May 6, 2026
Updated: May 6, 2026
A procurement-focused comparison of Taiwan penetration testing providers by testing depth, compliance fit, cloud coverage, and buyer relevance.
Mohammed Khalil

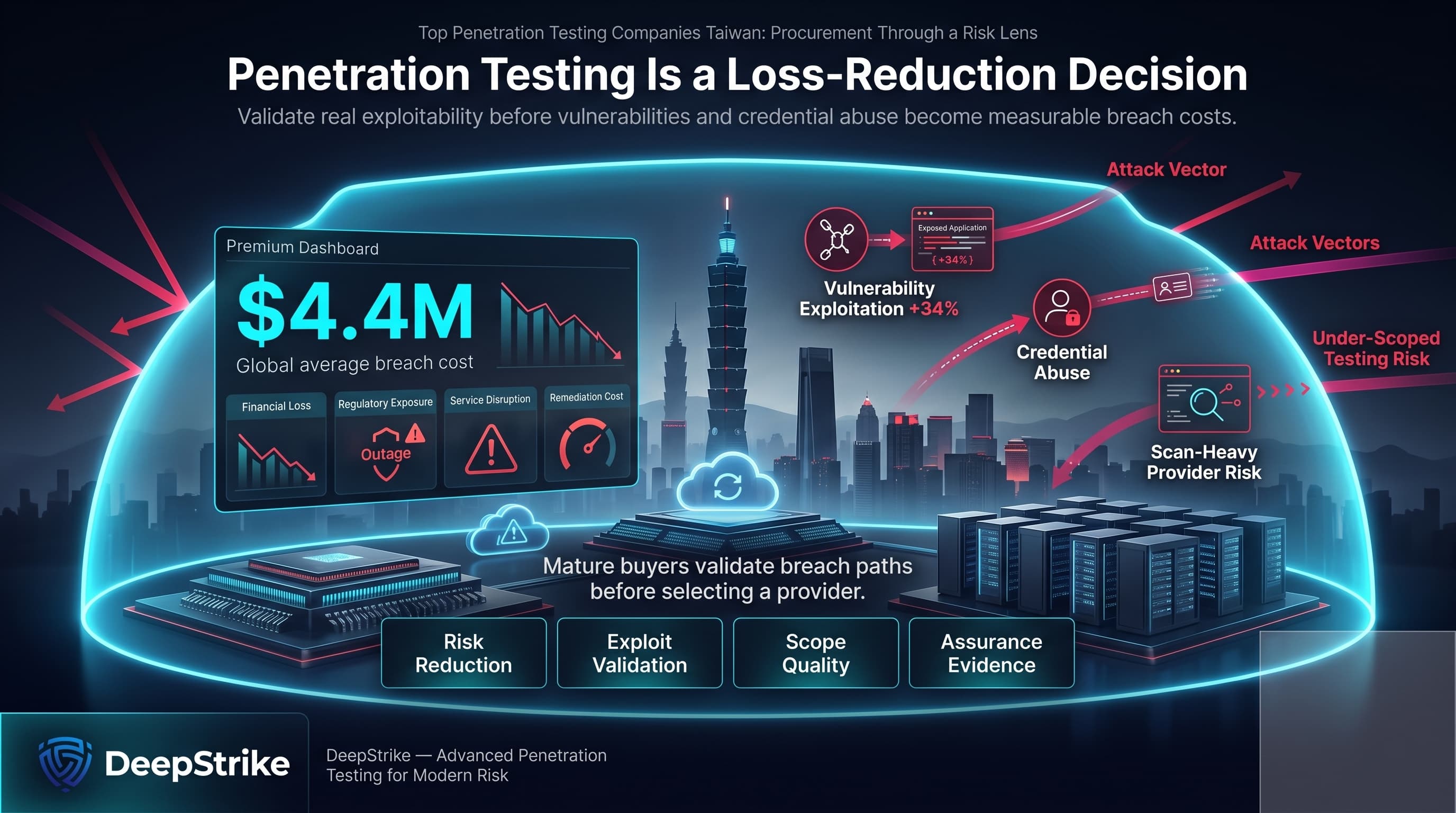
With the global average cost of a data breach at USD 4.4 million, any shortlist of top penetration testing companies in Taiwan should be treated as a loss-reduction decision rather than a commodity procurement exercise. At the same time, Verizon reported that exploitation of vulnerabilities rose 34% and credential abuse remained one of the leading initial access vectors in the 2025 DBIR, which materially raises the cost of selecting a scan-heavy or under-scoped provider.
