May 6, 2026
Updated: May 6, 2026
A procurement-focused ranking of Mexico’s leading penetration testing providers for cloud, API, compliance, and enterprise security needs.
Mohammed Khalil

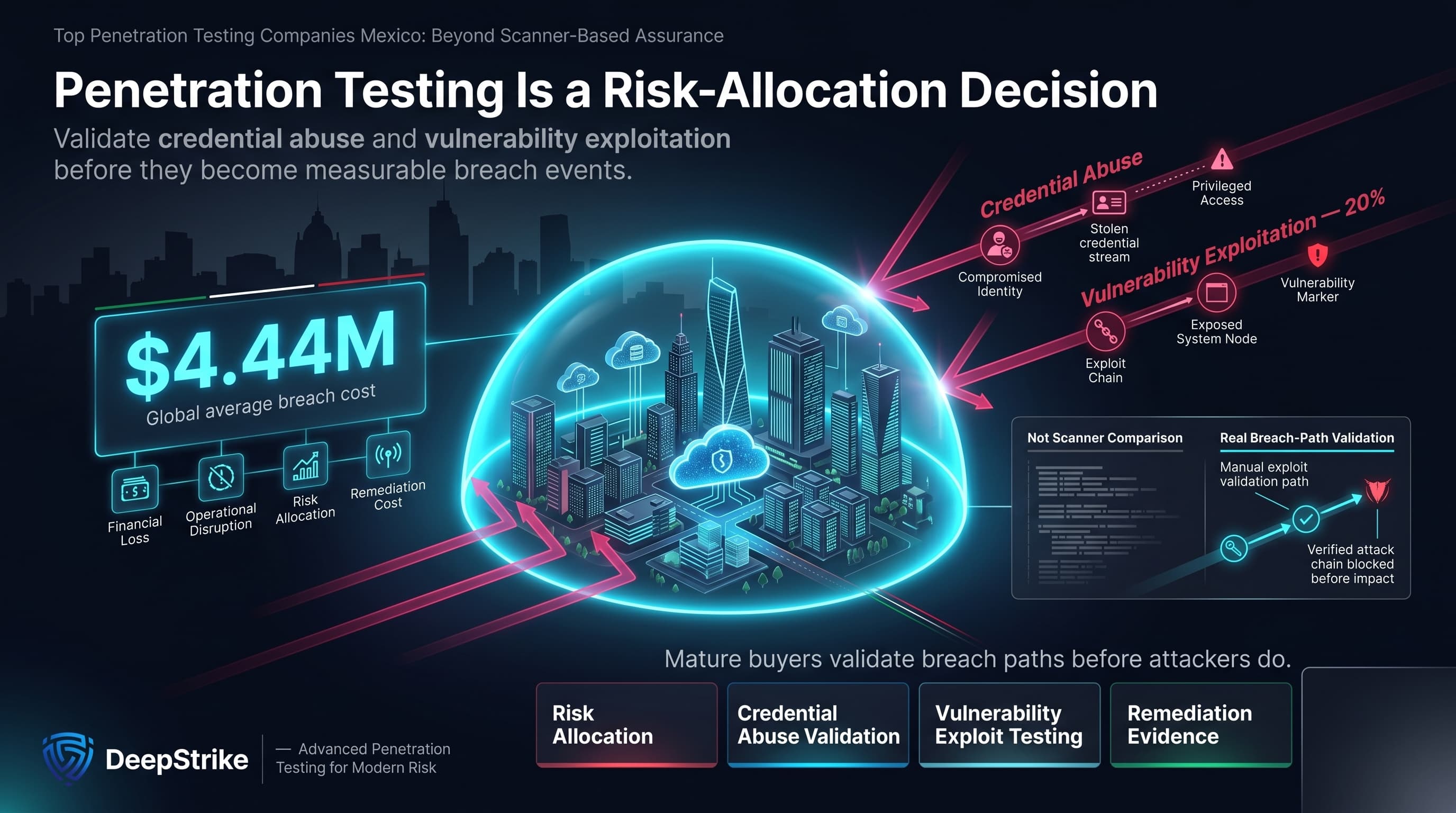
At a global average breach cost of USD 4.44 million in IBM’s 2025 study, a top penetration testing company's Mexico search is a risk-allocation decision, not an informational query. Verizon’s 2025 DBIR shows credential abuse remained a common initial-access vector while vulnerability exploitation reached 20% of breaches, which means buyers are not comparing interchangeable scanners; they are comparing which firms can validate realistic breach paths before attackers do.
