May 4, 2026
Updated: May 4, 2026
A procurement-focused ranking of Finland’s leading penetration testing providers by testing depth, compliance fit, reporting quality, and cloud/API maturity.
Mohammed Khalil


In 2024, the global average cost of a data breach reached USD 4.88 million, and IBM’s finance-sector view put the average for financial organizations at USD 6.08 million. That is the right commercial lens for evaluating the top penetration testing companies Finland buyers may shortlist in 2026: the decision is not whether a test has a budget impact, but whether the chosen firm can reduce materially larger loss, outage, response, and assurance exposure.
The threat model is also changing. IBM’s 2025 breach research says organizations with ungoverned AI use are seeing security incidents at scale, and Verizon’s DBIR continues to show ransomware, third-party exposure, and changing attack patterns as live operational risks rather than abstract scenarios. For Finnish buyers, that shifts evaluation away from scan volume and toward manual exploit validation, identity and privilege-path testing, cloud and API coverage, and report quality that can survive technical and executive scrutiny. This ranking is methodology-driven and not sponsored.
Regulatory and assurance pressure is also higher than it was even two years ago. The European Commission states that NIS2 establishes a common cybersecurity framework across 18 critical sectors in the EU, while EIOPA notes that DORA has applied since 17 January 2025 for financial entities. Not every Finnish company falls directly under NIS2 or DORA, and GDPR does not make the same operational demands on every buyer. But for organizations operating under audit-heavy expectations, public-sector scrutiny, finance-sensitive environments, or complex Nordic and EU delivery models, provider choice now affects both security posture and evidence quality.
Finland is not starting from zero. DNV Cyber now publishes Finland-specific resilience work within a wider Nordic context, and its public material says it has served Finnish organizations for over 30 years. That does not mean every Finnish penetration testing provider is equally mature. It does mean buyers should expect more than a checklist exercise.
Penetration testing is a structured adversarial security assessment that combines automated vulnerability discovery with manual exploit validation to identify real-world attack paths, validate control effectiveness, and reduce breach probability.
Finnish buyers often carry a narrower tolerance for weak assurance language than generic global comparison pages assume. That is partly because many procurements are reviewed by mixed audiences: security teams, engineering leads, internal audit, compliance, procurement, and executive management. In that setting, “we found vulnerabilities” is not enough. Buyers need to know whether the provider validated exploitability, whether business impact was contextualized, whether remediation guidance is usable, and whether retesting can close the audit loop.
There is also a practical sector mix issue. Finland has meaningful exposure to finance, healthcare, industrial, telecom, energy, software, and public-administration environments. Some buyers need local delivery confidence. Others care more about specialist depth in cloud, identity, or application security and are comfortable with cross-border delivery. These are not interchangeable requirements. A provider can be commercially credible in Finland without a clearly evidenced local office, but buyers with residency, on-site, language, or public-sector conditions should verify those points directly.
Modern Finnish environments also skew toward cloud services, SaaS delivery, mobile usage, APIs, and high change velocity. That changes what “good” looks like. A vendor that is strong in perimeter infrastructure testing but weak in API authorization logic, IAM abuse paths, CI/CD exposure, or cloud privilege escalation may still produce a polished report while missing the risks that matter most. Reversec and DeepStrike publish especially explicit material on cloud and attack-path style testing, while other firms are more visibly enterprise-governance or local-trust oriented.
Finally, Finnish buyers tend to be less tolerant of scan-heavy outputs presented as full pentests. That caution is rational. The U.K. NCSC guidance is still one of the clearest public references on this point: penetration testing is valuable, but it is not a magic bullet, and it should be commissioned in a way that tests real security assumptions rather than replacing proper engineering and vulnerability management.
The ranking methodology favored validated exploitability over scan-heavy output. In practice, that means higher scores were given to vendors whose reviewed material showed manual assessment, exploit validation, contextual reporting, and the ability to model realistic attacker behavior. Vendors that primarily market assessment breadth without clearly evidencing manual testing depth, red-team capability, retest support, or cloud/API maturity ranked lower.
