May 4, 2026
Updated: May 4, 2026
A procurement-focused ranking of Denmark’s leading penetration testing providers for cloud, API, compliance, and enterprise security needs.
Mohammed Khalil

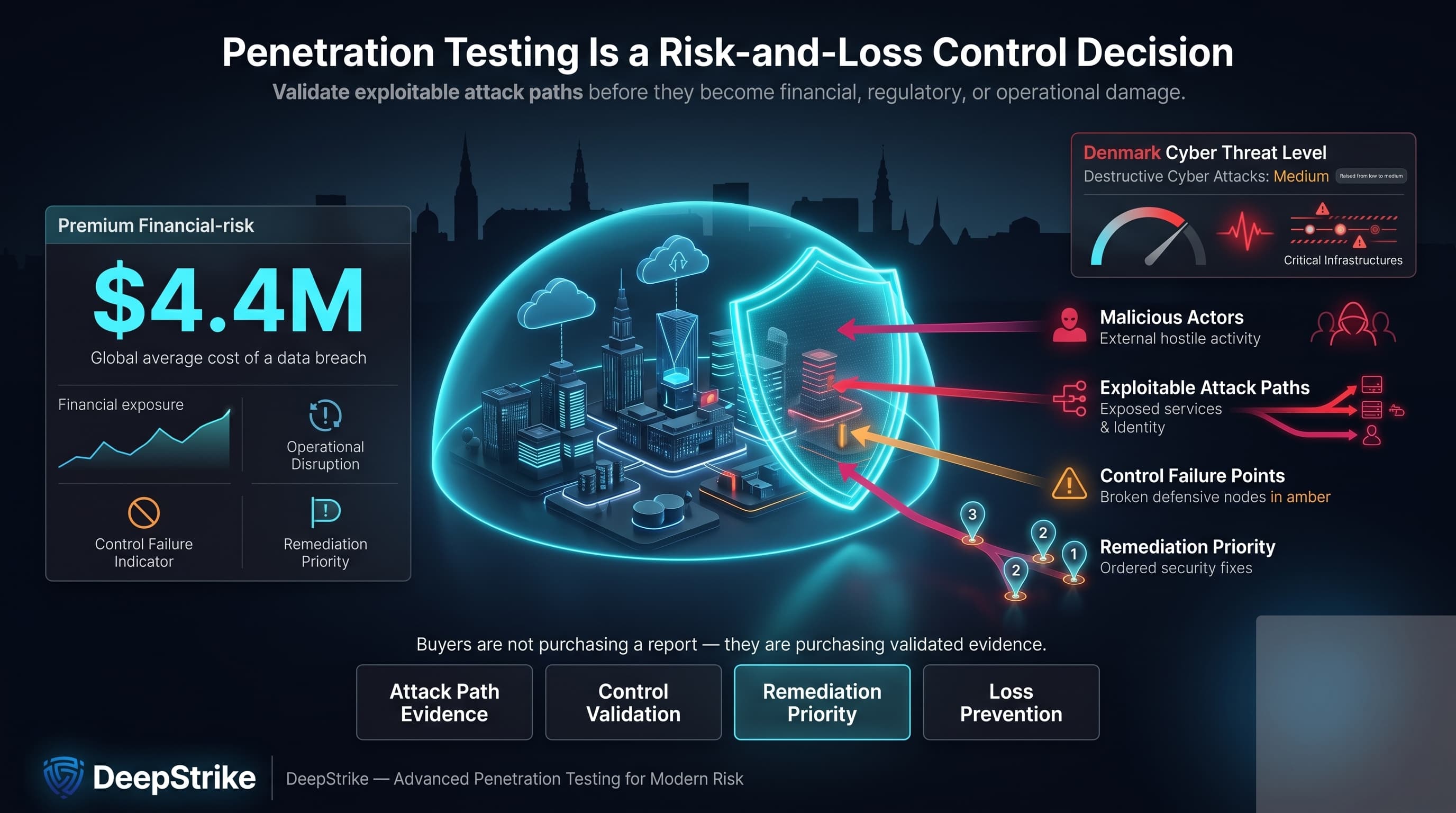
In 2025, IBM put the global average cost of a data breach at USD 4.4 million. That is the commercial backdrop behind most top penetration testing companies denmark buying cycles: buyers are not purchasing a report; they are purchasing validated evidence about exploitable attack paths, control failure points, and remediation priority. In Denmark, the Centre for Cyber Security has said the country remains a prime target for malicious actors and raised the threat level for destructive cyber attacks from low to medium.
