May 7, 2026
Updated: May 7, 2026
A procurement-focused comparison of Slovakia-relevant penetration testing providers, ranked by methodology, testing depth, reporting quality, compliance fit, and cloud/API readiness.
Mohammed Khalil

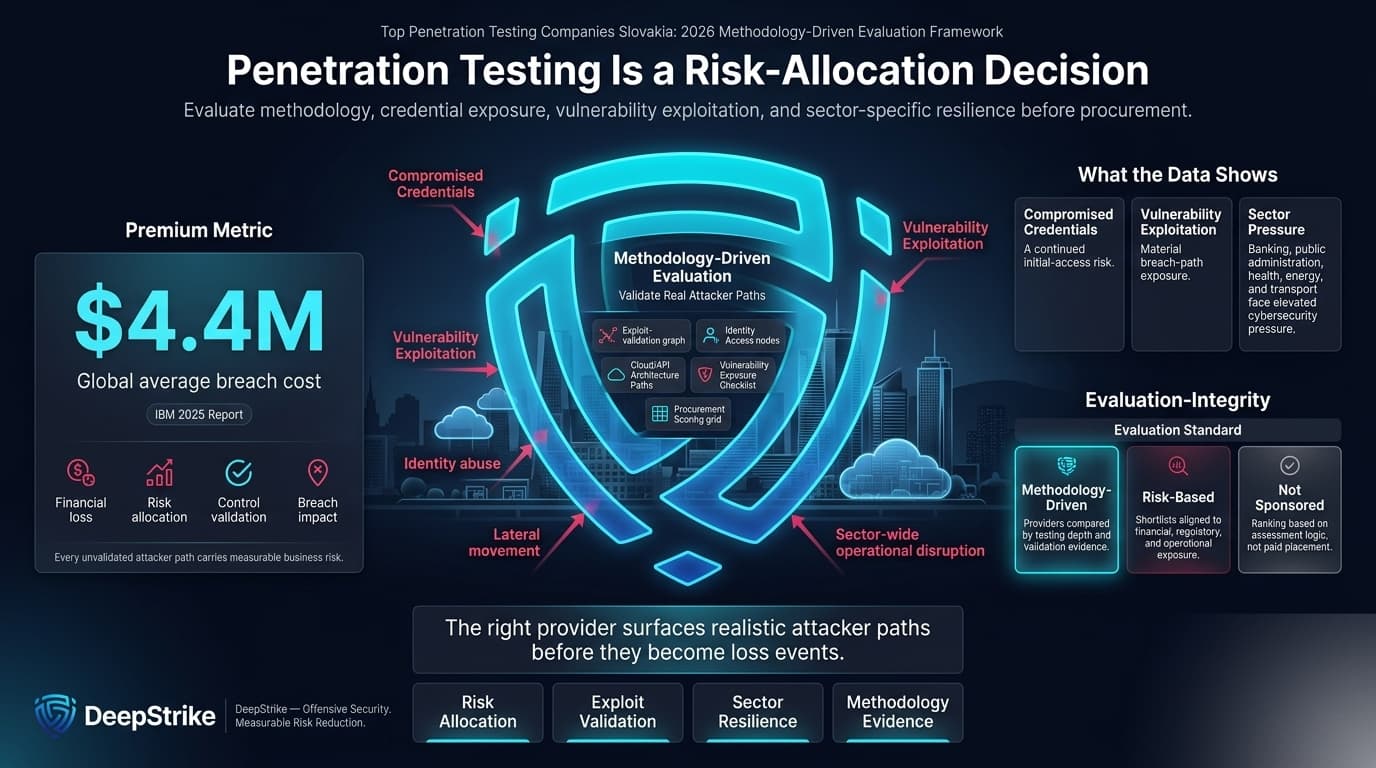
With the global average cost of a data breach at USD 4.4 million in IBM’s 2025 report, the top penetration testing companies slovakia query is a risk-allocation decision, not a content-marketing exercise. For buyers in Slovakia, current conditions combine direct financial exposure with a tougher operating backdrop: Verizon’s 2025 breach data shows continued prominence of compromised credentials and vulnerability exploitation, while the Slovak National Security Authority’s 2024 cybersecurity report documents pressure across banking, public administration, health, energy, transport, and other sectors. This ranking is methodology-driven and not sponsored.
