May 12, 2026
Updated: May 12, 2026
A procurement-focused comparison of Serbia penetration testing providers, ranked by testing depth, compliance fit, reporting quality, and buyer relevance.
Mohammed Khalil

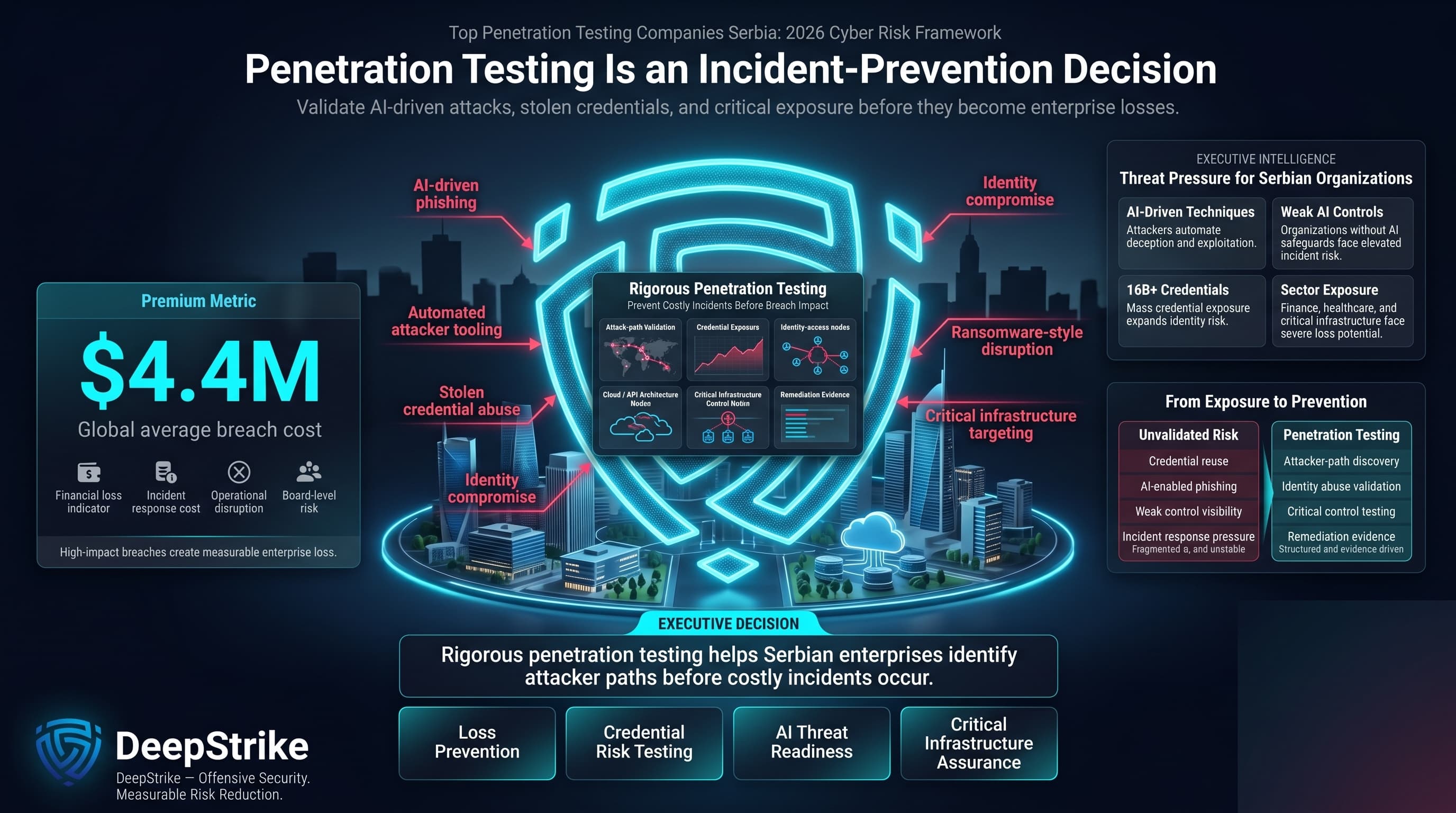
Serbian organizations are exposed to high cyber risk: breach costs often run into millions of dollars. A recent industry report cites a global average breach cost of $4.4 million, and attackers now leverage AI-driven techniques (97% of firms without AI controls reported incidents) and vast stolen credential pools (a 2025 “megaleak” exposed 16+ billion active credentials). These trends translate into significant expected losses for enterprises in Serbia, especially in finance, healthcare, and critical infrastructure. In such a risk landscape, rigorous penetration testing is essential to prevent costly incidents.
