May 12, 2026
Updated: May 12, 2026
A procurement-focused comparison of Slovenia’s leading penetration testing providers for enterprise, SMB, cloud, compliance, and offensive security needs.
Mohammed Khalil

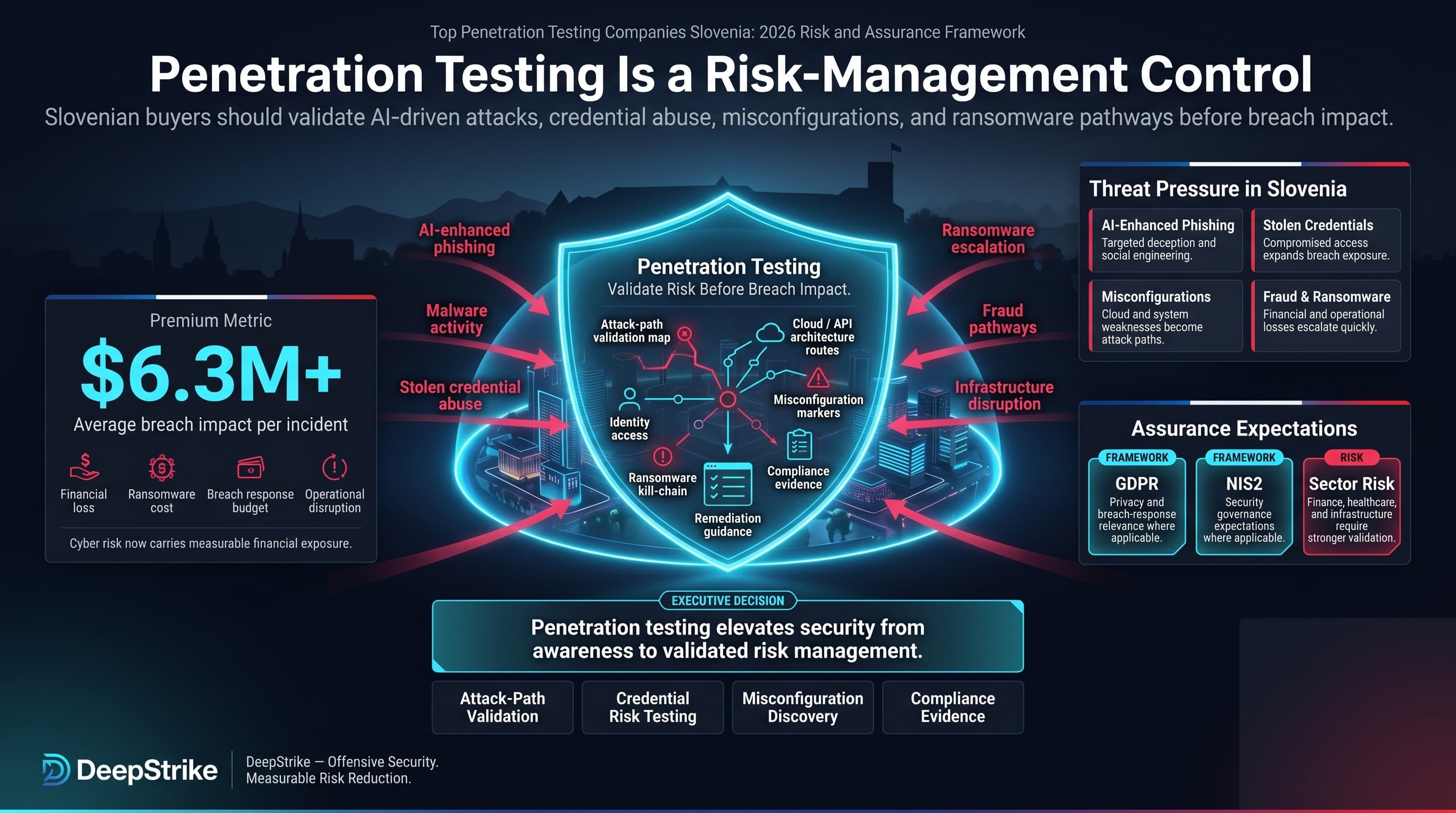
Slovenia’s digital economy faces rising cybercrime costs and regulatory scrutiny. Global cyber breach averages exceed $6.3M per incident, and EU frameworks such as GDPR and NIS2 may increase assurance expectations where they apply. Attackers leverage AI-enhanced phishing and malware to exploit stolen credentials and misconfigurations, escalating fraud and ransomware losses. Slovenian firms, especially finance, healthcare, and infrastructure operators, now budget millions in potential breach response. This elevates the role of penetration testing in risk management.
