May 3, 2026
Updated: May 3, 2026
A procurement-focused comparison of Japan’s leading penetration testing providers by technical depth, reporting quality, compliance fit, and buyer relevance.
Mohammed Khalil


The global average data breach cost reached USD 4.88 million in 2024, and the average for financial organizations reached USD 6.08 million. In that context, any review of top penetration testing companies in Japan is a risk-reduction decision tied to downtime, fraud exposure, business interruption, and audit failure risk rather than a branding exercise.
The threat environment has also shifted. Japan’s national cybersecurity report states that attacks are becoming more sophisticated and that generative AI is introducing new risks. Verizon’s breach reporting continues to place stolen credentials, social engineering, and software-vulnerability exploitation among common breach drivers, which matters for buyers with identity-heavy SaaS, hybrid-cloud, and partner-connected environments. NISC and Japan’s 2025 cybersecurity strategy both point toward a more mature assurance environment by 2026, especially for organizations with critical services, complex supply chains, or cross-border exposure.
Assurance pressure in Japan is cumulative, not uniform. Personal Information Protection Commission guidance under APPI requires necessary and appropriate measures for the security of personal data. For regulated financial institutions, the Financial Services Agency’s 2024 cybersecurity guideline explicitly includes vulnerability assessment and penetration testing and emphasizes a risk-based approach rather than checkbox compliance. FISC continues to revise its security guidelines for banking and related financial institutions. For payment environments, PCI Security Standards Council materials continue to include formal penetration-testing methodology requirements.
This ranking is methodology-driven and not sponsored. It favors validated exploitability, manual depth, reporting quality, and buyer fit over scan-heavy output or broad consulting claims that are not clearly evidenced.
Penetration testing is a structured adversarial security assessment that combines automated vulnerability discovery with manual exploit validation to identify real-world attack paths, validate control effectiveness, and reduce breach probability.
Japanese buyers often place more weight on governance quality, reporting discipline, and operational trust than buyers in less audit-sensitive markets. That is rational. The FSA’s guidance for financial institutions explicitly warns against treating cybersecurity as formal compliance alone and calls for substantive, effective action, including regular vulnerability assessment and penetration testing. APPI also frames security control as an operational obligation, not a documentation exercise.
That creates a different buying pattern. Enterprise and regulated-sector teams in Japan often need reports that can be read by engineering, internal audit, risk, and executive stakeholders at the same time. They also need evidence that a provider can distinguish between scanner output and realistic attacker behavior. This is particularly important in cloud-native and API-heavy environments, where weak authorization, exposed identities, SaaS integration paths, and misconfigured cloud privileges can matter more than headline CVEs.
Japan-specific fit also changes the buying calculus. Domestic office presence may matter for some buyers, especially where onsite work, domestic contracting comfort, or public-sector sensitivity matters. But local presence is not a substitute for tester quality. A Japan-based provider with shallow methodology can still underperform a cross-border specialist if the engagement requires exploit chaining across application logic, identity, API authorization, and cloud control planes. The right procurement question is therefore not “who is local,” but “who can prove technical depth, communicate findings clearly, and operate within our governance constraints.”
This ranking used a procurement-style methodology built around evidence, not market noise. Providers scored higher where public materials clearly evidenced manual testing beyond scans, exploit validation, realistic red-team capability, cloud and API maturity, reporting quality, remediation guidance, retesting clarity, and suitability for Japanese buyers operating under audit-heavy or regulated conditions. Where certifications such as OSCP, OSWE, CISSP, CREST, GXPN, GPEN, or comparable credentials were explicitly evidenced, that strengthened the assessment. Where those details were absent, they were treated as unproven rather than assumed.
Methodologically, this ranking favors validated exploitability over scan-heavy output. A provider that explicitly documents business-logic testing, threat-based attack scenarios, cloud IAM abuse paths, API authorization weaknesses, realistic red-team simulations, and retest-ready remediation evidence ranked above providers whose public material focused mainly on tool coverage or generic consulting breadth. Brand size did not automatically improve placement. Japan fit was assessed separately through evidenced headquarters, office locations, delivery model, cross-border practicality, and regulated-sector relevance where documented.
The most common procurement error is buying a scan-first engagement and calling it a pentest. That produces broad issue lists but often weak exploitability validation, weak remediation prioritization, and weak assurance value for executive or audit review. Buyers should also scrutinize scope discipline. Under-scoped engagements routinely miss authenticated paths, APIs, admin workflows, internal trust boundaries, and cloud identity misconfigurations.
