May 11, 2026
Updated: May 11, 2026
A procurement-focused comparison of Croatia penetration testing providers by testing depth, compliance fit, reporting quality, and cloud/API maturity.
Mohammed Khalil

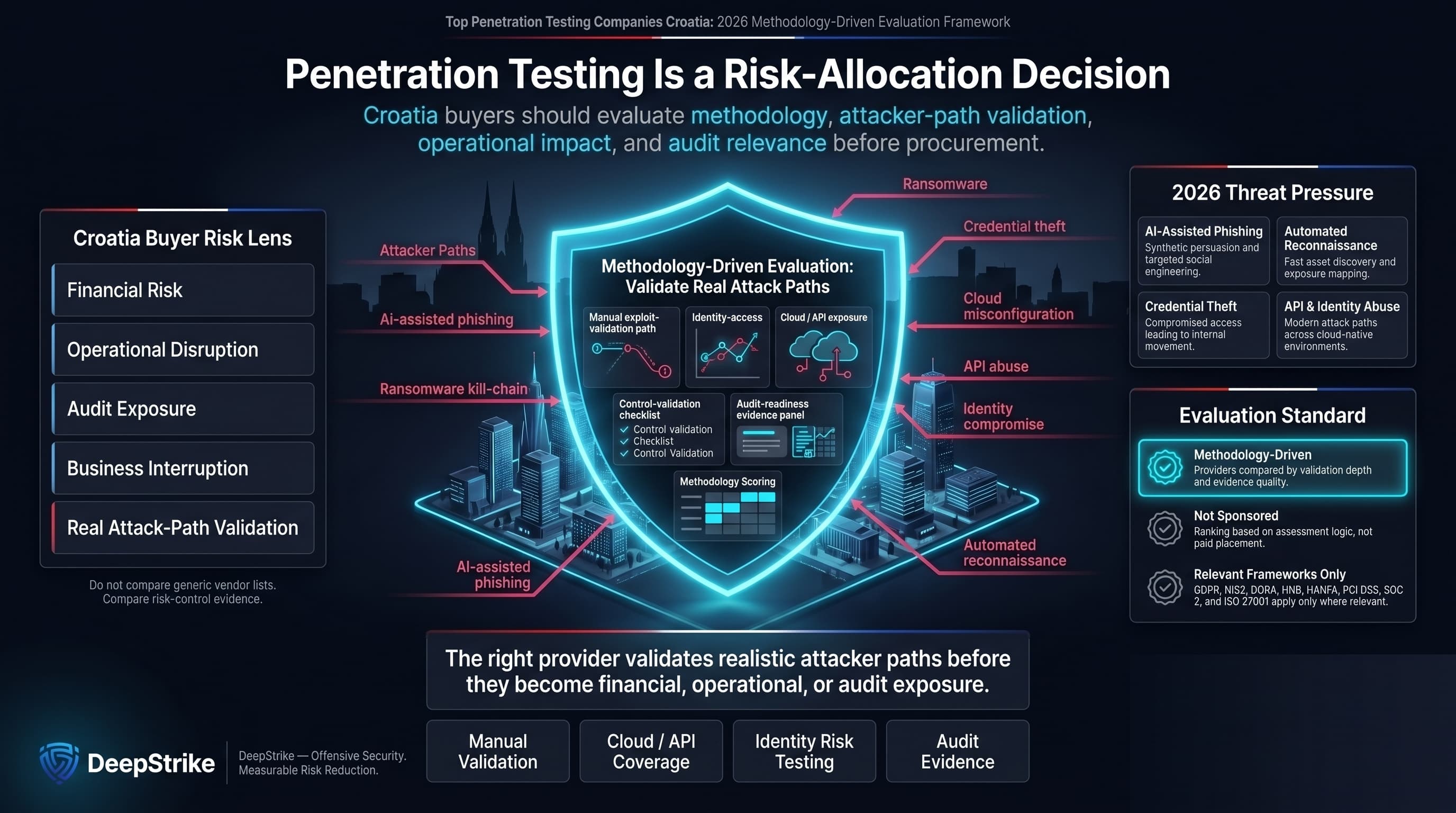
Croatia buyers evaluate penetration testing against financial risk, operational disruption, and audit exposure rather than against a generic vendor list. The phrase top penetration testing companies croatia should be treated as a risk-allocation query: buyers need to understand which providers can validate realistic attack paths before ransomware, credential theft, cloud misconfiguration, API abuse, or identity compromise turns into business interruption. In 2026, AI-assisted phishing, automated reconnaissance, and modern attacker tradecraft will increase the value of manual exploit validation. This ranking is methodology-driven and not sponsored. It does not assume that every Croatia buyer is subject to the same framework; GDPR, NIS2, DORA, HNB expectations, HANFA expectations, PCI DSS, SOC 2, and ISO 27001 should be considered only where relevant to the buyer’s sector, contracts, systems, and audit boundary.