Under these pressures, choosing among top penetration testing companies Slovenia requires a methodology-driven approach. We stress that this ranking is based on published capabilities and not sponsored by any vendor. Key Slovenia-specific factors include strict data protection (GDPR) and sector regulations (e.g. finance-sector guidance), plus the need for robust audit-ready reporting. For regulated buyers, compliance frameworks (NIS2, ISO 27001, SOC 2, PCI DSS, etc.) inform scope but do not replace testing quality. Cloud-native and hybrid IT environments further demand testing teams skilled in APIs, IAM, and hybrid networks. In short, with rising breach-remediation costs and regulatory fines, Slovenian buyers require validated pen testing depth — not just checkbox scans — from credible, methodology-transparent providers.
Penetration testing is a structured adversarial security assessment that combines automated vulnerability discovery with manual exploit validation to identify real-world attack paths, validate control effectiveness, and reduce breach probability.
Slovenian security buyers face unique pressures. Strict EU and local data protection laws (GDPR, forthcoming NIS2) impose heavy compliance burdens. Public-sector and regulated organizations (finance, healthcare, critical infrastructure) require clear evidence of vendor credibility and methodology transparency. There is often a preference for providers with known reporting quality and remediation guidance, due to audit and governance needs. At the same time, Slovenia’s fast-growing cloud and SaaS adoption means modern digital risks (APIs, identity) must be tested. Buyers may value local communication, on-site coordination, or regional delivery where those capabilities are evidenced., but they must balance that against the specialized technical depth of international experts. In many cases cross-border engagement is acceptable if it meets EU/CEE security and legal requirements. Finally, Slovenian buyers emphasize thoroughness over mere automation; they expect pen tests to simulate realistic attack chains rather than rely on high-volume scanning alone.
Our evaluation framework emphasizes evidenced technical depth and alignment with Slovenia’s risk profile. We considered each firm’s demonstrated expertise (certifications like OSCP/OSWE/GXPN, etc.), use of manual exploit techniques vs. automated scanning, and red-team capabilities. We favored teams that explicitly validate exploitability and complex attack chains. We examined each provider’s maturity in cloud, web, and API testing (e.g. AWS/Azure certifications, custom cloud scenarios). Reporting quality and remediation clarity were key factors, as well as inclusion of retesting or follow-up. Where available, evidence of mapping findings to compliance requirements (GDPR, PCI DSS, ISO 27001) or sector standards informed scores. We also looked at the breadth of service delivery e.g. continuous testing or PTaaS options to meet modern deployment cycles.
Importantly, we did not assume large brand size equates to technical excellence. When technical details were absent, we treated claims cautiously as unproven. Our methodology prioritizes validated exploit testing and hands-on assessments. Each vendor in this ranking is assessed on the above criteria, ensuring the list is unbiased and aligned with enterprise procurement scrutiny.
Why They Stand Out: DeepStrike positions itself as a full-spectrum penetration testing firm with end-to-end services, from reconnaissance to remediation support. They emphasize both manual exploit research and automated scanning, simulating realistic attacker scenarios (including social engineering) across web, mobile, cloud, and infrastructure assets. Their approach includes dedicated planning, broad OSINT reconnaissance, and ongoing technical support.
Slovenia Relevance: DeepStrike is included based on uniform criteria; it serves international clients remotely. Buyers with requirements for in-country presence or language support should confirm those details. DeepStrike does not evidence local offices in Slovenia, but offers compliance-focused testing (e.g. PCI DSS) and cloud expertise that may benefit Slovenian organizations in regulated and modern digital sectors.
Testing Depth Model: Red Team-oriented DeepStrike’s methodology (as presented) simulates advanced attacker behavior through multi-stage workflows. The tester team reportedly exploits and validates vulnerabilities to assess impact (CVSS scoring). This indicates manual exploit-chaining and adversary-emulation relevance where supported by reviewed material. Their offerings (including Red Team assessments and Continuous Testing) indicate a focus on realistic breach-path validation and extended testing engagements.
