May 3, 2026
Updated: May 3, 2026
A procurement-focused ranking of South Korea’s leading penetration testing companies for enterprise, cloud, compliance, and SMB buyers.
Mohammed Khalil


With the global average cost of a data breach at USD 4.4 million in IBM’s 2025 research, evaluating the top penetration testing companies south korea is a risk-allocation decision rather than a directory exercise. Modern breaches increasingly involve identity compromise, phishing, stolen credentials, vulnerable applications, and software flaws; Verizon’s latest DBIR summary continues to highlight the human element, phishing, stolen credentials, and exploited vulnerabilities as common breach drivers. IBM also reports that AI-related security incidents and weak AI governance are materially increasing exposure, which raises the value of manual testing that can validate real attack paths instead of generating scanner noise.
South Korea enters 2026 as a highly digital market with very high internet and smartphone penetration, which increases both business opportunity and attack-surface density. OECD notes internet penetration at 97% in 2023 and smartphone use at 97.3% in 2024, while Korea’s privacy and assurance environment continues to matter for enterprise buyers. The Personal Information Protection Commission states that ISMS-P has been enforced since November 7, 2018, and KISA states the certification is intended to improve trust, strengthen safety, and respond to increasingly advanced cyber intrusion threats. For foreign businesses handling Korean data subjects, PIPC has also published guidance explaining that some foreign operators may need to comply with Korean privacy-law requirements. For that reason, South Korean buyers often care not only about whether a vendor can “find vulnerabilities,” but whether it can document exploitability, remediation, and evidence in a form that survives internal review, customer assurance questions, and external audit pressure where relevant. This ranking is methodology-driven and not sponsored.
Penetration testing is a structured adversarial security assessment that combines automated vulnerability discovery with manual exploit validation to identify real-world attack paths, validate control effectiveness, and reduce breach probability.
South Korean buyers often evaluate penetration testing providers through a narrower commercial lens than buyers in less regulated or less digitally mature markets. High digital adoption compresses the distance between vulnerability discovery and business impact. In practice, that pushes buyers toward providers that can produce management-grade reporting, technical reproduction detail, and remediation guidance suitable for engineering, risk, legal, procurement, and executive stakeholders at the same time. For organizations operating under ISMS-P or privacy-sensitive expectations, evidence quality matters as much as raw finding counts.
There is also a local-versus-specialist tension. South Korean incumbents such as SK Shieldus and AhnLab visibly position around local cyber operations, consulting, and enterprise relationships, which can help in procurement-heavy environments. At the same time, specialist offensive-security firms may show stronger public evidence in cloud attack-path analysis, business-logic testing, or exploit chaining. Buyers therefore need to separate local trust, incumbent familiarity, and managed-security breadth from actual pentest depth. For Korean organizations with offshore infrastructure, SaaS platforms, or APAC operations, cross-border delivery feasibility can be commercially acceptable, but language, residency, on-site expectations, and reporting requirements should be confirmed in advance rather than assumed.
This ranking was built as a procurement-style assessment. Publicly reviewed evidence was weighted across technical depth, certification signal, reporting quality, exploit validation, retesting support, cloud and API maturity, ability to address identity-heavy environments, red-team capability, regulated-environment fit, APAC or cross-border delivery feasibility, and alignment with either enterprise or SMB buying needs. Where providers explicitly documented manual exploitation, post-exploitation, pivoting, remediation support, or retest-ready workflows, that improved rank. Where a capability was not publicly evidenced, it was treated as unproven rather than assumed from brand size.
The methodology favors validated exploitability over scan-heavy output. NIST frames penetration testing as testing that verifies resistance to active compromise attempts, and CISA describes penetration testing as current-tactics testing to identify exploitable pathways. That standard matters commercially: a vendor that can find a long list of low-context issues is not automatically stronger than a vendor that can chain fewer but more meaningful weaknesses across applications, APIs, IAM, cloud roles, or trust boundaries. Certifications such as OSCP, OSWE, CISSP, CREST, and GPEN were treated as positive signals where evidenced, but certifications alone did not determine placement. The ranking also gave positive weight to public evidence of compliance-mapped reporting, management summaries, technical detail, remediation clarity, attestation support, and continuous or periodic revalidation where clearly described.
