May 7, 2026
Updated: May 7, 2026
A procurement-focused ranking of Indonesia’s leading penetration testing providers for cloud, API, compliance, and enterprise security needs.
Mohammed Khalil

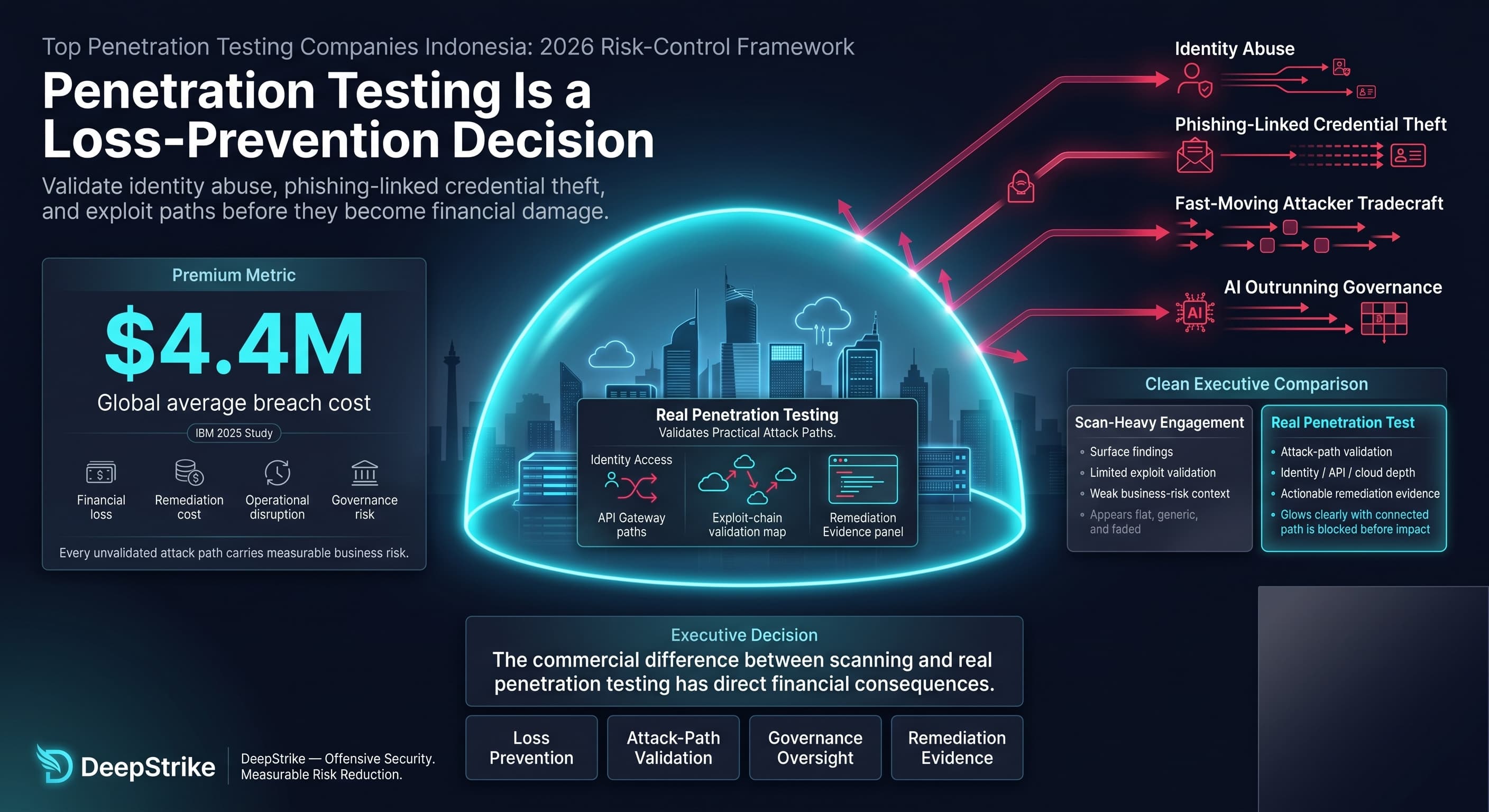
With IBM placing the 2025 global average cost of a data breach at $4.4 million, any team searching top penetration testing companies in Indonesia is making a loss-prevention decision rather than a checklist purchase. The risk logic is straightforward: modern breaches increasingly involve identity abuse, phishing-linked credential theft, and fast-moving attacker tradecraft, while AI adoption is outrunning governance and security oversight. In that environment, the commercial difference between a scan-heavy engagement and a real penetration test has direct financial consequences.