Key Strengths:
Potential Limitations:
Best For: Regulated enterprises, SaaS/cloud-driven businesses, and modern API-first organizations seeking a rigorous, hands-on pentesting partner with a broad technical focus.

Why They Stand Out: Secmentis positions itself as a cybersecurity consultancy with manual testing and professional-credential relevance where evidenced. Their team holds a range of accreditations (CISA, CEH, GIAC). They emphasize customized penetration tests (“tailor-made for your organization”) and fixed-cost pricing. Secmentis’s approach includes thorough manual and automated methods to simulate external and insider attacks, aiming for high coverage of attack vectors.
Slovenia Relevance: Secmentis explicitly offers services in Slovenia and across Europe, suggesting familiarity with EU data protection environments. The firm’s experience with global clients (insurance, beverage, forex, etc. from testimonials) implies relevance for Slovenian enterprises and cross-border operations. Buyers should confirm local language or on-site support; Secmentis appears to operate remotely from the UK.
Testing Depth Model: Hybrid model Secmentis combines automated scanning with manual exploit techniques. They promote both custom tooling and standard tools. The presence of certified testers and a variety of penetration test types indicates a balanced approach: deeper manual analysis for high-risk targets, with automation for broader coverage.
Key Strengths:
Potential Limitations:
Best For: Large enterprises and multinational organizations seeking compliant, audit-ready penetration tests from experienced consultants.

Why They Stand Out: 3fs is an engineering-focused firm integrating cybersecurity into product development. It positions penetration testing within a broader DevSecOps context. The company holds multiple cloud certifications (AWS SysOps, Azure) and ISO 27001. Their testing services leverage in-house tools and continuous development pipelines, catering to IoT and SaaS clients. 3fs highlights agility and innovation (they call themselves a "socially responsible employer" compliant with ISO 26000).
Slovenia Relevance: Deeply local with offices in Kranj and Nordic outposts (Stockholm, Copenhagen), 3fs can serve Slovenian clients with regional support. Its Slovenian base and EU presence suggest familiarity with local standards. The focus on cloud and IoT makes it appealing for Slovenia’s tech firms and startups. Nordic office or client references may indicate cross-border relevance where evidenced; buyers should confirm delivery scope directly.
Testing Depth Model: Hybrid model 3fs combines automated tools with hands-on expertise. Cloud/AWS/Azure certifications imply deep cloud testing skill, while ISO27001 indicates formal processes. The mention of "ethical hacking" and red teaming suggests they perform manual exploit validation as part of their assessments.
Key Strengths:
Potential Limitations:
Best For: Cloud-native and IoT-driven companies (SMB to mid-market) seeking agile security testing integrated into development cycles, with a preference for EU/Slovenian delivery.
Why They Stand Out: OSI specializes in application and identity security. They combine custom penetration testing with system integration expertise. The company holds ISO/IEC 27001, ISO 20000, and ISO 9001 certifications, reflecting a mature quality and security management framework. OSI’s electronic identity positioning indicates identity and cryptography relevance where evidenced.
Slovenia Relevance: Operating from Slovenia and participating in EU-wide projects, OSI is familiar with local regulations (GDPR, government ID standards). Their niche in secure software development and infrastructure integration makes them a practical choice for Slovenian public entities and banks deploying national ID or secure e-services.
Testing Depth Model: Automated-heavy OSI’s emphasis on application security reviews and static code analysis suggests a focus on systematic scanning and code-based testing. They provide specialized application pentests, which likely combine tool-based code scans (SAST/DAST) with limited manual exploitation.
Key Strengths:
Potential Limitations:
Best For: Government agencies, financial institutions, and enterprises looking for specialized application and identity security testing, particularly within their own software development lifecycle.

Why They Stand Out: SIQ is the Slovenian Institute of Quality and Metrology and appears relevant for standards-driven cybersecurity assessment where evidenced. It provides penetration testing as part of its wide service portfolio. SIQ brings decades of compliance and standards experience to security assessments. It holds numerous accreditations (ISO 17025/17020/17065, ISO 9001:2015, ISO 27001:2022, etc.), making it well-suited to audit-heavy environments.
Slovenia Relevance: As a domestic institute, SIQ appears locally relevant for quality-assurance and standards-oriented buyers where evidenced. It serves local industries needing both product certification and cybersecurity, and thus understands national and EU regulatory contexts. Its penetration testing services are likely aligned with broader product safety and compliance goals.