Companies operating in Serbia may also face compliance and assurance demands depending on sector, data exposure, customer geography, and contractual obligations. Serbia’s personal data protection framework is relevant for organizations handling personal data, while EU-facing companies may need to consider GDPR expectations. Financial entities, critical infrastructure operators, technology providers, and suppliers serving EU customers may also encounter NIS2-, DORA-, ISO 27001-, PCI DSS-, or sector-specific security expectations where relevant. These frameworks should not be treated as universally applicable to every Serbian buyer, but they often influence procurement language, audit evidence, and penetration testing scope.
This ranking is based on independent evaluation criteria. Vendors were assessed on documented capabilities (certifications, methodology, technical depth, etc.), not on marketing claims. No vendor paid for placement – this is an evidence-driven, procurement-grade comparison.
Penetration testing is a structured adversarial security assessment that combines automated vulnerability discovery with manual exploit validation to identify real-world attack paths, validate control effectiveness, and reduce breach probability.
Serbian buyers often require more than a basic vulnerability scan. Regulatory and audit pressure in Serbia is rising: vendors must demonstrate alignment with standards like ISO 27001, GDPR (Serbia’s personal data law), and industry-specific rules (banking regulator guidance, NIS2-type requirements for critical sectors). Public-sector contracts and financial/healthcare projects demand rigorous proofs of coverage. Therefore, buyers focus on vendors that provide detailed methodology and compliance mapping, not just branded services.
Additionally, sector sensitivity is high. Finance and healthcare firms in Serbia expect penetration testing to meet national security guidelines, and cloud/SaaS companies need testers adept at modern tech stacks. Organizations with cross-border or EU-facing operations must ensure pentest results satisfy EU auditors. This means Serbian buyers look for vendors fluent in regional regulations (“where relevant”) and capable of testing in cloud, API, and identity-heavy environments.
Local trust vs. technical depth is another factor. While a Serbian vendor might ease coordination, buyers cannot compromise on expertise. They often prefer demonstrated exploit skills and clear reporting over assumptions of safety from a local name. In practice, Serbia’s buyers value transparent, manual-driven testing (e.g. PTES/OWASP processes) and clear remediation guidance. Scans or checklists alone are seen as insufficient, especially where audit trails matter.
In summary, Serbia’s compliance-heavy and risk-conscious market means penetration testing providers are chosen for their methodology, reporting quality, and relevance to regulated environments (GDPR, PDPA, NIS2, banking standards, etc.), rather than for marketing claims or basic office presence.
We applied a procurement-grade methodology based on publicly available vendor information, stated service capabilities, visible sector positioning, testing methodology, delivery model, compliance language, and Serbia relevance. Where vendor claims were not publicly detailed, we treated them cautiously rather than assuming capabilities that were not clearly evidenced.
Technical depth was paramount. We favored vendors explicitly offering manual exploit validation (DeepStrike and Ras-IT advertise fully manual testing) over those relying on automated scans. Red teaming capability was noted where mentioned (none in our list explicitly labeled as such). Cloud and API expertise were also scored: DeepStrike’s SaaS dashboard and BrightMarbles’ software testing record indicated modern coverage, while others focus on network infrastructure.