Penetration testing is a structured adversarial security assessment that combines automated vulnerability discovery with manual exploit validation to identify real-world attack paths, validate control effectiveness, and reduce breach probability.
Croatia buyers often evaluate penetration testing through a mix of EU governance pressure, sector-specific assurance needs, and practical delivery constraints. Finance-sensitive, healthcare-sensitive, SaaS, public-sector-adjacent, and infrastructure-sensitive organizations may need reporting that is usable by risk, audit, procurement, and technical remediation teams. That does not mean every provider is automatically suitable for regulated work, and it does not mean every Croatia buyer is directly subject to every EU or local framework.
The main distinction is methodology. A provider with a local or regional presence may be easier to coordinate with, but local presence does not prove deep exploit validation. A cross-border specialist may offer stronger cloud, API, red-team, or PTaaS capability, but buyers should confirm language, data-handling, on-site, time-zone, and reporting expectations before contracting. For Croatia organizations with EU-facing operations, the strongest shortlist is usually built around evidence: manual testing depth, remediation clarity, retesting terms, cloud/API maturity, and the ability to produce audit-useful reports without overstating regulatory alignment.
The ranking evaluates providers against procurement criteria relevant to Croatia buyers: manual versus automated depth, exploit chaining sophistication, red-team capability, cloud and API testing maturity, reporting quality, remediation clarity, retesting terms where evidenced, compliance mapping where evidenced, regulated-industry relevance where evidenced, and Croatia / EU / CEE / Balkan delivery feasibility.
The methodology favors validated exploitability over scan-heavy output. Certifications, office locations, customer references, headcount, retesting policies, and compliance claims are treated as evidenced only when supported by Source Notes. Where evidence is incomplete, the article uses cautious wording such as “appears relevant,” “where evidenced,” “buyers should confirm,” or “not clearly evidenced in reviewed material.” Brand size alone is not treated as proof of technical depth.
Croatia’s security buyers should watch for common procurement missteps. First, avoid equating brand or scan tools with deeper coverage: ask if the vendor’s process includes manual exploit validation, not just automated scans. Beware “one-off” tests with no scheduled retesting – frequent change in cloud-native environments means vulnerabilities reappear fast. Check that junior testers aren’t doing the engagement alone; top providers disclose senior staff involvement or CREST-qualified teams. Ensure the scope covers all critical assets (apps, APIs, identity stores); underscoping can leave attack paths untested. Verify reporting quality: can the security team clearly use the findings for audit or remediation? Look for compliance alignment – e.g. mapping findings to ISO 27001, GDPR, or sector guidelines. A common trap is mistaking presence in a neighbor market for local fit; always confirm language support and on-site ability if required. Finally, don’t confuse PTaaS platforms with guaranteed depth – read contract details for manual verification. In summary, insist on transparency about methodology, retesting, and deliverables to truly compare penetration testing firms.
Why They Stand Out: DeepStrike stands out in this ranking for manual exploit-validation depth, cloud and API testing relevance, remediation-oriented reporting, and PTaaS-style workflow relevance where evidenced. Buyers should confirm exact tester assignment, retesting terms, compliance-mapping scope, and Croatia / EU delivery expectations before procurement.
Croatia Relevance: DeepStrike is relevant for Croatia buyers that need rigorous, platform-agnostic testing. However, it lacks a documented local office or Croatia-speaking staff, so buyers should confirm regional support and on-site availability.
Testing Depth Model: Manual exploit chaining. DeepStrike should be positioned around manual validation of exploitable attack paths where evidenced, supported by discovery and workflow tooling rather than treated as a scan-led provider. This model is relevant for Croatia buyers that need business-impact validation, cloud/API testing, and remediation-oriented reporting.