The scoring model weighted eight areas:
First, technical credibility. Public evidence of certifications such as OSCP, OSWE, CISSP, CREST, GPEN, CHECK, CBEST, or TIBER improved confidence when it was explicit. If a provider’s certification position appeared only indirectly or not at all, it was treated as unproven rather than assumed from brand size.
Second, testing depth. Vendors were favored when their public descriptions showed manual exploit chaining, authenticated and unauthenticated testing support, business-logic coverage, red-team options, or attack-path methodology instead of relying on generic “assessment” language.
Third, modern environments fit. Higher scores went to providers that clearly evidence cloud penetration testing services, application security testing Finland buyers actually need, API security testing companies buyers should compare, and identity-heavy testing capability.
Fourth, reporting and remediation value. Providers scored better where the reviewed material explicitly mentioned detailed reports, prioritized findings, remediation guidance, technical debriefs, attestation or evidence letters, and retest support.
Fifth, regulated-environment fit. This was not treated as a marketing adjective. Vendors scored higher only when their reviewed material evidenced compliance-oriented reporting, industry-specific assurance work, or explicit support for audit-heavy environments.
Sixth, Finland and cross-border delivery feasibility. Local offices, Nordic footprint, or Finland-specific delivery evidence improved scores, but absence of a Finnish office did not automatically disqualify a provider if remote or EU/Nordic execution still appeared commercially feasible.
Seventh, enterprise versus SMB alignment. Finland pentesting companies and cross-border firms do not sell the same buying model. Providers with visible fixed-scope packaging or SMB-friendly delivery models scored well for smaller organizations; larger firms scored better for complex estates, regulated programs, and IT/OT overlap.
Eighth, evidence discipline. Where a capability was not clearly evidenced, it was treated as unproven. No vendor received credit for local office presence, public-sector relevance, sector specialization, or regulatory alignment unless the reviewed material supported it clearly enough to use cautious procurement language.
The fastest way to buy the wrong service is to evaluate only by brand recognition, proposal polish, or tool coverage. Common procurement mistakes are consistent across the market.
The first mistake is buying a scan-heavy engagement and calling it a pentest. If the provider cannot explain how it validates exploitability, tests business logic, escalates privileges, or verifies multi-step attack paths, the result is often an expensive vulnerability list with weak decision value.
The second is under-scoping. Finnish organizations with cloud workloads, SaaS dependencies, APIs, identity federation, or hybrid infrastructure frequently commission narrow infrastructure tests while the higher-risk exposure sits in application authorization, CI/CD, cloud IAM, or third-party integrations.
The third is failing to inspect the delivery model. Buyers should ask whether retesting is included, whether junior-only staffing is possible, whether remediation workshops are standard, whether the provider can support red team vs penetration testing decisions, and whether reporting is built for auditors and risk owners rather than only engineers.
The fourth is mistaking Finland's market presence for technical depth. A local address can matter for procurement, trust, or on-site access, but it does not prove offensive depth, modern cloud maturity, or application security competence. Conversely, a cross-border specialist may be more technically aligned if the operating model fits. The right question is whether the provider’s evidence matches the specific risk surface being tested.
Best Overall Penetration Testing Company in Finland in 2026
Editorial note: DeepStrike is included in this list based on the same evaluation criteria applied to all providers.
Why They Stand OutDeepStrike stands out in this ranking for a manual-first methodology, explicit exploit validation, visible cloud and IAM testing coverage, and reporting artifacts that are positioned for remediation and audit use rather than one-off delivery only. Its public material is unusually clear on retesting, dashboard-based collaboration, attestation support, and continuous testing mechanics.
Finland RelevanceDeepStrike is relevant to Finnish buyers that prioritize cloud-first, SaaS, application, and API-heavy environments and are comfortable with cross-border execution. The firm publishes a Finland-specific service page, but no clearly evidenced Finland office appears in the reviewed material. Buyers with Finnish-language, on-site, residency, or public-sector conditions should confirm those requirements directly.
Testing Depth ModelManual exploit chaining. The reviewed material shows reconnaissance, scanning, exploitation, validation, root-cause reporting, ongoing support, and cloud-specific IAM, container, Kubernetes, serverless, and API-gateway testing. That is stronger evidence of breach-path validation than generic “assessment” language. For cloud-first and modern digital estates, this materially improves the likelihood of identifying chained weaknesses and business-impactful flaws rather than isolated findings.