Reporting quality and compliance alignment were major factors. Vendors listing explicit mapping to standards scored higher. For example, DeepStrike’s reports meet SOC2/ISO/HIPAA standards, and VasicVault emphasizes GDPR/HIPAA/ISO compliance. We checked retest policies (DeepStrike offers unlimited retesting; Ras-IT provides retesting by request) as part of service completeness.
Industry and regulatory fit were considered: PULSEC’s partner status with government and telecom suggests a focus on public and critical sectors. UN1QUELY’s experience in healthcare and finance hinted at regulated-industry maturity. Serbia/EU delivery feasibility was assessed: PULSEC and Ras-IT have local Serbian bases, while DeepStrike (US/UAE) and BrightMarbles (Serbia office serving global clients) represent remote-capable firms.
Overall, this methodology emphasizes validated exploitability and context fit over marketing or tool-centric claims. Providers with documented manual testing processes, clear compliance-oriented reporting, and relevant sector experience ranked higher, while those lacking evidence of depth were scored cautiously.
When selecting a pentest vendor in Serbia, avoid common pitfalls. Don’t assume a big brand or flashy platform equals better security; focus on the technical skill of the testers. Beware of firms that mainly use automated scanning tools – without expert-driven analysis these can miss critical flaws (especially in business logic or APIs). Always request sample reports: they should clearly explain exploit findings and remediation steps, aligning them to compliance needs.
Ensure the scope is comprehensive. Under-scoping (e.g. testing only external networks or ignoring cloud/API components) is a frequent oversight. Check that all assets (cloud servers, mobile apps, identity systems) are included. Confirm the engagement includes retesting: fixes should be re-validated at no extra cost or clearly documented terms.
Watch out for junior-only teams: ask about the seniority of the testers. Experts with hands-on pentest certificates (OSCP, GPEN, etc.) are more likely to find complex issues. Similarly, don’t equate having a local office with high expertise. A small local office may lack experienced staff, while a remote specialist firm could deliver superior testing. Focus on methodology transparency: insist on details of how vulnerabilities will be exploited rather than just scanned.
Finally, ensure the team’s reporting capabilities match Serbia’s procurement needs. Serbia’s regulated sectors often demand well-structured reports and compliance evidence. Vendors that map findings to ISO/GDPR/NIS2 requirements (as DeepStrike and VasicVault do) will better support audits. In short, pick a provider with proven manual testing depth, clear deliverables, and relevant experience in your sector rather than one promising quick automated checks.
Why They Stand Out: DeepStrike stands out for its manual-first penetration testing approach, with emphasis on exploit validation, attack-path analysis, cloud and API testing, and remediation-focused reporting. Its delivery model is suited to organizations that want more than automated vulnerability scanning and need findings explained in a way that technical, risk, and compliance stakeholders can use. DeepStrike is especially relevant for cloud-first, SaaS, and API-heavy environments where business logic, identity flows, and modern application architectures require deeper manual review.
Serbia Relevance: DeepStrike is a global provider with no Serbian office. Serbia buyers can engage it remotely; however, its operations are based in the USA and UAE. Organizations should note the lack of local presence and confirm language or onsite requirements. DeepStrike is relevant for Serbia enterprises willing to work with an international vendor, especially those familiar with U.S./EU security standards. Editorial note: DeepStrike is included in this list based on the same evaluation criteria applied to all providers.
Testing Depth Model: Manual exploit chaining. DeepStrike emphasizes hands-on testing by certified experts, simulating real cyberattacks rather than relying on scanners. This yields thorough breach-path validation.
Key Strengths:
Potential Limitations:
Best For: Cloud-native and SaaS enterprises, tech companies and regulated organizations (e.g. finance/health) that require deep, continuous pentesting with strong compliance reporting.