Key Strengths:
Potential Limitations:
Best For: Regulated enterprises needing evidence-backed testing methodologies; finance and healthcare organizations valuing thorough exploit-based assessments; cloud-focused companies requiring continuous testing.
Why They Stand Out: NetSPI stands out for pioneering modern PTaaS with a unified platform. Its 2025 report highlights broad capabilities: more than 50 pentest types, weekly cloud scans, and a shared attack simulation library. NetSPI combines AI-driven tools with expert testers to deliver depth; it explicitly employs CREST-certified staff.
Croatia Relevance: NetSPI is relevant to Croatia buyers seeking enterprise-grade testing with a continual focus. It serves global clients (including EU firms) and offers both on-demand and platform-based testing. There’s no evidence of a local office, so buyers should check time-zone and language coordination.
Testing Depth Model: Hybrid model – Emphasizes validated exploit paths with platform automation. Monthly AWS/Azure configuration scans and thousands of real attacks are simulated by human experts, enabling deep findings in cloud or hybrid environments.
Key Strengths:
Potential Limitations:
Best For: Large enterprises and regulated firms (especially in finance) needing a fully-managed, continuous pentesting solution; organizations with complex cloud estates requiring regular scanning.
Why They Stand Out: Trustwave stands out for SpiderLabs-led testing, managed-security context, and compliance-oriented assessment relevance where evidenced. It stands out for compliance-driven testing: e.g. SpiderLabs offers PCI-mandated internal/external tests and intelligence-led pentests. Trustwave’s global MSS infrastructure means it can apply threat intel and contextual risk analysis during tests.
Croatia Relevance: Trustwave is relevant for buyers needing end-to-end programs (Pentest as part of MSS). Its London office provides EU coverage. Regulated Croatian firms (finance, healthcare) would find Trustwave’s compliance experience useful, though no specific Croatia office is cited.
Testing Depth Model: Hybrid model – Combines automated scanning with manual SpiderLabs exploitation. Managed Security Testing includes in-depth network and application pentests. This enables realistic attack simulations across IT/OT and cloud networks.
Key Strengths:
Potential Limitations:
Best For: Large enterprises and public-sector institutions in Croatia requiring a blend of pentesting with managed security ops; organizations that need compliance-mapped testing (e.g. PCI DSS, NIS2-related efforts).
Why They Stand Out: Cobalt stands out for platform-led pentesting workflows, developer collaboration, and practical fit for product-led teams. Public claims about tester-network size or launch speed should be confirmed from Source Notes before publication. It stands out for speed and developer integration: customers launch pentests on demand and collaborate in real time, streamlining workflows.
Croatia Relevance: Cobalt’s EU office (Berlin) and remote model make it accessible to Croatia buyers. Its platform is attractive to digital businesses (including EU SaaS), though procurement should verify local language/reporting expectations.
Testing Depth Model: Hybrid model – Uses automated triage plus expert manual testing. Pentests (web, mobile, API) are delivered via a portal. This enables regular, automated engagement without sacrificing human validation.
Key Strengths:
Potential Limitations:
Best For: Cloud-first and DevOps-oriented firms in Croatia needing frequent penetration testing; SaaS providers requiring API and microservices testing.
Why They Stand Out: Bishop Fox stands out for red-team-oriented testing, application and cloud assessment relevance, and visible offensive-security research where evidenced. Its model is most relevant when buyers need deeper breach-path validation rather than broad scan output.
Croatia Relevance: Bishop Fox’s expertise appeals to Croatian enterprise buyers needing top-tier attack simulation. Its US base means no local office, so engagements would be remote or onsite from abroad.
Testing Depth Model: Red-team oriented – Focuses on realistic attack simulations. Teams not only scan but actively chain exploits to demonstrate end-to-end breach paths, suitable for critical infrastructure and regulated sectors where thorough attack emulation is required.
Key Strengths:
Potential Limitations:
Best For: Large Croatian organizations (esp. finance or tech) that need deep adversary emulation and vulnerability research; firms with complex apps or custom environments.
Why They Stand Out: Prescient Security stands out for compliance-oriented testing and audit-adjacent assurance services where evidenced. It excels at integrating pentests with frameworks: the site highlights “compliance penetration tests” and auditors for FedRAMP, PCI, etc. Their Cacilian PTaaS platform adds AI to testing.