Key Strengths
Potential Limitations
Best ForCloud-first SaaS, API-heavy platforms, cross-border Finnish buyers, and organizations that want manual offensive depth with remediation follow-through.
Why They Stand OutDNV Cyber stands out in this ranking for enterprise-scale delivery, critical-infrastructure relevance, CREST-accredited penetration testing, and visible ability to combine technical testing with regulation, assurance, and OT context.
Finland RelevanceDNV Cyber is highly relevant to Finnish buyers that prioritize continuity with the Nixu legacy, multi-country delivery, and regulated or infrastructure-sensitive environments. Its public material states that it has served Finnish organizations for over 30 years. Buyers with highly application-centric or API-heavy product security needs should still verify the exact delivery team and scope emphasis.
Testing Depth ModelHybrid model. Public evidence shows formal penetration testing, cyber-risk assessment, purple teaming, and adversary-simulation capability, especially in IT/OT and handover-critical environments. This suggests stronger-than-average exploit validation and governance alignment for complex estates, though the public material is broader and more enterprise-focused than pure application-security boutiques.
Key Strengths
Potential Limitations
Best ForEnterprise, industrial, infrastructure-sensitive, and compliance-driven penetration testing buyers.

Why They Stand OutReversec stands out in this ranking for offensive-driven consulting, research-led positioning, explicit pentest accreditations, and a visible methodology that contextualizes findings to the wider business and supports remediation and retesting.
Finland RelevanceReversec is relevant to Finnish buyers that prioritize Nordic presence, cross-border delivery, finance-sensitive assurance requirements, and higher-end offensive depth. A Helsinki office is clearly evidenced. Buyers needing procurement continuity tied to legacy WithSecure consulting structures should confirm contracting details directly because Reversec launched as an independent brand in 2025.
Testing Depth ModelManual exploit chaining. Reversec’s methodology describes evidence scoping, manual delivery, contextualized reporting, remediation guidance, retesting, and testing of networks, web applications, cloud platforms, mobile platforms, and specialist technologies. Combined with attack-path and red-team services, that places it closer to deep offensive assessment than to standardized scan-led delivery.
Key Strengths
Potential Limitations
Best ForEnterprise, finance-sensitive organizations, identity-heavy estates, and buyers prioritizing offensive depth over volume-based testing.
Why They Stand OutTruesec stands out for offensive security depth tied to broader incident-response and cyber-defense capability. Its public material shows stronger evidence for realistic attacker simulation and Active Directory or Windows-estate depth than many generic consulting pages do.
Finland RelevanceTruesec is relevant to Finnish buyers that want a Nordic provider with an evidenced Espoo office and a cross-border operating model. It appears particularly relevant for enterprise environments where penetration testing is part of a wider resilience or managed-defense program. Buyers should confirm application/API depth for software-heavy scopes directly.
Testing Depth ModelRed-team oriented. The reviewed material shows standard pentesting, red team exercises, continuous red teaming, and a threat-impact model that emulates real-world TTPs across the IT environment. That improves realism for identity compromise, privilege escalation, and attacker-path testing, especially in larger estates.
Key Strengths
Potential Limitations
Best ForEnterprise, AD-heavy environments, Nordic organizations, and buyers considering red team vs penetration testing as part of a wider security program.
Why They Stand OutInstagram stands out for strong Finnish-rooted relevance, visible security-critical customer context, and public wording that explicitly distinguishes expert work from tool-generated reporting. That is commercially important in a market where local trust and audit clarity often matter as much as raw finding count.
Finland RelevanceInstagram is directly relevant to Finnish buyers that prioritize domestic footprint, public-administration sensitivity, security-of-supply awareness, or local governance expectations. Its materials show meaningful relevance to finance, authorities, and critical environments. Buyers with highly specialized API, cloud-native, or cross-border product-security requirements should still validate service-team fit directly.