Testing Depth Model: Hybrid (leaning manual) SIQ’s Red Team and “cybersecurity testing for connected products” offerings imply human-driven tests. Their emphasis on complete solutions suggests thorough manual validation, though exact methodology details are limited.
Key Strengths:
Potential Limitations:
Best For: Large enterprises and public sector organizations needing audit-quality penetration tests tied to formal certification/regulatory programs, especially where cross-domain testing (IT/OT) is needed.
Why They Stand Out: ASTEC is one of Slovenia’s oldest ICT security consultancies. It offers comprehensive security assessments, emphasizing compliance and ICT governance. Their partnership history (now part of Unistar LC) signals alignment with leading vendors. ASTEC’s positioning around security management and ISO-oriented consulting may be relevant for risk-averse sectors where evidenced.
Slovenia Relevance: As a domestic firm founded in 1991, ASTEC knows Slovenian regulatory environments intimately. Public-sector or telecom references should be included only where directly evidenced in Source Notes., indicating trust in highly regulated projects.
Testing Depth Model: Hybrid ASTEC blends automated scans with manual security reviews. Given their consulting background, their penetration testing is likely structured and compliance-oriented, possibly more conservative than offensive. They explicitly implement security policy by ISO standards.
Key Strengths:
Potential Limitations:
Best For: Public-sector agencies and heavily regulated companies requiring risk-based assessments and compliance-driven penetration testing with a known local partner.

Why They Stand Out: GO-LIX is a veteran security firm (over 30 years) focused purely on information security. They explicitly mention a certified and experienced project team conducting all types of penetration tests, security audits, and incident response. The founder and team hold advanced certifications (CEH Master, OSCP, OSWP, CompTIA Pentest+), signaling hands-on technical prowess.
Slovenia Relevance: Based in Slovenia’s west, GO-LIX delivers local expertise with a long-standing local reputation. They mention GDPR services and ISO 27001 prep, which aligns with compliance requirements in Slovenian enterprise. Their service range covers both corporate and possibly government clients.
Testing Depth Model: Manual exploit chaining with senior OSCP-certified testers, GO-LIX emphasizes deep technical analysis. The presence of OSWP (wireless focus) suggests they cover unconventional network segments as well. They likely rely on heavy manual testing in addition to standard tooling.
Key Strengths:
Potential Limitations:
Best For: Small to mid-sized enterprises or divisions needing intensive technical testing or red teaming by seasoned professionals, especially where personal attention and bespoke testing (e.g. wireless, OT) is valued.
Why They Stand Out: Viris is a local cybersecurity firm with explicit focus on penetration testing. Their marketing states that system, network, and mobile penetration testing are their core business. They outline a thorough methodology (scoping, scanning, exploit, reporting, retesting) using OWASP standards. This suggests a disciplined approach targeting real infrastructure and applications.
Slovenia Relevance: As a domestic provider in Maribor, Viris may be relevant for Slovenian buyers seeking local coordination; language support and on-site testing should be confirmed directly. They have explicit mentions of using OWASP methods and providing verification after remediation, aligning with Slovenian buyers’ needs for clear process and results.
Testing Depth Model: Hybrid model Viris emphasizes both automated scanning and manual testing. They note the use of “different methodologies like OWASP” and ability to do black/grey/white box tests. This indicates a balance between tool use and hands-on validation.
Key Strengths:
Potential Limitations:
Best For: Regional SMEs and manufacturing firms in northeastern Slovenia that need practical penetration testing and remediation support, especially those wanting local language and direct engagement.
Why They Stand Out: VitalIT is a Slovenian IT consultancy that includes cybersecurity testing among its services. They brand themselves as advocates of best practices, with a focus on network audits and encouraging organizations to secure assets before testing. They mention expertise in information security basics and provide educational content. Notably, they facilitate clients securing EU co-funding (Digital Innovation Hub vouchers) for penetration tests, indicating an active role in the local tech community.
Slovenia Relevance: A Ljubljana-based firm, VitalIT is fully local and speaks to domestic buyers about co-financing options. Its Slovenian-language presence and small-team approach may appeal to smaller businesses and government units. Any innovation or recognition claims should be included only where directly evidenced and relevant to procurement evaluation.
Testing Depth Model: Hybrid VitalIT’s offerings combine automated network scans with manual tests. As network security check and penetration testing are separate services, they likely perform basic pen tests (network layer, social engineering) possibly with less emphasis on deep application exploits. They also simulate physical intrusion, which is more manual.