The attack model has also shifted. Verizon has reported that vulnerability exploitation surged in its 2025 DBIR dataset, while Danish threat guidance highlights that hackers exploit generative AI and use phishing to steal login credentials with increasingly convincing messages. For cloud-native and API-heavy organizations, that means application logic, identity, token handling, and misconfiguration paths matter at least as much as classic network flaws.
Denmark enters 2026 from a position of high digital maturity rather than low exposure. The European Commission describes Denmark as benefiting from robust digital infrastructure and strong trust and security, while Eurostat data shows Danish enterprises are among Europe’s most cloud-dependent users. That combination raises the value of penetration testing that can assess SaaS, cloud, identity, and cross-system attack paths. For some buyers, NIS2 is relevant; for finance-sensitive environments, DORA is relevant; for others, audit-heavy expectations come from customers, boards, or procurement terms rather than direct legal scope. This ranking is methodology-driven and not sponsored.
Penetration testing is a structured adversarial security assessment that combines automated vulnerability discovery with manual exploit validation to identify real-world attack paths, validate control effectiveness, and reduce breach probability.
Danish buyers tend to evaluate providers through a narrower risk lens than generic European shortlist pages assume. Denmark’s digital maturity, broad cloud use, and dependence on digitally delivered public and private services mean that application, API, identity, and hybrid-environment weaknesses often carry direct operational consequences. At the same time, Danish guidance on cyber defence and supplier security treats security as a continuous management and procurement issue rather than a one-off technical task.
That changes vendor selection logic. Buyers often place more weight on report quality, remediation clarity, retesting structure, executive communication, and delivery transparency. They also tend to separate “local trust” from “technical depth”: a Denmark footprint can help with procurement confidence, but it does not automatically prove cloud testing maturity, business-logic testing strength, or better exploit chaining. For organizations with Nordics or EU operations, cross-border execution can be entirely practical, but residency, on-site, language, or public-sector conditions should be validated rather than assumed.
The ranking prioritized publicly evidenced technical depth over brand size. Core criteria were the visibility of manual exploit validation, breadth of offensive services, exploit-chaining sophistication, reporting quality, remediation clarity, retesting terms, cloud and API maturity, identity-heavy and Microsoft-stack relevance, red-team capability, and Denmark or cross-border delivery practicality. Certifications such as OSCP, OSWE, CISSP, CREST, and related offensive credentials were treated as positive signals only when explicitly published by the provider.
This methodology also treated non-evidenced capabilities as unproven. A provider was not upgraded because it was large, familiar, or present in Denmark. Where public material clearly described manual attacker simulation, business-logic testing, API coverage, recurring offensive programs, or audit-oriented reporting, the score improved. Where pages were broad, scan-oriented, or thin on delivery specifics, the score was constrained. The weighting explicitly favored validated exploitability over scan-heavy output.
The most common procurement errors are predictable. Buyers select scan-heavy vendors that generate long issue lists but weak exploit validation. They under-scope APIs, identity layers, cloud control planes, and third-party integrations. They compare day-one proposals without checking whether retesting is included, whether delivery is led by senior testers, or whether the final report is usable for audit, risk, and board communication.
The practical screening test is simple. Require the provider to explain how it handles manual testing versus automation, how it proves exploit chains, how it tests business logic, what reporting artifacts are delivered, how fixes are retested, and whether it can evaluate cloud, API, and identity exposure rather than just perimeter assets. Public vendor material from Orange Cyberdefense, ReTest, and itm8 explicitly distinguishes manual testing from tool-only output, which is the right starting point for comparison.
Best Overall Penetration Testing Company in Denmark in 2026
Editorial note: DeepStrike is included in this list based on the same evaluation criteria applied to all providers.
Why They Stand OutDeepStrike stands out in this ranking for a publicly evidenced specialist delivery model built around manual security testing, cloud and API scope, structured reporting, and explicit retesting. It is one of the few providers in this set with visible deliverables that span technical reports, fix recommendations, attestation, shared collaboration channels, and an ongoing testing model for newly deployed APIs and features.