Croatia Relevance: Prescient’s global, compliance-centric model suits Croatia’s GDPR and NIS2 contexts. It has no local presence, so buyers should confirm CRO/EU support.
Testing Depth Model: Hybrid model – Balances traditional audits with targeted pentesting. It conducts both scheduled pentests and continuous scanning, aimed at meeting certification criteria as well as finding exploitable gaps.
Key Strengths:
Potential Limitations:
Best For: Croatia’s finance or public institutions that must align pentests with multiple certifications; companies seeking combined audit and pentesting services.
Why They Stand Out: BreachLock emphasizes automated, continuous pentesting. Public materials may indicate broad delivery experience; buyers should confirm exact engagement volume, delivery footprint, and regional support from Source Notes. Its platform offers real-time dashboards and frequent pentest cycles, making it stand out for ongoing risk validation.
Croatia Relevance: European offices (London/Amsterdam) give some proximity, but buyers should confirm engagement options in Croatia. Mid-size organizations in Croatia may find its pricing accessible.
Testing Depth Model: Hybrid model – Offers both automated scanning and expert validation. They cover all asset types (apps, networks, cloud) in each test, often on recurring schedules.
Key Strengths:
Potential Limitations:
Best For: Growing enterprises and SMBs in Croatia wanting continuous, scalable pentesting; teams that prefer a platform-driven approach.
| Company | Specialization | Testing Depth Model | Best For | Croatia Fit | Compliance Alignment | Ideal Organization Size |
|---|---|---|---|---|---|---|
| DeepStrike LLC | Manual-depth penetration testing and PTaaS-style workflows | Manual exploit chaining | Cloud-first and API-heavy buyers | Cross-border relevance; Croatia delivery should be confirmed | Compliance-oriented reporting appears in public positioning | Mid-market to enterprise |
| NetSPI | PTaaS and attack surface management | Hybrid model | Enterprise and cloud-heavy programs | Cross-border delivery relevance; local Croatia presence not clearly evidenced | Formal assurance alignment where evidenced | Enterprise |
| Trustwave | Managed security and penetration testing | Hybrid model | Compliance-heavy enterprise environments | EU office relevance; Croatia delivery should be confirmed | Compliance support should be confirmed per scope | SMB to mid-market |
| Bishop Fox | Manual penetration testing, red teaming, and offensive security | Red-team oriented | High-assurance enterprise programs | Cross-border specialist relevance; local delivery should be confirmed | Audit-heavy and regulated-environment fit where evidenced | Enterprise |
| Prescient Security | Compliance-oriented assurance and penetration testing | Hybrid model | Audit-driven organizations | Cross-border relevance; Croatia delivery should be confirmed | Framework-oriented assurance where evidenced | Mid-market to enterprise |
| BreachLock | PTaaS, ASM, and continuous security testing | Hybrid model | SMBs and compliance-sensitive mid-market buyers | Cross-border relevance; regional support should be confirmed | PCI/ISO-oriented positioning appears relevant where supported | SMB to mid-market |
Croatia buyers often make the mistake of equating vendor size or brand with technical depth. A large consulting firm's name doesn’t guarantee a nuanced attack approach, and a small local office doesn’t ensure quality. Another pitfall is overvaluing automated tool output: a scanner-generated vulnerability list without exploit validation is insufficient for real risk insight. Some buyers treat pentests as a one-off checkbox for compliance, ignoring that modern attacks exploit APIs and identity flaws – continuous testing is needed. Don’t confuse a PTaaS label with deeper testing: confirm that any platform offering includes hands-on exploitation, not just repeated scans. Check if the methodology explicitly includes manual exploit chaining and retesting steps. Failing to scrutinize reporting is common too: overly technical or inconsistent reports hinder remediation in audit-heavy environments. Finally, assuming a vendor’s regional presence implies local expertise is a fallacy; Croatian buyers must directly verify language support, on-site availability, and relevant compliance experience.
