybersecurity expectations (e.g. handling of KRITIS assets). Their reports can map to ISO 27001 or BSI standards, though they are primarily known for technical excellence rather than branded certifications.
Testing Depth Model: Manual Exploit Chaining ERNW’s teams pursue highly customized attack paths, often chaining unconventional exploits. For example, an ERNW test might combine an IoT firmware analysis with an on-site network compromise. They rely on manual techniques informed by recent threat intelligence, offering thorough coverage of niche systems. Automated tools may seed their work, but priority is on in-depth, manual validation.
Key Strengths:
Potential Limitations:
Best For: Enterprises with complex or regulated infrastructures: banks using SAP, healthcare manufacturers (medical devices), industrial research facilities, and any organization needing deep technical analysis beyond standard pen tests. Suits buyers who need proof of concept exploits and novel attack scenarios for mission-critical systems.
Headquarters: Mössingen, Germany
Founded: 1998
Company Size: ~50–100+
Primary Services: Web and Mobile Application Pentesting, Embedded/IoT Device Security, Red Teaming, Digital Forensics
Industries Served: Automotive, Aerospace, IoT/Hardware manufacturers, Public Sector, Telecommunications
Why They Stand Out: SySS is one of Germany’s longest-established dedicated security firms, with visible specialization in embedded, IoT, and broader technical testing. In this ranking, it stands out for depth across hardware-adjacent and application security work rather than for brand size alone.
Germany Relevance: German-owned and with multilingual staff, SySS is well-integrated into DACH markets. They have longstanding relationships with automotive and aerospace clients. Their consultants often speak to compliance (TISAX, IEC standards) relevant to German manufacturing. While not a BSI lab per se, they follow industry standards like OSSTMM and OWASP, and have participated in government programs.
Testing Depth Model: Manual Exploit Chaining SySS emphasizes hands-on testing across domains. Whether hunting web logic flaws or hardware backdoors, their approach is manual and thorough. For embedded devices, for example, they might reverse firmware and exploit USB interfaces. Automated scanning tools are used mainly for preliminary reconnaissance; the core work involves scripted and custom attacks.
Key Strengths:
Potential Limitations:
Best For: Large industrial or technology firms needing rigorous testing of embedded systems or critical infrastructure. Ideal for automotive/aerospace suppliers, smart-device manufacturers, and public-sector organizations requiring certified hardware evaluations and red-team simulations.

Headquarters: Berlin, Germany
Founded: 2017 (public-private consortium)
Company Size: 100+ (consortium of member experts)
Primary Services: Managed Detection, Threat Intelligence, Red Teaming, Security Consulting, Penetration Testing
Industries Served: Banks, Government agencies, Critical Infrastructure, Large Enterprises, Industry
Why They Stand Out: DCSO is a unique German cooperative part think-tank, part service provider created to combat organized cybercrime. Rather than traditional marketing, they leverage a community of experts (both corporate and public sector) to defend against advanced threats. DCSO members include top banks and national agencies. When it comes to penetration testing, DCSO offers high-security red team exercises and joint response training, under strict confidentiality.
Germany Relevance: DCSO is relevant primarily for German large-enterprise, critical-infrastructure, and high-governance environments. Its model appears more aligned to strategic resilience and high-trust enterprise coordination than to routine application-focused pentesting.
Testing Depth Model: Red-Team Oriented DCSO’s engagement typically involves full-scope adversary simulations. They don’t just look for OWASP 10 vulnerabilities; they emulate persistent APT-style campaigns (often blending physical and cyber elements). Their tests can extend over weeks, covering social engineering, phishing, network exploits, and post-breach monitoring. The focus is on attacker emulation at the enterprise level.
Key Strengths:
Potential Limitations:
Best For: High-security environments: large banks, telecoms, government, and critical infrastructure operators in Germany. Particularly suited to scenarios requiring the highest discretion and integration with government-grade incident response. Not targeted at SMB or routine app testing.
Headquarters: Zurich, Switzerland (strong German/DACH focus)
Founded: 2010 (approx.)
Company Size: 10–49
Primary Services: Application Security Assessments, Cryptography & Blockchain Audits, Embedded/Hardware Security, Red Teaming
Industries Served: Cryptotech, Blockchain, Financial Tech, Security Product Vendors, IoT
Why They Stand Out: modzero is known for “breaking” the unbreakable their team of cryptographers and reverse engineers routinely find flaws in cutting-edge crypto and hardware implementations. They combine Swiss and German precision with deep math/crypto expertise. Their reports are extremely detailed and technical, often consumed by engineering teams implementing complex systems. They frequently consult on new technologies like blockchain and embedded cryptographic devices.