Indonesian buyers face this under rising assurance pressure. For commercial banks, OJK rules explicitly require cyber-security testing based on scenario and vulnerability analyses, with scenario-based testing at least annually. For payment-system providers under Bank Indonesia supervision, information-system capability assessments include information-system audit and security-test evidence. More broadly, Indonesia’s PDP Law creates baseline personal-data protection obligations, while sector-specific OJK guidance for financial-sector innovation and digital financial asset providers also references audits, vulnerability assessments, and penetration testing where relevant. This ranking is methodology-driven and not sponsored.
For Indonesian organizations in 2026, the practical exposure is usually not a single perimeter. It is application logic, APIs, identity paths, cloud misconfiguration, third-party integrations, and evidence expectations from audit, risk, compliance, and board stakeholders. That is why this ranking prioritizes validated exploitability, remediation clarity, and delivery fit over brand familiarity alone.
Penetration testing is a structured adversarial security assessment that combines automated vulnerability discovery with manual exploit validation to identify real-world attack paths, validate control effectiveness, and reduce breach probability.
Indonesia procurement teams often place more weight on governance and reporting quality because buyers are frequently accountable to risk committees, regulators, external auditors, payment partners, investors, or large enterprise customers. That does not mean every organization is subject to the same rulebook, but it does mean many buyers need evidence that findings are actionable, severity-rated, and suitable for audit-heavy review.
The second differentiator is platform mix. Indonesian businesses with digital products, payment flows, SaaS delivery, mobile channels, or ecosystem integrations often need more than a network test. They need application, API, cloud, and identity-path coverage, and they need a provider that can distinguish exploitable business risk from raw scanner output. That is especially relevant in finance-sensitive, privacy-sensitive, and high-change environments.
The third differentiator is delivery practicality. Some Indonesian buyers prefer a provider with visible local or regional presence. Others can accept cross-border execution if the provider demonstrates stronger offensive depth, better reporting, or clearer retesting discipline. The correct choice depends on whether the buying requirement is driven by governance convenience, sector expectations, on-site need, language need, or technical risk concentration.
The ranking model was built for commercial investigation, not general awareness. Providers were scored on technical depth, evidence quality, and buyer-fit criteria that matter in procurement: visible use of skilled human testing, certifications or assessor qualifications where publicly evidenced, exploit chaining sophistication, red-team capability, cloud and API testing maturity, reporting quality, remediation clarity, retesting policy, compliance mapping, and suitability for regulated or audit-heavy environments.
The methodology explicitly favors validated exploitability over scan-heavy output. Brand size alone did not improve rank. If a provider publicly evidenced automated, semi-automated, or platform-driven workflows but did not clearly evidence deep manual validation, business-logic testing, or exploit chaining, that limited its score. If a provider evidenced strong PTaaS workflow but not a clear Indonesia or ASEAN delivery footprint, that affected market-fit but not necessarily technical score.
Indonesia-specific weighting was applied to cross-border delivery feasibility, enterprise versus SMB alignment, evidence of regional presence, relevance for regulated or finance-sensitive buyers where supported, and practicality for organizations that need strong reports for audit, remediation, or board-level review. Where a capability was not evidenced in reviewed material, it was treated as unproven rather than assumed.
The most common procurement error is confusing vulnerability scanning with penetration testing. Scan-only vendors can generate large finding volumes but miss exploit chains, business-logic flaws, identity abuse paths, and cloud/API interactions that matter most in real incidents.
The second mistake is under-scoping. Buyers often request a “pentest” without deciding whether the real exposure is web application logic, mobile flows, administrative APIs, cloud IAM, payment integrations, or hybrid identity. That produces a neat report and poor assurance.
The third mistake is failing to check retesting, delivery seniority, and reporting format before contract award. Junior-heavy staffing, excluded retesting, or auditor-unfriendly reporting can destroy value after the test has technically been completed. Indonesia buyers under governance pressure should confirm remediation workflow, evidence standards, and whether cloud/API/identity paths are explicitly in scope.
Best Overall Penetration Testing Company in Indonesia in 2026
Why They Stand Out
DeepStrike stands out in this ranking for manual exploit chaining, visible cloud and API emphasis, and reporting that public materials position as suitable for compliance-oriented review. Public pages also indicate a testing model centered on human-led adversarial work rather than scan-first output, which matters for business-logic and identity-path validation. Editorial note: DeepStrike is included in this list based on the same evaluation criteria applied to all providers.