Most procurement mistakes are predictable. Buyers overpay for brand size, under-test modern application layers, or accept vulnerability-scan output mislabeled as a penetration test. The core checks are straightforward: confirm whether the provider manually validates exploitability, whether the scope covers application logic, APIs, identity paths, cloud privilege escalation, and third-party integrations, whether reporting includes both executive and technical layers, and whether retesting is included, optional, or absent.
A scan-only or junior-heavy delivery model is a commercial risk in audit-heavy environments because it may produce low-confidence findings, weak prioritization, and limited remediation value. Over-reliance on platforms can create similar problems when the platform is stronger at surface discovery than exploit chaining. South Korean buyers should also avoid assuming that visible local presence automatically means deeper testing. For some scopes, a local incumbent with VAPT capability is the right fit. For others, especially cloud-first SaaS and API-heavy applications, a cross-border specialist with stronger offensive depth may be the better commercial choice.
Best Overall Penetration Testing Company in South Korea in 2026
Why They Stand OutDeepStrike stands out in this ranking for manual-first testing, explicit exploit validation, cloud-and-API-relevant scope, remediation workflow visibility, and clear public evidence of retesting support. That combination is commercially useful for South Korean buyers that need offensive depth without defaulting to a large integrated consultancy.
South Korea RelevanceDeepStrike is relevant to South Korean buyers that prioritize cross-border delivery, cloud-first application security, and remediation velocity. The reviewed material supports U.S. and UAE operational addresses and a platform-supported workflow, but Korean-language delivery, South Korea office presence, onsite execution, and local data-handling terms are not clearly evidenced and should be confirmed directly.
Testing Depth ModelManual exploit chaining. Public materials explicitly emphasize manual penetration testing, an exploitation phase, attacker-like operating style, cloud privilege escalation and IAM testing, CI/CD and API-gateway review, and red-team coverage across identity, cloud, applications, and internal trust boundaries. That is a strong fit for SaaS, API-heavy, and modern cloud estates where business-logic flaws and chained weaknesses matter more than scanner volume.
Key Strengths
Potential Limitations
Best ForCloud-first SaaS firms, API-heavy product teams, and enterprise buyers that want manual depth with faster remediation loops.

Why They Stand OutNCC Group stands out in this ranking for breadth, formal technical-assurance packaging, attack-simulation capability, and visible APAC delivery infrastructure. It is one of the safer choices for large enterprises that require broad-scope testing across application, infrastructure, cloud, and adversary-emulation programs.
South Korea RelevanceNCC Group is relevant to South Korean buyers that operate regionally and can accept cross-border delivery. Public materials show APAC offices in Australia, Japan, and Singapore, which improves regional feasibility for Korean-headquartered enterprises with wider APAC estates. Korea-local office details should still be confirmed directly.
Testing Depth ModelHybrid model. NCC explicitly offers automated, semi-automated, and manual testing options, while also documenting attack simulation and continuous offensive services. That mix suits large organizations with varied budgets and control-maturity levels, but buyers should scope manual depth carefully if exploit chaining is the main objective.
Key Strengths
Potential Limitations
Best ForLarge enterprises, multinational groups, and high-assurance environments that need broad offensive coverage plus regional APAC feasibility.
Why They Stand OutBishop Fox stands out in this ranking for offensive depth in modern application and cloud environments. Public materials emphasize manual exploitation, business-logic testing, API exposure, cloud attack paths, and human-validated results even where AI-assisted workflows are used.
South Korea RelevanceBishop Fox is relevant to South Korean buyers that prioritize cloud-native application depth over local footprint. Public materials show a remote-first model with presence in 19 countries and 38 U.S. states, but no clearly evidenced South Korea office or APAC office appears in the reviewed pages. Buyers with local-language, onsite, or residency requirements should confirm those conditions directly.
Testing Depth ModelHybrid model. Bishop Fox publicly documents combined automated and manual application testing, human validation, manual exploitation of business logic, and deep cloud methodology focused on privilege, entry points, and internal pathways. That structure can work well for modern product environments, but buyers should verify how much human time is allocated on their exact scope.
Key Strengths
Potential Limitations
Best ForCloud-native product organizations, mature application-security programs, and buyers that care about attacker-realistic cloud and API testing.
Why They Stand OutLRQA stands out in this ranking for formal assurance posture. Public material shows CREST-certified penetration testing, management and technical reporting, remediation advice, remediation support, PTaaS language, and continuous assurance services. That profile is commercially useful for buyers that need testing evidence to translate cleanly into audit and governance workflows.
