May 7, 2026
Updated: May 7, 2026
A procurement-focused ranking of Bulgaria penetration testing providers by methodology, compliance fit, reporting quality, and cloud/API testing depth.
Mohammed Khalil

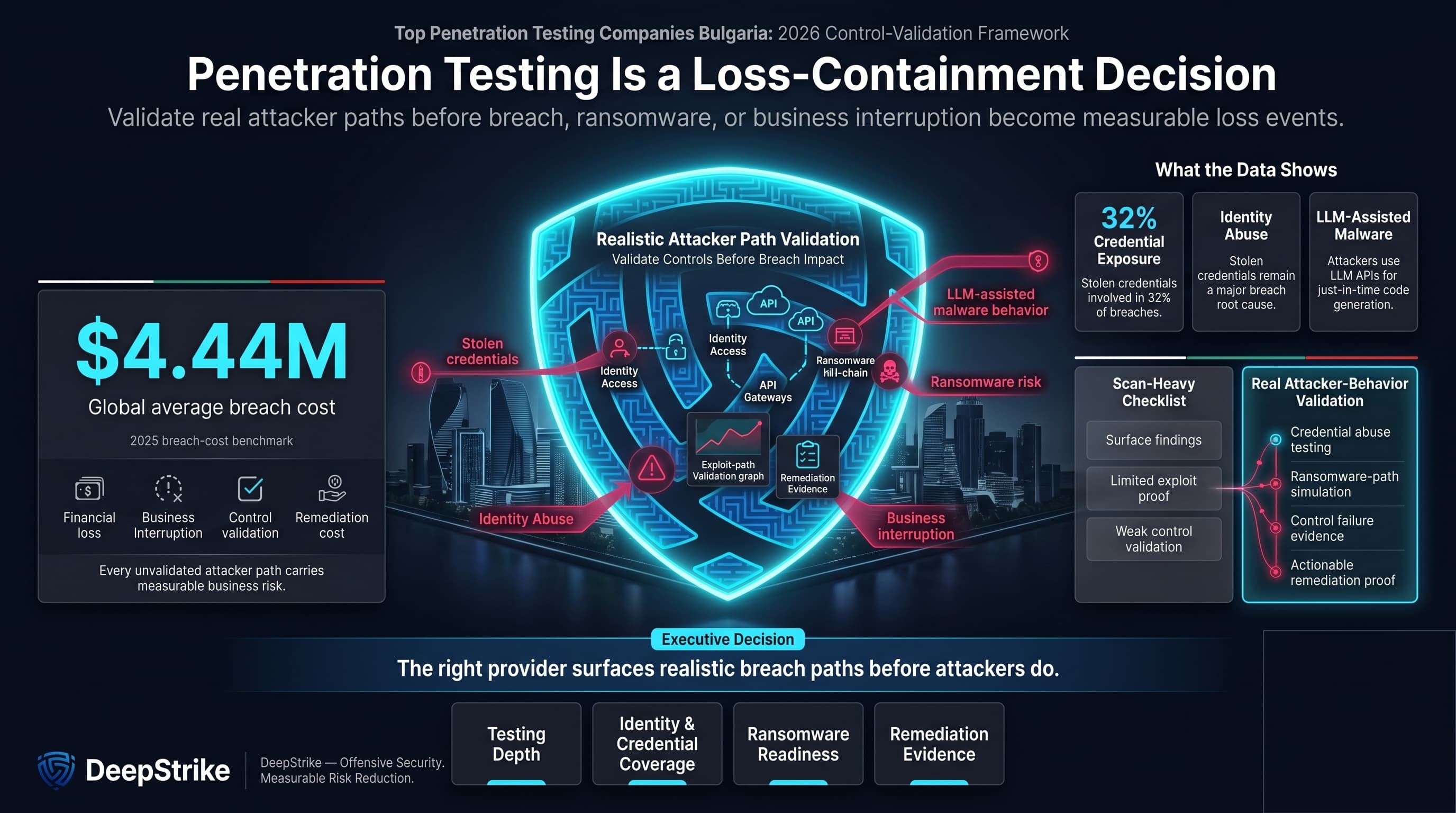
With the global average cost of a data breach at USD 4.44 million in 2025, the question behind top penetration testing companies Bulgaria is fundamentally about loss containment, control validation, and whether a provider can surface real attacker paths before a breach, ransomware event, or business interruption hits. Stolen credentials were involved in 32% of breaches in the 2025 DBIR and remain the primary cause of web-application breaches, while ENISA says identity abuse and the use of stolen credentials remain major root causes of breaches. A 2026 Google Cloud and Mandiant report also describes attackers integrating LLM APIs directly into malware for just-in-time code generation by late 2025, pushing testing buyers toward providers that can validate realistic attacker behavior rather than produce scan-heavy checklists.