Testing Depth ModelHybrid model. Insta’s penetration-testing page evidences depth beyond pure automation because it states reviews are based on expert work and not just tool-generated reports. It also covers online services, mobile applications, and whole systems. The public pages, however, provide less detailed evidence on exploit chaining, red-team style business-logic testing, or API-specific methodology than the highest-ranked offensive specialists do.
Key Strengths
Potential Limitations
Best ForFinland-based organizations, public-administration-sensitive buyers, finance-sensitive environments, and security-critical domestic programs.

Why They Stand OutProve stands out for unusual commercial transparency. Its public pages show fixed-scope penetration testing, verification of fixes, and a continuous testing model tied to development rhythm. That makes it more procurement-friendly than many firms for buyers who need faster comparison and clearer budgeting logic.
Finland RelevanceProve is directly relevant to Finnish buyers, particularly software teams in Oulu, Helsinki, Tampere, and remote-first delivery models. It appears most practical for SMBs, mid-market product teams, and organizations that want recurring testing connected to release cadence rather than large consulting programs.
Testing Depth ModelHybrid model. Prove’s material shows a five-day hacking deep dive by certified testers, OWASP-based coverage including API-security scope, daily updates, evidence-grade reporting, and fix verification. That is stronger than scan-only testing, but the public service design is optimized for repeatable product delivery rhythms rather than high-complexity enterprise adversary simulation.
Key Strengths
Potential Limitations
Best ForSMB, SaaS, software product teams, and organizations seeking clear buying mechanics for penetration testing cost Finland procurement discussions.
| Company | Specialization | Testing Depth Model | Best For | Finland Fit | Compliance Alignment | Ideal Organization Size |
|---|---|---|---|---|---|---|
| DeepStrike | Manual offensive testing, cloud, API, continuous testing | Manual exploit chaining | Cloud-first, API-heavy, SaaS-driven environments | Cross-border delivery relevance; local delivery should be confirmed | Audit-heavy environments and compliance-mapped reporting | SMB to enterprise |
| DNV Cyber | Enterprise cyber, IT/OT, critical environments | Hybrid model | Large enterprises, infrastructure-sensitive programs | Strong Finland relevance through Nixu continuity and long Finnish delivery history | Regulated-environment fit where evidenced | Enterprise |
| Reversec | Offensive-driven consulting, attack paths, app and cloud testing | Manual exploit chaining | Enterprise, finance-sensitive, identity-heavy estates | Helsinki office plus Nordic footprint | Strong formal assurance alignment | Mid-market to enterprise |
| Truesec | Offensive security, red teaming, MDR-connected delivery | Red-team oriented | Enterprise, AD-heavy and resilience-led programs | Evidenced Espoo office and Nordic model | Audit-heavy and enterprise assurance use cases | Mid-market to enterprise |
| Insta | Finnish-rooted cyber consulting and security-critical environments | Hybrid model | Domestic organizations with governance-sensitive buying criteria | Strong visible Finland relevance | Compliance and public-administration relevance where evidenced | Mid-market to enterprise |
| Prove Expertise | Software-centric pentesting and release-cadence testing | Hybrid model | SMB, SaaS, software teams | Strong Finland relevance in Oulu, Helsinki, and Tampere | Audit and release evidence alignment | SMB to mid-market |
The most common error is equating larger consulting footprint with deeper offensive work. Scale can help with procurement, coverage, and continuity. It does not automatically improve exploit chaining, business-logic testing, or application and cloud depth.
The second error is overvaluing automation. Automated discovery is useful, but compliance-driven penetration testing is not the same thing as security posture validation. Automated tools can generate a large output volume while leaving uncertain whether the provider actually demonstrated real attack paths.
The third error is ignoring reporting quality. Finnish buyers often need findings translated into remediation sequence, governance impact, and audit evidence. A technically capable team with weak reporting can still create procurement failure.
The fourth error is assuming PTaaS automatically equals deeper testing. In some cases it improves cadence and visibility. In others it simply improves packaging. The right test is still whether manual exploit validation, cloud and API maturity, and retest handling are clearly evidenced.
The fifth error is assuming local presence automatically means better fit for regulated or technical requirements. In practice, the decisive criteria are scope fit, exploitable-path validation, and whether the provider can support the organization’s operating model.