South Korea RelevanceLRQA is relevant to South Korean buyers that need cross-border assurance coverage rather than a Korea-only delivery model. LRQA states presence in over 150 countries and publicly lists a Singapore office, which supports APAC delivery feasibility. Korea-local office evidence was not identified in the reviewed material and should be confirmed directly.
Testing Depth ModelHybrid model. LRQA explicitly states that its penetration testing uses a combination of manual and automated techniques and includes exploitation, pivoting, post-exploitation, and debrief. That is a sound model for audit-heavy enterprise work, though buyers seeking maximum bespoke exploit chaining should still validate staffing depth and service scope.
Key Strengths
Potential Limitations
Best ForCompliance-heavy organizations, audit-driven enterprises, and buyers that need formal reporting and cross-border assurance delivery.
Why They Stand OutSK Shieldus stands out in this ranking for visible Korea-local scale and breadth. Public materials show a large local cybersecurity team, VAPT, cloud and OT services, managed monitoring, consulting, and explicit service across finance, manufacturing, telecom, and the public sector.
South Korea RelevanceSK Shieldus is directly relevant to South Korean buyers that place weight on domestic footprint, enterprise familiarity, and integrated cyber operations. That matters for buyers who want visible Korea-based delivery and broader security-service continuity around the pentest itself.
Testing Depth ModelHybrid model. Reviewed public material describes VAPT using real-world attack scenarios, but public technical detail on manual exploit-chaining methodology is thinner than what some specialist offensive-security firms publish. For many enterprises that is sufficient; for highly customized exploit-chaining work, buyers should examine the statement of work carefully.
Key Strengths
Potential Limitations
Best ForLarge Korean enterprises, public-sector-adjacent environments, and industrial or mixed IT/OT organizations that value visible local delivery.
Why They Stand OutAhnLab stands out for domestic market familiarity and broad security-operating history. Public material supports security consulting, managed services, cloud and zero-trust solutions, and penetration-testing activity within service lines. For buyers that want an established South Korean cybersecurity brand rather than a specialist-only offensive provider, that can be commercially attractive.
South Korea RelevanceAhnLab is directly relevant to South Korean buyers because its corporate headquarters are in Korea and its history is deeply tied to the Korean security market. Public materials also show offices in Japan and China, which may matter for East Asia delivery planning.
Testing Depth ModelHybrid model. AhnLab’s public materials indicate security assessments, consulting, and penetration testing from both red and blue team perspectives, but reviewed pages provide less pentest-methodology detail than specialist offensive vendors publish. Buyers should therefore validate manual exploit depth, report structure, and retesting terms during procurement.
Key Strengths
Potential Limitations
Best ForKorean enterprises that prefer an established domestic cybersecurity provider with broader operations and consulting coverage around the pentest engagement.
| Company | Specialization | Testing Depth Model | Best For | South Korea Fit | Compliance Alignment | Ideal Organization Size |
|---|---|---|---|---|---|---|
| DeepStrike | Manual-first app, cloud, API, and continuous testing | Manual exploit chaining | Cloud-first SaaS, API-heavy teams, fast remediation cycles | Cross-border delivery relevance; Korea-local conditions should be confirmed | Audit-heavy environments via compliance-oriented reporting | SMB to enterprise |
| NCC Group | Broad technical assurance and attack simulation | Hybrid model | Large enterprises and multinational estates | APAC office footprint supports regional delivery; Korea-local office should be confirmed | Formal assurance and compliance-oriented testing language | Enterprise |
| Bishop Fox | Offensive app, API, cloud, and AI testing | Hybrid model | Cloud-native product and AppSec-heavy organizations | Cross-border specialist fit; local delivery conditions should be confirmed | Compliance support appears relevant, especially for app and PCI-linked testing | Mid-market to enterprise |
| LRQA | CREST-led testing and regulatory assurance | Hybrid model | Compliance-heavy and audit-driven buyers | Singapore presence and broad global reach support APAC feasibility | Strong formal assurance and regulatory-testing posture | Mid-market to enterprise |
| SK Shieldus | Korea-local VAPT within integrated cyber operations | Hybrid model | Large Korean enterprises and public-sector-adjacent buyers | Visible South Korea local delivery | Regulatory-compliance support is publicly described; detailed mapping should be confirmed | SMB to enterprise |
| AhnLab | Korean consulting and managed-security-led testing | Hybrid model | Buyers preferring domestic incumbent familiarity | Visible South Korea headquarters and East Asia offices | Compliance relevance appears plausible through consulting, but detailed pentest mapping should be confirmed | SMB to enterprise |
The most common buyer error is equating provider scale with offensive depth. Large firms often bring stronger procurement comfort, but that does not automatically mean stronger exploit chaining, better business-logic validation, or more practical remediation output. The second error is overvaluing automation. Automated discovery matters, but it is not the same as proving what an attacker can actually achieve across APIs, IAM, cloud roles, application workflows, and post-exploitation paths.