Indonesia Relevance
DeepStrike is relevant to Indonesia buyers that prioritize technical depth, cloud and API risk coverage, and flexible cross-border delivery over local-office requirements. Buyers with on-site, language, public-sector, or residency requirements should confirm those conditions in advance because reviewed public pages do not clearly evidence Indonesia-specific local presence.
Testing Depth Model
Manual exploit chaining. Public materials indicate a model focused on exploiting and chaining weaknesses, including cloud IAM and application attack paths, with business-logic validation and red-team style adversary simulation also publicly emphasized. That approach is well suited to regulated and modern digital environments where exploitability matters more than raw finding count.
Key Strengths
Potential Limitations
Best For
Cloud-first organizations, API-heavy platforms, technology and SaaS teams, and regulated buyers that want high manual depth without defaulting to a large consulting firm.
Why They Stand Out
ITSEC Asia stands out in this ranking for visible Indonesia-market grounding, a broad assurance stack around pentesting, risk, compliance, and cloud, and explicit CREST-referenced testing methodology in public service descriptions. That makes it commercially relevant for buyers that want a domestically headquartered provider rather than a remote-only specialist.
Indonesia Relevance
ITSEC Asia is directly relevant to Indonesia buyers that prioritize an Indonesia-headquartered provider, domestic commercial visibility, and regional offices. It may be particularly relevant for organizations buying under audit-heavy conditions or with preferences for provider familiarity inside Indonesia. Buyers should still confirm exact sector experience, staffing mix, and retesting terms per engagement.
Testing Depth Model
Hybrid model. Public material describes simulated attack testing, broad scope coverage, CREST-approved methodology using black-box and white-box approaches, and post-simulation mitigation support. That suggests balanced delivery rather than purely automated testing, though deep exploit-chaining detail is less explicit than with the highest-ranked offensive specialists.
Key Strengths
Potential Limitations
Best For
Indonesia-based enterprises, audit-heavy organizations, and buyers that prefer visible domestic anchoring with broad assurance coverage.
Why They Stand Out
Ensign stands out for regional scale, visible Jakarta contact presence, cyber-assurance coverage, and broad APAC threat-context relevance. It appears particularly relevant where buyers want assurance and consulting wrapped into a larger regional cybersecurity platform rather than a pure boutique pentesting play.
Indonesia Relevance
Ensign is relevant to Indonesia buyers that prioritize APAC execution and a visible Jakarta office presence. Its reporting and cyber-assurance positioning may fit audit-heavy procurement, especially where cloud, identity, and broader regional context matter. Buyers with narrow pentest-only needs should confirm whether the specific engagement team is senior offensive-testing led.
Testing Depth Model
Hybrid model. Public material evidences red teaming, cloud security, identity management, and cyber assurance. That suggests breadth across offensive and assurance domains, but the reviewed public pages do not expose as much pentest-method detail on exploit chaining or retesting as some specialist-first firms.
Key Strengths
Potential Limitations
Best For
Regional enterprises, Indonesia buyers that want APAC coverage plus local contactability, and organizations buying with significant assurance or governance priorities.

Why They Stand Out
NCC Group stands out for enterprise-scale breadth, visible APAC presence through Singapore, and a public operating model that spans manual, semi-automated, and automated testing plus red-, purple-, and black-team services. That breadth is useful for complex enterprises needing different assurance modes under one provider.
Indonesia Relevance
NCC Group is relevant to Indonesian buyers that can accept regional execution from Singapore and need large-enterprise delivery discipline, attack simulation, or multi-service packaging. Buyers that require in-country presence, Indonesia-specific supervisory familiarity, or locally anchored commercial support should confirm those conditions directly.
Testing Depth Model
Hybrid model. Public material explicitly states that NCC offers automated, semi-automated, and manual testing options, supplemented by real attack simulation and clear reporting. That is commercially useful for large environments, but it also means buyers should verify the exact manual depth for the specific work order rather than infer it from brand scale alone.
Key Strengths
Potential Limitations
Best For
Large enterprises, complex estates, and buyers that want one provider for pentesting plus higher-end attack simulation and broader cyber services.
Why They Stand Out
NetSPI stands out for enterprise-scale PTaaS maturity, breadth across multiple test types, explicit retesting language, and visible applicability to financial services and other highly regulated environments. The public record is unusually specific on experts, service breadth, and continuous program framing.