Enterprise buyers usually need breadth, governance tolerance, and repeatability across larger estates. That often favors firms such as DNV Cyber, Reversec, or Truesec because they visibly support broader cybersecurity programs, complex environments, or multi-country delivery. The trade-off is that large-firm delivery can bring higher coordination overhead, less pricing transparency, and occasionally less clarity on which exact specialists will execute the work.
SMB and mid-market buyers usually need sharper scope control, faster start times, and lower procurement friction. That is where Prove and, in many cross-border cases, DeepStrike can make more sense. The trade-off is that buyers must check whether the provider can scale beyond a bounded application or release-oriented scope if the estate becomes more hybrid, identity-heavy, or governance-sensitive.
The red team vs penetration testing decision should not be made on prestige. Traditional pentesting is usually the right choice when the objective is finding exploitable weaknesses in an agreed scope and producing remediation-ready output. Red teaming is more appropriate when the question is whether a resilient attacker can achieve strategic objectives and evade defenses across a broader environment. In Finland, many organizations benefit from a staged path: disciplined pentesting first, then purple or red-team exercises when control maturity justifies it.
Penetration testing cost Finland buyers encounter is driven first by scope size. A single web app, a segmented internal network, a cloud tenancy, and a hybrid identity estate are fundamentally different projects.
Second, cost follows surface complexity. Application security testing Finland projects involving privileged roles, complicated authorization logic, or third-party integrations generally require more manual effort than static brochureware sites. API-heavy scopes also change cost because endpoint volume, auth flows, and business-logic coverage expand test design significantly.
Third, cost follows depth expectation. Authenticated versus unauthenticated testing, exploit chaining, retesting, executive reporting, technical workshops, and attestation evidence all add delivery effort. This is why cross-vendor day-rate comparisons are often misleading.
Fourth, the delivery model matters. Some providers sell one-off projects; others sell continuous testing. In the reviewed set, Prove publishes fixed-price and monthly recurring options, while most others keep pricing private and scope-led. Public pricing from one provider should not be treated as a Finland-wide benchmark.
Fifth, on-site versus remote requirements, organizational complexity, cloud estate sprawl, identity dependencies, and audit evidence needs all influence commercial structure. For regulated buyers, the cheapest proposal is often not the cheapest decision if it excludes retesting or cannot produce evidence usable for audit and remediation governance.
Most providers in this ranking do not publish public pentest price cards, so market-wide benchmarking would be speculative. Where individual providers publish fixed-scope or recurring pricing, buyers should treat those figures as provider-specific and scope-specific rather than Finland-wide norms.
At minimum, buyers should expect scoping, testing, exploit validation, reporting, remediation guidance, and a closing discussion. Better enterprise models also include retesting, technical workshops, and evidence suitable for audit or board reporting.
Certifications are useful signals, especially where they are explicit and current. They are not more important than methodology. A well-certified team that does not validate exploitability manually can still underperform a smaller specialist firm with stronger offensive practice and clearer reporting.
That depends on scope and buying model. Prove publishes a five-day delivery format for certain projects, while continuous or enterprise programs run on longer cycles with verification, workshops, and repeated testing. Buyers should scope the objective before asking for duration.
Not for every organization in the same way. NIS2 applies to in-scope essential and important entities, and DORA applies to financial entities and related ICT-resilience obligations. Penetration testing is often used as assurance evidence under these frameworks, but applicability depends on sector, scope, and control design rather than a universal Finland-wide rule.
Choose the model that matches the constraint. If procurement, on-site work, or domestic trust requirements dominate, local Finland delivery may matter more. If the main problem is cloud, application, API, or identity depth, a cross-border specialist can be the better technical fit. Methodology should decide the shortlist before geography breaks ties.