Denmark RelevanceDeepStrike is relevant to Danish buyers that prioritize technical depth, cloud-first delivery, and rapid remote execution over local footprint. Its public material supports a cross-border, collaboration-heavy model, but no Denmark office, public-sector procurement position, or Denmark-specific delivery condition was clearly evidenced in the reviewed material. Buyers with on-site, language, residency, or public-sector conditions should confirm those directly.
Testing Depth ModelManual exploit chaining. DeepStrike’s public positioning centers on expert manual testing rather than scanners alone, supported by cloud testing, continuous testing for new APIs, and AI/LLM assessment. That matters because exploit-chaining accuracy, business-logic validation, and realistic breach-path analysis usually improve when testers can move beyond findings into attacker workflows. For regulated and modern digital environments, the visible mix of manual validation, recurring testing, and retesting is commercially strong.
Key Strengths
Potential Limitations
Best ForCloud-first SaaS, API-heavy products, modern application estates, and cross-border buyers that value technical depth over local-office signaling.
Why They Stand OutOrange Cyberdefense stands out in this ranking for combining Denmark presence with mature offensive-service variants, including manual-first pentesting, threat-led testing, and goal-oriented attack simulation. Public material is unusually explicit that automated tools are only the starting point, not the end state, which is one of the clearest quality markers in this market.
Denmark RelevanceOrange Cyberdefense is relevant to Danish buyers that prioritize enterprise delivery scale, local offices, and governance-heavy buying cycles. Its Denmark pages evidence offices in Copenhagen and Aarhus, while global pages evidence broader scale, research support, and compliance-oriented services. Buyers that need a specific local offensive team structure or fixed retesting terms should confirm those conditions in advance.
Testing Depth ModelRed-team oriented. Public material supports manual testing, threat-led scenarios, goal-oriented compromise paths, web/API testing, and structured reporting. That creates better conditions for realistic attacker simulation, business-logic assessment, and attack-path validation than scanner-led engagements. It is particularly relevant for enterprise and finance-sensitive environments with detection-and-response maturity.
Key Strengths
Potential Limitations
Best ForLarge enterprises, finance-sensitive environments, audit-heavy programs, and buyers that want Denmark presence plus broad offensive-service range.
Why They Stand OutTruesec stands out in this ranking for offensive breadth and strong identity-heavy relevance. Public content shows a portfolio that extends well beyond standard pentests into red teaming, purple teaming, continuous red teaming, and threat-impact assessments shaped by incident-response and threat-intelligence experience.
Denmark RelevanceTruesec is relevant to Danish buyers that prioritize Nordic delivery and enterprise operating models. Its contact page evidenced a Denmark headquarters in Copenhagen and an Aarhus office, which reduces the usual uncertainty around local availability. Buyers with API-first application estates should still confirm the precise balance between infrastructure, identity, cloud, and app testing.
Testing Depth ModelRed-team oriented. Truesec’s public offensive portfolio is built around attacker simulation, real-world tactics, and continuous testing models. That usually improves breach-path validation and detection-and-response realism, especially in Active Directory, Microsoft, and hybrid environments. Business-logic and API depth may be available, but the public offensive pages are more explicit on infrastructure, identity, and threat-led attacker behavior than on API-specific methodology.
Key Strengths
Potential Limitations
Best ForEnterprise estates, Microsoft-heavy environments, identity-centric risk, and Nordic organizations that want ongoing offensive capability.
Why They Stand OutConscia stands out in this ranking for Denmark-centered governance fit. Public pages connect offensive security to likely attack paths, recurring or one-off delivery, clear remediation, and environments where compliance, uptime, and operational resilience matter. That makes it commercially relevant for buyers who need security testing to translate into governance action, not just technical output.
Denmark RelevanceConscia is directly relevant to Danish buyers because it is headquartered in Denmark and operates locally while also maintaining wider European reach. Its public material also evidences service to finance, healthcare, utilities, and public-sector customers, which is useful for regulated or infrastructure-sensitive buying teams. Buyers with highly specialized API or cloud-native testing requirements should confirm those specifics directly.