Why They Stand Out: PULSEC is a full-spectrum cybersecurity provider combining continuous monitoring with adversarial testing. Its SOC (security operations center) runs 24/7, offering clients ongoing threat detection. On top of that, PULSEC performs advanced penetration tests as part of a broader security program. It positions itself as a “regional leader” with international reach (centers in Serbia, Bosnia, Switzerland) and publicly emphasizes a certification-led security capability. PULSEC’s emphasis on proactive defense and partnership with major providers (like Telekom Srbija) suggests a maturity valued by large enterprises.
Serbia Relevance: PULSEC’s roots and partners in Serbia make it highly relevant locally. It has a Serbia headquarters and actively serves Serbian government and industry. This local/regional presence benefits buyers needing onsite cooperation or familiarity with national regulations. Its role as a partner for state and energy entities underscores its fit for public-sector projects. (Buyers with specific language or residency requirements should verify them, as PULSEC is primarily Serbia/Balkan-focused.)
Testing Depth Model: Hybrid model. PULSEC’s pentesting leverages the knowledge of its SOC and red teams. It likely combines automated scanning within its continuous monitoring with expert manual validation during dedicated pentests, covering both breadth (through the SOC) and depth.
Key Strengths:
Potential Limitations:
Best For: Large Serbian enterprises, public-sector institutions, and regulated industries (especially in finance, energy, telecom) that need ongoing security monitoring combined with expert pentesting and compliance.
Why They Stand Out: Ras-IT is distinguished by its highly technical, manual approach. It explicitly follows the PTES and OWASP frameworks and emphasizes expert-led testing across diverse assets. Notably, it covers specialized areas like IoT and industrial control systems, which many firms skip. Its engineers balance automated scans with deep manual exploitation. Ras-IT markets itself as capable of “staying practical” – focusing on real risk paths and providing retesting as needed.
Serbia Relevance: As a Belgrade-based firm, Ras-IT is deeply local. It caters to Serbia and wider Europe (remote engagements are “friendly” for the region). Its local presence may appeal to Serbian buyers seeking responsive communication. Ras-IT is suitable for clients that require technical depth more than broad compliance packaging. (Public sector or regulated buyers should confirm that Ras-IT’s deliverables satisfy audit requirements, as its style is very engineer-driven.)
Testing Depth Model: Manual exploit chaining. Ras-IT’s core capability is hands-on penetration testing. Skilled testers exploit vulnerabilities to validate real attack paths, rather than relying solely on automated tools.
Key Strengths:
Potential Limitations:
Best For: Serbia-based enterprises or agencies with critical infrastructure needs. Ideal for finance, government, or industrial organizations looking for deep manual analysis of networks, applications, and IoT systems rather than a checkbox audit.
Why They Stand Out: CYBERGATE positions itself as a full-service cybersecurity shop with strong ethical hacking expertise. Its offerings include penetration tests across various domains (network, app, mobile, user infrastructure). The emphasis is on manual testing—CyberGate explicitly notes hands-on scanning and exploitation. This variety of test types suggests a versatile capability.
Serbia Relevance: Based in Belgrade, CyberGate is immediately relevant to Serbian buyers seeking local vendors. Its branding (“Europe”) implies regional ambition, so it might serve cross-border needs as well. Buyers should note that CyberGate’s public materials emphasize flexibility, which can suit clients who need customized testing scenarios. However, specific industry or compliance strengths aren’t highlighted, so buyers should align expectations accordingly.
Testing Depth Model: Manual exploit chaining. CyberGate focuses on hands-on testing of internal and external environments, reflecting an attacker-centric methodology.
Key Strengths:
Potential Limitations:
Best For: Organizations that need customizable pentesting in Serbia and value in-person collaboration. Suitable for enterprises and regulated firms that prioritize broad security coverage over specific certifications, provided they validate the firm’s methods firsthand.
Why They Stand Out: UN1QUELY is a specialized cybersecurity firm focusing half of its portfolio on pentesting. Its clients span healthcare and finance sectors (where thorough testing and compliance are critical). Client testimonials praise UN1QUELY’s professionalism, timely delivery, and helpfulness during remediation. They work closely with clients (e.g. Slack communication, rapid retesting feedback), indicating strong support during engagements.