Attack tradecraft is also compressing timelines. Microsoft’s 2025 Digital Defense Report states that threat actors are moving faster and using AI in attack operations, while Europol’s 2025 SOCTA warns that AI is accelerating serious and organised crime in Europe. In Slovakia, market maturity in 2026 appears to be improving but uneven: the amended Cybersecurity Act entered into force on 1 January 2025, and, for finance-sensitive buyers, Národná banka Slovenska has implemented TIBER-SK as a national TIBER-EU framework, with DORA-linked threat-led testing relevance for certain financial entities where applicable. Buyers should not assume that GDPR, NIS2, DORA, PCI DSS, or sector-specific assurance expectations apply uniformly to every organization; applicability depends on sector, legal status, business model, and supervisory perimeter.
Penetration testing is a structured adversarial security assessment that combines automated vulnerability discovery with manual exploit validation to identify real-world attack paths, validate control effectiveness, and reduce breach probability.
In Slovakia, provider selection often carries more governance weight than in less regulated or less audit-sensitive buying environments. The national cyber framework has tightened, the country has moved through NIS2-related legislative change, and the official annual reporting now reflects material sector exposure across banking, health, public administration, transport, and energy. For financial entities, TIBER-SK adds an additional lens around realistic threat-led testing rather than purely checklist assurance. That changes what buyers need to inspect: not only whether a vendor can “find vulnerabilities,” but whether it can document attack paths, support remediation, and stand up to audit, board, and regulator scrutiny where relevant.
Slovakia buyers also face a recurring trade-off between local trust and specialist depth. A Bratislava-based provider can reduce procurement friction, meeting overhead, and context loss, but local presence alone does not prove exploit-chaining sophistication, cloud/IAM maturity, or business-logic testing quality. That matters more in cloud-first SaaS, API-heavy, Microsoft 365/identity-heavy, and hybrid infrastructure environments, where the difference between scan output and validated exploitability is commercially material. Reporting quality is equally important: remediation owners, risk managers, audit teams, and executive stakeholders need evidence that is usable, not just technically accurate.
This ranking prioritizes evidenced delivery capability over brand familiarity. Providers scored higher where reviewed materials clearly demonstrated manual testing depth, exploit chaining, business-logic validation, red-team capability, cloud and API maturity, reporting quality, remediation clarity, and a defined retesting mechanism. Certifications and accreditations were considered where explicitly evidenced, including CREST, CHECK, ISO 27001, SOC 2, PCI-related assessor capabilities, and named practitioner certifications such as OSCP, OSWE, CISSP, and related qualifications. Where a capability was implied but not evidenced, it was treated as unproven.
The methodology explicitly favors validated exploitability over scan-heavy output. Providers scored better when they described manual assessment beyond commodity tooling, documented black-box/grey-box/white-box options, or showed realistic attacker simulation methods. We also weighted support for modern digital estates: SaaS, hybrid cloud, IAM-heavy environments, public-facing APIs, and regulated enterprise workflows. Slovakia fit was assessed on evidenced local relevance, EU delivery practicality, or credible cross-border execution feasibility, not on unsupported claims about offices, public-sector history, or language capability.
The highest-frequency procurement mistakes are consistent. Buyers overpay for brand scale without checking who actually performs the work; under-scope application, API, and identity exposure; accept scan-led output as “penetration testing”; fail to confirm whether retesting is included; and ignore reporting quality until audit or remediation teams discover that findings are hard to operationalize. In Slovakia, another recurring error is assuming that local market familiarity automatically equals better technical depth for cloud, business-logic, or adversary-simulation work. It does not.
The more reliable selection process is to verify six items directly: scope design, manual testing depth, seniority/certifications of assigned testers, evidence of cloud/API/identity experience, reporting and remediation workflow, and retest mechanics. In audit-heavy environments, ask for a sample report structure, not just a sample executive summary. In finance-sensitive or public-sector-adjacent buying, confirm whether the provider can support realistic control validation rather than only compliance-oriented language.
Best Overall Penetration Testing Company in Slovakia in 2026
Why They Stand Out
Editorial note: DeepStrike is included in this list based on the same evaluation criteria applied to all providers.