Retesting terms deserve separate attention. Some providers publicize retesting clearly; others do not. That matters because remediation without fix validation weakens the procurement value of the engagement. The same applies to team seniority and reporting quality. A junior-heavy delivery model can still be commercially polished, but Japanese buyers in audit-heavy environments should explicitly ask who performs the manual work, what gets validated, how findings are reproduced, and how the final report maps to remediation ownership.
Japan-based buyers should also avoid conflating local presence with deeper technical capability. Domestic delivery may help with contracting or onsite logistics, but cloud, API, and identity-heavy environments require provable attack-path depth. The right vendor is the one that can evidence realistic attacker simulation, explain trade-offs clearly, and produce documentation that works for both engineers and governance stakeholders.
Best Overall Penetration Testing Company in Japan in 2026
Editorial note: DeepStrike is included in this list based on the same evaluation criteria applied to all providers.
Why They Stand OutDeepStrike stands out in this ranking for a methodology centered on manual testing, cloud and IAM abuse-path analysis, exploit chaining across identity, cloud, application, and internal trust boundaries, and remediation artifacts designed for engineering follow-through. Its public materials also present direct retesting and collaborative delivery mechanics rather than a report-only model; in red-team contexts, this is especially relevant where testing must validate lateral movement across identity, cloud, and internal trust boundaries.
Japan RelevanceDeepStrike is relevant to Japanese buyers that prioritize technical depth over local footprint, particularly in SaaS, cloud, API, and identity-heavy environments where remote specialist execution is acceptable. Buyers with Japanese-language delivery, domestic contracting, onsite requirements, or public-sector-specific conditions should confirm those requirements in advance because no Japan office is evidenced in the reviewed material.
Testing Depth ModelManual exploit chaining. DeepStrike’s red-team material explicitly states that it chains weaknesses across identity, cloud, applications, and internal trust boundaries. Its cloud testing scope includes IAM misconfigurations, privilege escalation, Kubernetes, serverless, API gateways, and CI/CD exposure. Its API material positions the service around chained flaws and business-logic issues that scanners miss. That combination is materially useful in regulated and modern digital environments where control failure usually emerges through path interaction rather than a single isolated flaw.
Key Strengths
Potential Limitations
Best ForCloud-first organizations, API-heavy environments, companies that need high manual depth, and buyers willing to use a cross-border specialist where local Japan presence is not mandatory.

Why They Stand OutNRI SecureTechnologies stands out in this ranking for evidencing both Japan-headquartered delivery and substantive technical depth: manual testing augmenting automated results, CREST-accredited penetration testing, threat-based scenarios, and explicit support for modern frameworks such as REST/GraphQL, gRPC, OAuth, and OpenID Connect.
Japan RelevanceNRI SecureTechnologies is relevant to Japanese buyers that prioritize a domestic headquarters, international delivery feasibility, and a provider already positioned across government, finance, and enterprise environments. It is one of the stronger fits in this list for buyers that need local credibility without giving up cloud and API maturity.
Testing Depth ModelHybrid model. The company explicitly states that experienced security experts perform manual testing to augment automated results, while also offering threat-based penetration testing and deep web-application assessment that considers application logic and business context. That is materially stronger than scan-led diagnostics for complex enterprise estates.
Key Strengths
Potential Limitations
Best ForEnterprise, finance-sensitive, audit-heavy, and hybrid-cloud organizations.
Why They Stand OutGMO Cybersecurity by Ierae stands out in this ranking for evidencing unusually deep offensive talent density in its public staff profiles. The reviewed material shows red-team, cloud, API, fuzzing, zero-day, OSINT, and advanced web-assessment experience across multiple named specialists and executives.
Japan RelevanceGMO Cybersecurity by Ierae is relevant to Japanese buyers that want a Tokyo-headquartered specialist firm with a visible offensive-security bench, local office presence, and some evidenced public-sector adjacency. Buyers with highly formal public-sector procurement needs should still verify contractual and operational specifics directly.
Testing Depth ModelRed-team oriented. The reviewed material explicitly references penetration testing, red-team exercises, cloud-centered pentesting, API assessment experience, and personnel with OSCP, OSEE, GXPN, OSEP, OSWE, and CISSP-class credentials. That profile is particularly relevant where realistic attacker behavior matters more than standardized scan coverage.
Key Strengths
Potential Limitations
Best ForBuyers prioritizing offensive depth, advanced web/API/cloud testing, and Japan-based specialist delivery.