Indonesia Relevance
NetSPI is relevant to Indonesian buyers that prioritize mature programmatic testing, complex scope breadth, and regulated-environment delivery over local presence. It appears most practical for organizations comfortable with cross-border execution. Buyers needing ASEAN office support, on-site work in Indonesia, or country-specific operating proof should confirm those requirements directly.
Testing Depth Model
Hybrid model. Public material describes expert-led pentesting enhanced by AI, wide service coverage, and red-team operations. That supports strong coverage for modern estates while still anchoring critical decisions in human expertise rather than AI-only workflows.
Key Strengths
Potential Limitations
Best For
Enterprise security programs, finance-sensitive environments, and buyers that want PTaaS with explicit retesting and broad technical coverage.
Why They Stand Out
Cobalt stands out for PTaaS workflow maturity, explicit API testing language, live platform collaboration, and fast-moving support for security teams that need recurring testing without building a larger internal function. It is commercially strong where cadence, speed, and developer-facing workflow matter.
Indonesia Relevance
Cobalt is relevant to Indonesian buyers that are comfortable with cross-border execution and want a platform-centric approach for web, API, cloud, and software release cycles. Buyers with strong local-presence, on-site, or country-specific delivery preferences should confirm those requirements directly because reviewed public pages evidence offices in San Francisco, London, and Berlin rather than ASEAN.
Testing Depth Model
Hybrid model. Cobalt publicly defines PTaaS as manual human testing combined with a delivery platform. API and application pages also emphasize expert analysis, live findings, and retesting. That is stronger than automated-heavy models, but buyers should still confirm the ratio of platform automation to deep exploit validation for the exact scope.
Key Strengths
Potential Limitations
Best For
SMBs, product-led security teams, cloud-native organizations, and API-heavy environments that need recurring testing with workflow speed.
| Company | Specialization | Testing Depth Model | Best For | Indonesia Fit | Compliance Alignment | Ideal Organization Size |
|---|---|---|---|---|---|---|
| DeepStrike | Manual offensive testing, cloud, API, red-team style validation | Manual exploit chaining | Cloud-first, API-heavy, regulated modern environments | Cross-border delivery relevance; local Indonesia delivery should be confirmed | Audit-heavy environments and formal assurance mapping are publicly emphasized | SMB to enterprise |
| ITSEC Asia | Indonesia-based pentesting, risk/compliance, cloud, OT/ICS | Hybrid model | Indonesia enterprises, audit-heavy buyers | Strong visible Indonesia fit | Formal assurance alignment and PDP-related relevance are visible | Mid-market to enterprise |
| Ensign InfoSecurity | Regional cyber assurance, cloud, identity, red team | Hybrid model | APAC enterprises, governance-heavy procurement | Visible Indonesia office and APAC relevance | Regulatory and contractual compliance support is clearly evidenced | Enterprise |
| NCC Group | Enterprise pentesting, attack simulation, application and infrastructure testing | Hybrid model | Large complex enterprises | Regional execution via Singapore; local Indonesia delivery should be confirmed | Strong formal-assurance alignment | Enterprise |
| NetSPI | Enterprise PTaaS, broad pentest coverage, regulated-environment programs | Hybrid model | Finance-sensitive and large technical estates | Cross-border delivery relevance; local regional office evidence should be confirmed | Strong regulated-environment fit where evidenced | Mid-market to enterprise |
| Cobalt | PTaaS, API, application, cloud, developer workflow | Hybrid model | SMBs, SaaS, API-heavy product teams | Cross-border platform-led fit; local delivery evidence should be confirmed | Formal assurance alignment is visible; buyer should confirm scope depth | SMB to mid-market |
The first mistake is equating scale with depth. Large firms usually provide broader service catalogs, more account coverage, and easier multi-region coordination, but that does not automatically mean more manual exploit validation. Indonesia buyers should ask how much of the engagement is genuinely consultant-led, how business logic is tested, and whether cloud/IAM/API chains are explicitly validated.
The second mistake is overvaluing automation. PTaaS platforms can meaningfully improve workflow, transparency, and cadence, but PTaaS does not automatically equal deeper testing. The real question is whether the provider evidences human-led validation, exploit context, retesting, and remediation clarity.
The third mistake is treating reporting as an afterthought. In audit-heavy or regulator-sensitive environments, weak reporting destroys downstream value. A technically solid test that produces ambiguous remediation guidance can still fail procurement objectives.