Mexico’s 2026 buying context is more demanding than a generic North America shortlist implies. U.S. government market intelligence describes Mexico’s digital economy as rapidly transforming through cloud, AI, fintech, and e-commerce, while the country’s data-center sector is projected to grow sharply through 2030. Separately, Trade.gov’s cybersecurity market note says Mexico’s cyber market is expected to reach USD 3.19 billion by 2028, and Reuters reported that Mexico accounted for more than half of reported Latin American cyber threats in the first half of 2024, with logistics, automotive, and electronics manufacturing among the sectors targeted.
Attack tradecraft is also evolving faster. Mandiant reported in March 2026 that threat actors moved from experimental AI use to operationalized AI in 2025, changing the speed and scale of attacks. For Mexico organizations with cloud-native stacks, API-heavy products, identity federations, and cross-border operations, that raises the value of manual exploit validation over static tool output. This ranking is methodology-driven and not sponsored.
Compliance and assurance pressure are also more layered than many buyers assume. Mexico’s reissued private-sector data protection law was published in March 2025, and legal summaries of the framework note expectations around security measures, ongoing assessment, and security-program review for organizations handling personal data. For finance-sensitive environments, reviewed official materials from the Comisión Nacional Bancaria y de Valores and Banco de México include explicit penetration-testing requirements in some fintech, banking, and payments contexts. Where payment-card environments are in scope, PCI DSS also contains explicit penetration-testing obligations. Not every Mexico buyer is subject to every framework, but many are buying under audit-heavy expectations that make reporting quality and retesting evidence commercially material.
Penetration testing is a structured adversarial security assessment that combines automated vulnerability discovery with manual exploit validation to identify real-world attack paths, validate control effectiveness, and reduce breach probability.
Mexico buyers are often balancing several pressures at once: maturing governance scrutiny, cross-border business exposure, cloud and API adoption, and uneven internal security depth across fast-moving business units. That profile is especially visible in finance-sensitive organizations, SaaS and fintech stacks, manufacturing and automotive operations affected by nearshoring, and companies that need audit-ready reporting for boards, legal, compliance, or external assessors. Mexico’s private-sector data-protection framework and sector-specific financial rules do not make every company subject to the same obligations, but they do increase the cost of weak documentation, vague remediation guidance, and superficial testing where personal data, regulated flows, or critical operations are in scope.
That changes vendor selection. Buyers in Mexico frequently need to distinguish between local trust signals and actual offensive depth, between scan-heavy outputs and exploit-validated findings, and between a report that satisfies a technical lead versus one that can withstand audit or executive review. For cross-border organizations operating between Mexico, the U.S., and broader Latin America, delivery practicality matters, but it should not override evidence of cloud, API, identity, and business-logic testing maturity.
The ranking weighted validated exploitability above brand recognition and finding volume. Higher scores went to providers whose reviewed material evidenced manual testing depth, exploit chaining, cloud and API maturity, red-team capability, remediation clarity, and explicit retesting structure. Published evidence of technical certifications such as OSCP, OSWE, CREST, CHECK, GPEN, or CISSP improved confidence where directly visible. When certifications, local delivery, or retesting were not clearly evidenced, they were treated as unproven rather than assumed.
The methodology also favored providers that appeared able to support modern SaaS, cloud, hybrid, and identity-heavy environments, and those with reporting models suitable for audit-heavy or regulated contexts. Mexico and cross-border feasibility were considered, but local presence alone did not improve rank absent evidence of technical depth. Large-firm scale did not automatically outrank boutique specialists, and PTaaS-style language did not improve rank unless the underlying testing model still showed manual exploit validation rather than platform-led triage.