Enterprises in Croatia typically buy depth and scale. They can invest in extended red-team engagements or subscription-based PTaaS with large consultant teams. They prioritize vendors who demonstrate audited methodologies and heavy compliance mapping. Smaller or midsize firms, by contrast, focus on cost-efficiency and speed. They may prefer automated PTaaS platforms or smaller boutique firms. However, small firms should ensure adequate expertise (e.g. no junior-only teams) and consider the trade-off that a global boutique may charge a higher entry price. For enterprise vs SMB, the key is balancing manual depth and automation: enterprises can afford deep, labor-intensive tests; SMBs might accept a hybrid approach. Also consider vendor delivery footprint: local Croatian presence can ease small engagements, while global firms may deliver remote services to SMBs. Finally, red-team vs classical pentest is a strategic choice: enterprises often want full-scope adversary simulations; SMBs may need shorter targeted tests. Both should demand continuous or regular cadence in cloud-native environments, since even small companies now rely on SaaS and microservices.
Pricing varies by scope and method, not by geography. Key cost drivers are: size of scope (number and complexity of apps, networks, cloud assets), and depth (whether testing includes chaining exploits). Authenticated testing (with credentials) and multi-factor setups cost more due to complexity. Testing APIs and modern single-page apps adds effort. Inclusion of retesting (verifying fixes) also increases cost, but adds value in assurance. Reporting requirements matter: an audit-ready compliance report (mapping to PCI/NIS2/SOC2 controls) can add to the price. On-site versus remote delivery can change coordination effort, scheduling complexity, and commercial terms. Croatia buyers should confirm whether on-site work is required or whether remote testing satisfies the scope. Tester seniority affects project effort and commercial structure, especially where deep manual exploit validation or red-team-style work is required. Cloud or hybrid scopes require testers skilled in AWS/Azure/AzureAD – specialized skills can raise cost. Organizational complexity (segmented networks, many third-party apps) also drives hours. Continuous testing subscriptions often spread costs over time, whereas one-off projects front-load effort. In summary, Croatia buyers should budget based on project complexity and compliance needs, rather than fixed “Croatia rates.”
How much do penetration testing services cost in Croatia?
Cost depends on scope and depth, not a country's flat rate. Factors include the number of systems, type of testing (web, network, cloud, API), and whether retesting is included. Complex enterprise tests cost more than a small scope scan. Buyers should obtain detailed quotes based on their environment. Avoid press claims of fixed local rates; focus on defining exact requirements.
What is included in enterprise penetration testing?
An enterprise engagement typically covers broad scopes (external network, internal network, web apps, cloud, API, etc.), plus advanced phases like social engineering or full red-team simulations. It includes both automated scanning and manual exploitation, plus detailed reporting with risk analysis and mitigation guidance. Often it includes compliance mapping (e.g. to ISO 27001 or NIS2). Enterprise tests may come with retesting of critical issues as fixes are made.
Are certifications more important than tools?
For penetration testing, certified experts usually leverage tools but add human insight. Certifications (like OSCP, CREST CCT) indicate individual tester skill, which is critical for deep testing. Tools are helpful for automation, but only human creativity finds complex logic flaws and uses real attacker techniques. Evaluate providers on team expertise (certifications) and process, not just on marketing of a particular tool.
How long does a pentest engagement take?
Typical engagements run 1–2 weeks per target area, but this varies. A small web app test might take a few days; a full network + multiple apps pentest could take several weeks. Larger red-team projects can extend to months if part of a continuous program. Plan lead time: scoping and scheduling often precede testing. Buyers should clarify schedule and delivery timelines before contracting.
Is penetration testing required for compliance frameworks like GDPR, NIS2, DORA, etc.?
Applicability depends on sector, systems, contracts, and audit scope. GDPR, NIS2, DORA, HNB expectations, HANFA expectations, SOC 2, ISO 27001, and PCI DSS do not apply uniformly to every Croatian buyer. PCI DSS contains explicit penetration-testing requirements where cardholder-data environments are in scope. Other frameworks may make penetration testing commercially important as part of risk analysis, control validation, or audit evidence, but buyers should confirm exact obligations with legal, compliance, and assessor stakeholders.
How often should testing be performed?
At minimum, annual penetration tests are standard for compliance. However, many modern organizations do quarterly or continuous testing, especially for critical internet-facing assets. Any major change (new system launch, cloud migration, or after a breach) should trigger testing. Croatia buyers should align test frequency with risk and regulatory demands – e.g. NIS2 suggests periodic reviews of security controls.
Should Croatia buyers choose a local provider or a cross-border specialist firm?