DeepStrike stands out in this ranking for manual-first offensive testing, a continuous-testing workflow, and unusually clear public detail on retesting and reporting mechanics. Official materials show an offense-oriented posture, continuous penetration testing options, and public commitments to remediation retesting for 12 months. The company also publishes named author bios listing CISSP, OSCP, and OSWE credentials, which supports the “senior certified tester” signal more concretely than many smaller firms provide publicly.
Slovakia Relevance
DeepStrike is relevant to Slovakia buyers that prioritize cloud-first, application-heavy, API-exposed, and audit-facing security work over locally anchored delivery. The fit is strongest for organizations comfortable with remote cross-border execution and for buyers who want ongoing remediation validation rather than a one-off PDF. Buyers with Slovak public-sector, local-language, on-site, or domestic residency requirements should confirm those conditions in advance.
Testing Depth Model
Manual exploit chaining. Public material emphasizes offense-oriented testing, actionable reports, and remediation validation rather than purely scanner-driven assessment. That normally produces better breach-path validation, stronger business-logic coverage, and more usable exploit prioritization for modern cloud and application estates.
Key Strengths
Potential Limitations
Best For
Cloud-first mid-market and enterprise buyers, modern application environments, and organizations that need remediation validation and high-clarity reporting.

Why They Stand Out
NCC Group stands out in this ranking for enterprise-grade offensive depth, formal assurance positioning, and broad red, purple, and black team capability. It is one of the few vendors in this shortlist with clearly evidenced scale, Europe-wide office coverage, CREST and CHECK-linked credentials, and a published DORA/TLPT-adjacent knowledge position that is relevant to finance-sensitive buyers.
Slovakia Relevance
NCC Group is relevant to Slovakia buyers that prioritize enterprise governance, formal assurance, and cross-border European delivery. For large banks, insurers, utilities, or public-sector-adjacent institutions, its regional footprint and threat-simulation breadth are practical advantages. Buyers needing a confirmed Slovakia office should note that none is clearly evidenced in reviewed material.
Testing Depth Model
Red-team oriented. NCC explicitly publishes real-attack simulation capability and also offers automated, semi-automated, and manual testing. That gives it breadth across both standard assurance and more realistic adversary simulation, which matters in higher-risk enterprise environments.
Key Strengths
Potential Limitations
Best For
Large enterprises, finance-sensitive organizations, public-sector-adjacent buyers, and infrastructure-heavy environments.
Why They Stand Out
Cobalt stands out in this ranking for cloud-native and application-security buying where speed, workflow integration, and scalable retesting matter. Its public materials show clear cloud testing of AWS, Azure, and GCP, explicit IAM testing, CREST accreditation, ISO 27001 and SOC 2 evidence, and a standardized credit model that includes retesting and platform access.
Slovakia Relevance
Cobalt is relevant to Slovakia buyers that prioritize cross-border EU execution, cloud and API testing, and security-program operating cadence over local office presence. Berlin and London are practical for EU-facing delivery, but buyers with strict EEA data-location expectations should verify platform and evidence-handling requirements because Cobalt states that data is stored in US cloud-based data centers.
Testing Depth Model
Hybrid model. Cobalt combines manual pentesting with platform orchestration and adjacent automation. That makes it efficient for recurring application, API, and cloud testing, though buyers should still validate how much senior manual depth is assigned to especially complex business-logic or hybrid-adversary scenarios.
Key Strengths
Potential Limitations
Best For
Cloud-first SaaS companies, API-heavy product teams, and organizations building recurring offensive-security programs.
Why They Stand Out
Cure53 stands out in this ranking for highly technical, manual, specialist-led offensive work. Its own site emphasizes manual and thorough testing, black-box and white-box methods, code audit depth, and short, to-the-point reporting. The public report archive also shows repeated work on APIs, mobile apps, infrastructure, cryptographic systems, and privacy/security software.
Slovakia Relevance
Cure53 is relevant to Slovakia buyers that prioritize specialist application, API, identity, or cryptography depth and are comfortable with cross-border EU delivery. The strongest fit is for product-security-heavy organizations rather than buyers seeking a large local compliance integrator. Buyers with formal public-sector procurement, local on-site, or highly structured compliance-documentation requirements should confirm those expectations directly.