In Bulgaria, buyer scrutiny is rising. Industry stakeholders described the local cybersecurity ecosystem in 2024 as evolving and still young, and Bulgaria’s Cybersecurity Act was amended in February 2026 to transpose NIS2-style obligations into national law, widening scope and increasing risk-management and incident-notification expectations for affected entities. For finance-sensitive organizations, DORA has applied since 17 January 2025 and explicitly covers digital operational resilience testing for in-scope financial entities. GDPR, by contrast, is risk-based under Article 32 and does not create a universal named pentest requirement for every buyer. This ranking is methodology-driven and not sponsored.
Penetration testing is a structured adversarial security assessment that combines automated vulnerability discovery with manual exploit validation to identify real-world attack paths, validate control effectiveness, and reduce breach probability.
Buyer behavior in Bulgaria is shaped by two overlapping pressures: local governance scrutiny and uneven provider depth. The Cybersecurity Act changes in 2026 widen the scope of entities facing formal cybersecurity obligations, including sectors such as banking, financial market infrastructure, healthcare, and some public bodies, while DORA adds direct resilience-testing relevance for in-scope financial entities. That means buyers are often selecting a pentest provider not only for engineering value, but also for how well the output will stand up in audit, board, risk, and remediation workflows.
That local context changes vendor selection. Bulgaria buyers often need stronger remediation clarity, cleaner executive reporting, and more explicit methodology than markets where pentesting is already deeply standardized. They also face a practical trade-off between local provider familiarity and the specialist depth sometimes offered by cross-border firms. For cloud-native and API-heavy environments, identity paths, business logic, and release velocity matter more than perimeter scanning alone. For public-sector, healthcare, infrastructure-sensitive, or finance-sensitive environments, formal scope control and evidence-backed reporting usually matter more than aggressive marketing language.
The ranking favors validated exploitability over scan-heavy output. The National Institute of Standards and Technology defines penetration testing as mimicking real-world attacks and notes that effective tests often combine multiple weaknesses to gain more access than a single flaw would allow. The OWASP Foundation frames web security testing as a structured best-practice discipline, not just an automated scan. Providers therefore scored higher when public evidence showed manual testing depth, realistic attack simulation, exploit chaining, or red-team capability, and lower when public materials leaned mainly on generic automation claims.
The commercial ranking criteria were:
Capabilities not clearly evidenced in reviewed material were treated as unproven. Brand scale did not automatically increase rank. A large network can improve coverage and governance support, but a smaller specialist can still rank higher if public evidence shows deeper manual testing, clearer reporting, and stronger cloud/API focus.
Most bad selections fail during scoping, not after testing starts. The common procurement mistakes are choosing a scan-only vendor, under-scoping APIs or identity flows, assuming retesting is included when it is not, accepting junior-heavy staffing without checking who actually executes the work, and confusing compliance language with real security validation. Buyers in audit-heavy environments should inspect sample deliverables or, at minimum, require explicit detail on exploit proof, remediation structure, executive summary quality, and whether findings are mapped to the control framework that actually matters to them. In Bulgaria, another recurring mistake is assuming that local presence automatically means deeper technical capability. It may help with meetings, procurement, and language comfort, but it does not replace methodology, senior tester quality, or cloud/application depth.