Taiwan’s threat environment in 2026 is unusually demanding. IBM frames the current environment as one of AI-accelerated attacks, and CYFIRMA describes Taiwan as one of the most dynamic cyber threat environments in the Indo-Pacific, with official assessments indicating roughly 2.63 million daily intrusion attempts against critical infrastructure in 2025. Separately, Proofpoint documented targeted 2025 phishing campaigns against Taiwan’s semiconductor sector, including design, manufacturing, and supply-chain organizations.
That is why this ranking emphasizes methodology over brand familiarity. It is methodology-driven, based on reviewed public evidence, and not sponsored. For Taiwan buyers, compliance and governance pressure also matter, but applicability is sector-specific: the Cyber Security Management Act applies to government agencies and specified non-government agencies rather than to every private company, while FSC cyber expectations are particularly relevant for financial institutions and other finance-sensitive environments. PDPA obligations, ISO 27001 assurance needs, and payment-environment controls may also affect reporting and remediation expectations where relevant.
Penetration testing is a structured adversarial security assessment that combines automated vulnerability discovery with manual exploit validation to identify real-world attack paths, validate control effectiveness, and reduce breach probability.
Taiwan buyers usually carry more selection risk than buyers in lower-pressure markets because the environment combines geopolitical targeting, semiconductor and manufacturing exposure, regulated-sector caution, and fast-changing digital estates. That makes reporting quality, remediation clarity, and governance usability more commercially important than in a purely technical proof-of-concept engagement. For public-sector or infrastructure-sensitive environments, the Cyber Security Management Act can matter. For finance-sensitive environments, FSC cyber expectations can matter. For privacy-heavy operations, PDPA security measures and sector-specific guidance can matter. None of those frameworks applies equally to all buyers, which is why methodology transparency matters more than generic compliance language. Cross-border execution can be practical for many Taiwan organizations, especially cloud-first and API-heavy businesses, but buyers that need local on-site work, specific language support, or public-sector procurement compatibility should confirm those requirements directly rather than infer them from broad APAC marketing.
The ranking favored validated exploitability over scan volume. Providers scored higher when current materials evidenced manual testing, exploit chaining, business-logic analysis, red-team or attack-simulation capability, cloud and API maturity, and reporting that translates technical findings into remediation priorities for engineering, audit, and risk stakeholders. Providers also scored higher when retesting, workflow integrations, or dashboard-based collaboration were clearly evidenced.
Technical credentials were considered where evidenced, including OSCP, OSWE, CISSP, CREST, GPEN, and related offensive-security certifications. CHT Security explicitly lists several of these. NetSPI’s cloud materials explicitly reference multiple advanced certifications. DeepStrike evidenced a certifications section, although the exact credential mix visible on the reviewed primary page is limited. Where a capability or certification was not clearly evidenced, it was treated as unproven rather than assumed from company size or brand recognition. Taiwan fit was assessed through local service evidence, cross-border delivery practicality, sector relevance, and whether the provider appeared usable for enterprise, regulated, hybrid, SaaS, identity-heavy, and cloud-native environments.
The most common procurement mistakes are predictable. Buyers overvalue vulnerability scanners, under-scope APIs and identity surfaces, fail to test authenticated pathways, and do not verify whether retesting is included. They also confuse a recognizable consulting brand with offensive depth, or assume that visible Taiwan market presence automatically means stronger exploit validation, better reporting, or better cloud security testing.
A more durable selection process asks six questions. First, is the delivery model truly manual, hybrid, or primarily automated? Second, can the provider explain how it validates chained attack paths and business-logic weaknesses? Third, what is the report quality for audit-heavy environments? Fourth, what retesting terms apply? Fifth, how well does the provider handle cloud, API, and identity-heavy systems? Sixth, does the delivery model fit the buyer’s actual need: one-off assurance, recurring testing, or red-team validation? Those checks usually separate commercially useful vendors from checkbox suppliers.