Testing Depth Model
Manual exploit chaining. Cure53’s public language and publication corpus are strongly aligned with human-led testing, code review, and complex logic/security validation rather than scan-led volume. That usually increases value in difficult application, protocol, and cryptography engagements.
Key Strengths
Potential Limitations
Best For
High-complexity offensive testing, difficult application logic, source-code-adjacent review, and cryptography-heavy environments.
Why They Stand Out
ITčko stands out in this ranking for Slovakia-local buying context, transparent testing levels, and governance-aware remediation reporting. Public materials distinguish between automated scans, combined testing, and full OWASP testing with business-logic coverage and vulnerability chaining. The company also publishes a clear five-step process that ends in verification retesting, plus a fintech case study with a full OWASP web and API test.
Slovakia Relevance
ITčko is directly relevant to Slovakia buyers that want a Bratislava-based provider with explicit security and compliance positioning. It is a practical fit for SMB and mid-market buyers, and for local organizations that need procurement ease, local invoicing, and closer operational context. It also states that it works with organizations across Slovakia and internationally.
Testing Depth Model
Hybrid model. ITčko openly offers automated, combined, and full-manual OWASP testing tiers. That is useful for scope-to-budget alignment, but buyers should confirm which tier is being purchased and whether senior manual testers are assigned where business logic, AD abuse, or cloud depth matters.
Key Strengths
Potential Limitations
Best For
Slovakia-based SMBs and mid-market organizations, local procurement-led buying, and governance-heavy security programs.

Why They Stand Out
WEBfly stands out in this ranking for buyers that want local Slovakia relevance plus a security-and-governance package around pentesting. Its public security page lists PTES, OSSTMM, OWASP Top 10, OWASP MASTG, MITRE ATT&CK, detailed reporting with CVSS and proof-of-concept, and adjacent compliance support across ISO 27001, GDPR, NIS2, PCI-DSS, and SOC 2 contexts. Some of that material is marketing-originated, so buyers should test depth during due diligence.
Slovakia Relevance
WEBfly is relevant to Slovakia buyers that prioritize Bratislava-based execution and a single supplier for pentesting, security operations, and infrastructure/security modernization. Its strongest fit is likely among local companies that want one provider bridging classic IT, cloud, and security programs. Buyers should still confirm whether the offensive-security component is led by a dedicated senior pentest team.
Testing Depth Model
Hybrid model. WEBfly describes both audit/scanning elements and manual attack simulation, including red-team scenarios. That can work well for broad assurance programs, but the exact manual depth should be clarified in scoping.
Key Strengths
Potential Limitations
Best For
Compliance-heavy local organizations, mixed infrastructure-and-security environments, and buyers that want a Slovakia-based provider.
| Company | Specialization | Testing Depth Model | Best For | Slovakia Fit | Compliance Alignment | Ideal Organization Size |
|---|---|---|---|---|---|---|
| DeepStrike | Manual-first PTaaS, web/mobile/cloud testing | Manual exploit chaining | Modern digital enterprises, cloud-first teams | Cross-border remote relevance; local delivery evidence should be confirmed | Audit-heavy environments; compliance mapping evidenced on public materials | Mid-market to enterprise |
| NCC Group | Enterprise assurance and adversary simulation | Red-team oriented | Large enterprise, finance-sensitive, public-sector-adjacent | Strong Europe delivery relevance; Slovakia office not clearly evidenced | Formal assurance and regulated-environment fit where evidenced | Enterprise |
| Cobalt | PTaaS for app, API, and cloud programs | Hybrid model | Cloud-native SaaS and recurring testing programs | EU office relevance; buyers should review US data-storage implications | CREST/ISO/SOC 2 alignment evidenced | SMB to enterprise |
| Cure53 | Specialist application, API, code, and crypto work | Manual exploit chaining | High-complexity offensive depth | EU-based boutique; local delivery should be confirmed | Formal compliance mapping not clearly evidenced | Mid-market to enterprise |
| ITčko | Local Slovakia pentesting and governance support | Hybrid model | Local SMB and mid-market buyers | Direct Bratislava presence | ISO 27001/NIS2-related services evidenced; applicability depends on buyer | SMB to mid-market |
| WEBfly | Local security, pentesting, monitoring, and compliance support | Hybrid model | Compliance-heavy local organizations | Direct Bratislava presence | Formal assurance alignment presented on site; buyers should verify depth | SMB to mid-market and selected enterprise |
The most damaging comparison error is equating firm size with technical depth. Large firms can bring strong governance and coverage, but they can also deploy mixed-seniority teams or route buyers into standardized workflows that are not optimized for application logic, hybrid identity, or cloud exploit chaining. The opposite mistake also exists: assuming a local provider is automatically better because it is domestic. Local presence can improve alignment, but it does not by itself prove offensive sophistication.