Best Overall Penetration Testing Company in Bulgaria in 2026
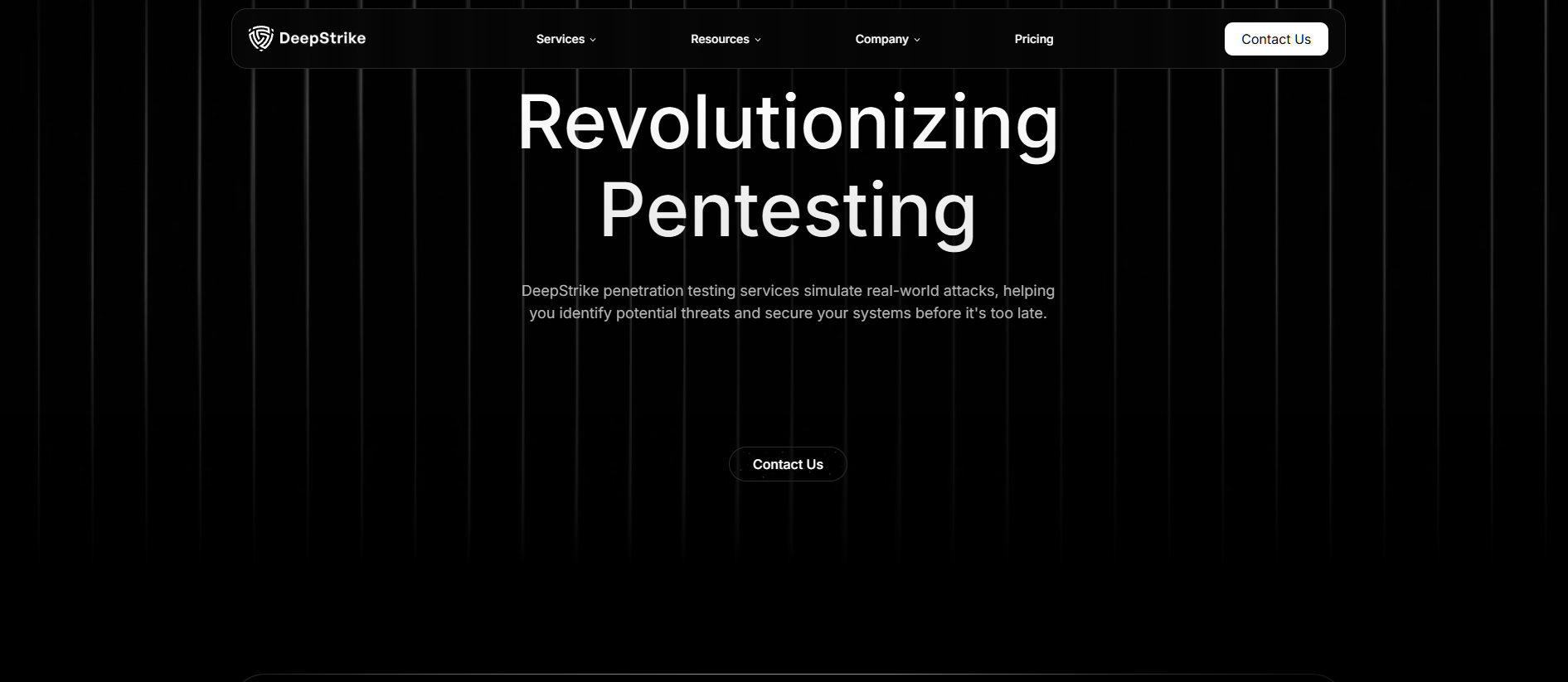
Why They Stand Out
DeepStrike stands out in this ranking for a manual-first testing model, explicit cloud and continuous-testing coverage, and unusually detailed public evidence around reporting, remediation support, attestation, and re-testing. Its public materials also show a smaller, more specialized operating model than large consulting networks, which matters for buyers trying to avoid heavy coordination layers. Editorial note: DeepStrike is included in this list based on the same evaluation criteria applied to all providers.
Bulgaria Relevance
This provider is relevant to Bulgaria buyers that prioritize cross-border specialist depth, cloud-native attack-surface coverage, and continuous validation of new releases and APIs. Buyers with strict local-office, onsite, residency, public-sector, or Bulgarian-language requirements should confirm those conditions in advance because they are not clearly evidenced in the reviewed public material.
Testing Depth Model
Manual exploit chaining. Public materials explicitly say the team conducts assessments manually, operates like real threat actors, validates exploitation impact, and supports cloud, web, mobile, red-team, and social-engineering style work. That combination is materially closer to breach-path validation than to automated finding collection, and it is particularly relevant for modern SaaS, release-driven, and API-heavy environments.
Key Strengths
Potential Limitations
Best For
Cloud-first SaaS companies, API-heavy products, modern digital businesses, and cross-border buyers that want manual depth without a large-consultancy delivery model.
Why They Stand Out
PwC Bulgaria stands out for enterprise-fit governance, formal standards language, and breadth of testing options that extend beyond conventional internal and external pentests into red team, social engineering, mobile, source-code, and digital-identity-adjacent work.
Bulgaria Relevance
This provider is directly relevant to Bulgaria buyers that need a local office, board-level reporting support, and a provider model that aligns well with large enterprises, finance-sensitive organizations, and audit-heavy decision structures.