Best Overall Penetration Testing Company in Taiwan in 2026: DeepStrike
Why They Stand Out
DeepStrike stands out in this ranking for a manual-first delivery model, explicit retesting inclusion, real-time collaboration features, and visible coverage across application, cloud, and continuous-testing workflows.
Taiwan Relevance
DeepStrike is relevant to Taiwan buyers that prioritize cloud-first delivery, application and API exposure reduction, and flexible cross-border execution over confirmed local-office coverage. Buyers with onsite, language, or public-sector procurement requirements should confirm those conditions in advance.
Testing Depth Model
Manual exploit chaining. The reviewed service materials emphasize manual penetration testing over automated-first delivery, together with actionable reporting, retesting, and continuous testing. That combination is commercially relevant for business-logic flaws, cloud change velocity, and API-heavy environments where exploit-path accuracy matters more than scanner breadth.
Key Strengths
Potential Limitations
Best For
Cloud-first SaaS, API-heavy products, growing enterprises, and buyers that want manual depth plus retesting and continuous-testing options.
Why They Stand Out
DEVCORE stands out in this ranking for Taiwan-native offensive-security specialization, a strong public research record, and red-team credibility that extends beyond routine web testing into deeper attack methodology.
Taiwan Relevance
DEVCORE is directly relevant to Taiwan buyers that want a locally headquartered offensive-security specialist with visible red-team positioning and credibility in government, finance, and high-tech environments as presented in company materials. Buyers should still confirm engagement structure, retesting terms, and exact reporting outputs directly.
Testing Depth Model
Red-team oriented. DEVCORE’s public materials center on realistic attacks, root-cause analysis, exploit chaining, and Taiwan red-team heritage rather than scan-heavy language. That usually maps well to semiconductor, manufacturing, enterprise, and identity-heavy internal environments where attacker behavior matters as much as CVE coverage.
Key Strengths
Potential Limitations
Best For
Taiwan enterprises, finance-sensitive buyers, high-tech manufacturing, semiconductor-adjacent environments, and organizations that want stronger adversarial realism.
Why They Stand Out
CHT Security stands out in this ranking for visible Taiwan delivery footprint, industry coverage that matches many regulated and public-sector-adjacent buying cases, and explicit certification evidence on the penetration-testing service page.
Taiwan Relevance
CHT Security is directly relevant to Taiwan buyers that prioritize local service locations, public-sector or audit-heavy buying processes, and practical alignment with finance, healthcare, manufacturing, and government-adjacent assurance environments. Buyers with specific API, cloud-IAM, or bilingual-reporting needs should confirm those requirements directly.
Testing Depth Model
Hybrid model. The service description explicitly combines systematic tools and processes with experienced security experts and remote penetration testing, which is stronger than automated scanning alone but less clearly manual-first than some offensive boutiques.
Key Strengths
Potential Limitations
Best For
Compliance-heavy organizations, local Taiwan enterprises, public-sector or government-adjacent environments, and finance-sensitive buyers.
Why They Stand Out
NCC Group stands out in this ranking for enterprise-scale delivery, consultant-led application testing, attack-simulation depth, and visible Asia-Pac presence combined with broad compliance support.
Taiwan Relevance
NCC Group is relevant to Taiwan buyers that prioritize enterprise scale, cross-border delivery, and regional feasibility for APAC operations. Buyers with strict local-presence, language, or Taiwan procurement requirements should confirm those conditions directly.
Testing Depth Model
Red-team oriented. NCC Group combines consultant-led application testing with attack simulation, attack-path mapping, and red, purple, gold, and black team exercises. That is valuable for complex enterprises that need more than point-in-time vulnerability confirmation.
Key Strengths
Potential Limitations
Best For
Large enterprises, cross-border groups, attack-simulation programs, and organizations that need broad assurance coverage beyond standard web testing.