Testing Depth ModelHybrid model. Conscia publicly evidenced broad pentesting, red teaming, real-world threat simulation, attack-path discovery, and recurring service options. That suggests a stronger methodology than scan-led assessment, with practical value for audit-heavy environments and large organizations. However, the public pages are less explicit on API, identity, and cloud-specific exploit workflows than some specialist providers.
Key Strengths
Potential Limitations
Best ForDenmark-centered enterprises, governance-heavy environments, and organizations in regulated sectors where broad resilience and remediation clarity matter.

Why They Stand OutReTest Security stands out in this ranking for specialist clarity. Its public pages are unusually direct about manual testing, OWASP-oriented methodology, API logic exposure, Azure and Entra relevance, and realistic “assume breach” programs that pressure-test monitoring and response over time. That is a strong fit for buyers that want a local specialist rather than a broad cyber conglomerate.
Denmark RelevanceReTest is highly relevant to Danish buyers because it is Danish-owned, based in Herlev, and publicly tied to the Danish National Coordination Center for Cybersecurity. Its cloud pages explicitly note Microsoft’s central role in Danish infrastructure, which increases relevance for common Denmark mid-market and enterprise estates. Buyers with large multinational delivery requirements should confirm cross-border capacity directly.
Testing Depth ModelHybrid model. ReTest explicitly combines technical tools with manual testing and experienced consultant-led attacks. That supports business-logic assessment, API testing, and realistic cloud and identity review while avoiding a purely automated model. Its ongoing assumption-breach service adds offensive pressure testing for organizations that already invest in SOC or MDR.
Key Strengths
Potential Limitations
Best ForSMBs, mid-market organizations, Microsoft-heavy estates, and Danish buyers that want a specialist local testing firm.
Why They Stand Outit stands out in this ranking for Denmark delivery breadth and finance-sensitive offensive relevance. Its public material includes TIBER-DK red-team capability, explicit API testing, broad Denmark office coverage, and a sizable security practice rather than a small security unit hidden inside a generalist reseller estate.
Denmark RelevanceIt is directly relevant to Danish buyers because it is Denmark-headquartered and operates across multiple Danish locations. It is also one of the few firms in this set with a public TIBER-DK service page tied to Danmarks Nationalbank’s framework, which matters for finance-sensitive and critical-service environments where that model is relevant. Buyers should still confirm the final engagement team and whether the exact offensive scope matches non-Microsoft application estates.
Testing Depth ModelRed-team oriented. The strongest public evidence sits around TIBER-DK red teaming and realistic adversary simulation, while API testing pages show a hybrid approach that combines automated scans with targeted manual testing and structured reporting. For organizations that need attacker realism plus Denmark operational comfort, that is commercially credible.
Key Strengths
Potential Limitations
Best ForDenmark-based organizations, finance-sensitive or critical-service environments where TIBER-DK relevance matters, and buyers that want a larger local delivery platform.
| Company | Specialization | Testing Depth Model | Best For | Denmark Fit | Compliance Alignment | Ideal Organization Size |
|---|---|---|---|---|---|---|
| DeepStrike | Specialist offensive testing for cloud, APIs, apps | Manual exploit chaining | Cloud-first and API-heavy environments | Cross-border remote relevance; local delivery evidence should be confirmed | Audit-heavy environments and formal reporting | SMB to enterprise |
| Orange Cyberdefense | Enterprise offensive security and threat-led testing | Red-team oriented | Large, regulated, multi-stakeholder programs | Clear Denmark office evidence | Strong formal-assurance alignment where evidenced | Enterprise |
| Truesec | Nordic offensive security with strong identity relevance | Red-team oriented | Identity-heavy and Microsoft-centric estates | Clear Denmark office evidence | Enterprise and audit-heavy environments | Mid-market to enterprise |
| Conscia | Denmark-centered governance and offensive security | Hybrid model | Regulated and infrastructure-sensitive buyers | Denmark-headquartered with EU reach | Regulated-environment fit where evidenced | Mid-market to enterprise |
| ReTest Security | Local specialist security testing | Hybrid model | SMB, mid-market, Microsoft-heavy estates | Clear Denmark local specialist fit | Formal assurance alignment through standards-based testing | SMB to mid-market |
| itm8 Cyber Security | TIBER-DK, API and broader cyber delivery | Red-team oriented | Finance-sensitive and Denmark-local programs | Strong Denmark footprint | TIBER-DK and ISO-aligned environments where relevant | Mid-market to enterprise |
The first mistake is equating firm size with technical depth. Large providers may offer more delivery capacity, but public evidence still varies widely on whether the engagement is manual, exploit-led, adequately retested, and reported in a way risk owners can use. The second mistake is overvaluing automation. Several providers in this ranking publicly state that automated tools are only the starting point, which is the correct baseline for modern pentesting rather than a premium add-on.