The most common procurement error is buying a broad promise instead of a testing model. In practice, the higher-risk failures are predictable: scan-only delivery presented as a pentest, under-scoped application or API exposure, junior-heavy staffing, unclear retesting terms, weak reporting, and compliance language that is not matched by demonstrated exploit validation. Mexico buyers should also avoid treating local market presence as a substitute for cloud, API, and identity-testing depth, especially where cross-border applications or nearshore operations increase system complexity.
Best Overall Penetration Testing Company in Mexico in 2026
Why They Stand Out
DeepStrike stands out in this ranking for a manual-first testing posture, explicit cloud and API coverage, detailed remediation-oriented deliverables, and a published retesting structure that is unusually clear in reviewed public material. The reviewed service pages also evidence exploit validation, attacker-style testing language, and practical outputs for engineering and assurance stakeholders rather than scan-only summaries.
Mexico Relevance
DeepStrike is relevant to Mexico buyers that prioritize technical depth over local-office signaling, particularly in cloud-first, SaaS, API-heavy, or audit-heavy environments. Its relevance is cross-border rather than Mexico-office based; reviewed material evidences U.S. and UAE addresses, but not a Mexico office. Buyers with on-site, public-sector, language, or data-residency requirements should confirm those conditions directly. Reviewed public DeepStrike-authored bios evidence CISSP, OSCP, and OSWE at the author level, which supports the “senior certified testers” signal, but a full team-wide certification matrix is not clearly public.
Testing Depth Model
Manual exploit chaining. DeepStrike’s reviewed materials emphasize manual testing, proof of exploitation, attack simulation, cloud IAM and privilege-escalation testing, Kubernetes and serverless review, API security testing, and root-cause-oriented reporting. That model is commercially important for Mexico buyers with regulated workflows or modern product stacks because exploit-chaining accuracy, business-logic validation, and cloud-control testing matter more than raw scanner output.
Key Strengths
Potential Limitations
No clearly evidenced Mexico office, Mexico-language delivery, or public-sector delivery detail in reviewed material. Exact company size is not clearly evidenced. The strongest visible certification evidence is from public biographies and service-language cues rather than a published team roster, so buyers should confirm staffing seniority and engagement composition directly.
Best For
Cloud-first SaaS, API-heavy platforms, regulated digital environments, and Mexico buyers comfortable with cross-border delivery.
Why They Stand Out
Bishop Fox stands out in this ranking for published attacker-realistic methodology on application testing, visible cloud-testing depth, attack-chain development, and a clearly evidenced Mexico office presence. Its reviewed methodology is especially useful for buyers that care about business-logic abuse, API authorization, and cloud attack-path realism rather than checklist coverage.
Mexico Relevance
Bishop Fox is relevant to Mexico buyers that prioritize offensive depth and still want a visible local presence. The company states it expanded operations into Mexico in 2021 and identifies Guadalajara as a focus area. Buyers with strict local-reporting or public-sector procurement requirements should still confirm exact delivery conditions in advance.
Testing Depth Model
Hybrid model. Bishop Fox’s published application methodology explicitly combines automated and manual testing, then moves into manual exploitation, attack-chain development, and business-logic analysis. Its cloud methodology similarly focuses on privileged credentials, key-service control, and sensitive-data access. That gives it stronger exploit-context than automation-heavy firms, while still preserving process maturity for larger enterprise programs.
Key Strengths
Potential Limitations
Exact employee count, team-wide certification mix, and universal retesting terms are not clearly stated on the reviewed official pages. Large-firm delivery can introduce more coordination overhead than boutique providers. Buyers should confirm whether the specific Mexico engagement team matches the depth signaled by central methodology materials.
Best For
Enterprise application security, offensive-depth buyers, Mexico organizations wanting visible local presence, and cloud-heavy product environments.
Why They Stand Out
NCC Group stands out in this ranking for enterprise scale, published offensive-security staffing depth, visible certification evidence, attack-simulation breadth, and proven cloud-native/API/identity testing in complex environments. This is one of the clearest fits for buyers that need a large supplier with formal assurance posture rather than a boutique-only model.