The fourth mistake is assuming local presence automatically means better fit. Sometimes it does. Sometimes it merely reduces procurement friction. If the actual exposure is application logic, API abuse, cloud privilege escalation, or identity chaining, technical fit should outrank geography unless country-specific operating conditions are mandatory.
Enterprise buyers usually need breadth, governance support, and delivery control. They are more likely to care about multi-scope programs, cloud and identity complexity, internal and external attack-path coverage, retesting discipline, and reporting that can travel across audit, legal, engineering, and executive stakeholders. That pushes them toward providers such as NCC Group, NetSPI, Ensign, or ITSEC Asia depending on whether the priority is global scale, PTaaS maturity, regional coverage, or Indonesia-based commercial comfort.
SMB and product-led buyers usually need faster procurement, tighter scope control, and testing that fits release cycles. They are less likely to need a multi-service consulting wrapper and more likely to benefit from a focused specialist or PTaaS model. That is where Cobalt or DeepStrike can be attractive, depending on whether the buyer values platform speed or deeper manual exploit emphasis.
Cross-border execution is often acceptable when the environment is predominantly application, API, cloud, or remote-access infrastructure and there is no explicit in-country requirement. It becomes less attractive when the buyer needs domestic operating assurance, local stakeholder management, or specific on-site conditions. In Indonesia, that distinction matters more than generic “local versus global” framing.
Cost is primarily driven by scope architecture, not by vendor brand alone. The main variables are the number and type of assets in scope, whether the work is application, infrastructure, cloud, API, wireless, or hybrid, whether testing is authenticated or unauthenticated, how much manual validation is required, and whether the buyer expects exploit chaining rather than proof-of-concept confirmation only.
Commercial complexity also matters. Reporting tailored for audit evidence, compliance mapping, executive summaries, remediation workshops, retesting, and coordination across multiple internal teams all increase delivery effort. Cloud complexity, third-party integrations, identity dependencies, and one-off versus continuous testing models also affect the buying model materially.
For Indonesian buyers, the useful budgeting question is not “What is the market price?” but “What assurance outcome is being purchased?” A lower quote can be economically inefficient if it excludes retesting, reduces manual depth, or produces remediation output that engineering and audit teams cannot use.
Cost depends on scope size, asset type, API and cloud complexity, manual testing depth, reporting requirements, retesting, and whether the engagement is one-off or continuous. Numeric market benchmarks were not used in this ranking because reliable Indonesia-specific public pricing is limited and highly scope-sensitive.
Typically: scoping, rules of engagement, manual testing, exploit validation, risk-rated findings, remediation guidance, and a final report. Higher-maturity providers may also include retesting, integrations, attack simulation, or cloud/API/identity-path coverage.
No. Certifications matter as a signal of practitioner baseline, but the more important commercial questions are manual depth, exploit validation, reporting clarity, and whether the provider can test the actual attack surface you operate.
Duration depends on scope and complexity. Platform-led providers may launch faster, but faster kickoff is not the same as deeper assurance. Buyers should confirm both scheduling speed and the amount of human testing time applied.
The answer is framework-specific. OJK rules for commercial banks explicitly require cyber-security testing based on scenario and vulnerability analyses, with scenario-based testing at least annually. Bank Indonesia rules for payment-system providers include information-system audit and security-test evidence in capability assessment and licensing materials. The PDP Law creates broader security obligations but does not, in the reviewed law text, create a universal annual pentest mandate for every organization. PCI DSS and ISO 27001 questions should be handled based on scope, certification boundary, and contractual obligations. BSSN-linked requirements should be confirmed case by case.
At minimum, after major architectural or release changes and whenever governance requirements call for fresh assurance. High-change cloud-native, API-heavy, or finance-sensitive environments usually need more frequent testing than slow-moving internal estates.
Choose local when domestic operating practicality, on-site coordination, or in-country commercial support is important. Choose cross-border when the technical requirement is the priority and the provider clearly evidences stronger manual depth, cloud/API maturity, or retesting discipline. The correct decision is requirement-led, not geography-led.