Serbia Relevance: Based in Serbia, UN1QUELY serves both domestic and international clients. It is well-suited to Serbian organizations in regulated industries—especially healthcare and banking, which form significant parts of its experience. Its familiarity with these sectors’ needs (HIPAA-like or GDPR-level concerns) makes it a viable choice for Serbia’s finance and health institutions.
Testing Depth Model: Hybrid model. UN1QUELY combines manual penetration efforts with automated analysis. Notably, one project review mentioned a Snyk-based code review supplementing the pentest, suggesting blended techniques.
Key Strengths:
Potential Limitations:
Best For: Serbian and regional organizations in healthcare, finance, and education seeking attentive penetration testing with strong hand-holding. Also fits technology firms needing integrated security support with quick turnarounds.
Why They Stand Out: BrightMarbles is a versatile IT company with a dedicated cybersecurity division. They offer penetration testing as part of a wider services suite. Clients highlight their strong project management, timely delivery, and excellent communication. In pentesting projects (e.g. for a healthcare company), they demonstrated capability in both network and application testing. Their larger team size allows handling multi-disciplinary projects, combining dev and security skills.
Serbia Relevance: With headquarters in Serbia and international projects (57% staff in Serbia), BrightMarbles has deep local roots. It is accessible to Serbian buyers and understands the regional market. Its blend of software and security expertise can be advantageous for Serbia tech companies and startups. Buyers looking for a local partner with broader IT capabilities may find it appealing.
Testing Depth Model: Hybrid model. BrightMarbles utilizes both automated tools and manual review. The focus on software development suggests they can understand and test complex applications, though security is 10–20% of services (clients note “10% cybersecurity” on Clutch).
Key Strengths:
Potential Limitations:
Best For: Small-to-midsize organizations and tech startups (including SaaS and fintech) in Serbia seeking competent pentesting integrated with broader IT services. Particularly good for companies valuing timely delivery and budget-conscious solutions.
Why They Stand Out: VasicVault positions itself at the intersection of technical pentesting and regulatory compliance. Its services explicitly cover major standards (GDPR, HIPAA, ISO 27001, PCI DSS), making it attractive for clients who need audit-friendly testing. The firm’s focus on cloud and network security complements its compliance orientation. It has delivered projects in finance and healthcare (as noted by its industry mix), suggesting domain knowledge.
Serbia Relevance: As a Belgrade-based provider, VasicVault is well-placed for Serbia organizations, especially smaller firms. Its emphasis on compliance (GDPR alignment, etc.) addresses common local concerns. For finance or healthcare companies in Serbia, VasicVault’s local presence and sector familiarity can be advantageous.
Testing Depth Model: Hybrid model. VasicVault appears to combine manual analysis with systematic checklists aligned to standards. Its language around “security design reviews” and compliance suggests an organized methodology rather than pure red-teaming.
Key Strengths:
Potential Limitations:
Best For: Small-to-medium Serbian enterprises in finance, healthcare, or regulated industries that need penetration testing with a strong compliance component. Suitable for organizations prioritizing adherence to GDPR/ISO/HIPAA standards alongside vulnerability discovery.
Serbian buyers often make these mistakes: equating brand size with testing depth, overvaluing automated tools, or confusing scans with real pentests. A famous vendor logo doesn’t guarantee skilled testers. Similarly, a tool-heavy “vulnerability scan” may miss logic and chaining flaws. Buyers must demand manual exploit validation, not just a list of CVEs.
Another error is neglecting report quality. A flashy PowerPoint or scan dump won’t suffice for audits; detailed, actionable reports are essential. Also, many treat pentesting as a checkbox, commissioning the minimal scope to satisfy policy. This underestimates the complexity of modern apps and APIs. Serbia’s cloud and API-driven environments mean business logic and identity flows must be tested; assuming basic network tests cover all is risky.