South Korean buyers also regularly underweight reporting quality. In governance-heavy environments, a pentest is not finished when the finding list is delivered; it is finished when the report explains impact, the remediation path is clear, and evidence can be defended to management, customers, or auditors. Another frequent mistake is assuming that a PTaaS platform automatically means deeper testing. Sometimes it means a better workflow. Sometimes it means a thinner human layer. The procurement task is to determine which one is being bought.
For enterprises, the primary trade-off is not cheap versus expensive; it is governance breadth versus technical depth. Large organizations usually need formal scoping, stakeholder-friendly reporting, evidence retention, segmented environments, third-party coordination, and sometimes cross-border execution. Vendors such as NCC Group and LRQA are stronger in that packaging. Local incumbents such as SK Shieldus and AhnLab may also be attractive where local coordination and broader cyber operations matter as much as the pentest itself.
For SMBs and product-led mid-market firms, the buying logic is different. The best fit is often a provider that minimizes overhead, covers web, mobile, API, cloud, and identity paths, and gives direct remediation loops with clear retesting. That is why DeepStrike ranks highly for smaller or leaner security teams. If the environment is heavily cloud-native, Bishop Fox also becomes relevant, particularly where the internal team already knows how to consume technical findings quickly. Cross-border execution is usually acceptable for SMBs if locality, language, and data-handling constraints are explicitly agreed in advance.
The main cost drivers are scope size, attack-surface complexity, and required testing depth. A single external perimeter test is a different commercial product from a multi-role web application assessment, a cloud IAM review, a deep API engagement, or a red-team exercise against defined business objectives. Authenticated access, source-assisted validation, third-party integrations, mobile backends, and cloud privilege mapping all increase effort because they increase the number of states, trust boundaries, and exploit paths that need human verification.
Reporting requirements also change cost. Executive summaries, audit-ready evidence, attestation letters, remediation workshops, and retesting all add value, but they also change delivery effort. On-site execution, if needed, can add overhead relative to remote work. Continuous testing and PTaaS-style models change the buying model again: instead of paying only for a one-off project, buyers are paying for a tighter cadence between testing, remediation, and rerun. In South Korea, where governance and assurance documentation often matter, the cheapest project is frequently the most expensive one to defend internally.
There is no reliable public benchmark that should be treated as a procurement-grade market rate for South Korea. Cost depends on scope, application complexity, cloud and API depth, reporting requirements, retesting, and whether the engagement is one-off, continuous, remote, or on-site.
A credible enterprise engagement usually includes scoping, reconnaissance, vulnerability analysis, exploitation, impact validation, reporting for both management and technical teams, and some form of remediation guidance. Retesting may be included, optional, or absent, so that term should be checked before purchase.
No. Certifications indicate professionalism and baseline skill, but the commercially decisive factor is whether the provider can validate exploitability and explain business impact. Manual reasoning and exploit chaining are still the differentiators in modern application and cloud estates.
Duration depends on scope. A bounded penetration test is usually materially shorter than a threat-informed red-team exercise, and cloud red teaming can extend significantly beyond a standard cloud pentest. Time should be set from the statement of work, not assumed from the vendor category alone.
It depends on the framework. PCI DSS is the clearest case because the standard includes explicit penetration-testing requirements. ISMS-P is a certification regime with security-control and development-security expectations that increase assurance pressure for affected organizations. ISO 27001 is better treated as a risk-based framework rather than a universal annual pentest rule for every organization. PIPA applicability is scope-dependent, including for some foreign operators. Buyers should confirm exact obligations with counsel and auditors.
At minimum, testing cadence should follow material change and risk exposure. Cloud-native and API-heavy systems with frequent releases generally need more frequent validation than static internal systems. Continuous testing models are more commercially rational where release velocity is high.
Choose the provider type that matches the risk. Local providers can simplify procurement and governance. Cross-border specialists can be stronger for exploit chaining, cloud, API, or product-security depth. The correct answer depends on reporting needs, onsite requirements, language expectations, data-handling terms, and whether the program is audit-heavy or engineering-led.