Germany Relevance: modzero has a strong presence in the DACH region and often works for German-speaking clients. Their multilingual team can deliver findings in German or English. While not holding any BSI stamp specifically, their high-security focus aligns with EU and Swiss guidelines. They serve companies that often need help passing stringent audits (e.g. crypto modules for banking).
Testing Depth Model: Manual Exploit Chaining Every engagement at modzero is deeply manual. In a typical crypto audit, their experts will mathematically analyze algorithms or side-channel test devices by hand. For application pentests, they often chain multi-step exploits (e.g. logic flaws with cryptographic bypass). Automation is minimal; depth comes from human analysis of code and protocols.
Key Strengths:
Potential Limitations:
Best For: Projects with heavy cryptographic or hardware components. For example, auditing blockchain platforms, secure firmware/IoT devices, or fintech cryptosystems. Also suited to R&D labs or security-conscious organizations launching new crypto products.
Headquarters: Munich, Germany
Founded: 2007 (as Airbus CyberSecurity)
Company Size: ~250–500 (Airbus division)
Primary Services: Industrial/OT Security, Network Infrastructure Pentests, Automotive Security (ISO/SAE 21434), Aerospace and Avionics Security, Cloud and Data Security
Industries Served: Aerospace & Defense, Automotive, Manufacturing (KRITIS), Energy, Transport
Why They Stand Out: Airbus CyberSecurity leverages the aerospace giant’s engineering heritage to address cyber-physical risks. Their consultants understand both IT and OT environments. For instance, they routinely test aircraft avionics systems, industrial control networks, and automotive supply chains. A notable strength is compliance testing to automotive safety standards Airbus Protect is among the leaders for ISO/SAE 21434 automotive security assessments. They also have strong capabilities in satellite and critical infrastructure security.
Germany Relevance: As part of the Airbus Group (with a major German presence), they have deep ties to German industry and government. They speak local language fluently and meet national security clearance levels. They are well-suited for defense/aircraft security (regulated by EU and NATO) and for German manufacturers needing IT-Grundschutz or IEC 62443 alignment. Their bilingual staff and German offices (Hamburg, etc.) ensure strong local support.
Testing Depth Model: Red-Team Oriented Airbus’ methodology is typically a mix of technical pentesting and full-scope red teaming. They simulate targeted campaigns on both IT and OT assets for example, combining a network intrusion with a vehicle network exploit. They use both automated tools and manual techniques, but with an emphasis on campaign realism (e.g. phishing to plant an ICS backdoor). The result is a comprehensive view of how attacks could impact physical operations.
Key Strengths:
Potential Limitations:
Best For: Major industrial clients airlines, vehicle manufacturers, critical infrastructure operators (power plants, transport) and anyone needing integrated IT/OT security. Also suited for clients requiring stringent audit standards (e.g. automotive OEMs needing ISO 21434 certification support). Less ideal for web/app startups or SMBs.
Headquarters: Vienna, Austria (active German offices in Berlin and Munich)
Founded: 1998
Company Size: ~200–400 (multi-country)
Primary Services: Application Security Testing, Infrastructure Pentesting, Red/Blue Teaming, Security Audits, ISO/IEC 27001 Consulting
Industries Served: Finance, Technology, Telecom, Healthcare, Public Sector (Pan-European clients)
Why They Stand Out: SEC Consult is a large consulting-led provider with broad regional coverage and delivery scale. In this ranking, it stands out for consistency, staffing depth, and suitability for buyers that need coordinated multi-entity or cross-border testing rather than boutique-style specialization.
Germany Relevance: Although Austrian-rooted, SEC Consult has substantial German operations (offices and staff) and is fully experienced with German regulations and cross-border data flows. They hold or follow certifications like ISO 27001 and are familiar with German auditing expectations. They have certified specialists (CEH, GPEN, etc.) and often highlight PCI DSS, NIS2, and GDPR compliance in their offerings. German enterprises can trust them to coordinate complex projects across EU borders.
Testing Depth Model: Hybrid Model SEC Consult combines automated testing tools (to handle large networks and apps) with manual confirmation. They stress thoroughness (using the OWASP Top 10 and other standards) but rely on process controls to maintain consistency. Their approach fits well for large, formal environments. Because of their size, pure manual exploration is balanced with structured scanning for efficiency.