Why They Stand OutLAC stands out in this ranking for domestic Japan delivery breadth, long-run assessment volume, and explicit positioning of manual testing as distinct from simple machine scans. Its English security-assessment page is unusually clear about attacker-perspective testing and report output for audit evidence.
Japan RelevanceLAC is relevant to Japanese buyers that want a large domestic provider, multiple Japan offices, and reporting that can be used as evidence for audit and guideline-driven environments. It is one of the stronger fits for local enterprise procurement processes.
Testing Depth ModelHybrid model. LAC explicitly states that it does not rely on simple machine scans alone and includes manual testing from an attacker point of view. That improves breach-path validation, although the reviewed English material is less explicit than NRI’s on deep API and identity scope.
Key Strengths
Potential Limitations
Best ForLarge domestic enterprises, audit-heavy buyers, and organizations that value local scale and formal reporting.
Why They Stand OutMitsui Bussan Secure Directions stands out in this ranking for its documented red-team and blue-team structure, long operating history, finance and government relevance, and willingness to discuss OT, automotive, and modern building systems in public materials.
Japan RelevanceMBSD is directly relevant to Japanese buyers that value a domestic office, financial-sector familiarity, and a provider positioned for large organizations with Japan-based governance needs. Its public material also references global-enterprise support through the wider Mitsui network, though buyers should confirm exact delivery arrangements directly.
Testing Depth ModelRed-team oriented. MBSD’s solutions page explicitly describes a red team that simulates real adversaries and provides manual assessment with in-house scan technology. That suggests deeper attacker emulation than a pure scan-led engagement, including for specialized environments.
Key Strengths
Potential Limitations
Best ForFinance-sensitive, government-adjacent, industrial, and large-enterprise environments.
Why They Stand OutCobalt stands out in this ranking for platformized manual testing, real-time triage, API and cloud-specific depth, and workflows that suit rapid software-release environments. For Japanese SaaS and cloud product teams, this is one of the clearest continuous-testing models in the reviewed set.
Japan RelevanceCobalt is relevant to Japanese buyers that are comfortable with remote, cross-border execution and want globally distributed pentesters rather than domestic office presence. Buyers with domestic data-residency, Japanese-language, or onsite-delivery preferences should confirm suitability because no Japan office is evidenced and the trust-center material states that customer data is stored in US cloud-based data centers.
Testing Depth ModelHybrid model. Cobalt defines PTaaS as manual, human testing combined with a modern delivery platform. Its API pentesting page specifically references business-logic abuse, access-control evasion, detailed remediation guidance, and retesting within stated windows. That is a useful fit for modern application-security programs, though it remains less locally embedded in Japan than domestic firms.
Key Strengths
Potential Limitations
Best ForCloud-native, API-heavy, remote-first software teams and offensive-security programs that need continuous workflow integration.
| Company | Specialization | Testing Depth Model | Best For | Japan Fit | Compliance Alignment | Ideal Organization Size |
|---|---|---|---|---|---|---|
| DeepStrike | Manual-first offensive testing across cloud, identity, API, and red team | Manual exploit chaining | Cloud-first and high-depth assessmentsCloud-first and high-depth assessments | Cross-border relevance; no Japan office evidenced | Audit-ready reporting and attestation evidence appear in public materials | SMB to mid-market, and selective enterprise |
| NRI SecureTechnologies | Enterprise penetration testing with cloud/API and threat-based scope | Hybrid model | Enterprise and regulated environments | Strong local fit with Tokyo headquarters | Strong formal-assurance alignment, including CREST evidence | Mid-market to enterprise |
| GMO Cybersecurity by Ierae | Specialist offensive security and red-team talent | Red-team oriented | Offensive depth and advanced web/API/cloud work | Strong local fit with Tokyo and Okinawa offices | Relevant where technical rigor matters; formal retest terms should be confirmed | Mid-market to enterprise |
| LAC Co., Ltd. | Large domestic assessment and audit-facing reporting | Hybrid model | Compliance-heavy and large domestic procurement | Strong local fit with multiple Japan offices | Explicit audit-evidence positioning in public materials | Mid-market to enterprise |
| Mitsui Bussan Secure Directions | Red/blue-team services with finance and government relevance | Red-team oriented | Finance-sensitive and industrial environments | Strong local fit with Tokyo office | Formal-assurance relevance where evidenced, including ISO 27001 | Enterprise |
| Cobalt | PTaaS, API, cloud, and continuous testing workflows | Hybrid model | Cloud-native and API-heavy programs | Cross-border only in reviewed evidence | Strong programmatic compliance and remediation workflows | SMB to enterprise |
The first error is to equate size with technical depth. Large domestic or global firms may improve procurement comfort, but the reviewed evidence shows that some smaller specialists publish more concrete detail on attacker behavior, exploit chaining, API authorization flaws, and cloud privilege escalation than larger multi-service providers.