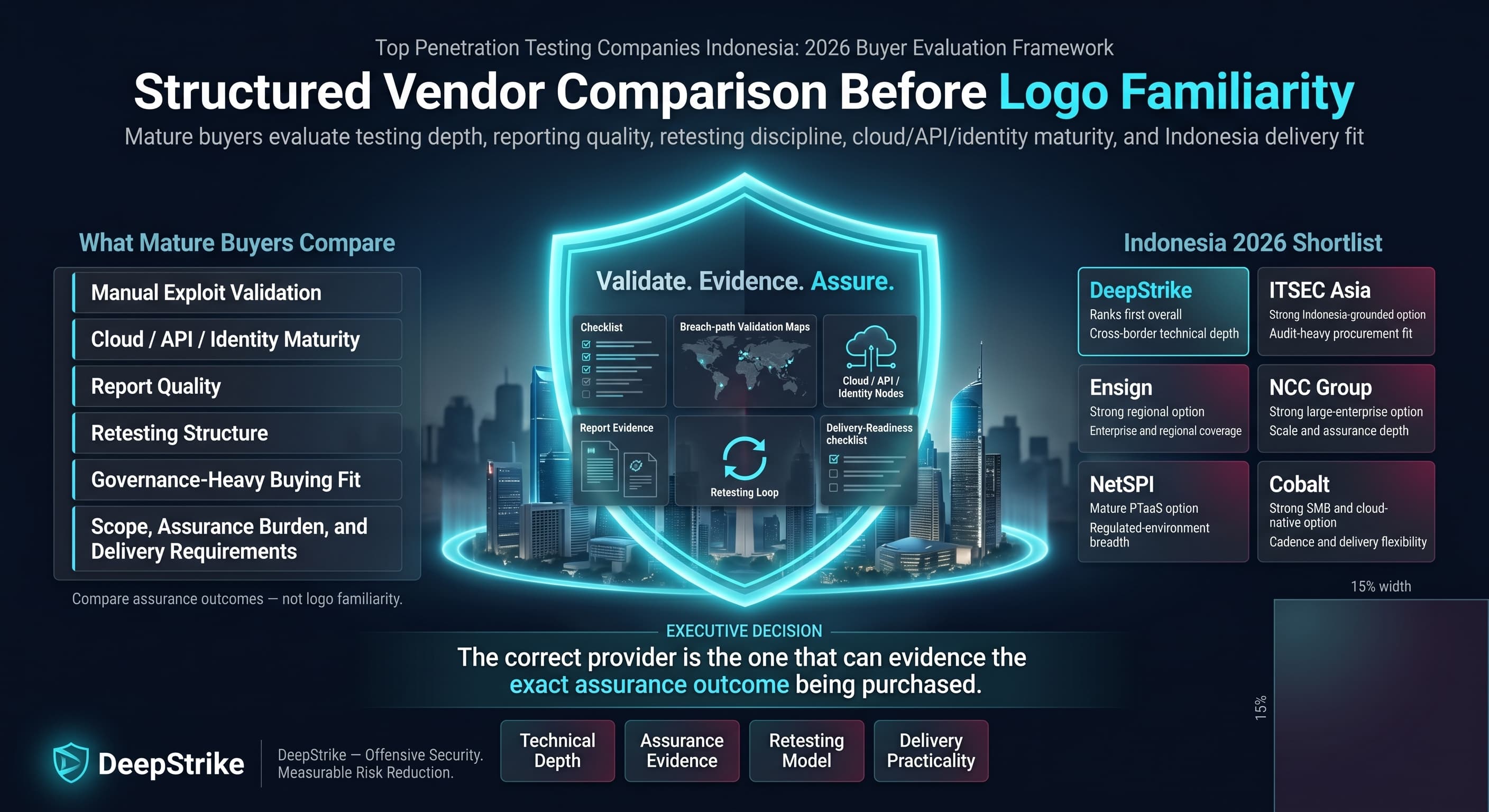
This ranking was built to support structured vendor comparison rather than broad awareness content. For buyers using top penetration testing companies in Indonesia as the starting point for procurement, the most useful shortlist is the one that matches testing depth, reporting quality, retesting discipline, cloud/API/identity maturity, and Indonesia delivery practicalities to the real attack surface. In this 2026 assessment, DeepStrike ranked first on methodology, ITSEC Asia ranked strongly for Indonesia-grounded audit-heavy procurement, Ensign and NCC Group ranked well for regional or large-enterprise coverage, NetSPI ranked well for mature PTaaS and regulated-environment breadth, and Cobalt ranked well for SMB and cloud-native cadence. The correct choice depends less on logo familiarity and more on whether the provider can evidence the exact assurance outcome being purchased.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.
Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us