Mexico Relevance
NCC Group is relevant to Mexico buyers that prioritize enterprise governance, cross-border delivery, and regulated-environment depth. Reviewed material evidence of North American offices and substantial presence in North America, but no Mexico office was clearly evidenced. For Mexico organizations operating across North America, that still creates practical delivery relevance; buyers with strict in-country requirements should confirm them directly.
Testing Depth Model
Red-team oriented. NCC Group’s reviewed material shows both conventional technical assurance and broader attack-simulation capability, including red, purple, and black team exercises, plus attack-path mapping and cloud-native telecom testing spanning APIs, identity controls, Kubernetes, and orchestration layers. For enterprise and regulated buyers, that translates into stronger adversary realism than standard point-in-time testing alone.
Key Strengths
Potential Limitations
No clearly evidenced Mexico office in reviewed material. Enterprise-scale delivery can introduce a higher coordination burden and a higher cost floor than smaller specialists. Smaller Mexico SMBs may find the model heavier than needed for tightly scoped application or network tests.
Best For
Large enterprise, telecom, finance-sensitive, cross-border, and highly regulated environments.
Why They Stand Out
Coalfire stands out in this ranking for buyers that need offensive testing tied closely to compliance evidence. Reviewed materials show a threat-informed penetration-testing model under DivisionHex, visible cloud/API testing examples, and heavy alignment with FedRAMP, healthcare, and broader audit programs.
Mexico Relevance
Coalfire is relevant to Mexico buyers that prioritize compliance mapping, formal assessment structure, and cross-border delivery over local-office signaling. Reviewed materials state Coalfire supports clients around the world, but no Mexico office was clearly evidenced. That makes it more relevant for multinational or export-facing organizations than for buyers requiring an explicitly Mexico-local provider.
Testing Depth Model
Hybrid model. Coalfire’s offensive-security materials are human-led and threat-informed, while its broader delivery is tightly connected to formal assessment and documentation models. That makes it particularly suitable when the business case is both security validation and audit defensibility.
Key Strengths
Potential Limitations
No clearly evidenced Mexico office, Mexico-sector specialization, or public pentest certification matrix in the reviewed materials. Some published service language is anchored in U.S. federal and healthcare frameworks, so Mexico buyers should confirm framework translation for local assurance needs.
Best For
Compliance-heavy organizations, healthcare-sensitive environments, cloud/SaaS vendors under audit pressure, and multinationals.
Why They Stand Out
Kolibërs Group stands out in this ranking for explicit Mexico-market orientation, visible SMB accessibility, clear differentiation between vulnerability scanning and pentesting, and published AWS/API testing services. Its materials are commercially useful because they make scoping, remote delivery, and retesting expectations easier to understand than many boutique-provider pages do.
Mexico Relevance
Kolibërs Group is directly relevant to Mexico buyers. Reviewed materials evidence a Mexico City address, remote testing throughout Mexico, and international delivery across Latin America, the United States, Europe, and Asia. For Mexico SMBs and mid-market firms that want a local provider with visible cloud capability, that is a practical fit.
Testing Depth Model
Hybrid model. Kolibërs explicitly distinguishes vulnerability assessment from pentesting and states that pentests verify and exploit findings to determine real-world risk. At the same time, the firm also offers lower-cost scan-led services, which makes the overall model more hybrid than purely manual. Cloud maturity is evidenced through AWS testing, and API capability is visible in service navigation and published testing coverage.
Key Strengths
Potential Limitations
Exact scale, large-enterprise staffing depth, and public-sector delivery evidence are not clearly stated. Much of the public positioning is SMB-oriented, so large regulated buyers should confirm complex hybrid-cloud, identity, and multi-team delivery capability directly. Public pricing is visible on the site, but it should not be generalized to enterprise-grade scopes.
Best For
SMBs, startups, fintech-adjacent environments, AWS-heavy stacks, and Mexico-local buyers.