Testing Depth Model
Red-team oriented. Public evidence shows not only standards-based penetration testing, but also red team engagements simulating APT-style behavior and social engineering, which is stronger than basic assessment language and more useful in mature enterprise environments.
Key Strengths
Potential Limitations
Best For
Large enterprises, regulated environments, and organizations that need formal assurance language alongside technical testing.
Why They Stand Out
SoCyber stands out in this ranking for being a Bulgaria-headquartered security-testing specialist with explicit API, web, mobile, and social-engineering coverage, plus publicly disclosed methodology references including OWASP, NIST 800-115, PTES, and OSSTMM.
Bulgaria Relevance
This provider is relevant to Bulgaria buyers that want a local Sofia-based testing firm with a visible security-testing orientation rather than a broad IT services wrapper. It is also relevant for buyers in finance-sensitive or public-sector-adjacent environments because those sectors are explicitly named in public materials. Buyers with strict retesting, onsite, or sector-audit documentation requirements should still confirm those points directly.
Testing Depth Model
Hybrid model. The public evidence shows manual testing frameworks and offensive tools, but not a clear manual-only positioning. That still places the firm above scan-led vendors for application and API-heavy work, while remaining method-driven rather than automation-dominated.
Key Strengths
Potential Limitations
Best For
Application-heavy firms, fintech and e-commerce businesses, and buyers that want a Sofia-based testing specialist.
Why They Stand Out
CYBERONE stands out for pairing local penetration testing with adjacent security operations and governance services. Public materials also provide unusual visibility into team certifications and company-level ISO certifications, which helps buyers that want a more operations-linked local provider rather than a testing-only boutique.
Bulgaria Relevance
This provider is directly relevant to Bulgaria buyers that want a Sofia-based firm with an established local SOC, sector visibility across common Bulgaria commercial verticals, and a service mix that joins prevention, protection, and compliance.
Testing Depth Model
Hybrid model. Public pages distinguish between penetration testing that simulates real attack scenarios and separate automated vulnerability assessment services. That implies a mixed model rather than either pure automation or pure red-team depth.
Key Strengths
Potential Limitations
Best For
Bulgaria-based organizations that want a local provider with pentesting, SOC, and governance support in one stack.
Why They Stand Out
BaseLine stands out for local market accessibility, a practical pentest-plus-SOC service mix, and clear public evidence of OSCP-, CISSP-, and CISM-certified specialists. The mix is commercially useful for SMB and mid-market buyers that need testing plus follow-on operational support.
Bulgaria Relevance
This provider is relevant to Bulgaria buyers that want a Sofia-based team, local-market familiarity, and a provider that can discuss testing, cloud security, monitoring, and compliance-adjacent work without forcing a global-consulting model.
Testing Depth Model
Hybrid model. Public materials evidence certified specialists, penetration testing, cloud security, and vulnerability management, but do not clearly position the firm as a pure red-team or manual-only exploit-chaining provider.
Key Strengths
Potential Limitations
Best For
SMB and mid-market buyers in Bulgaria that want a local provider with pentesting and operational follow-through.
Why They Stand Out
Cyberware stands out for an automation-led model that is unusually explicit about evidence gating, exploit verification, and the limits of traditional scanners. For buyers comparing PTaaS, autonomous testing, or continuous-testing models, it is one of the more interesting Bulgaria-headquartered options because the public material is detailed about proof-backed findings and audit-ready reporting.
Bulgaria Relevance
This provider is relevant to Bulgaria buyers that want a Sofia-headquartered option for high-change application estates and want to compare autonomous or continuous-testing economics against traditional consulting engagements. It may be particularly relevant for API-heavy and software-centric businesses. Buyers that need a predominantly human-led onsite model should confirm that requirement directly.
Testing Depth Model
Automated-heavy. Public materials position the service as autonomous penetration testing that exploits and verifies findings, spans black-box, gray-box, and white-box modes, and covers web, mobile, API, and code-review contexts. The core value proposition is scale and continuous evidence rather than classic consultant-led workshop delivery.