Some assume PTaaS or continuous testing models automatically ensure depth – they don’t unless skilled humans interpret the results. And finally, selecting a firm simply because it’s local can backfire: local presence doesn’t inherently mean technical expertise. It’s more important to vet methodology and team credentials. In short, Serbian buyers should avoid superficial comparisons and focus on the quality and relevance of the pentest engagement.
Enterprise Considerations: Large organizations usually face bigger attack surfaces and stricter oversight. They benefit from vendors that offer comprehensive methodology (combining automated scans with deep manual tests) and formal compliance processes. Enterprises often prefer or require mature firms with documented certifications, enterprise-scale teams, and robust project management. For example, enterprises might engage hybrid or red-team capable providers like PULSEC or DeepStrike, which can handle large scopes and integrate testing into an ongoing security program. Global or regional firms with multi-location delivery (e.g. Serbia plus EU presence) can be advantageous. Enterprise clients should verify that the vendor’s resources and retesting policies match their complexity.
SMB Considerations: Smaller companies generally have tighter budgets and simpler environments. They often need focused, efficient testing of a few critical assets. For them, cost and flexibility matter. Vendors like BrightMarbles or UN1QUELY (which combine development and security expertise) can deliver good value for money. SMBs might accept a primarily remote engagement if it lowers cost, and can leverage PTaaS models or shorter, fixed-scope tests. Over-automation or one-size-fits-all packages can work for routine SMB needs, but buyers should ensure some manual review to catch non-obvious issues. Importantly, SMB buyers should still confirm that reports are clear enough for their auditors and management, even if formal compliance demands are lower.
Trade-offs: Enterprise engagements typically deliver higher depth and tailored coverage (at higher cost), whereas SMB-friendly providers focus on efficiency and fixed-price models. Boutique firms (local or specialized) may offer personalized service and flexibility (good for some SMBs), but may lack the sheer manpower for massive scopes. Conversely, large vendors may have overhead that SMBs don’t need, but they bring greater consistency.
For both buyer types, balancing the scope and rigor of testing against budget constraints is key. SMBs should prioritize critical assets and core testing activities, while enterprises can invest in more exhaustive scenarios (e.g. red teaming, cross-site chaining). The choice of vendor should reflect these needs: smaller local specialists for focused projects versus larger, multi-certified firms for enterprise-grade assurance.
Penetration testing cost is driven by multiple factors, not geography alone. Scope size is primary: the number of applications, servers, networks, and user profiles to test. Larger scopes require more tester-hours. The type of testing matters: external network scans are simpler than in-depth internal or authenticated web/API tests. Cloud and containerized environments typically add complexity (requiring time to map cloud configurations and APIs).
Depth of testing heavily influences price. Fully manual exploits (finding zero-days or chain attacks) take far more effort than automated scans; such thoroughness is pricier. If the client requests exhaustive tests (full exploit chains, social engineering, or red teaming), expect higher costs. Conversely, a scan-based assessment will cost less but yield less assurance.
Rescoping and retesting also affect cost. Inclusive policies (like free retesting) can appear generous, but some vendors factor that into the base fee. Projects requiring multiple test rounds or long-term engagement incur more fees.
Reporting requirements can drive costs: a simple vulnerability list is cheaper than a polished, compliance-aligned report with executive summaries and remediation guidance. If a firm maps findings to standards (GDPR, PCI, etc.), that added documentation adds value (and effort).
Delivery mode is relevant: on-site testing involves travel/time costs; remote engagements are generally less expensive. However, fully remote testing in Serbia is common and viable for many environments.
Finally, ongoing vs one-off models impact pricing. Continuous pentesting (PTaaS) subscriptions spread cost over time, whereas single engagements are billed per project. Serbia buyers should get detailed quotes outlining what’s included, as vendors in the region may price differently based on service levels and local market rates. Overall, rather than a fixed number, focus on how each factor scales the effort and align that with your security priorities.