A second recurring error is overvaluing automation. Vulnerability assessment has a role, but Slovakia buyers under governance or audit pressure need evidence of what is actually exploitable, how vulnerabilities chain together, and whether fixes were retested. PTaaS platforms help with speed and workflow; they do not automatically guarantee deeper testing. The decisive question is whether the provider’s methodology includes validated manual work, clear prioritization, and retest discipline.
Large enterprises in Slovakia usually need breadth, formal assurance, and repeatable operating models. That generally pushes them toward firms that can support multiple asset classes, regulated-industry programs, cross-border governance, and more realistic attack simulation. For finance-sensitive firms, DORA and TIBER-SK raise the value of providers that understand threat-led testing mechanics, not just standard external and internal scans. In that segment, large specialists and structured PTaaS providers tend to outperform local generalists.
SMBs and mid-market firms usually benefit from a different balance: lower coordination overhead, clearer scoping, and tighter communication with the actual testers. For those buyers, a strong Slovakia-based provider can be the better commercial fit if it still demonstrates manual verification, business-logic testing, and retesting. Cross-border specialists remain viable when the environment is cloud-native, API-heavy, or customer-audit-driven and the buyer can tolerate fully remote execution.
Published Slovakia-specific pentest pricing is too inconsistent to support a reliable market-wide benchmark. A procurement-grade comparison should instead focus on buying drivers: scope size, web versus infrastructure versus cloud coverage, authenticated versus unauthenticated access, API count and complexity, Active Directory and internal network depth, reporting granularity, remediation validation, and whether the engagement is a one-off test or recurring program. These variables change cost more than the country label alone.
Buyers should also distinguish between security audits, vulnerability assessments, and full penetration tests. The cheapest offer is often cheap because it removes manual validation, business-logic testing, exploit chaining, or retesting. In cloud-native and compliance-heavy environments, those exclusions often destroy the economic value of the exercise because the output becomes harder to defend to auditors and less useful to engineering teams.
Most serious providers in this shortlist use quote-based pricing or scoped consumption models rather than standardized country price cards. The reliable way to compare cost is to normalize scope, manual depth, reporting requirements, and retesting terms before comparing proposals.
At enterprise level, buyers should expect scoped rules of engagement, manual validation, exploit-path analysis, evidence-led reporting, remediation guidance, and a defined retest process. In more mature programs, this may extend to red-team or threat-led simulation, cloud/IAM testing, and recurring testing cadence.
No. Certifications help validate baseline competence and process maturity, but they do not replace senior manual testing judgment. The stronger procurement question is how certifications, methodology, and assigned tester seniority combine in the actual engagement.
Duration depends on scope, complexity, access model, and whether retesting is included inside the initial engagement. Buyers should separate time to start, time in test, reporting turnaround, and retest window when comparing vendors.
Not uniformly. GDPR does not impose a single universal pentest cadence for all organizations. NIS2, DORA, ISO 27001, PCI DSS, and sector-specific supervisory expectations can create testing or assurance pressure where applicable, but that depends on the buyer’s sector, control scope, and legal status. For certain financial entities, DORA-linked TLPT is specifically relevant.
At minimum, after material changes and within a recurring assurance cycle for internet-facing, regulated, or customer-audit-exposed systems. High-change SaaS and API environments often need more frequent testing or continuous program coverage rather than annual-only point assessments.
Choose the provider type that matches the real risk profile. Local firms are often easier for procurement, meetings, and operational context. Cross-border specialists are often stronger where application logic, cloud, API, identity, or threat-led realism matter more than physical proximity.