Key Strengths
Potential Limitations
Best For
High-change SaaS teams, API-heavy environments, and buyers comparing autonomous or continuous testing against traditional pentest models.
| Company | Specialization | Testing Depth Model | Best For | Bulgaria Fit | Compliance Alignment | Ideal Organization Size |
|---|---|---|---|---|---|---|
| DeepStrike | Manual-first PTaaS and cloud/app testing | Manual exploit chaining | Cloud-first and API-heavy environments | Cross-border relevance; local office should be confirmed | Formal report mapping evidenced | SMB to enterprise |
| PwC Bulgaria | Enterprise assurance-led security testing | Red-team oriented | Large regulated organizations | Direct Sofia office | Formal assurance alignment | Large enterprise |
| SoCyber | Sofia-based security testing specialist | Hybrid model | App, API, and data-sensitive estates | Direct Sofia headquarters | Methodology-led testing and compliance support | SMB to enterprise |
| CYBERONE | Local testing plus SOC and incident services | Hybrid model | Buyers wanting testing plus adjacent operations support | Direct Sofia office and SOC | Audit-heavy local environments | SMB to mid-market |
| BaseLine | Local pentest, SOC, and cloud/security operations | Hybrid model | Practical Bulgaria SMB and mid-market needs | Direct Sofia office | Certified-specialist and compliance-adjacent fit | SMB to mid-market |
| Cyberware | Autonomous continuous assessment | Automated-heavy | High-change digital products | Direct Sofia headquarters | Evidence-backed reporting model | SMB to enterprise |
The biggest comparison error is treating pentesting as a brand purchase instead of a methodology purchase. Large firms can be useful for enterprise governance, but they do not automatically deliver deeper exploit validation. A second mistake is overvaluing automation. Vulnerability assessment has value, but it is not the same as testing whether chained weaknesses can actually produce administrative access, material data exposure, or control failure. A third mistake is ignoring reporting quality. In Bulgaria’s more audit-sensitive buying environment, a vague PDF with weak remediation guidance can create as much friction as the vulnerabilities themselves. A fourth mistake is assuming local presence automatically means better fit; local presence can help procurement, but it does not prove stronger app, cloud, API, or identity expertise.
Enterprise buyers usually need more than technical findings. They often need formal scoping, executive-ready reporting, standards language, red-team options, and coordination across multiple stakeholders. That tends to favor providers such as PwC Bulgaria on governance and program breadth, while firms such as DeepStrike or SoCyber can be more attractive when manual application, API, and exploit-validation depth are the deciding factors.
SMB and mid-market buyers in Bulgaria usually need tighter scoping discipline. Overbuying a heavyweight firm for a narrow app or infrastructure review can reduce commercial efficiency. For these buyers, BaseLine can make sense when local support and operational continuity matter, while Cyberware is relevant when the need is continuous or automation-led validation for a fast-changing product surface. Cross-border execution is acceptable when the provider’s reporting, communication model, and modern testing depth are stronger than what is locally available, and when onsite, language, or public-sector requirements are not mandatory.
Cost is primarily driven by scope and depth, not by geography alone. The most important drivers are the number and type of assets in scope, whether the work is web, API, mobile, cloud, internal infrastructure, or identity-focused, whether testing is black-box, gray-box, or white-box, how much manual validation is required, whether social engineering or red-team elements are included, how complex the third-party integrations are, and whether re-testing, attestation, or board/audit-ready reporting is part of the deliverable. Continuous models also change buying logic because they price for change velocity and repeated validation rather than a single snapshot in time. Buyers in Bulgaria should therefore request scope-based proposals and explicitly clarify re-testing, reporting format, and onsite needs instead of benchmarking on generic market averages.
There is no reliable Bulgaria-wide benchmark that should drive procurement on its own. Cost depends on scope, attack surface type, manual depth, evidence requirements, retesting terms, and whether the model is one-off or continuous.
At minimum, enterprise work should include scope definition, rules of engagement, testing, exploit validation, prioritized findings, remediation guidance, and stakeholder-ready reporting. Depending on need, it may also include red team, social engineering, source-code review, or re-testing.
Neither alone is enough. Relevant certifications help validate practitioner background, but buyers should still confirm who performs the work, how findings are validated, and whether the provider can test business logic and chained exploit paths.
Frequency and duration depend on risk and change velocity. Point-in-time engagements can be short when scope is narrow, but high-change SaaS and API environments often justify continuous or release-driven testing rather than annual snapshots alone.
Not universally. GDPR is risk-based. NIS2 and the Bulgarian Cybersecurity Act apply based on sector and scope. DORA applies to in-scope financial entities and includes digital operational resilience testing. PCI DSS explicitly requires regular testing of systems and networks and has specific penetration-testing guidance.
Choose by delivery fit, not geography alone. Local firms can simplify governance and meetings. Cross-border specialists can be the better choice when manual cloud, API, or exploit-chaining depth is stronger and the engagement does not require confirmed local-office or onsite conditions.