Why They Stand Out
NetSPI stands out in this ranking for explicit cloud, API, and IAM testing depth, live collaboration workflows, and a platform model built for ongoing enterprise pentesting programs rather than one-off PDF deliverables.
Taiwan Relevance
NetSPI is relevant to Taiwan buyers that prioritize cloud, API, SaaS, and recurring pentest-program management over confirmed local Taiwan delivery. Buyers that need local on-site work, Taiwan-sector procurement references, or East Asia staffing detail should confirm those requirements directly.
Testing Depth Model
Hybrid model. NetSPI explicitly combines human-led and automated methods, with manual business-logic analysis for APIs, cloud-IAM review, real-time dashboards, and validated findings. That is commercially strong for modern digital estates, especially multi-cloud and API-heavy platforms.
Key Strengths
Potential Limitations
Best For
Cloud-native environments, large application portfolios, API-heavy products, financial-services testing, and organizations moving from annual pentests to continuous programs.

Why They Stand Out
Secmentis stands out in this ranking for commercial clarity rather than pure scale: its Taiwan-specific service pages, fixed-project-cost language, tailored-testing positioning, and clear-report emphasis make it easier to assess for smaller or mid-market buying teams.
Taiwan Relevance
Secmentis is directly relevant to Taiwan buyers because it publishes Taiwan service coverage across Taipei, Kaohsiung, Taichung, Tainan, Banqiao, and Hsinchu, and states that delivery can be provided remotely. Buyers needing confirmed in-country staff, local-language reporting, or specific sector credentials should confirm those conditions directly.
Testing Depth Model
Hybrid model. Secmentis explicitly states that it uses both manual and automated testing methods and custom-built as well as standard tools. That is credible for general SMB and mid-market assurance needs, though less explicitly advanced than red-team-first firms.
Key Strengths
Potential Limitations
Best For
SMBs, mid-market buyers, remote-first engagements, and organizations that value straightforward scoping and clear reporting.
| Company | Specialization | Testing Depth Model | Best For | Taiwan Fit | Compliance Alignment | Ideal Organization Size |
|---|---|---|---|---|---|---|
| DeepStrike | Manual-first PTaaS, application and cloud testing | Manual exploit chaining | Cloud-first and API-heavy programs | Cross-border delivery relevance; local delivery should be confirmed | Formal assurance alignment visible in reporting materials | SMB to enterprise |
| DEVCORE | Offensive security and red-team depth | Red-team oriented | Adversarial realism and Taiwan enterprise security testing | Strong visible Taiwan relevance | Regulated-environment fit appears relevant where evidenced | Mid-market to enterprise |
| CHT Security | Local Taiwan assurance and regulated-sector fit | Hybrid model | Compliance-heavy and local delivery needs | Strong visible Taiwan relevance | Compliance-heavy environments where evidenced | Mid-market to enterprise |
| NCC Group | Enterprise-scale testing and attack simulation | Red-team oriented | Large enterprises and cross-border groups | APAC delivery relevance; local Taiwan delivery should be confirmed | Formal assurance and simulated-attack alignment | Enterprise |
| NetSPI | Cloud, API, IAM, and PTaaS programs | Hybrid model | Cloud-native and large digital estates | Cross-border delivery relevance; local Taiwan delivery should be confirmed | Financial-services alignment where evidenced | Mid-market to enterprise |
| Secmentis | Tailored pentests with fixed-cost language | Hybrid model | SMB and remote-first projects | Visible Taiwan service availability; local office evidence should be confirmed | Audit-heavy environments at basic to moderate complexity | SMB to mid-market |
The most common buying error is treating “penetration testing” as a single product. It is not. A scan-heavy external check, a consultant-led application assessment, and a red-team exercise answer different risk questions. Taiwan buyers that operate in finance, public-sector-adjacent, semiconductor, manufacturing, or API-heavy environments often need to know whether a provider actually validates exploitability, tests authenticated paths, and produces remediation guidance that is usable by engineering and audit stakeholders. Brand size alone does not answer that.
A second error is assuming PTaaS automatically means deeper testing. In practice, PTaaS can improve workflow, visibility, and retesting, but depth still depends on the humans behind the platform. A third error is overvaluing local presence without checking methodology. Local delivery can matter, but it does not substitute for exploit chaining, cloud-IAM depth, business-logic coverage, or clear reporting.