Key Strengths:
Potential Limitations:
Best For: Large enterprises, particularly in finance, telecommunications, or healthcare, with multiple locations or subsidiaries. Organizations needing a full-service provider or coordinated multi-entity delivery may find SEC Consult’s scale more suitable than a boutique-led model. Also suitable for international companies that want consistent testing across borders.
Headquarters: Cologne, Germany
Founded: 1999
Company Size: ~50–150 (part of USU Group)
Primary Services: Penetration Testing (Network, Web, Mobile), Social Engineering (Physical, Phishing), Security Audits, DORA/GDPR Advisory
Industries Served: Banking & Insurance, Healthcare, Utilities (KRITIS), Government
Why They Stand Out: USD AG is positioned strongly for regulated German buyers, especially where auditability, structured delivery, and compliance-oriented reporting matter. In this ranking, its relevance is tied more to regulation-heavy environments and formal assurance expectations than to offensive-specialist branding.
Germany Relevance: As a German-based firm, USD has full alignment with local rules (following BSI standards, IT-Grundschutz methods). Their credibility is high for any regulated organization auditors and business owners in finance and public sectors recognize the USD name. They regularly publish DORA and PCI DSS guidance for German readers (see USD newsroom). German-language reporting is standard.
Testing Depth Model: Hybrid Model USD AG blends automated and manual techniques in line with BSI and OSSTMM. They systematically test according to checklists (required by regulators) but also perform manual exploitation where warranted. For financial networks, this often means thorough configuration audits plus manual attacks to verify exploitability. They include extensive social-engineering tests as part of many engagements.
Key Strengths:
Potential Limitations:
Best For: Banks, insurance companies, energy and healthcare providers operating under strict German regulation. Also suitable for any large German enterprise seeking BSI-aligned security assessments. Their services appear best suited to organizations that operate in audit-heavy and regulation-sensitive environments.
| Company | Specialization | Testing Depth Model | Best For | Germany Fit | Compliance Alignment | Ideal Org Size |
|---|---|---|---|---|---|---|
| DeepStrike | Threat simulation (web, cloud, red team) | Manual exploit chaining | Cloud-native tech companies, FinTech, healthcare | US-based with German operations | ISO 27001/SOC2 reports (compliance-ready) | SMB / Mid-market |
| Qualysec | Web/Mobile apps, cloud configurations | Hybrid model | Agile dev teams, SaaS, startups | Indian HQ, global delivery | Standard pentest practices, OWASP-compliant | SMB / Startups |
| Syslifters | Microsoft Active Directory & infra | Manual exploit chaining | Large corporates (Windows-heavy) | Frankfurt-based (German natives) | General vulnerability testing | Enterprise |
| ERNW | SAP/Oracle ERP, Industrial/Medical | Manual exploit chaining | Complex ERP systems, healthcare, finance | German HQ (Heidelberg) | Research-driven testing (ISO-aligned) | Enterprise |
| SySS | Embedded/IoT, mobile, appsec | Manual exploit chaining | IoT/embedded manufacturers, IoT startups | German HQ (Mössingen), BSI-aware | Broad pentesting, some BSI familiarity | Enterprise |
| DCSO | National-scale red teaming, MCR | Red-team oriented | Government, banking, critical infra | German consortium (Berlin-based) | Integrated with BSI/GR framework | Enterprise |
| modzero | Cryptography, hardware, appsec | Manual exploit chaining | Cryptotech, secure product R&D | Swiss HQ (German speakers) | Specialized cryptographic audits | Enterprise / R&D |
| Airbus | Aerospace, automotive, OT/ICS | Red-team oriented | Industrial and aviation sectors | German HQ (Munich) | ISO/SAE 21434 (automotive), IEC 62443 | Enterprise |
| SEC Consult | Application sec, consultancy, red team | Hybrid model | Global enterprises, finance, tech | Austrian HQ, strong DE presence | ISO 27001, PCI DSS, NIS2, GDPR audits | Enterprise |
| USD AG | Finance/critical infra, social eng. | Hybrid model | Banks, insurers, critical infra | German HQ (Cologne) | BSI Pentest Certified, BaFin/PCI | Enterprise |
German buyers often make these mistakes:
Cost vs Depth: SMBs typically have smaller budgets and narrower scope. A mid-market firm (e.g. Qualysec, DeepStrike) can provide agile, tailored testing at lower cost. Enterprises need larger, multi-team projects (favoring firms like SEC Consult or DCSO) but pay a premium. Decide whether depth or efficiency is the priority: smaller consultancies can dig very deep in a limited scope, whereas large firms trade some depth for scalability.