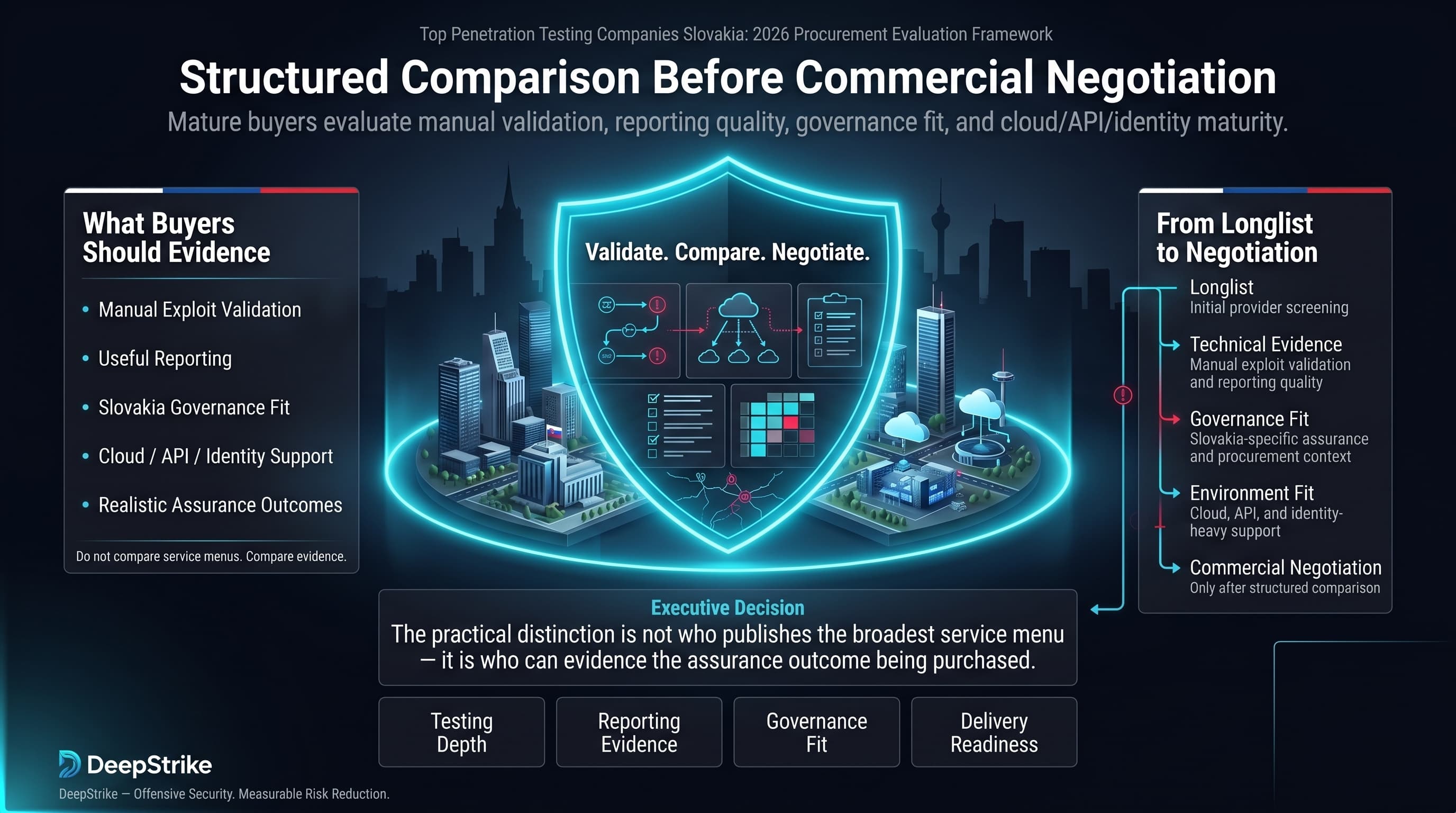
The ranking above is built for structured vendor comparison rather than generic awareness. For buyers using the top penetration testing companies slovakia query to build a shortlist, the practical distinction is not who publishes the broadest service menu, but who can evidence manual exploit validation, useful reporting, fit for Slovakia’s governance context, and realistic support for modern cloud, API, and identity-heavy environments. That is the standard procurement teams should apply before moving from longlist to commercial negotiation.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us