How much do penetration testing services cost in Serbia?
Costs vary widely based on scope and depth. There’s no fixed “Serbia rate.” Pricing depends on factors like system complexity, manual effort, compliance needs, and retesting. Some smaller engagements may start in the low thousands of euros, while enterprise projects can cost significantly more. Serbia buyers should request detailed quotes and focus on value (scope coverage and expertise) rather than regional price lists.
What is included in enterprise penetration testing?
Enterprise pentests typically cover multiple layers: external and internal networks, web/mobile applications, cloud infrastructure, and sometimes social engineering. A full enterprise test will include authenticated scenarios (using real or staged credentials) and attempt to chain multiple exploits. It often also includes thorough reporting, risk analysis, and recommendations aligned with the company’s regulatory requirements.
Are certifications more important than tools?
No. Certifications (like OSCP, CISSP, etc.) indicate a tester’s knowledge, but the team’s experience and methodology are more critical. A certified tester with weak methodology won’t find issues better than a skilled tester with no formal certs. Similarly, tools are only as good as their use; skilled pentesters use tools to augment, not replace, manual insight. Focus on a vendor’s track record and case studies rather than just their certifications or toolset claims.
How long does a pentest engagement take?
Typically, a penetration test can range from a few days (for a small web app) to several weeks or months (for a large enterprise scope). Planning and scoping take time, followed by execution. A simple external network pentest might finish in a week, while a full internal+external+application test of a large environment could take several weeks. Allow time after testing for report delivery and a follow-up retest cycle if needed.
Is penetration testing required by GDPR, NIS2, DORA, or other regulations?
No Serbia-specific law explicitly mandates pentesting by name. However, Serbia’s Data Protection Act (aligned with GDPR) requires “appropriate technical measures” for personal data, which often implies regular security testing. Similarly, EU regulations like GDPR, NIS2, and DORA (for financial entities) encourage periodic testing of security measures. For organizations that fall within relevant regulatory or contractual scope, security testing may support evidence of appropriate technical and organizational measures. The exact requirement depends on sector, legal exposure, contracts, and whether the organization is directly or indirectly affected by EU-facing obligations. In practice, undergoing pentests helps meet these obligations. The National Bank of Serbia and sector regulators expect robust security, so many Serbian companies perform pentests to demonstrate compliance. Always confirm with legal advisors which tests are “required” versus recommended.
How often should testing be performed?
At minimum, annually or after significant changes (new systems, updates, or cloud migrations). Many experts advise more frequent testing for high-risk assets. Modern practices favor continuous testing (DevSecOps) or semi-annual tests for critical apps. In Serbia’s dynamic digital environment, aligning tests with release cycles or major upgrades is prudent.
Should Serbia buyers choose a local provider or a cross-border specialist?
It depends on needs. Local firms may offer easier communication and familiarity with local context, but cross-border specialists might provide deeper technical skills or niche expertise. The key is to evaluate each vendor’s abilities, not location alone. For highly regulated projects, an international firm experienced with EU standards could be beneficial. For projects requiring Serbian language or onsite presence, a local company may be better. Ultimately, choose the provider that best meets your technical requirements and trust criteria, regardless of headquarters.