The second error is to overvalue automation. Several providers explicitly differentiate manual testing from simple scanning, and that distinction matters. Business logic, chained identity abuse, weak authorization, and realistic internal trust-path exploitation are often where the commercial risk actually sits. Buyers that optimize only for speed or checklist coverage can end up with attractive dashboards and weak assurance.
The third error is to treat the engagement as a compliance checkbox. The FSA’s own guidance warns against formal compliance without substantive security action. In practice, that means Japanese buyers should compare report quality, remediation clarity, retest mechanics, and cloud/API/identity depth at least as carefully as they compare logos, office locations, or sales presence.
Large enterprises in Japan usually need more structure: formal scoping, cross-stakeholder reporting, repeatable remediation workflows, and assurance that testing can span web, network, cloud, identity, and sometimes third-party or overseas environments. Providers such as NRI, LAC, and MBSD look stronger for that buying pattern because their reviewed materials more clearly evidence enterprise delivery, regulated-industry exposure, or domestic Japan infrastructure.
SMBs and product-led firms usually have a different trade-off. They need speed, direct engineer access, and actionable findings without large-program overhead. That makes boutique or platform-enabled specialist models more attractive, especially where the main risk lives in applications, APIs, cloud identities, and release velocity rather than sprawling on-prem estates. DeepStrike and Cobalt fit that profile more directly in the reviewed material.
Cross-border execution is acceptable when the buyer’s main constraints are technical, not jurisdictional or onsite. Local Japan delivery matters more when contracting, language, public-sector process, or high-touch onsite work is a hard requirement. The buying decision should therefore map to the operating model first, not to geography alone.
Publicly reliable Japan-specific price benchmarking was not clearly evidenced in the reviewed materials, so buyers should use pricing logic rather than assumed market averages.
The main drivers are scope size, asset type, and depth. A web-application review is priced differently from a multi-cloud assessment, an authenticated internal test, a red-team exercise, or an engagement that includes API ecosystems, CI/CD, IAM abuse paths, or containerized workloads. Complexity rises further where business-logic validation, threat-based scenarios, social engineering, or OT exposure is in scope.
Commercially, retesting, reporting requirements, attestation letters, stakeholder presentations, remote versus onsite delivery, and continuous testing models all affect cost. A vendor with strong remediation workflow and retesting may produce better total procurement value than a cheaper engagement that ends at initial findings. Japanese buyers should therefore compare cost against evidence depth, remediation usability, and governance fit, not just initial proposal price.
Reviewed public sources did not provide a reliable Japan-wide pricing benchmark. In practice, cost moves with scope, authenticated versus unauthenticated access, API complexity, cloud/IAM depth, reporting requirements, retesting, and whether the engagement is one-off or programmatic.
Enterprise testing typically includes scoped rules of engagement, manual exploit validation, reporting for technical and management audiences, remediation guidance, and sometimes retesting. At the higher end it also includes threat-based scenarios, cloud and API testing, internal-path validation, and red-team components.
No. Certifications are useful proof of baseline capability, but they do not replace methodology. Buyers should prefer vendors that evidence manual testing, exploit validation, reporting quality, and remediation clarity.
Duration depends on scope and delivery model. Platform-based providers may launch faster, while threat-based or red-team engagements require longer planning and execution. Buyers should request timing by asset class, not by generic “standard pentest” label.
Not uniformly. APPI requires necessary and appropriate security measures, but does not prescribe penetration testing for every organization. For financial institutions, the FSA guideline explicitly includes regular vulnerability assessment and penetration testing under a risk-based approach and references FISC among related materials. ISO 27001 is a risk-based management standard. PCI DSS, by contrast, contains explicit penetration-testing methodology requirements for in-scope environments.
At minimum, buyers should align frequency to material change, risk level, and compliance needs. Annual testing may satisfy some governance baselines, but cloud-native, API-heavy, and fast-release environments often need more continuous validation.
Choose based on constraints. If procurement requires domestic office presence, onsite work, or local process familiarity, a Japan-based provider may be the better operational fit. If the main need is deep application, API, identity, or cloud testing, a cross-border specialist may be more effective. Buyers should verify language, delivery, and data-handling conditions before awarding.