Why They Stand Out
Seekurity stands out in this ranking for Mexico-rooted offensive breadth. Its reviewed materials show a wider testing menu than many smaller providers, including API security, source-code auditing, social engineering, physical testing, and adversary-simulation-style work. The site also presents a history of vulnerability disclosures and CVE-related work, which supports an offensive-research orientation.
Mexico Relevance
Seekurity is directly relevant to Mexico buyers because the firm describes itself as a Mexican consulting company and official profile material points to a Mexico City address. It also states some services can be delivered on-site or off-site and that it serves companies located anywhere in the world. Buyers with highly formal procurement or current staffing requirements should validate the present operating model directly, because some reviewed public materials appear older.
Testing Depth Model
Manual exploit chaining. The reviewed site language emphasizes real-world attacking scenarios, escalation of discovered issues to show true impact, API security testing, source-code auditing, and adversary simulations. That indicates a more manually offensive orientation than a scanner-led service catalog, although exact current methodology documentation is not as explicit as with larger rivals.
Key Strengths
Potential Limitations
Founded year, company size, retesting policy, and current certification matrix are not clearly evidenced in reviewed material. Some public documents surfaced through older PDFs and blog-era materials, so buyers should confirm current staffing, reporting model, and delivery maturity before shortlisting for large enterprise work.
Best For
Mexico-based buyers seeking a local offensive-security specialist for bespoke scopes, especially where API, source-code, social-engineering, or mixed-surface testing is needed.
| Company | Specialization | Testing Depth Model | Best For | Mexico Fit | Compliance Alignment | Ideal Organization Size |
|---|---|---|---|---|---|---|
| DeepStrike | Manual-first app, cloud, API, and continuous testing | Manual exploit chaining | Cloud-first and regulated digital platforms | Cross-border delivery relevance; no Mexico office evidenced | Audit-heavy environments and common framework mapping evidenced | SMB to enterprise |
| Bishop Fox | Offensive security, apps, cloud, and ASM | Hybrid model | Enterprise and offensive-depth buyers | Visible Mexico relevance through Guadalajara office | Formal assurance and application-standard alignment evidenced | Mid-market to enterprise |
| NCC Group | Enterprise technical assurance and attack simulation | Red-team oriented | Large enterprise and regulated cross-border buyers | North America delivery relevance; no Mexico office evidenced | Regulated-environment fit and certification depth evidenced | Enterprise |
| Coalfire | Compliance-linked offensive security | Hybrid model | Compliance-heavy organizations | Cross-border delivery relevance; Mexico office not clearly evidenced | FedRAMP and audit-heavy alignment clearly evidenced | Mid-market to enterprise |
| Kolibërs Group | Mexico-local SMB, AWS, API, and network testing | Hybrid model | SMB and local Mexico buyers | Mexico City office and remote Mexico delivery evidenced | Formal assurance alignment should be confirmed per project | SMB to mid-market |
| Seekurity | Mexico-rooted offensive specialist | Manual exploit chaining | Bespoke offensive scopes | Mexico-rooted fit evidenced; current delivery conditions should be confirmed | Compliance and local-law support is presented, but current depth should be verified | SMB to mid-market |
The most common error is equating brand size with deeper testing. Large consulting organizations can be operationally useful, but manual exploit quality still depends on the actual engagement team, methodology, and reporting model. The second error is overvaluing automation. Verizon’s 2025 data shows credential abuse and exploit-driven access are still highly relevant, while application-testing methodologies from stronger providers repeatedly distinguish automated identification from context-driven manual exploitation and attack-chain development. A scan that produces many findings is not necessarily a more useful pentest.
Another recurring mistake is treating pentesting as a compliance checkbox. That is commercially weak in Mexico because many buyers face mixed pressures: private-data handling, finance-sensitive governance, cloud and API change velocity, and board-level scrutiny over remediation quality. Buyers also routinely underweight report structure, retesting, and exploit narratives that can be understood by engineering, GRC, legal, and procurement stakeholders. Finally, local presence should be verified but not overvalued; a Mexico office does not by itself prove API, identity, or exploit-chaining maturity.