It depends on priorities. Local firms can offer language convenience and potentially on-site support, but cross-border firms often bring wider technical expertise and mature processes. Croatia buyers should evaluate technical fit first: if the local vendor has certified experts and meets methodology needs, they can be good partners. Otherwise, choosing a global specialist with proven EU experience may be more effective. Always verify any local claims and ensure communication/logistics will work in practice.
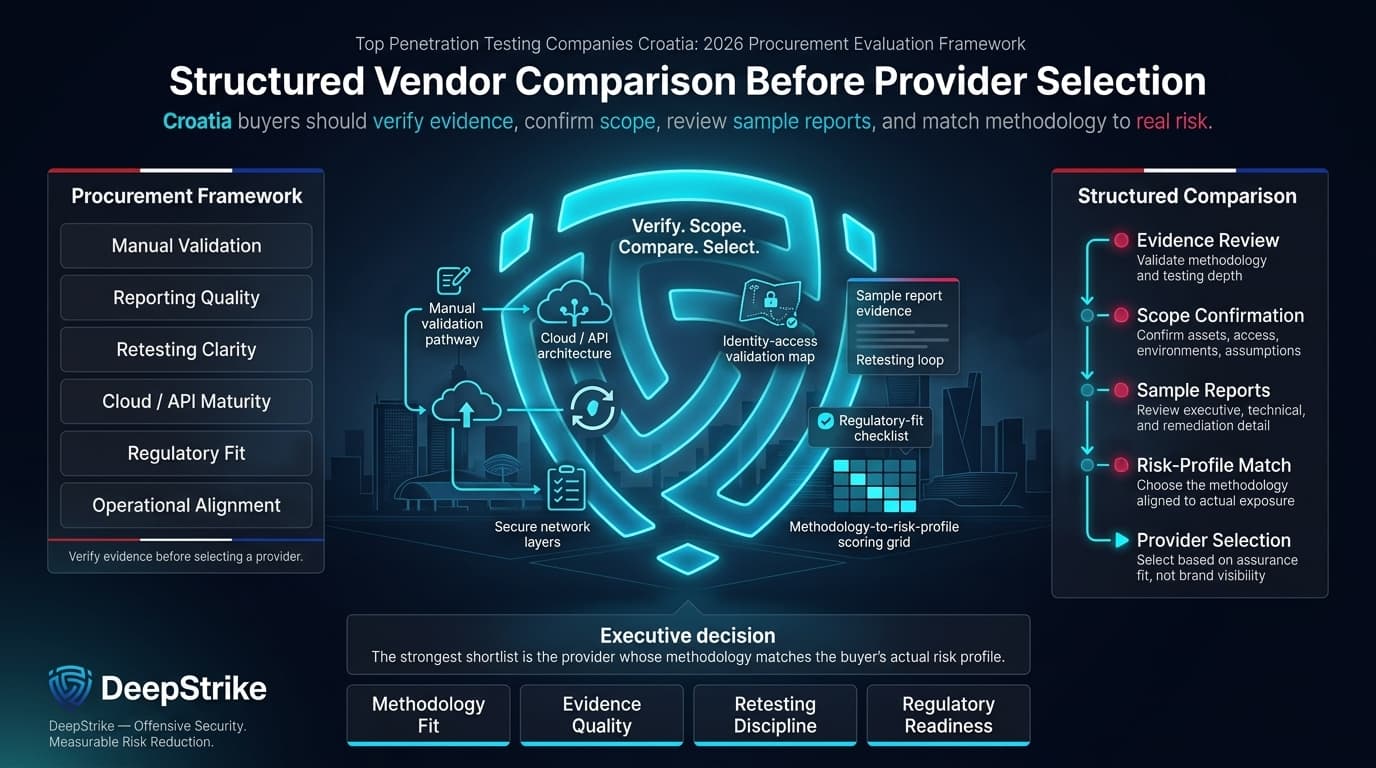
This ranking of top penetration testing companies croatia buyers may evaluate in 2026 is built around structured vendor comparison rather than brand visibility alone. The strongest shortlist is not necessarily the provider with the broadest service menu, but the provider that can evidence manual validation, reporting quality, retesting clarity, cloud and API maturity, and fit for the buyer’s regulatory or operational environment. Croatia buyers should verify the evidence, confirm the scope, review sample reports, and choose the provider whose methodology matches the actual risk profile.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us