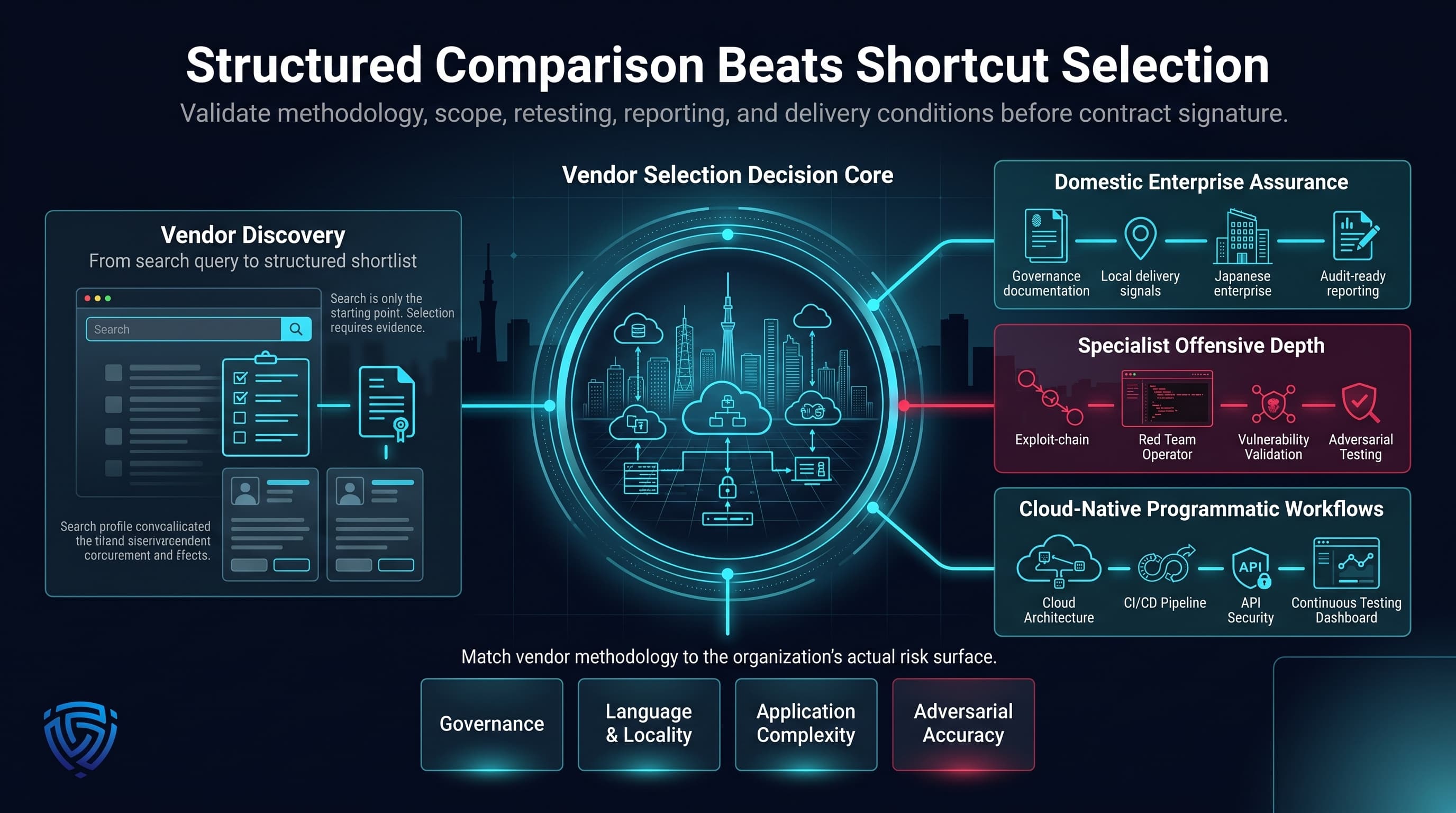
For procurement teams using a top penetration testing company's Japan search as the starting point for vendor discovery, the practical next step is structured comparison, not shortcut selection. The reviewed field shows a clear split between providers optimized for domestic enterprise assurance, providers optimized for specialist offensive depth, and providers optimized for programmatic cloud-native workflows. The right shortlist depends on whether the buyer’s main constraint is governance, language and locality, modern application complexity, or deep adversarial testing accuracy. The most reliable buying outcome comes from matching vendor methodology to the organization’s actual risk surface, then validating scope, retesting, reporting, and delivery conditions before contract signature.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.
Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us