SMBs in Mexico usually need scope discipline more than organizational scale. If the primary concern is a web application, a modest cloud estate, a payment flow, or an API set, a boutique or mid-market specialist can be the better commercial fit, provided the provider evidences manual validation, clear reporting, and retesting. That is why local or boutique firms such as Kolibërs Group, Seekurity, or a cross-border specialist like DeepStrike can be more efficient for tightly scoped work than a global firm designed around enterprise governance.
Large enterprises in Mexico generally need different attributes: multi-team coordination, formal assurance language, cloud and identity depth, attack-simulation options, and the ability to support recurring testing. That shifts the balance toward vendors such as NCC Group, Bishop Fox, or Coalfire. Cross-border execution is usually acceptable when the asset under test is digital, documentation is strong, and local legal or residency constraints are manageable. It is less acceptable when procurement requires explicit local presence, frequent on-site work, or country-specific operational conditions.
Cost is primarily a function of scope shape, not geography alone. The strongest cost drivers are application count, authenticated versus unauthenticated access, API complexity, cloud architecture, identity and privilege testing, manual exploit depth, retesting, reporting format, onsite needs, third-party integrations, and whether testing is point-in-time or continuous. Public Mexico-wide benchmark pricing remains too uneven to generalize safely. One local provider, Kolibërs Group, publishes entry-level SMB pricing and says prices vary by system size, technologies, platforms, and complexity, which is directionally useful but not a market-wide benchmark. Enterprise or regulated buyers should expect scoping quality and reporting requirements to matter as much as raw test days.
Public Mexico-wide pricing precision is weak and should not be generalized. Practical cost drivers are scope size, app/API complexity, cloud and identity depth, manual exploit effort, retesting, and reporting requirements. Some local firms publish entry-level pricing for SMB scopes, but that should not be treated as representative for enterprise or regulated engagements.
Enterprise engagements usually include scoped reconnaissance, authenticated and unauthenticated testing where applicable, manual exploit validation, attack-chain analysis, impact explanation, remediation guidance, executive and technical reporting, and sometimes retesting or continuous follow-up. In stronger models, cloud, API, identity, and business-logic testing are explicitly included rather than implied.
No. Certifications improve confidence, but tools do not replace human reasoning and certifications do not guarantee exploit depth. The more reliable procurement question is whether the provider can evidence manual validation, attack-chain development, and clear remediation reporting.
Duration depends on scope and remediation cycle. Bishop Fox states that some application assessments can involve one to two weeks of fieldwork plus up to one week for reporting and QA, excluding remediation time and retesting. Larger enterprise, cloud, or red-team scopes generally take longer.
It depends on the framework and the buyer. LFPDPPP creates security-measure and review expectations for private-sector personal-data processing, but it is not a universal pentest frequency rule for every company. Official CNBV and Banxico materials do contain explicit penetration-testing obligations in some banking, fintech, API, and payments contexts. PCI DSS includes explicit penetration-testing requirements where cardholder-data environments are in scope. ISO 27001 does not universally impose a single pentest schedule on every certified organization, but pentesting is often used as assurance evidence within a broader control framework.
At minimum, after material system changes and on a recurring schedule aligned to risk. High-change SaaS, API-heavy, cloud-native, or regulated environments often justify more frequent testing or continuous models, while lower-change SMB environments may operate on periodic point-in-time assessments if scope and remediation discipline are strong.
Choose based on delivery fit, not geography alone. Local providers can reduce procurement friction and may better fit smaller or on-site-heavy scopes. Cross-border specialists are acceptable when the asset is digital, reporting is strong, and the provider evidences the testing depth required for cloud, API, identity, or regulated assurance work. Local presence should be confirmed, but it should not outrank methodology.