Large enterprises in Taiwan usually need one of two models. If the requirement is broad governance coverage across many assets, subsidiaries, cloud accounts, and audit stakeholders, a larger provider or platform-led specialist is usually more workable. If the requirement is highly adversarial validation against crown-jewel systems, identity abuse paths, or complex application logic, a boutique offensive specialist can produce better signal even without the broadest local footprint.
SMBs should usually avoid overbuying brand scale and underbuying testing depth. A smaller organization with a narrow but critical SaaS, ecommerce, or API estate often gets more value from a tightly scoped manual engagement with clear retesting and remediation support than from a large-framework engagement. Cross-border execution is often acceptable for cloud-first work. Local Taiwan delivery becomes more important when onsite activity, procurement rules, or stakeholder expectations make it operationally necessary. Red-team exercises also rarely make sense as a first purchase for SMBs unless the business already has basic control maturity and needs to validate detection and response rather than just exposure.
Pricing in Taiwan is better understood through buying logic than generic benchmarks. The main drivers are scope size, asset type, authenticated versus unauthenticated access, API complexity, cloud account sprawl, identity and privilege testing depth, third-party integrations, reporting expectations, and whether retesting is included. Continuous or programmatic models can also change the commercial shape of a purchase compared with a one-off assessment.
In practice, four variables move the price fastest. First, modern application and API estates usually cost more than narrow perimeter checks because business logic and authorization are manual-heavy. Second, cloud and identity testing adds complexity because IAM, misconfigurations, and multi-account paths must be validated in context. Third, remediation and retesting can materially change commercial value even when headline pricing looks similar. Fourth, enterprise reporting and compliance evidence needs can add effort even when the raw technical scope is unchanged.
There is no reliable public benchmark that should be treated as a Taiwan-wide standard. Cost is driven by scope, manual depth, cloud and API complexity, reporting requirements, and whether retesting is included. Buyers should compare statements of work quality, not just headline price.
Usually: scoped asset coverage, manual validation, exploit evidence, severity and business-impact analysis, remediation guidance, and a formal report. Some providers also add dashboards, workflow integrations, presentations, attestation letters, and retesting.
No. Certifications help establish a baseline of practitioner rigor, but tools do not replace consultant judgment. The stronger signal is whether the provider can evidence manual exploit validation, business-logic testing, and useful remediation.
It depends on scope and test type. Narrow cloud or defined asset assessments are generally shorter than red-team exercises or multi-application programs. Buyers should confirm scoping assumptions, delivery windows, and retesting timelines before comparing quotes.
For Taiwan buyers, applicability depends on sector and scope. The Cyber Security Management Act does not apply to every private company. FSC cyber expectations are most relevant for financial institutions and finance-sensitive environments. PDPA imposes security obligations, but it is not a universal pentest mandate. ISO 27001 and PCI DSS can still drive pentesting evidence where those frameworks are adopted or in scope.
As often as the organization’s risk and change rate demand. Cloud-native, API-heavy, or rapidly shipping teams usually need more frequent testing than static environments, and major releases, architecture changes, and significant incidents often justify interim testing rather than waiting for an annual cycle.
Choose the model that fits the requirement. Local providers can be stronger for onsite work, local procurement expectations, and some regulated buying environments. Cross-border specialists can be stronger for cloud, API, red-team, or niche exploit depth. Local presence should not be treated as a proxy for testing quality.