Key Strengths:
Potential Limitations:
Best For: Slovenian small businesses and public organizations that need a pragmatic security check and compliance awareness, possibly leveraging co-funded programs.
Buyers often equate big brand names with better security results, but size does not guarantee penetration depth. Over-reliance on automated tools is a common pitfall: a superficial scan can miss chained exploits or business-logic flaws. Some organizations focus on compliance checkboxes (e.g. “we did a pen test”) without verifying actual exploitability. Others undervalue report clarity. A colorful scan report is useless if it doesn’t explain how to fix issues in context. Confusion between vulnerability scanning and true penetration testing is frequent: the former lists known flaws, the latter proves what an attacker can achieve. Many buyers assume penetration tests cover all modern risks; in reality, tests must explicitly include APIs, identity systems, and cloud configurations to be comprehensive. Another mistake is assuming PTaaS or platform-based providers inherently deliver deeper tests often they automate recurring scans rather than simulate real attacks. Finally, we’ve seen buyers overvalue a local office as a proxy for quality; in Slovenia’s market, the technical methodology matters far more than where a company’s logo is printed. Always verify that the chosen vendor actually employs the promised manual exploit validation and has demonstrable expertise for your specific environment.
Enterprises face extensive digital footprints and regulatory scrutiny, so they invest in deep, multi-scope tests (internal/external, application suites, IoT, etc.) and often demand continuous or red-team services. They can afford premium firms with broad expertise and compliance support. Large organizations also may choose global consultancies (Secmentis, SIQ) that offer formal processes and extensive reporting. In contrast, SMBs need efficient, cost-effective tests focused on their critical assets. SMBs often benefit from agile local providers (GO-LIX, 3fs, CyberAudit) who balance price with thoroughness.
Risk tolerance scales with size: larger companies may accept higher costs for confidence, while smaller ones weigh cost vs coverage. Boutique or medium-sized specialized firms can deliver SMBs with more targeted depth per euro, whereas big consultancies may add overhead. Regulatory intensity also plays a role: a fintech might behave like an enterprise (needing compliance evidence), whereas a small tech startup may prioritize a quick vulnerability check.
Boutique depth vs global scale: Large firms can marshal bigger teams for simultaneous projects (beneficial for multi-site/multi-country tests), but they may charge a premium and have rigid processes. Niche specialists provide personal service and flexibility, but may lack multinational exposure.
Finally, SMBs often have simpler networks but can still run complex cloud services. They should ensure cloud/APIs are tested. Enterprises, meanwhile, need to balance red team realism with budget; they might integrate pentesting into a continuous security program (DevSecOps or PTaaS), while SMBs often stick to annual or biannual pentests. Choose based on scope complexity, compliance needs, and change velocity: cloud-first companies (even SMBs) need firms with strong API and cloud expertise, whereas traditional enterprises might also require OT and physical security tests.
Costs are driven by scope and complexity. Larger IP ranges, more web applications, and extensive cloud infrastructure mean more testing hours. Adding diverse scope (network, wireless, physical, IoT) raises effort. Authenticated vs. unauthenticated testing: providing credentials increases time but yields deeper insights. Application complexity: custom, legacy, or poorly documented systems take longer than standard apps. API or mobile components add specialized testing steps.
Testing depth: A test focusing on basic vulnerability scanning is cheaper than one with extensive manual exploit attempts. Retesting and remediation support increase price but ensure fixes worked many firms include a follow-up test. Reporting needs: Detailed executive reports and compliance mappings (e.g. to GDPR or ISO controls) take analyst time. Delivery mode: On-site engagements (travel/time) cost more than remote. In Slovenia’s case, local remote testing can reduce travel fees.
Compliance requirements: If the test must meet PCI DSS, NIS2, or other frameworks, additional documentation and scope (e.g. segmented tests for PCI networks) add effort. Organization size and structure: more stakeholders or distributed teams require more coordination.
Finally, remember that vendor model matters: subscription/PTaaS services can spread costs over time but may have minimum terms, while one-off engagements charge by project. Buyers should focus on needed outcomes rather than per-day rates. A thorough test with actionable results is more valuable than a lower quote that only covers cursory scanning.
How much do penetration testing services cost in Slovenia?