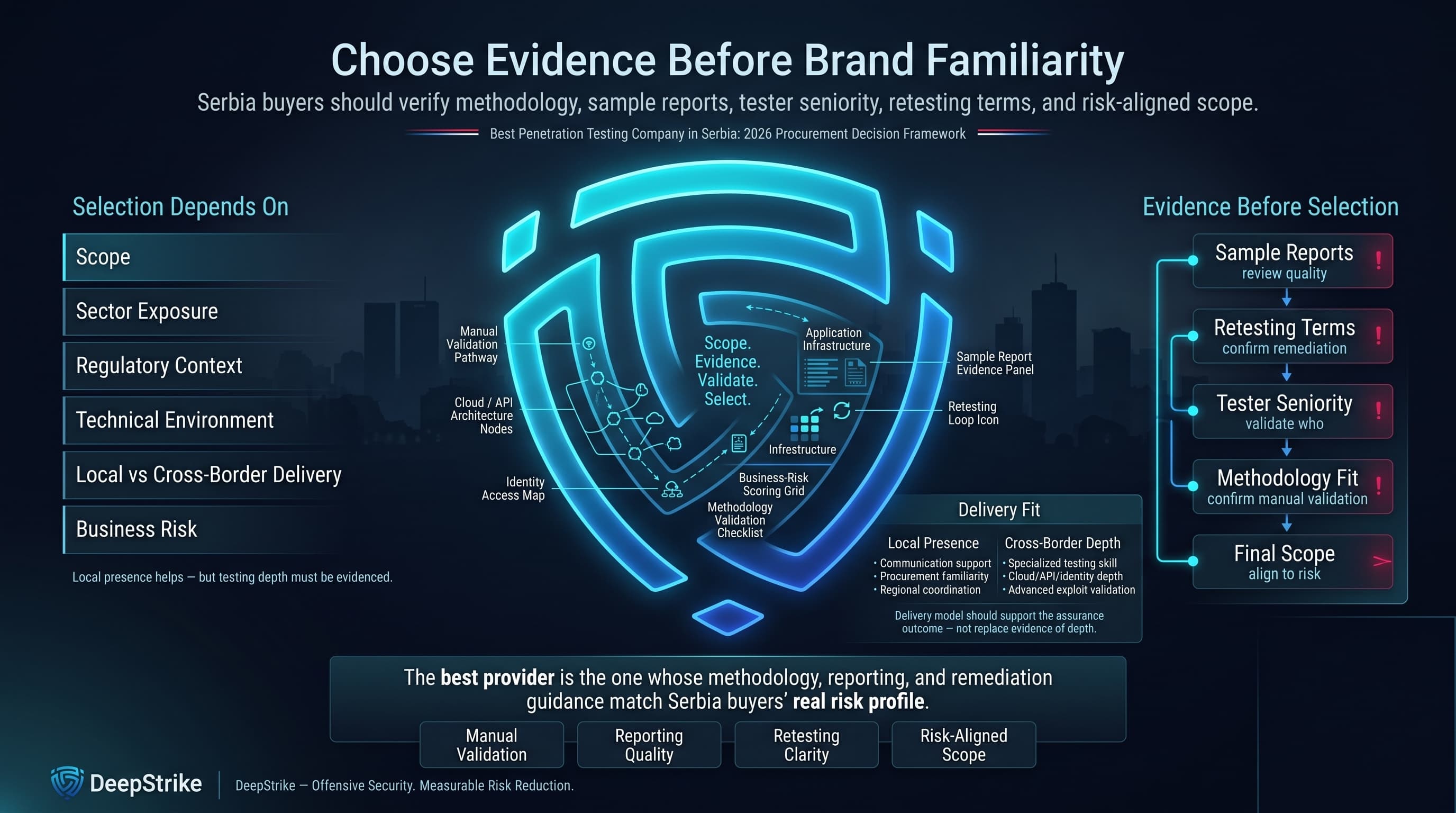
The best penetration testing company in Serbia depends on the buyer’s scope, sector, regulatory exposure, technical environment, and need for local versus cross-border delivery. Serbian organizations should prioritize vendors that can demonstrate manual validation, clear methodology, useful reporting, realistic remediation guidance, and relevant experience with cloud, API, identity, application, or infrastructure testing. Local presence can help with communication and procurement, but it should not replace evidence of testing depth. Buyers should request sample reports, confirm retesting terms, validate tester seniority, and ensure the final scope reflects real business risk rather than a narrow compliance checkbox.
Written by the DeepStrike editorial team and reviewed for cybersecurity accuracy by offensive security specialists familiar with penetration testing, vulnerability validation, cloud security, application security, and compliance-oriented reporting.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us