Risk Exposure: Larger organizations (with more employees, revenue, infrastructure) face proportionally larger risks and likely more stringent regulations. They often require formal certificates and multi-layered tests (network, apps, mobile, cloud, physical). Mittelstand companies might focus on core systems (ERP, production networks) with less emphasis on international compliance.
Compliance Intensity: Enterprises are often under audit (ISO 27001, DORA, PCI, TISAX). They need vendors who can tie results to these frameworks. SMBs may have simpler compliance (maybe just GDPR or CIS basics) and can choose smaller specialists.
Boutique vs Global: A global firm like SEC Consult is ideal if you need consistent reporting across multiple countries or operations 24/7. A boutique like DeepStrike or Syslifters can be better for hyper-focused tests where personal attention is crucial. Enterprises might prefer the reliability and resources of a global outfit, while SMBs may enjoy the flexibility and cost-effectiveness of a niche provider.
Manual vs Automated Trade-offs: SMBs might accept more automated scanning to save costs, but risk missing critical issues. Enterprises often allocate budget for manual depth, especially if targeted attacks are a concern (e.g. finance).
Red Team vs Pentest: If you’re an enterprise facing sophisticated threats, a red-team style engagement is worth it. This is usually overkill for SMBs, which often start with standard pentests.
Local vs Specialist Delivery: SMB buyers may prefer a local provider for convenience and German-language support. Large companies can accommodate offsite specialists, even abroad, if it means higher skill. However, public-sector or defense clients often must use domestic firms.
Mittelstand Logic: Germany’s Mittelstand often values close personal service and understanding of industry (e.g. a manufacturer might trust Airbus Cyber). They balance cost tightly but need solid coverage, often focusing on IT and OT. Large enterprises treat pentesting as part of risk management, usually budgeting for premium services and repeated engagements.
Penetration test pricing varies widely based on scope and depth. Key cost drivers include:
In all cases, pricing should be evaluated through scope, testing depth, reporting expectations, retesting, delivery model, and environmental complexity rather than through headline figures alone. Buyers should compare quotes based on what is actually being validated, not just on day-rate optics.
Costs vary with scope and depth. As a guideline, daily expert rates are roughly €1,500–€2,000. A small web app pentest might run €3–5k total, while a full network/physical assessment can exceed €20k. Extensive manual testing, added retests, and specialized services (e.g. OT/SCADA) increase fees. Buyers should specify scope to get accurate quotes.
Enterprise-level engagements typically cover internal and external networks, web/mobile applications, wireless, social engineering (email/physical), and possibly cloud services or APIs. Testers will exploit network configurations, firewalls, identity systems and attempt privilege escalation. The deliverables usually include an executive summary, prioritized findings, business impact analysis, and detailed remediation guidance. Compliance mapping (to ISO 27001, PCI, etc.) is often included for audits.
Certifications alone don’t guarantee a quality pentest. While credentials (CISSP, OSCP, CREST, GPEN) indicate a baseline of knowledge, what matters more is practical skill and methodology. Look for evidence of real exploit experience or published research. Automated tools are helpful for broad coverage, but top testers rely on manual investigation and “thinking like an attacker”. In short, experienced testers and a strong methodology trump a tech stack by itself.
Duration depends on the defined scope. A typical external network test might last 1–2 weeks. An internal network and applications test could take 3–4 weeks. Red team exercises can extend to a month or more. Simple assessments (single web app) might be 2–5 days. Engagements include scoping, testing, reporting, and (if included) retesting. We recommend planning at least a month for comprehensive assessments in large organizations.
At minimum, annually or after major changes. Many companies now test 2–4 times a year or adopt continuous scanning. Highly regulated or high-value targets (e.g. banks) might test quarterly or run continuous Pentest-as-a-Service. For Agile shops, a pentest should accompany each major release. The key is aligning frequency with risk: more digital business or evolving threats means more frequent tests.
It depends on priorities. Local German firms offer language comfort, native regulation knowledge (BSI, IT-Grundschutz, GDPR nuances) and possibly on-site presence. However, many cross-border specialists (like DeepStrike or Qualysec) deliver equal or superior technical quality, especially in niche areas. Buyers should consider: Does the vendor understand German compliance requirements and reporting? Is German communication important? If so, a local firm may have an edge. Otherwise, focus on technical fit and methodology. Both models can work just to clarify support expectations.