Costs vary widely with scope. Instead of quoting rates, consider factors: number of assets (servers, apps), complexity (e.g. custom APIs, cloud environment), and testing depth (automated scan vs hands-on validation). A small internal network pentest might run tens of hours; a comprehensive external+application test across cloud services could span weeks of effort. Buyers should obtain detailed quotes based on their exact requirements. Remember that cheaper services often use automated tools only, which may leave risk gaps.
What is included in enterprise penetration testing?
Typically, an enterprise-grade engagement covers external (internet-facing) infrastructure, internal networks, web application testing, mobile apps, APIs, and often wireless/physical security. It includes authenticated scenarios (with provided credentials) and multi-step exploitation. The deliverable should be an executive summary plus a technical report with reproduction steps, risk ratings, and remediation guidance. For compliance-driven tests, the report may include mapping to relevant controls (GDPR, ISO 27001 clauses, etc.). Enterprises often get some retesting of critical issues to verify fixes.
Are certifications more important than tools?
Both matter but in different ways. Certifications like OSCP, OSWE, CREST, GIAC (GPEN, etc.) demonstrate a tester’s proven skills in real-world hacking techniques. Tools are essential for efficiency, but smart testers know that no tool finds every vulnerability and that tools often miss logic flaws. In procurement, prioritize tester experience and qualifications tools should complement, not replace, human expertise. A certified expert with basic tools is generally more effective than an uncertified operator with fancy scanners.
How long does a pentest engagement take?
Typical durations in Slovenia range from a few days (for small web app or network tests) to several weeks (for full-scope enterprise tests). Simple application or network tests might be 1–2 weeks end-to-end (scoping, testing, reporting). Large multi-layered assessments (multiple networks, large codebases, cloud services) can take 4–6 weeks or more. Timeline also depends on scheduling, retest inclusion, and the need for interim reviews. Always confirm the proposed schedule and ensure it includes buffer time for remediation.
Is penetration testing required for GDPR, NIS2, or other regulations?
No law explicitly mandates pentesting for all organizations. However, GDPR and NIS2 (EU directives) require “appropriate technical measures” to protect personal data and critical systems. Pentesting is considered a best practice to demonstrate due diligence in those areas. Financial regulators (Bank of Slovenia) and Slovenian information security laws emphasize risk assessments, which often include testing. In practice, any company under audit-heavy regimes (finance, health, public sector) should have regular penetration tests to satisfy auditors, but it is not a universal statutory checkbox. Buyers should confirm their specific compliance obligations with regulators.
How often should penetration testing be performed?
Annually is a common minimum for most environments, or whenever major changes occur (new applications, system upgrades, mergers). Highly dynamic or critical systems may benefit from more frequent testing or continuous testing where release velocity or exposure changes are high. In regulated sectors, tests are often required at least once a year or after significant changes. Ultimately, the frequency should match the organization’s risk profile and change rate e.g. ecommerce sites updated weekly might test every quarter, while static legacy systems might test yearly.
Should Slovenia buyers choose a local provider or a cross-border specialist?
It depends on priorities. Local firms (3fs, SIQ, ASTEC, GO-LIX, Viris, VitalIT, CyberAudit) offer easier communication, potential on-site support, and better understanding of local context. They may also help navigate regional funding schemes. However, specialized cross-border vendors (DeepStrike, Secmentis) may bring broader expertise in niche areas (cloud security, global threat intel) and scalability. In many cases, a hybrid approach works: use a local provider for initial testing and strategy, and supplement with external specialists for red teaming or specific technologies. Importantly, verify that any chosen firm can legally and technically operate in Slovenia (e.g. data handling, remote access) and meets EU data protection expectations.