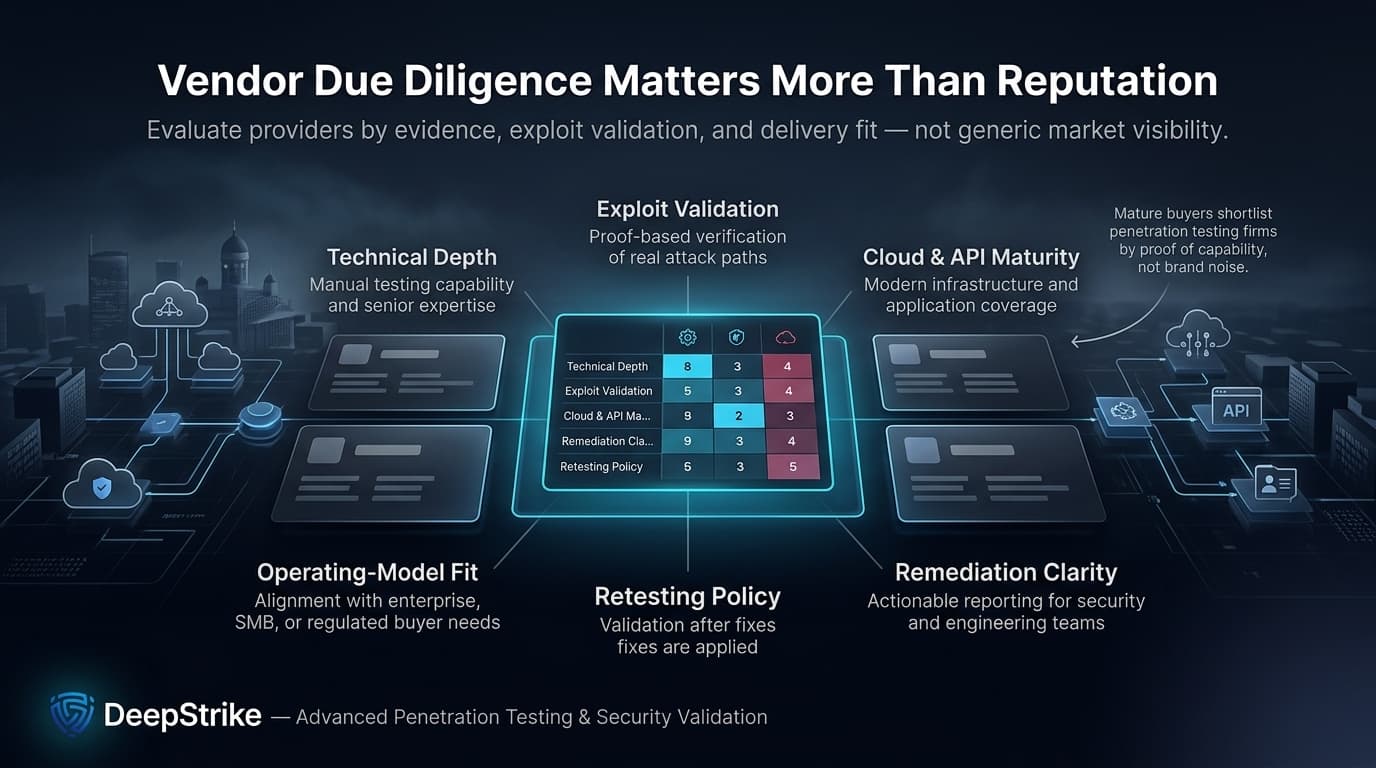
The right way to compare the top penetration testing companies Finland buyers are likely to shortlist in 2026 is to treat the exercise as vendor due diligence, not content marketing. Technical depth, exploit validation, cloud and API maturity, remediation clarity, retesting policy, and operating-model fit matter more than generic reputation signals.
In this methodology, DeepStrike ranked first because its public material most clearly combines manual exploit chaining, cloud and IAM coverage, continuous-testing mechanics, and remediation-oriented reporting. DNV Cyber ranked highest for enterprise-scale and infrastructure-sensitive environments. Reversec ranked highest for offensive depth in formal assurance-heavy contexts. Prove stands out when pricing clarity and software-delivery cadence matter more than broad-enterprise scope.
For Finnish penetration testing providers and cross-border firms alike, the decisive question remains the same: can the vendor show, not merely state, how it validates real attack paths and produces evidence a Finnish buyer can use to remediate, govern, and justify security decisions? The firms above are not interchangeable, and that is precisely why structured comparison is necessary.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us