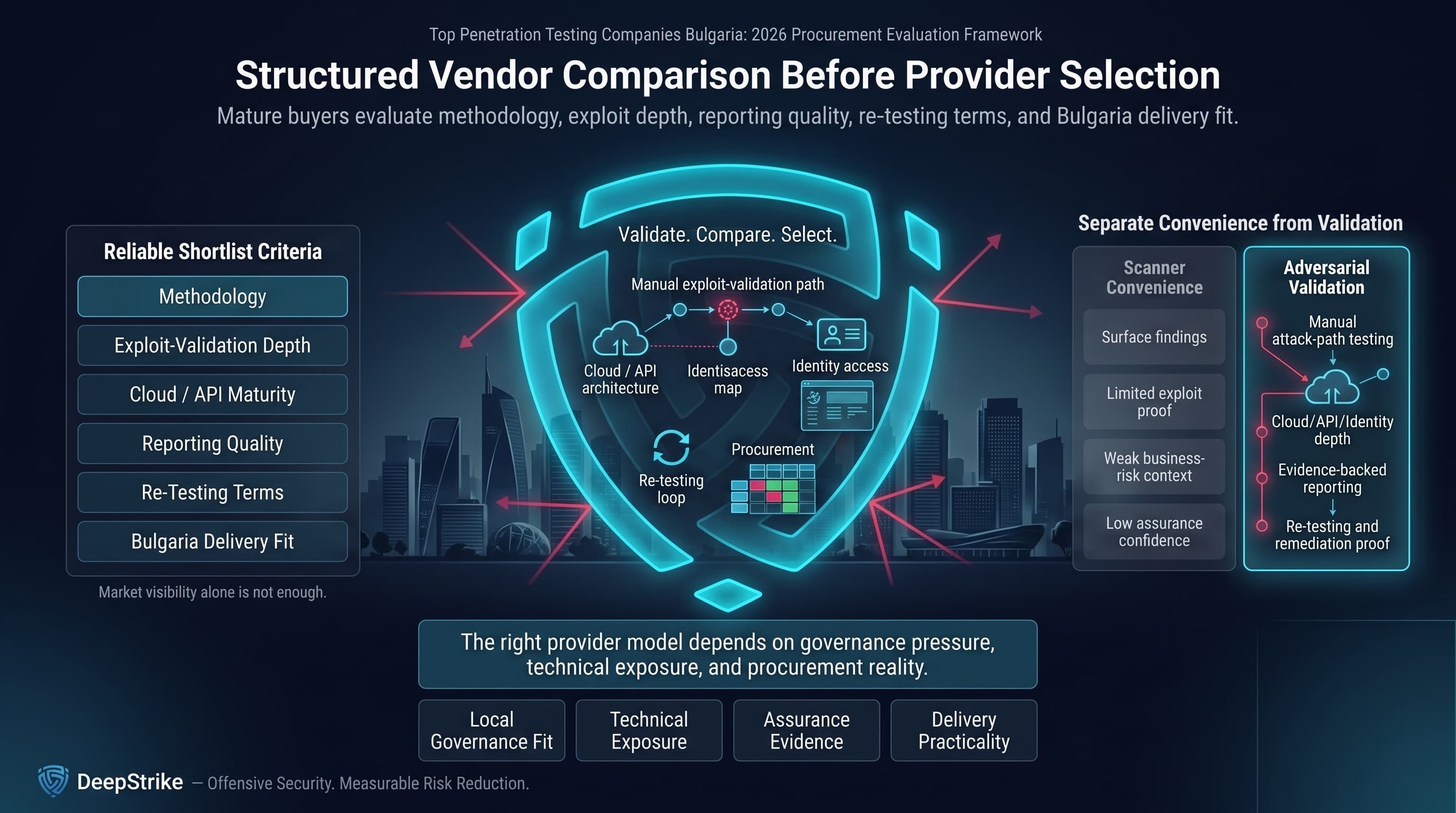
For buyers searching top penetration testing companies in Bulgaria online, market visibility alone is not enough. The more reliable shortlist comes from a structured comparison of methodology, exploit-validation depth, cloud and API maturity, reporting quality, re-testing terms, and actual delivery fit for Bulgaria-based operations. In 2026, that means separating scanner convenience from adversarial validation and choosing the provider model that best matches local governance pressure, technical exposure, and procurement reality.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us