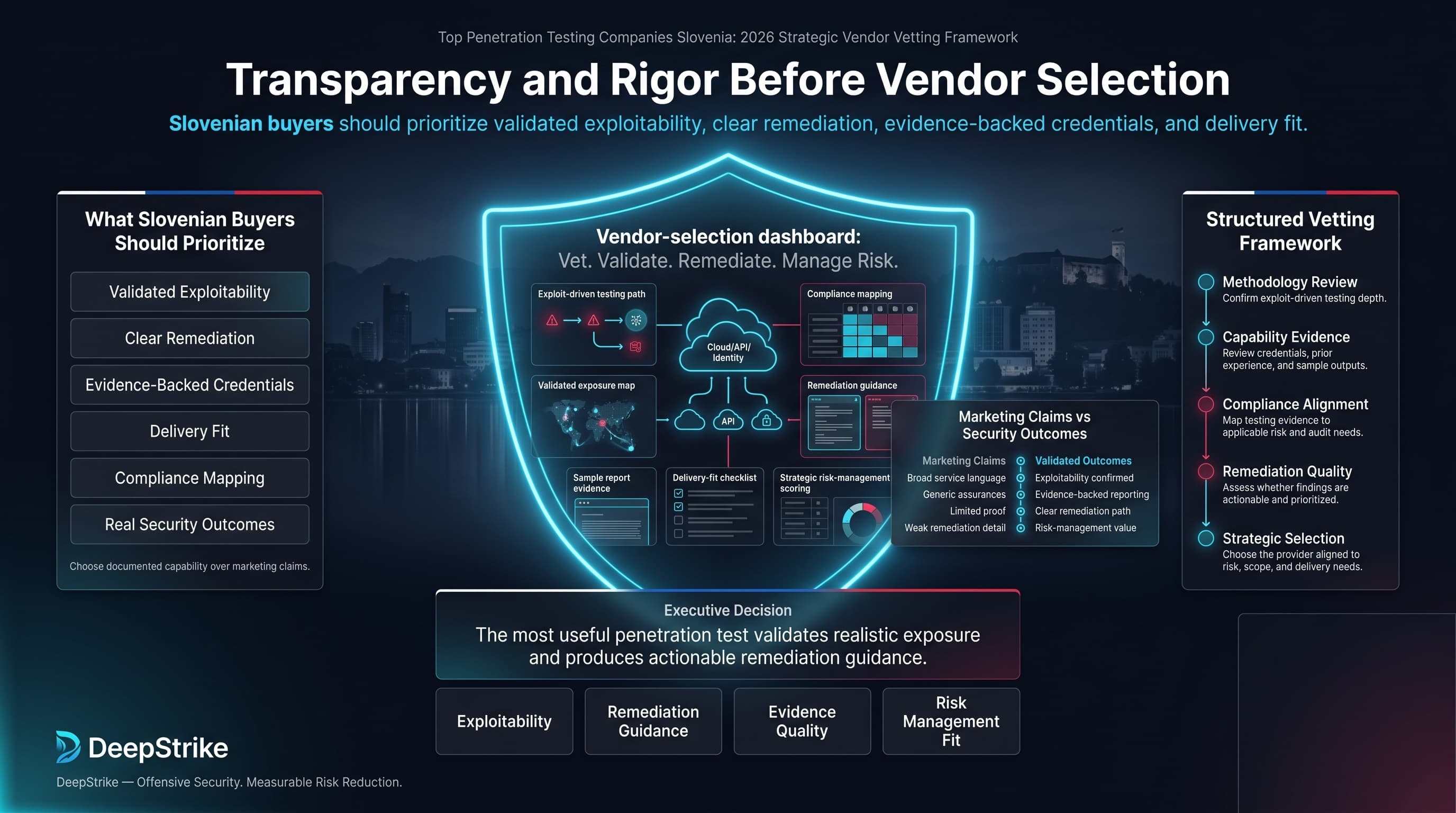
Selecting a penetration testing partner in Slovenia demands transparency and rigor. This vendor comparison has laid out key differences in methodology, expertise, and local fit. By focusing on documented capabilities and real security outcomes (not just marketing claims), Slovenian buyers can shortlist firms that truly align with their compliance and risk needs. The listed companies have been ranked based on consistent criteria from exploit-driven testing depth to compliance mapping to assist in procurement. Remember: The most useful penetration test is one that validates realistic exposure and produces actionable remediation guidance. Prioritize validated exploitability, clear remediation, evidence-backed credentials, and delivery fit over brand visibility alone. With informed choice and structured vetting, organizations in Slovenia can turn penetration testing into a strategic risk management tool rather than a perfunctory exercise.
Mohammed Khalil is a Cybersecurity Architect at DeepStrike, specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements for Fortune 500 companies, focusing on cloud security, application vulnerabilities, and adversary emulation. His work involves dissecting complex attack chains and developing resilient defense strategies for clients in the finance, healthcare, and technology sectors.

Stay secure with DeepStrike penetration testing services. Reach out for a quote or customized technical proposal today
Contact Us