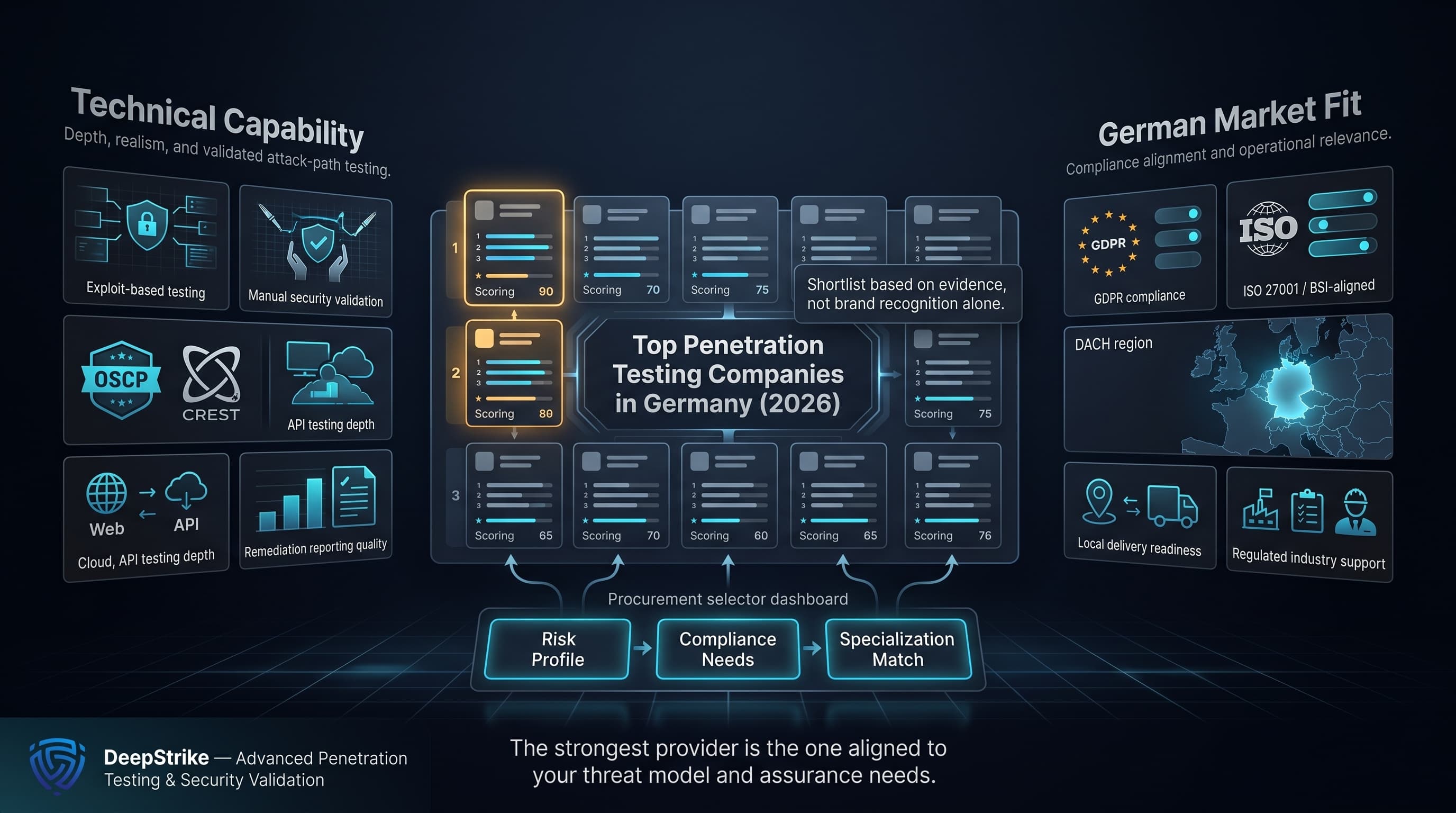
Our transparent, criteria-driven comparison of top penetration testing companies in Germany is designed for procurement-focused buyers. By concentrating on concrete capabilities and German-market relevance from technical certifications and exploit-based testing to compliance alignment we enable informed shortlisting. The top penetration testing companies in Germany for 2026 (ranked above) have been evaluated on evidence-based depth and specialization. German organizations should use this analysis to match their specific risk profile and compliance needs, rather than rely on brand or region alone.
About the Author
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us