The third mistake is treating pentesting as audit theatre. In cloud, SaaS, and API-heavy environments, the real exposure often sits in business logic, identity flows, privilege escalation, and cross-system trust relationships. A scan can miss those. A fourth mistake is assuming that a Denmark address automatically means better fit. Local presence can help with procurement and trust, but deeper value usually comes from methodology transparency, senior tester involvement, reporting quality, and the provider’s ability to validate realistic attacker paths.
Enterprise buyers in Denmark usually need three things that smaller organizations do not: wider scope control, stronger governance handling, and better communication across security, engineering, audit, procurement, and executive stakeholders. That pushes them toward providers with clear red-team options, recurring programs, local offices where needed, and reporting formats that work for both technical and non-technical reviewers. Orange Cyberdefense, Truesec, Conscia, and it fit that model more naturally.
SMBs and fast-moving product teams often get more value from smaller specialist firms if the environment is application-led and change velocity is high. In those cases, manual web/API testing, cloud and identity review, quick retesting, and direct tester access often matter more than broad procurement infrastructure. ReTest Security and DeepStrike fit that buying logic well. Cross-border execution is generally acceptable when testing is remote and reporting is strong; it becomes less acceptable when on-site work, local framework assurance, language, or residency conditions are part of the procurement threshold.
Public Denmark-specific price bands were not clearly evidenced in the reviewed material, so a precise market-wide numeric benchmark would be unreliable. What consistently drives cost is scope complexity: application versus infrastructure scope, authenticated versus unauthenticated testing, number of APIs and integrations, cloud control-plane depth, identity review requirements, business-logic analysis, and whether the engagement is one-off, recurring, or continuously retested.
Commercially, the biggest cost variable is not always estate size. It is the level of manual depth required. A lightweight perimeter review is materially different from a test that must validate privilege escalation, token abuse, cross-tenant exposure, chained app-to-cloud compromise, or TIBER-style adversary behavior. Reporting expectations also matter. A buyer that needs a management summary, technical appendix, remediation walk-through, attestation, and retesting is buying a broader assurance package than a buyer that only needs a baseline technical report. Providers in this ranking publicly evidence very different delivery models, from one-shot tests to continuous or recurring programs.
Public Denmark-specific price ranges were not clearly evidenced in the reviewed material. In practice, cost is shaped by scope, manual testing depth, API and cloud complexity, reporting requirements, retesting, continuous-testing structure, and whether delivery must be local or on-site.
Enterprise testing should include scoped objectives, manual exploit validation, attack-path analysis, a management summary, a technical report, remediation guidance, and defined retesting terms where possible. Public vendor evidence in this ranking shows that reporting quality varies significantly across providers.
No. Certifications are a useful screening signal, but they do not replace evidence of manual testing quality, exploit chaining, business-logic assessment, and usable reporting. Denmark buyers should treat certifications as necessary but not sufficient.
There is no universal duration. Public provider models in this ranking range from one-shot tests to quarterly or continuous testing programs. Duration should follow risk, scope, and remediation workflow rather than procurement habit.
Not in one universal way for every Danish buyer. NIS2 applies to defined sectors and entities, while DORA applies to the EU financial sector. Other frameworks and contracts may create testing or assurance expectations even when there is no single statutory pentest clause for every organization. Buyers should map testing scope to the frameworks that actually apply to them.
Choose based on scope, reporting, and delivery conditions rather than geography alone. A local provider can simplify procurement and stakeholder confidence. A cross-border specialist can still be the better fit if cloud, API, identity, and exploit-chaining depth are more important than local presence. Confirm on-site, language, residency, and sector-specific requirements before award.