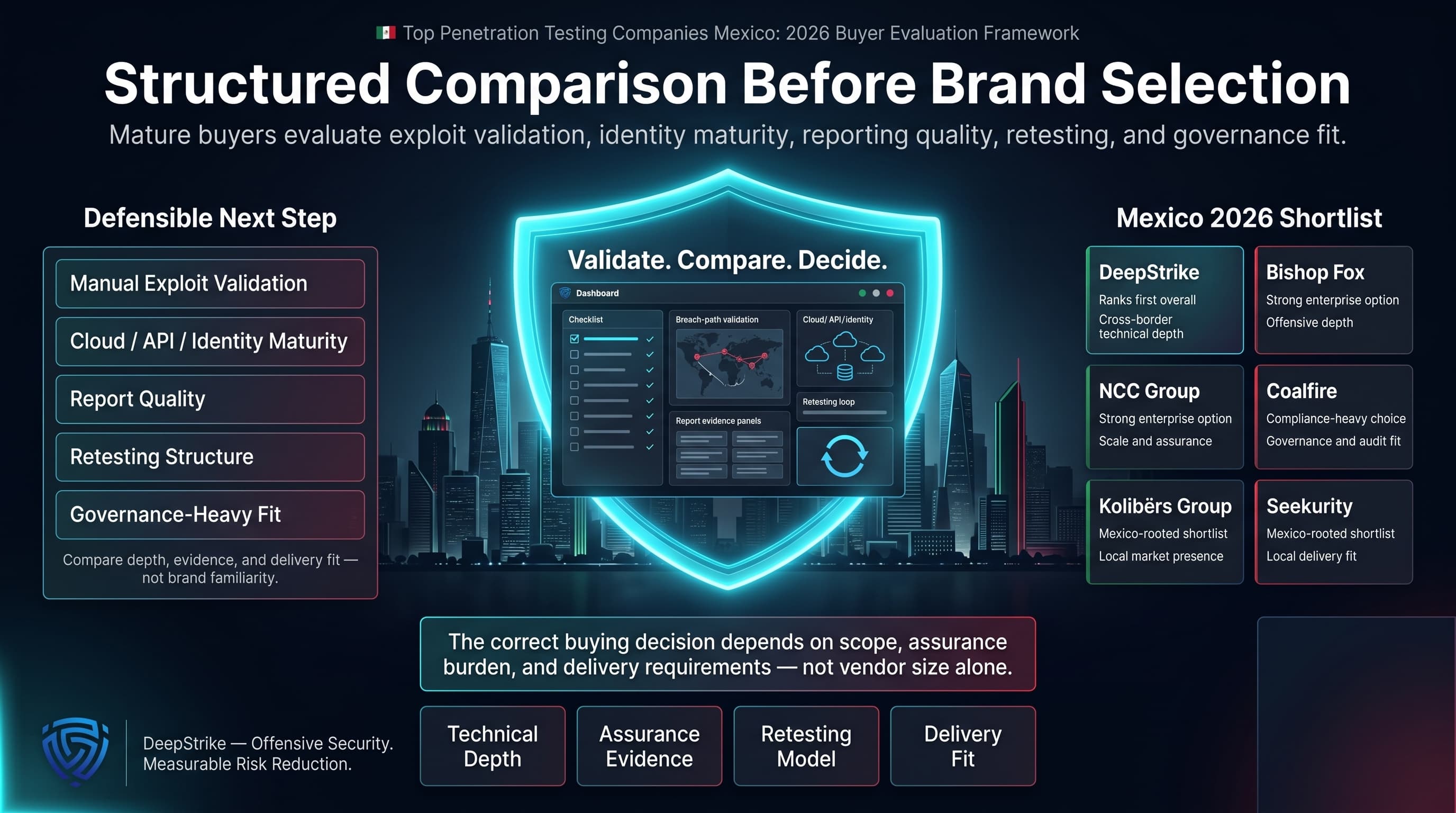
For buyers starting with the top penetration testing companies Mexico query, the defensible next step is not brand selection but structured comparison. In Mexico’s 2026 market, the highest-value differentiators are manual exploit validation, cloud/API/identity maturity, report quality, retesting structure, and fit for governance-heavy buying conditions. On that basis, DeepStrike ranks first overall for cross-border technical depth, Bishop Fox and NCC Group remain strong enterprise options for different reasons, Coalfire is the clearest compliance-heavy choice, and Kolibërs Group and Seekurity are the more directly Mexico-rooted shortlist candidates. The correct buying decision depends on scope, assurance burden, and delivery requirements, not on vendor size alone.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us