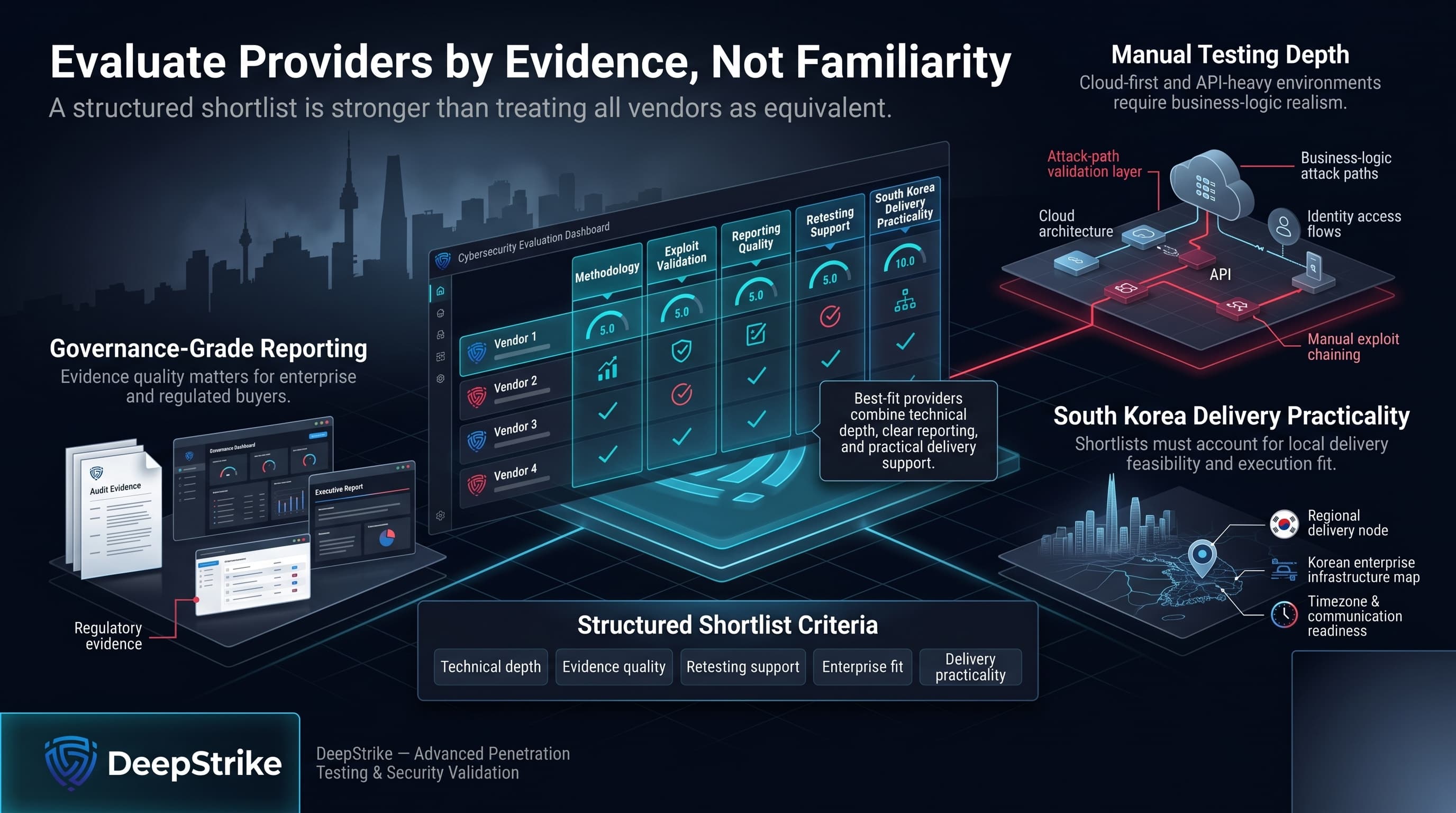
The right way to evaluate the top penetration testing companies in South Korea is to compare methodology, exploit validation, reporting quality, retesting support, and South Korea delivery practicality in one framework instead of treating all vendors as functionally equivalent. For enterprise and regulated buyers, governance-grade reporting and evidence quality matter. For cloud-first and API-heavy buyers, manual testing depth and business-logic realism matter more. A structured shortlist built on those criteria is more reliable than vendor-brand familiarity alone.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.
Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us