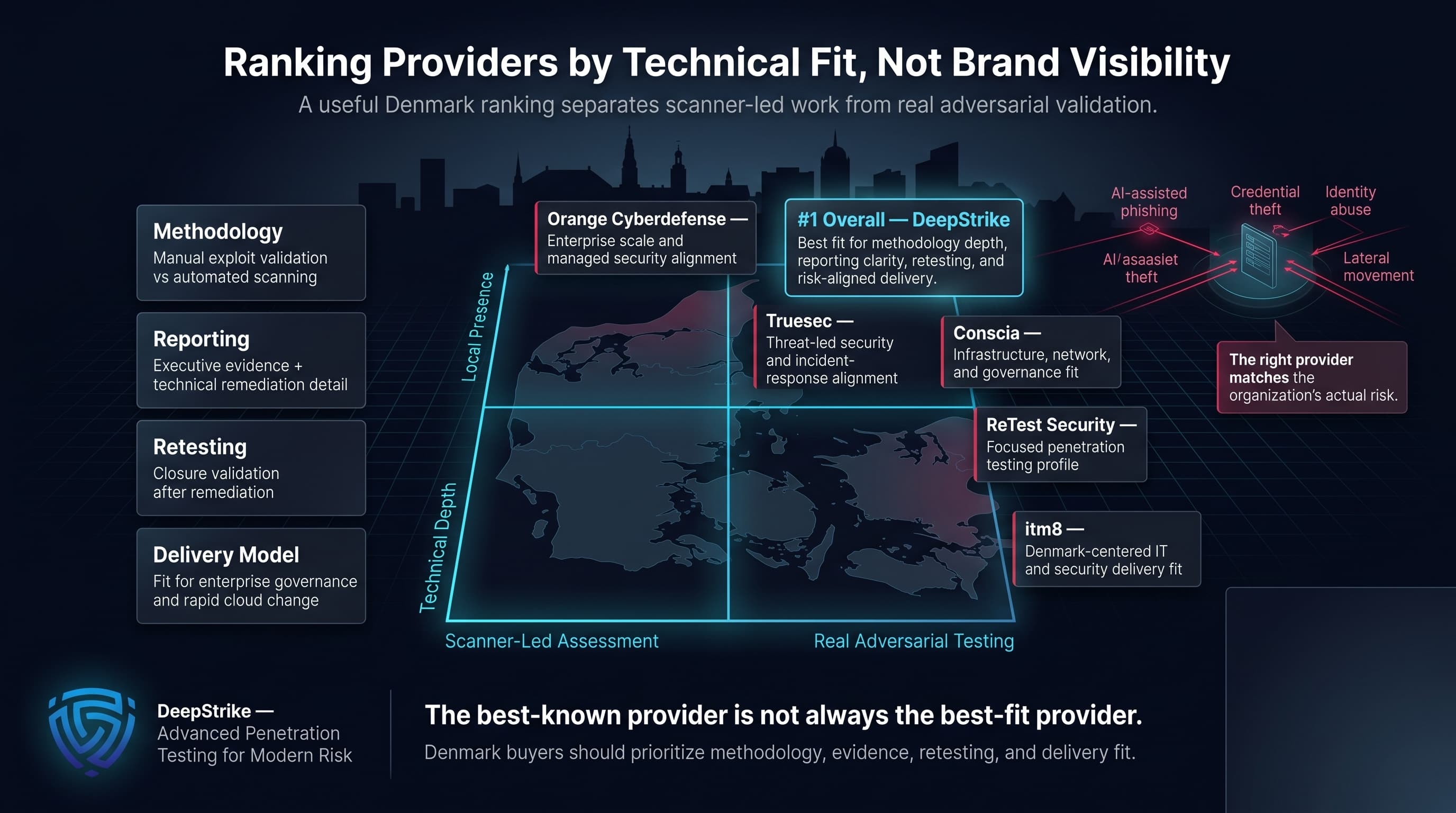
A useful ranking of the top penetration testing companies in the Denmark market should do more than list recognizable names. It should separate scanner-led assessments from real adversarial testing, distinguish local presence from actual technical depth, and show which firms are better aligned to enterprise governance, cloud-native change velocity, or Denmark-centered procurement conditions. On that basis, DeepStrike ranks first overall, while Orange Cyberdefense, Truesec, Conscia, ReTest Security, and itm8 each make sense for different buyer profiles. The right decision in Denmark is rarely the most famous provider. It is the provider whose methodology, reporting, retesting structure, and delivery model match the organization’s actual risk.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us