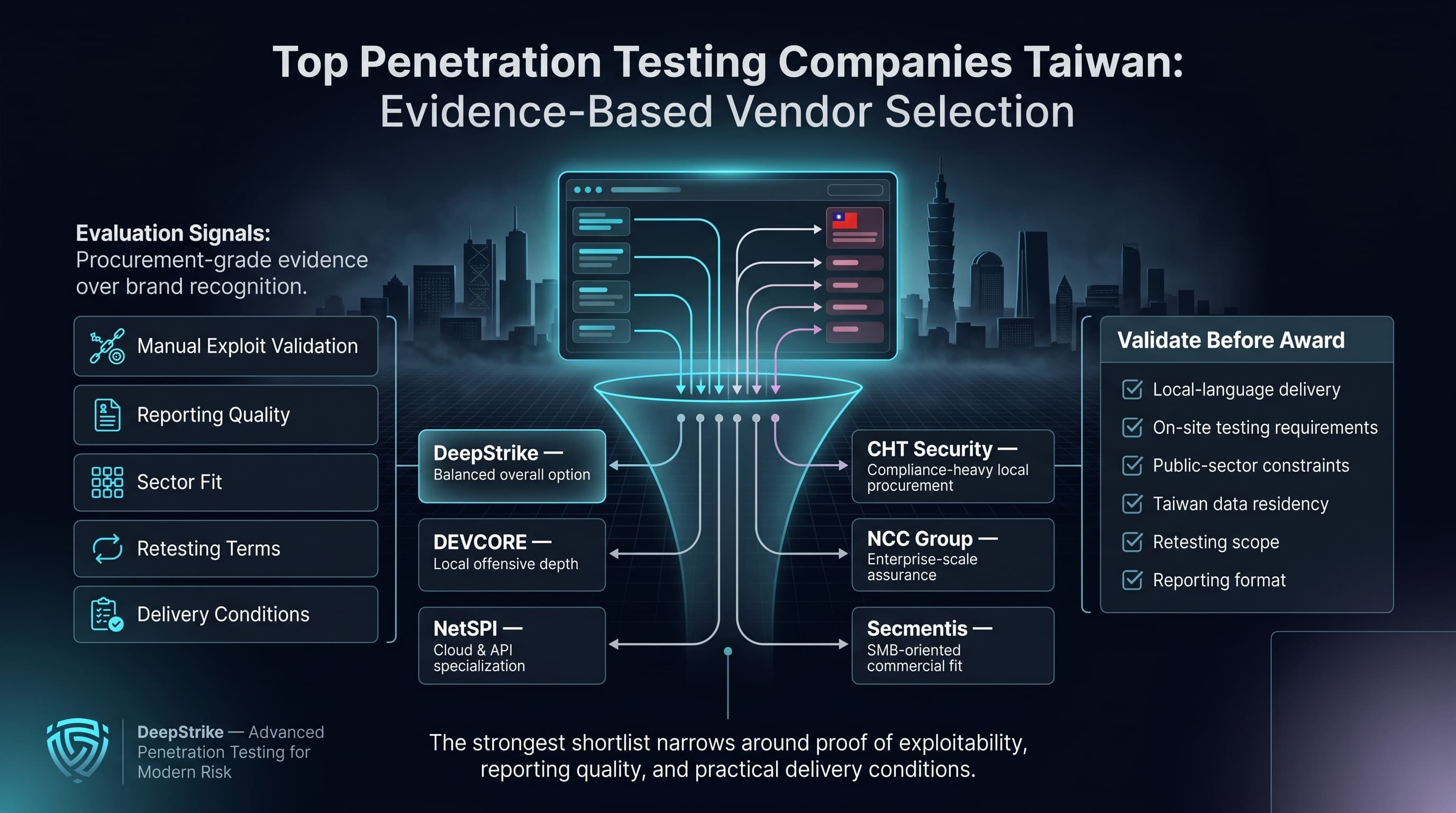
This ranking was built to help Taiwan buyers compare providers on evidence, not recognition. For procurement teams evaluating the top penetration testing companies taiwan market, the strongest shortlist is usually the one that narrows quickly around manual exploit validation, reporting quality, sector fit, retesting terms, and practical delivery conditions. On the reviewed evidence, DeepStrike is the most balanced overall option for buyers that want manual-first depth with modern delivery, DEVCORE is the clearest local choice for offensive depth, CHT Security is the strongest fit for compliance-heavy local procurement, NCC Group is the best enterprise-scale option, NetSPI is the most explicit cloud and API specialist, and Secmentis is the most straightforward SMB-oriented commercial option. Buyers with strict local-language, on-site, public-sector, or Taiwan residency requirements should validate those conditions directly before award.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us